Frauds in Indian Banks
Diunggah oleh
Vivek SinghDeskripsi Asli:
Judul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Frauds in Indian Banks
Diunggah oleh
Vivek SinghHak Cipta:
Format Tersedia
Frauds in Indian Banking Sector
Introduction:
EVOLUTION OF BANKING SYSTEM IN INDIA:
Banking system occupies an important place in a nations economy. A banking
institution is indispensable in a modern society. It plays a pivotal role in
economic development of a country and forms the core of the money market in
an advanced country.
Banking industry in India has traversed a long way to assume its present stature.
It has undergone a major structural transformation after the nationalization of 14
major commercial banks in 1969 and 5 more on 15 April 1980.
Banks are the engines that drive the operations in the financial sector, which is
vital for the economy. With the nationalization of banks in 1969, they also have
emerged as engines for social change. After Independence, the banks have
passed through three stages. They have moved from the character based lending
to ideology based lending to today competitiveness based lending in the context
of India's economic liberalization policies and the process of linking with the
global economy.
A sound banking system should possess three basic characteristics to protect
depositors interest and public faith. Theses are
(i)
a fraud free culture,
(ii)
a time tested Best Practice Code, and
(iii)
an in house immediate grievance remedial system. All these
conditions are their missing or extremely weak in India.
Section 5(b) of the Banking Regulation Act, 1949 defines banking as
Banking is the accepting for the purpose of lending or investment, deposits of
Frauds in Indian Banking Sector
money from the purpose of lending or investment, deposits of money from the
public, repayable on demand or otherwise and withdraw able by cheque, draft,
order or otherwise.
In the present day, Global Scenario Banking System has acquired new
dimensions. Banking did spread in India. Today, the banking system has entered
into competitive markets in areas covering resource mobilization, human
resource development, customer services and credit management as well.
With the rising banking business, frauds in banks are also increasing and the
fraudsters are becoming more and more sophisticated and ingenious. In a bid to
keep pace with the changing times, the banking sector has diversified its
business manifold. Replacement of the philosophy of class banking with mass
banking in the post-nationalization period has thrown a lot of challenges to the
management on reconciling the social responsibility with economic viability.
The banking system in our country has been taking care of all segments of our
socio-economic set up. A bank fraud is a deliberate act of omission or
commission by any person carried out in the course of banking transactions or
in the books of accounts, resulting in wrongful gain to any person for a
temporary period or otherwise, with or without any monetary loss to the bank.
Definition of Fraud:
Fraud is defined as any behavior by which one person intends to gain a
dishonest advantage over another. In other words , fraud is an act or omission
which is intended to cause wrongful gain to one person and wrongful loss to the
other, either by way of concealment of facts or otherwise.
Fraud is defined u/s 421 of the Indian Penal Code and u/s 17 of the Indian
Contract Act. Thus essential elements of frauds are:
Frauds in Indian Banking Sector
1. There must be a representation and assertion;
2. It must relate to a fact;
3. It must be with the knowledge that it is false or without belief in its
truth; and
4. It must induce another to act upon the assertion in question or to do or
not to do certain act.
A false representation of a matter of fact whether by words or by conduct, by
false or misleading allegations, or by concealment of what should have been
disclosed that deceives and is intended to deceive another so that the
individual will act upon it to her or his legal injury.
In law, the deliberate misrepresentation of fact for the purpose of depriving
someone of a valuable possession or legal right. Any omission or concealment
that is injurious to another or that allows a person to take unconscionable
advantage of another may constitute criminal fraud. The most common type of
fraud is the obtaining of property by giving a check for which there is
insufficient funds in the signer's account. Another is the assumption of someone
else's or a fictitious identity with the intent to deceive. Also important are mail
and wire fraud (fraud committed by use of the postal service or electronic
devices, such as telephones or computers). A tort action based on fraud is
sometimes referred to as an action of deceit.
Bank Frauds:
Losses sustained by banks as a result of frauds exceed the losses due to robbery,
dacoit, burglary and theft-all put together. Unauthorized credit facilities are
extended for illegal gratification such as case credit allowed against pledge of
goods, hypothecation of goods against bills or against book debts. Common
modus operandi are, pledging of spurious goods, inletting the value of goods,
hypothecating goods to more than one bank, fraudulent removal of goods with
Frauds in Indian Banking Sector
the knowledge and connivance of in negligence of bank staff, pledging of goods
belonging to a third party.
While the operations of the bank have become increasingly significant, there is
also an occupation hazard. There is a Tamil proverb, which says that a man who
collects honey will always be tempted to lick his fingers. Banks are all the time
dealing with money and the temptation should therefore is very high. Oscar
Wilde said that the thief was an artist and the policeman was only a critic. There
are many people who are unscrupulous and are able to perpetrate a fraud. We
must be able to see that we devise our systems and procedures in such a way
that the scope for such clever and unscrupulous people is reduced.
Frauds in deposit accounts take place by opening of bogus accounts, forging
signatures of introducers and collecting through such accounts stolen or forged
cheques or bank drafts. Frauds are also committed in the area of granting
overdraft facility in the current accounts of customers. A large number of frauds
have been committed through bank draft, mail transfers and telegraphic
transfers.
An analysis made of cases brings out broadly the under mentioned four major
elements responsible for the commission of frauds in banks.
1. Active involvement of the staff-both supervisor and clerical either
independent of external elements or in connivance with outsiders.
2. Failure on the part of the bank staff to follow meticulously laid down
instructions and guidelines.
3. External elements perpetuating frauds on banks by forgeries or
manipulations of cheques, drafts and other instruments.
Frauds in Indian Banking Sector
4. There has been a growing collusion between business, top banks
executives, civil servants and politicians in power to defraud the banks,
by getting the rules bent, regulations flouted and banking norms thrown
to the winds.
5. Mechanics of bank frauds:
By Insiders:
1. Wire fraud
Wire transfer networks such as the international interbank fund transfer
system are tempting as targets as a transfer, once made, is difficult or
impossible to reverse. As these networks are used by banks to settle accounts
with each other, rapid or overnight wire transfer of large amounts of money
are commonplace; while banks have put checks and balances in place, there
is the risk that insiders may attempt to use fraudulent or forged documents
which claim to request a bank depositor's money be wired to another bank,
often an offshore account in some distant foreign country.
2. Rogue traders
A rogue trader is a highly placed insider nominally authorised to invest
sizeable funds on behalf of the bank; this trader secretly makes progressively
more aggressive and risky investments using the bank's money, when one
investment goes bad, the rogue trader engages in further market speculation
in the hope of a quick profit which would hide or cover the loss.
Unfortunately, when one investment loss is piled onto another, the costs to
the bank can reach into the hundreds of millions of dollars; there have even
been cases in which a bank goes out of business due to market investment
losses.
5
Frauds in Indian Banking Sector
3. Fraudulent loans
One way to remove money from a bank is to take out a loan, a practice
bankers would be more than willing to encourage if they know that the
money will be repaid in full with interest. A fraudulent loan, however, is one
in which the borrower is a business entity controlled by a dishonest bank
officer or an accomplice; the "borrower" then declares bankruptcy or
vanishes and the money is gone. The borrower may even be a non-existent
entity and the loan merely an artifice to conceal a theft of a large sum of
money from the bank.
4. Forged or fraudulent documents:
Forged documents are often used to conceal other thefts; banks tend to count
their money meticulously so every penny must be accounted for. A document
claiming that a sum of money has been borrowed as a loan, withdrawn by an
individual depositor or transferred or invested can therefore be valuable to a
thief who wishes to conceal the minor detail that the bank's money has in
fact been stolen and is now gone.
5. Uninsured deposits
There are a number of cases each year where the bank itself turns out to be
uninsured or not licensed to operate at all. The objective is usually to solicit
for deposits to this uninsured "bank", although some may also sell stock
representing ownership of the "bank". Sometimes the names appear very
official or very similar to those of legitimate banks. For instance, the "Chase
Trust Bank" of Washington D.C. appeared in 2002 with no licence and no
affiliation to its seemingly apparent namesake; the real Chase Manhattan
Bank is based in New York.
Frauds in Indian Banking Sector
There is a very high risk of fraud when dealing with unknown or uninsured
institutions.
The risk is greatest when dealing with offshore or Internet banks (as this
allows selection of countries with lax banking regulations), but not by any
means limited to these institutions.
6. Demand draft fraud
Demand draft fraud is usually done by one or more dishonest bank
employees. They remove few DD leaves or DD books from stock and write
them like a regular DD. Since they are insiders, they know the coding,
punching of a demand draft. These Demand drafts will be issued payable at
distant town/city without debiting an account. Then it will be cashed at the
payable branch. For the paying branch it is just another DD. This kind of
fraud will be discovered only when the head office does the branch-wise
reconciliation, which normally will take 6 months. By that time the money is
unrecoverable.
By others:
7. Forgery and altered cheques
Thieves have altered cheques to change the name (in order to deposit
cheques intended for payment to someone else) or the amount on the face of
a cheque (a few strokes of a pen can change Rs.10000 into Rs.100,000,
although such a large figure may raise some eyebrows).
Instead of tampering with a real cheque, some fraudsters will attempt to
forge a depositor's signature on a blank cheque or even print their own
cheques drawn on accounts owned by others, non-existent accounts or even
alleged accounts owned by non-existent depositors. The cheque will then be
7
Frauds in Indian Banking Sector
deposited to another bank and the money withdrawn before the cheque can
be returned as invalid or for non-sufficient funds.
8. Stolen cheques
Some fraudsters obtain access to facilities handling large amounts of
cheques, such as a mailroom or post office or the offices of a tax authority
(receiving many cheques) or a corporate payroll or a social or veterans'
benefit office (issuing many cheques). A few cheques go missing; accounts
are then opened under assumed names and the cheques (often tampered or
altered in some way) deposited so that the money can then be withdrawn by
thieves. Stolen blank chequebooks are also of value to forgers who then sign
as if they were the depositor
9. Accounting fraud
In order to hide serious financial problems, some businesses have been
known to use fraudulent bookkeeping to overstate sales and income, inflate
the worth of the company's assets or state a profit when the company is
operating at a loss. These tampered records are then used to seek investment
in the company's bond or security issues or to make fraudulent loan
applications in a final attempt to obtain more money to delay the inevitable
collapse of an unprofitable or mismanaged firm.
Accounting fraud has also been used to conceal other theft taking place
within a company.
10.Bill discounting fraud
Essentially a confidence trick, a fraudster uses a company at their disposal to
gain confidence with a bank, by appearing as a genuine, profitable customer.
To give the illusion of being a desired customer, the company regularly and
8
Frauds in Indian Banking Sector
repeatedly uses the bank to get payment from one or more of its customers.
These payments are always made, as the customers in question are part of
the fraud, actively paying any and all bills raised by the bank. After time,
after the bank is happy with the company, the company requests that the
bank settles its balance with the company before billing the customer. Again,
business continues as normal for the fraudulent company, its fraudulent
customers, and the unwitting bank. Only when the outstanding balance
between the bank and the company is sufficiently large, the company takes
the payment from the bank, and the company and its customers disappear,
leaving no-one to pay the bills issued by the bank.
11.Cheque kiting
Cheque kiting exploits a system in which, when a cheque is deposited to a
bank account, the money is made available immediately even though it is not
removed from the account on which the cheque is drawn until the cheque
actually clears.
Deposit Rs.1000 in one bank, write a cheque on that amount and deposit it to
your account in another bank; you now have Rs2000 until the cheque clears.
In-transit or non-existent cash is briefly recorded in multiple accounts.
A cheque is cashed and, before the bank receives any money by clearing the
cheque, the money is deposited into some other account or withdrawn by
writing more cheques. In many cases, the original deposited cheque turns out
to be a forged cheque.
Some perpetrators have swapped checks between various banks on a daily
basis, using each to cover the shortfall for a previous cheque.
Frauds in Indian Banking Sector
What they were actually doing was check kiting; like a kite in the wind, it
flies briefly but eventually has to come back down to the ground.
12.Payment card fraud:
Credit card fraud is widespread as a means of stealing from banks,
merchants and clients. A credit card is made of three plastic sheet of
polyvinyl chloride. The central sheet of the card is known as the core stock.
These cards are of a particular size and many data are embossed over it. But
credit cards fraud manifest in a number of ways.
They are:
i) Genuine cards are manipulated
ii) Genuine cards are altered
iii) Counterfeit cards are created
iv) Fraudulent telemarketing is done with credit cards.
v) Genuine cards are obtained on fraudulent applications in the
names/addresses of other persons and used.
It is feared that with the expansion of E-Commerce, M-Commerce and
Internet facilities being available on massive scale the fraudulent fund
freaking via credit cards will increase tremendously.
i) Booster cheques:
A booster cheque is a fraudulent or bad cheque used to make a payment to a
credit card account in order to "bust out" or raise the amount of available
credit on otherwise-legitimate credit cards. The amount of the cheque is
credited to the card account by the bank as soon as the payment is made,
even though the cheque has not yet cleared. Before the bad cheque is
discovered, the perpetrator goes on a spending spree or obtains cash
10
Frauds in Indian Banking Sector
advances until the newly-"raised" available limit on the card is reached. The
original cheque then bounces, but by then it is already too late.
ii) Stolen payment cards:
Often, the first indication that a victim's wallet has been stolen is a phone
call from a credit card issuer asking if the person has gone on a spending
spree; the simplest form of this theft involves stealing the card itself and
charging a number of high-ticket items to it in the first few minutes or hours
before it is reported as stolen.
A variant of this is to copy just the credit card numbers (instead of
drawing attention by stealing the card itself) in order to use the numbers in
online frauds. The use of a four digit Personal Identity Number (PIN) instead
of a signature helps to prevent this type of fraud.
iii) Duplication or skimming of card information:
This takes a number of forms, ranging from a dishonest merchant copying
clients' credit card numbers for later misuse (or a thief using carbon copies
from old mechanical card imprint machines to steal the info) to the use of
tampered credit or debit card readers to copy the magnetic stripe from a
payment card while a hidden camera captures the numbers on the face of the
card.
Some thieves have surreptitiously added equipment to publicly accessible
automatic teller machines; a fraudulent card stripe reader would capture the
contents of the magnetic stripe while a hidden camera would sneak a peek at
the user's PIN. The fraudulent equipment would then be removed and the
data used to produce duplicate cards that could then be used to make ATM
withdrawals from the victims' accounts.
11
Frauds in Indian Banking Sector
13.Empty ATM envelope deposits:
A criminal overdraft can result due to the account holder making a worthless
or misrepresented deposit at an automated teller machine in order to obtain
more cash than present in the account or to prevent a check from being
returned due to non-sufficient funds. The crime could also be perpetrated
against another person's account in an "account takeover" or with a
counterfeit ATM card, or an account opened in another person's name as part
of an identity theft scam. This scenario may become a thing of the past next
decade due to the emergence of ATM deposit technology that scans currency
and checks without using an envelope.
14. Impersonation:
Impersonation has become an increasing problem; the scam operates by
obtaining information about an individual, then using the information to
apply for identity cards, accounts and credit in that person's name. Often
little more than name, parents' name, date and place of birth are sufficient to
obtain a birth certificate; each document obtained then is used as
identification in order to obtain more identity documents. Governmentissued standard identification numbers such as "social security numbers"
PAN numbers are also valuable to the fraudster.
Information may be obtained from insiders (such as dishonest bank or
government employees), by fraudulent offers for employment or investments
(in which the victim is asked for a long list of personal information) or by
sending forged bank or taxation correspondence.
In some cases, a name is needed to impersonate a citizen while working as
an illegal immigrant but often the identity thieves are using the bogus
12
Frauds in Indian Banking Sector
identity documents in the commission of other crimes or even to hide from
prosecution for past crimes. The use of a stolen identity for other frauds such
as gaining access to bank accounts, credit cards, loans and fraudulent social
benefit or tax refund claims is not uncommon.
Unsurprisingly, the perpertators of such fraud have been known to take out
loans and disappear with the cash, quite content to see the wrong persons
blamed when the debts go bad or the police come calling.
15. Fraudulent loan applications
These take a number of forms varying from individuals using false
information to hide a credit history filled with financial problems and unpaid
loans to corporations using accounting fraud to overstate profits in order to
make a risky loan appear to be a sound investment for the bank.
Some corporations have engaged in over-expansion, using borrowed money
to finance costly mergers and acquisitions and overstating assets, sales or
income to appear solvent even after becoming seriously financially
overextended.
16. Prime bank fraud:
The "prime bank" operation which claims to offer an urgent, exclusive
opportunity to cash in on the best-kept secret in the banking industry,
guaranteed deposits in "prime banks", "constitutional banks", "bank notes
and bank-issued debentures from top 500 world banks", "bank guarantees
and standby letters of credit" which generate spectacular returns at no risk
and are "endorsed by the World Bank" or various national governments and
central bankers. However, these official-sounding phrases and more are the
hallmark of the so-called "prime bank" fraud; they may sound great on
13
Frauds in Indian Banking Sector
paper, but the guaranteed offshore investment with the vague claims of an
easy 100% monthly return are all fictitious financial instruments intended to
defraud individuals.
17. Phishing and Internet fraud:
Phishing operates by sending forged e-mail, impersonating an online bank,
auction or payment site; the e-mail directs the user to a forged web site
which is designed to look like the login to the legitimate site but which
claims that the user must update personal info. The information thus stolen is
then used in other frauds, such as theft of identity or online auction fraud.
Phishing means sending an e-mail that falsely claims to be a particular
enterprise and asking for sensitive financial information. Phishing, thus, is an
attempt to scam the user into surrendering private information that will then
be used by the scammer for his own benefit.Phishing uses 'spoofed' e-mails
and fraudulent Web sites that look very similar to the real ones thus fooling
the recipients into giving out their personal data. Most phishing attacks ask
for credit card numbers, account usernames and passwords. According to
statistics phishers are able to convince up to five per cent of the recipients
who respond to them.
18. Money laundering
Money laundering has been used to describe any scheme by which the true
origin of funds is hidden or concealed.
The operations work in various forms. One variant involved buying
securities (stocks and bonds) for cash; the securities were then placed for
safe deposit in one bank and a claim on those assets used as collateral for a
loan at another bank. The borrower would then default on the loan. The
14
Frauds in Indian Banking Sector
securities, however, would still be worth their full amount. The transaction
served only to disguise the original source of the funds.
19. Forged currency notes:
Paper currency is the usual mode of exchange of money at the personal level,
though in business, cheques and drafts are also used considerably. Bank note
has been defined in Section 489A.If forgery of currency notes could be done
successfully then it could on one hand made the forger millionaire and the
other hand destroy the economy of the nation. A currency note is made out of
a special paper with a coating of plastic laminated on both sides of each note
to protect the ink and the anti forgery device from damage. More over these
notes have security threads, water marks. But these things are not known to
the majority of the population. Forged currency notes are in full circulation
and its very difficult to catch hold of such forgers as once such notes are
circulated its very difficult to track its origin.
20. Computer Frauds:
Computerization has brought advantages of efficiency, speed and economy
in all spheres of life. It is a very powerful tool and provides opportunities of
efficiency and speed to everybody using it. Further, the vast increase in the
memory (whether RAM or storage) and processing speeds as well as
availability of wide range of software, particularly Internet and web-based
applications i.e. connectivity, have made them pervade all aspects of our
lives. This has also brought large economy of scale particularly in our
economic environment and we are becoming more and more dependent on
computers and their networks for the services such systems deliver.
Frauds committed using computers vary from complex financial frauds
where large amounts are illegally transferred between accounts by
15
Frauds in Indian Banking Sector
sophisticated hackers, to the simpler frauds where computer is only a tool
that a criminal uses to commit a crime.
It also provides ample opportunities for their misuse particularly for
economic or financial gains. This is as computers networks can also be used
to commit crimes from geographically far places. Such computer frauds are
known by various names such as cyber crimes or e-crimes and we can
describe them as an act involving computer equipment, software or data that
results in an unauthorized financial advantage. Worldwide frauds in
computerized environment cause losses running into very large sums.
Although in India, frauds committed so far have not revealed any extensive
manipulation of computer systems, it is no doubt a potentially high-risk area,
which should be addressed carefully and in timely manner. According to a
recent survey, companies in India have not addressed security issues
appropriately.
1) Manipulation:
In an ideal situation, where information systems have all the necessary
controls, which are properly integrated with other manual controls and
maintained, there will generally be no cause of worry. It is however, not so.
Not only, most system controls are not perfect, people also try to manipulate
systems for variety of motives from games playing, ego peer pressure, and
hatred for the organization, emotional maladjustment, blackmail and
economic gains. Such people could be insiders, outsiders as well as vendors,
competitors in fact any one.
Computer frauds gain their criticality as they are easy to commit, difficult to
detect and even harder to prove. The most important type of such frauds is
16
Frauds in Indian Banking Sector
committing the fraud by manipulation of input, output or throughput of a
computer system.
a) Input Manipulation:
In input manipulation, input data such as deposit amounts in ledgers, limits
in accounts or face value of cheques are changed.
b) Output manipulation:
Output manipulation is achieved by affecting the output of the system, such
as use of stolen or falsified cards in ATM machines.
c) Throughput manipulation:
Throughput manipulation could be by rounding off sums credited to different
accounts and siphoning of the rounded digits to another account. No system
is foolproof and fraudulent transfers can occur in even highly automated and
secure funds transfer systems.
2) Unauthorized use:
Other types of such frauds or crimes could be unauthorized access to
computers by hacking into systems or stealing passwords, deliberate damage
caused to computer data or programs, computer forgery (changing of data or
images stored in computers) and un-authorized reproduction / modification
of computer programs.
3) Awareness:
Other important causes of such frauds are lack of employee awareness, poor
implementation of security policies and segregation of duties, vendor
products with weak security controls, outsourced service providers and
17
Frauds in Indian Banking Sector
hackers (many as young as school students). Computer frauds in such cases
are generally for economic benefit to the fraudster and corresponding loss to
the organization
Other sources of computer crimes are terrorists, organized criminals and
groups hating the organization.
Frauds- Prevention and Detection:
A close study of any fraud in bank reveals many common basic features. There
may have been negligence or dishonesty at some stage, on part of one or more
of the bank employees. One of them may have colluded with the borrower. The
bank official may have been putting up with the borrowers sharp practices for a
personal gain. The proper care which was expected of the staff, as custodians of
banks interest may not have been taken. The banks rules and procedures laid
down in the Manual instructions and the circulars may not have been observed
or may have been deliberately ignored.
Components of Fraud:
There are two important components in any fraud committed by an employee of
a bank, himself or in collusion with a burrower. They are, firstly, the intention
which is subjective; and secondly, the opportunity which is objective.
Conditions must be created in the bank that the person who intends perpetrating
a fraud does not get the opportunity to commit it.
In India, the design, management and regulation of electronically-based
payments system are becoming the focus of policy deliberations. The
imperatives of developing an effective, efficient and speedy payment and
settlement systems are getting sharper with introduction of new instruments
such as credit cards, telebanking, ATMs, retail Electronic Funds Transfer (EFT)
18
Frauds in Indian Banking Sector
and Electronic Clearing Services (ECS). We are moving towards smart cards,
credit and financial Electronic Data Interchange (EDI) for straight through
processing.
We are basically concerned about computer frauds committed by an
unauthorized user (whether insider or outsider) to the computer networks, which
aims at causing economic or financial gains to the user by this act or an
economic or financial loss to the information system (i.e. hardware, software
and data) owner.
Prevention of frauds:
i) Internal Prevention:
It is said that failures are the stepping stone for success. What this means is that
if we are able to analyse why a particular failure by way of a fraud took place,
we can then detect the loopholes in our system which led to the fraud and take
corrective measures or change the system. For instance the great Harshad Mehta
scam took place because among other things, the public debt office of the
Reserve Bank of India was not computerised and was operating on a manual
system. This gave a float of fifteen days, which gave opportunity for people like
Ketan Parekh to perpetrate the fraud. Even after this scam while in the case of
the RBI the defect was rectified the overall banking system is still manual. Only
5000 out of the 65000 branches of banks are computerised. In today's
competitive market, it is necessary that the banks are able to service their clients
effectively. Therefore strongly urge is that we should have a massive effort at
computerisation of the banks.
19
Frauds in Indian Banking Sector
Execution of Documents:
1. A bank officer must adopt a strict professional approach in the execution
of documents. The ink and the pen used for the execution must be
maintained uniformly.
2. Bank documents should not be typed on a typewriter for execution.
These should be invariably handwritten for execution.
3.
The execution should always be done in the presence of the officer
responsible for obtain them,
4. The borrowers should be asked to sign in full signatures in same style
throughout the documents.
5. Unless there is a specific requirement in the document, it should not be
got attested or witnessed as such attestation may change the character of
the instruments and the documents may subject to stamp duty.
6. The paper on which the bank documents are made should be pilfer proof.
It should be unique and available to the banks only.
7. The printing of the bank documents should have highly artistic intricate
and complex graphics.
8. The documents executed between Banker and Borrowers must be kept in
safe custody,
One issue when a fraud is perpetrated is who should be held responsible. For
instance in the case of the borrower-based accounts, there is the person who
20
Frauds in Indian Banking Sector
posts the accounts, there is the person who passes the instrument and, there is a
third person who makes the payment. It has been suggested that there must be a
method of isolating the person who makes the payment from the people who
make the posting or pass the order. The relative responsibility of the three will
have to be fixed. This is an issue that has been raised before me by one of the
Chairman of the banks. Perhaps in a programme like this we will be able to go
into such issues and evolve guidelines about what should be done so that while
the innocent is not punished, the guilty are not spared.
Another issue, which is of importance to the Indian economy. This is the
reported fear of many officers, especially in the middle levels in the banks, to
take decisions regarding dispersal of funds. As a result, there is always a
tendency to push the case upwards and the whole banking system is operating in
a sub-optimal manner. We must be able to find a solution to this. In fact, the
whole vigilance function can become an effective function for economic growth
if we are able to create an environment in which the honest are encouraged to
take the decision and the dishonest are punished quickly.
Bank frauds are the failure of the banker. It does not mean that the external
frauds do not defraud banks. But if the banker is upright and knows his job, the
task of defrauder will become extremely difficult, if not possible.
ii) External Prevention:
In the banking and financial sectors, the introduction of electronic technology
for transactions, settlement of accounts, bookkeeping and all other related
functions is now an imperative. Increasingly, whether we like it or not, all
banking transactions are going to be electronic. The thrust is on commercially
important centers, which account for 65 percent of banking business in terms of
21
Frauds in Indian Banking Sector
value. There are now a large number of fully computerized branches across the
country.
a) Appropriate controls:
The first steps in prevention of frauds in computerized systems involve setting
up of proper access controls both physical and logical. The physical protection
of Information System assets means physical control of access to computer and
network systems and the devices to which they are connected. Access to these
systems could be controlled by security guards, installation of code locks, smart
card driven door opening devices or modern biometric devices (which control
the access on the basis of certain individual characteristics such as finger-prints,
eyes retina image etc., which cannot be changed or falsified).
However, in a computerized environment, logical access controls (i.e. controls
to operating systems, data-base systems as well as application systems) play
more important role. Adequate controls over system software and data is done
by keeping a strict control over functional division of labor between all classes
of employees, keeping in mind the principle of least privilege and that maker
and checker. A clear segmentation of access to system engineers, programmers
and administrators is also done depending on their work responsibility.
Information System Auditors / Security Management must exercise a great deal
of creativity in identifying ways in which unauthorized users could gain access.
Hence, the first step in prevention of computer frauds is setting up of the
appropriate controls.
22
Frauds in Indian Banking Sector
b) Proper Implementation;
Second step in prevention of frauds would be to ensure that the users properly
implement the control systems. Control measures could be either software
driven like passwords or system driven like exception reports and transaction
authorization processes. In this connection, it may be noted that access controls
are a system in themselves and existence of such controls means existence and
maintenance of such control systems.
In the case of passwords, as access control measures. It may be noted that
merely having passwords is not sufficient. It should also be ensured that
password have been prescribed to have certain minimum characters, are stored
in encrypted files, there is a forced change of passwords at the time of first login
as well as after a specified period. These features however depend on the
security policy of the organization.
Systems are also designed to keep a chronological record of the events
occurring in the system (i.e. commands executed by the users, actions on files,
messages displayed by the system, resources consumption by the users,
transaction entry and security violations) in the form of audit trails. These can
be built in operating systems, database management systems as well as
application software. A regular analysis of audit trails as control measure helps
in containing any future loss through fraud.
However, although having good controls and maintaining them is a major step
in prevention of frauds it is still not sufficient to prevent them. Even with the
best of systems and their maintenance, all the possibilities of their misuse can
neither be predicted nor tested. Even when the best of the access controls tools
are used and monitored, when data flows from within the network through data
communication lines or from one network to another or through Internet,
23
Frauds in Indian Banking Sector
protection of the data becomes an important tool for prevention of frauds. For
this, one can either depend on simple processes like check sum or hash totals
built in the software or may require using encryption technology or
cryptography. The complexity and cost of implementation of these methods
varies a lot and is, hence, decided by the risk element.
Examples:
1) When data relating to inter-branch reconciliation flows through network
simple processes like check sum or hash totals may suffice. However, in the
case of INFINET used for Real Time Gross Settlement, which uses dial-up
connections, leased lines as well as VSAT technology for access, use of Public
Key Infrastructure (PKI) with a larger key-size is necessitated.
2) Firewalls for computer networks are another important tool in prevention of
frauds when access is allowed across networks or Internet. They are used to
enforce an access control policy across the networks. They allow only
authorized traffic to pass and prevent unauthorized access. They also protect
sensitive data and provide audit or logging information. As such they provide a
focal point for monitoring and log access to the network and thus limit exposure
of network services.
3) Present technology also makes us available what is called as Intruder
Detection Systems (IDS). IDS are systems build up to detect intruders entering
the network. It is the process of identifying and responding to malicious activity
targeted at computing and networking resources and is an important component
of defensive measures protecting computer system and networks from abuses.
There are different kinds of IDS:
i) Network Intrusion Detection Systems (NIDS) monitor packets on the
network and attempt to discover if a hacker is trying to break into a system. ii)
24
Frauds in Indian Banking Sector
System Integrity Verifiers (SIV) monitors system files to detect when an
intruder changes them and send alert.
iii) Log File Monitor (LFM) monitors log files generated by network and look
for patterns in the log files that suggest an intruder is attacking. Once the hacker
gets into the network it triggers an alarm at the same time.
As firewall acts like a fence around the network, it cannot on its own detect
somebody trying to break in. It restricts access at the designated points. IDS, on
the other hand, are intended to recognize attacks against the network that
firewall are unable to see. 80% of all the financial losses are due to hacking that
come from inside the network. Firewall cannot see anything happening inside
the network. Firewall checks for traffic which passes between internal network
and the Internet. Adding IDS will double-check miss-configured firewalls; catch
attempts that fail; catch insider hacking; record electronic evidence.
Detection of Frauds:
i) Internal detection:
25
Frauds in Indian Banking Sector
Despite all care and vigilance there may still be some frauds, though their
number, periodicity and intensity may be considerably reduced. The following
procedure would be very helpful if taken into consideration:
1. All relevant data-papers, documents etc. Should be promptly collected.
Original vouchers or other papers forming the basis of the investigation
should be kept under lock and key.
2. All persons in the bank who may be knowing something about the time,
place a modus operandi of the fraud should be examined and their
statements should be recorded.
3. The probable order of events should thereafter be reconstructed by the
officer, in his own mind.
4. It is advisable to keep the central office informed about the fraud and
further developments in regard thereto.
One method of detection will be only by regular checks and this is where
apparently there is slackness today. Ultimately we must be able to create in our
banks an atmosphere of trust on the one side and transparency on the other so
that frauds if they occur are immediately detected, checked and penalized.
Apart from the systems and procedures, ultimately the whole issue boils down
to the values we have. Today we are highly tolerant of corruption. We also have
in our Hindu philosophy the two basic principles, which seem to indirectly
encourage corruption. These are extreme tolerance and the prayaschitta
principle. As a result many people who commit frauds can literally get away
freely. Our systems are really to be blamed. As it is seen, if we make a quick
analysis of 100 people in any given organisation, 10% may be honest and 10%
dishonest whatever we do. 80% depend on the systems we have.
26
Frauds in Indian Banking Sector
And our systems encourage corruption due to the following factors:
Scarcity of goods and services
Lack of transparency
Delay and red tape
Cushions of safety that have been built for the corrupt on the healthy
principle that everybody is innocent till proved guilty. We have got
voluminous vigilance manuals and the corrupt can find always some
method of escaping punishment by exploiting some loophole or other.
This must be checked.
Do not know to what extent the bank frauds can be attributed to the people in
our own banking system that, because of loyalty of the profession or
organisation, tends to protect the corrupt. Such people may be doing a
disservice to the nation. We should therefore be able to evolve ultimately
systems which tackle the corruption promoting factors mentioned above so that
the punishment of the corrupt becomes a perceived reality and acts as a check
for people who have a tendency to commit frauds. After all that is the way for
prevention and detection of frauds.
ii) External detection:
Despite all such measures, as technology is taking rapid strides (for fraudsters
as well as organizations), system security administrators are discovering that
27
Frauds in Indian Banking Sector
they have to constantly improve upon the technological tools. However, security
can only reduce the possibility of fraud and not totally rule it out. In a
computerized environment, the perpetrators of fraud also expect their crime to
be near impossible to detect among the thousands or millions of transactions
processed by the organization. Hence to reduce the losses, timely detection of
the frauds plays an important role.
Bank computer crimes have a typical feature, the evidence relating to crime is
intangible. The evidences can be easily erased, tampered or secreted. More over
it is not easily detectable. More over the evidence connecting the criminal with
the crime is often not available. Computer crimes are different from the usual
crimes mainly because of the mode of investigation. There are no eyewitness,
no usual evidentiary clues and no documentary evidences.
It is difficult to investigate for the following reasons:
Hi-tech crime
The information technology is changing very fast. The normal investigator does
not have the proper background and knowledge .special investigators have to be
created to carry out the investigations. the FBI of USA have a cell, even in latest
scenario there has been cells operating in the Maharashtra police department to
counter cyber crimes.C.B.I also have been asked to create special team for
fighting cyber crimes.
International crime:
A computer crime may be committed in one country and the result can be in
another country. There has been lot of jurisdictional problem a though the
Interpol does help but it too has certain limitations. The different treaties and
28
Frauds in Indian Banking Sector
conventions have created obstructions in relation to tracking of cyber criminals
hiding or operation in other nations
No-scene crime:
The computer satellite computer link can be placed or located any where. The
usual crime scene is the cyber space. The terminal may be anywhere and the
criminal need not indicate the place. The only evidence a criminal leaves behind
is the loss to the crime.
Faceless crime:
The major advantage criminal has in instituting a computer crime is that there is
no personal exposure, no written documents, no signatures, no fingerprints or
voice recognition. The criminal is truly and in strict sense faceless.
There are certain spy softwares which is utilized to find out passwords and
other vital entry information to a computer system. The entry is gained through
a spam or bulk mail.
The existing enacted laws of India are not at all adequate to counter cyber
crimes. The Indian Penal code, evidence act, and criminal procedure code has
no clue about computers when they were codified. It is highly required to frame
and enact laws which would deal with those subjects which are new to the
country specially cyber law; Intellectual property right etc.
The Reserve Bank of India has come up with different proposals to make the
way easier, they have enacted electronic fund transfer act and regulations, have
amended, The Reserve Bank of India Act, Bankers Book Evidence Act etc.,
experience of India in relation to information and technology is limited and is in
a very immature state. It is very much imperative that the state should seek the
help of the experienced and developed nations.
29
Frauds in Indian Banking Sector
As the success of the fraudster depends on how fast their crime is detected
among very large number of transactions processed by the organization,
auditors and fraud investigators find that computers are their best tools for
detection of fraud. Powerful, interactive software that quickly sifts through
mountains of electronic data enables auditors to effectively detect and prevent
fraud throughout an organization. The benefit is speed.
One such tool is the General Audit Software (like ACL - Audit Command
Language and IDEA - Interactive Data Extraction & Analysis). Such tools can
quickly compare and analyze data to identify patterns and trends that often
reveal fraudulent activity.
For effectively detecting and preventing fraud, one must be able to recognize
fraud and its symptoms. Auditors have been trained to look for anomalies and a
data analysis tool can highlight anomalies quickly. However, while gathering
evidence for fraud, one will have to be little creative and examine closely any
indication of fraud, however, small. In other words, to uncover a fraud, one
must think like a thief and not as an auditor.
In fact, as such crimes can be committed by comparatively with much less
investment and gains to fraudsters may be beyond geographic boundaries.
Another way to use such software for prevention of fraud could be identifying
organizations risks and exposures and assembling fraud profiles for targeted
audits.
One should not forget that, in a computerized environment, frauds increase, as
fraudsters believe their action near impossible to detect, if detected near
impossible to prove, if proved nearly impossible to convict and if convicted,
amounts nearly impossible to recover. The problem is compounded in
networked banks operating in different nations with different laws. Despite this,
30
Frauds in Indian Banking Sector
it has been observed that frauds perpetrated from across the globe have been
detected and amounts recovered by proper combination of technology and
sleuthing skills. Hence, while security administrators continually watch
incidences and plug the holes, fraud investigators improve their skills and
actively liaise with authorities to improve the legal framework.
Relevant Measures to tackle Bank Frauds in India:
All the major operational areas in banking represent a good opportunity for
fraudsters with growing incidence being reported under deposit, loan and interbranch accounting transactions, including remittances.
Broad analyses of various frauds that have taken place throw up the following
high-risk areas in committing frauds:
Misappropriation of cash by fudging accounts.
Unauthorized withdrawal or transfers of funds, mostly from long dormant
accounts.
Opening of fictitious accounts to misappropriate funds from illegal
activities i.e. Laundering through the fictitious accounts
31
Frauds in Indian Banking Sector
Use of interbank clearing for accommodation, kite-flying and
misappropriation.
Cheating in foreign exchange transactions by flouting exchange control
provisions.
Withdrawal from deposit accounts through forged documents.
The most effective defence banks could have against fraud is to strengthen their
operational practices, procedures, controls and review systems so that all fraudprone areas are fully sanitized against internal or external breaches. However,
the huge expansion in banking transactions consequent to the transition of banks
to mass banking and the large scale computerization have played a major role in
the perpetration of the frauds. Hence mere reliance on the internal controls is of
no use. The ten fold INDIA FORENSIC approach to tackle the bank fraud
will definitely play a crucial role in coming days.
Following is the procedure to tackle frauds in banks:
1) Expect fraud:
Nowhere in the world the fraud can be avoided hence the banks can be no
exceptions. It is a human tendency of taking the risk to commit the frauds if
he finds suitable opportunities. So it is wise to expect the occurrence of the
fraud. If the fraud is expected, efforts can be concentrated on the areas,
which are fraud prone. Fraud is the game of two. The rule makers and rule
breakers. Whoever is strong in the anticipation of the situations wins the
game of frauds. Fraud is a phenomenon, which cannot be eliminated, but it
needs to be managed.
2) Develop a fraud policy:
The policy should be written and distributed to all employees, Borrowers and
depositors. This gives a moral tension to the potential Fraudster. Maintain a
32
Frauds in Indian Banking Sector
zero tolerance for violations. The Indian bank needs to roar against the action
that is taken against the Fraudsters. The media publicity against the
fraudsters at all the levels is necessary. The announcement by US president
George W. Bush that the Corporate crooks will not be spared gave the
deep impact to the Corporate America. In India also we need to consider it as
a sever problem and need to fight against it.
3) Assess Risk:
Look at the ways fraud can happen in the organization. It is very important
to study the trend and the style of frauds in the bank. Some of the big
nationalized banks maintain the databases of the fraud cases reported in their
banks. But the databases are dumb. They yield nothing unless they are
analyzed effectively. Establish regular fraud-detection procedures. It could
be in the form of internal audit or it could also be in the form of inspections.
These procedures alone discourage employees from committing fraud. In
addition to this the Institute of Chartered Accountants of India has issued an
Accounting and Assurance standard on internal controls which is a real
guideline to test internal controls. Controls break down because people affect
them, and because circumstances change.
4) Segregate duties in critical areas:
It is the absolutely basic principle of auditing a single person should not
have the control of the books of accounts and the physical asset. Because this
is the scenario which tempts the employee to commit the fraud. Hence it
becomes essential to see that no one employee should be able to initiate and
complete a critical transaction without involving someone else.
Most of the banks in India have the well-defined authorization procedures.
The allocation of the sanctioning limits is also observed in most of the cases.
33
Frauds in Indian Banking Sector
But still the bankers violate the authorities very easily. They just need to
collude with the outside parties. However the detection of the collusions is
possible in most of the cases if the higher authorities are willing to dig the
frauds.
5) Maintain the tone of Ethics at the top:
The subordinates have the tendency to follow their superiors. When the
signals are passed on to the middle management about the unethical behavior
of the top management the fear of punishment gets reduced and the tendency
of following the superior dominates. Fear vanishes when the tendency of If
I have to die Ill take along the superior and die tendency rises.
6) Review and enforce password security:
The incidences of hacking and the Phishing have troubled the Indian Private
Sector banks to a great extent. In addition to this most of the Indian banks
are running behind the ATM and credit cards to compete with each other but
have conveniently forgone the fact that ATM cards and the credit cards are
the best tools available in the hands of the fraudsters. Inappropriate system
access makes it possible to steal large amounts of money very quickly and,
in many cases, without detection. Hence the review and the enforcement of
the security policy are going to be a crucial.
7) Conduct pre-employment screening:
Since the raw material of the Banks is cash the banker needs to be more
alert than any other employer before they recruit. Only testing the aptitude of
34
Frauds in Indian Banking Sector
a person is not of any use. Know whom you are hiring. More than 20 percent
of resumes contain false statements. Most employers will only confirm dates
of employment. Some times post employment condition might create the
greed in the minds of employee, hence at least the bankers should test check
the characters of their subordinates by creating real life scenarios such as
offering the bribes by calling on some dummy borrower.
8) Screen and monitor Borrowers:
Bad borrowers cause the biggest losses to the banks. What are they? Who
they represent themselves to be? Look at their ownership, clients, references,
and litigation history. In many cases the potential fraudsters have history of
defaulting in some other bank or Financial Institution.
Though this is not the foolproof solution to the disease of the frauds to some
extent it helps to combat the frauds.
35
Frauds in Indian Banking Sector
SECURITY IN BANKING SYSTEM:
Security implies sense of safety and of freedom from danger or anxiety. When a
banker takes a collateral security, say in the form of gold or a title deed, against
the money lent by him, he has a sense of safety and of freedom from anxiety
about the possible non-payment of the loan by the borrower. These should be
communicated to all strata of the organization through appropriate means.
Before staff managers should analyze current practices. Security procedure
should be stated explicitly and agreed upon by each user in the specific
environment. Such practices ensure information security and enhance
availability. Bank security is essentially a defense against unforced attacks by
thieves, dacoits and burglars.
PHYSICAL SECURITY MEASURES-CONCEPT:
A large part of banks security depends on social security measures. Physical
security measures can be defined as those specific and special protective or
defensive measures adopted to deter, detect, delay, defend and defeat or to
perform any one or more of these functions against culpable acts, both covert
and acclamations natural events. The protective or defensive, measures adopted
involve construction, installation and deployment of structures, equipment and
persons respectively.
The following are few guidelines to check malpractices:
1. To rotate the cash work within the staff.
2. One person should not continue on the same seat for more than two
months.
3. Daybook should not be written by the Cashier where another person is
available to the job.
36
Frauds in Indian Banking Sector
4. No cash withdrawal should be allowed within passbook in case of
withdrawal by pay order.
5. The branch manager should ensure that all staff members have recorder
their presence in the attendance registrar, before starting work.
CHANGES IN LEGISLATIONS AFTER ELECTRONIC TRANSACTIONS:
1. Section 91 of IPC shall be amended to include electronic documents also.
2. Section 92 of Indian Evidence Act, 1872 shall be amended to include
commuter based communications.
3. Section 93 of Bankers Book Evidence Act, 1891 has been amended to
give legal sanctity for books of account maintained in the electronic form
by the banks.
4.
Section 94 of the Reserve Bank of India Act, 1939 shall be amended to
facilitate electronic fund transfers between the financial institutions and
the banks. A new clause has been inserted in Section 58(2).
37
Frauds in Indian Banking Sector
Customer guidelines to avoid Fraud:
The customer should keep in mind the following guidelines to prevent
themselves from any frauds.
Never give your account number to people you do not know, especially
on telephone.
Never give out financial or other personal information such as bank
account or credit card numbers unless you are sure that the company is
legitimate and the information is necessary for the transaction.
Never judge a website by its appearance. Anyone can create a flashy
website. Just because it looks professional does not mean it is run by a
professional.
Do not write your credit card number on the cheque.
Dont leave blank spaces on the payee and amount lines.
Keep changing your e-mail password frequently because it can be
hacked.
Limit the amount of personal information on your cheque. For e.g.
drivers license, telephone numbers. A criminal can use this information
by applying for credit card or loan, opening a new account.
Dont send any personal information to any e-mail ID this can lead
phising.
Thus above are some the measures that the customer should undertake to
avoid any type of bank frauds.
38
Frauds in Indian Banking Sector
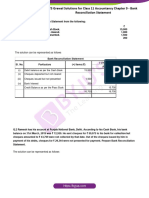
Bank Frauds Statistics in India:
Year
2002
2003
2004
Loss in
Rs.Crores
399.53 Cr.
653.5 Cr
600.16 Cr.
Fraud Cases
1744
2207
2663
A survey On Frauds:
Highlights of the first annual survey published by India forensic Research
Foundation. This study was carried out in the period of August'2006 and
February'2007. This is the first independent and privately funded study
carried out in India on the banking sector frauds.400 participants contributed
their valuable views on this subject.
Total fraud loss to Indian Banks in year 2005- 06 was Rs. 1381 crores
according to the report published by Reserve Bank of India.
Existence of the internal controls is still the methodology in India to
catch the frauds.
Collusion of the borrowers and the employees is the biggest cause of
the bank frauds.
39
Frauds in Indian Banking Sector
At least Rs.690 crores worth of frauds are known to the banks but are
not reported to various authorities for reasons like unclear definition
of word frauds, damage to the banks image etc.
Technology related frauds like (ATM Card, Debit card, Credit card)
are expected to be going un-exposed on the vast proportion.
Estimated minimum loss to the banking industry because of the
unknown frauds could be more than Rs.828 crores.
Total impact of frauds on banking revenues = 1.7% of the total
consolidated revenues of the banks are lost to frauds.
Money laundering is considered to be the risk of frauds in future.
Educating the bank employees is the most effective way to prevent the
bank frauds.
40
Frauds in Indian Banking Sector
Case Studies
1) Supposed ATM Fraud
Saturday, August 13, 2005
I did some snooping around the internet and found that even though this kind of
ATM fraud those occur there has been no indication that this is prevailant in
India or Pune for a matter of fact
Therefore the letter was either a warning from ICICI Bank to it's customers or
an attempt by someone to spread rumours or create a popular email forward.
Since no such warning is listed on the ICICI Bank website I would think it's the
latter.
A team of organized criminals are installing equipment on legitimate bank
ATM's in at least 2 regions to steal both the ATM card number and the PIN. The
team sits nearby in a car receiving the information transmitted wirelessly over
weekends and evenings from equipment they install on the front of the ATM.
If you see an attachment, do not use the ATM and report it, immediately to the
bank using the 800 number or phone on the front of the ATM.
The equipment used to capture your ATM card number and PIN are cleverly
disguised to look like normal ATM equipment. A "skimmer" is mounted to the
front of the normal ATM card slot that reads the ATM card number and
transmits
it
to
the
criminals
41
sitting
in
nearby
car.
Frauds in Indian Banking Sector
The thieves copy the cards and use the PIN numbers to withdraw thousands
from many accounts in a very short time directly from the bank ATM.
Equipment
being
installed
on
front
42
of
existing
bank
card
slot.
Frauds in Indian Banking Sector
The equipment as it appears installed over the normal ATM bank slot.
At the same time, a wireless camera is disguised to look like a leaflet holder and
is
mounted
in
position
to
view
ATM
PIN
entries.
Suprisingly this happens only in Pune for some reason. Pune India's high tech
crime capital.
43
Frauds in Indian Banking Sector
W E D N E S D A Y, D E C E M B E R 2 6 , 2 0 0 7 ,
SOURCE TIMES OF INDIA
Card crooks tap into data wires:
First, it was skimmers. Now, credit card crooks in Kolkata may be getting more
tech savvy, using wire-tapping gadgets to cash in on unsuspecting card users.
It's a new cause of worry for city police and CID. Wire-tapping is a complicated
scheme and much more difficult to track down. It's a technical maze that
involves telephone wires, receiving-terminals and a cable line parallel with
telephone cables to copy the card details when it is swiped for a transaction.
The first time that the city police got an inkling of fake credit card rackets in
Kolkata was when three Bangladeshis were arrested for using a card whose
owner was in Singapore.
44
Frauds in Indian Banking Sector
Wire-tapping is the most likely method, they now say. Though they have not
identified a racket as yet, cyber sleuths are sure the card racketeers are running a
hi-tech operation in the city. Their suspicions were strengthened when a private
bank recently held a workshop for CID to discuss fraud techniques.
"We haven't got any case where wire-tapping was used to dupe somebody but
we are sure the racketeers are out there. We are trying to find the right technique
to detect such crimes and also adopting safe-guard measures," said a senior CID
officer.
Wiretapping works in three phases. The first phase involves tapping into the
wires of the main server to capture card data as it is processed for a legitimate
transaction. The next step is to transfer the encoded data to another server, at the
fraudster's end, where it is decoded. In the last phase, the data is used to produce
counterfeit cards. The technology is definitely more complicated than a
skimmer - a gadget which copies the details of a card from a measured distance.
In advanced countries, encrypted cables are installed to prevent telephone wire
tapping but awareness is low in India.
"The cable linking the electronic data capturing machine (EDC) and the
distribution point box is a very sensitive area which is targeted by the
racketeers. When the card is swiped on the EDC, the machine records the
financial data in the card's magnetic strip and feeds it to the DP box, from where
it moves to the main server of the telephone service provider and is finally
transferred to the servers of banks where the transaction is recorded. The
hackers target the area between the EDC and the DP box, tap into the wires,
steal data and send it to another server," said an anti-fraud officer of a private
bank.
45
Frauds in Indian Banking Sector
Police officers say it is difficult to trace such rackets. "For the first phase, the
fraudsters need only a map of the telephone wiring, a receiving terminal and
cables matching the ones used by the telephone service provider. These are not
very difficult to manage and anybody who has a flair for technology can use it
to store the data. High-end technology comes in the next level," said an officer.
Police suspect card fraudsters in Kolkata could be using the technology to copy
the data and send it to other cities in India and abroad. They have a good reason
to suspect this. In the last one year, such units have been busted in Delhi, Jaipur
and Hyderabad. "We heard about it and are looking for effective measures to
prevent wire-tapping," said Jawed Shamim, deputy commissioner, detective
department. Kolkata Police could also take tips from south-east Asian countries
like Thailand and Philippines, where such rackets are active and where law
enforcement agencies have more experience in handling such crimes.
PNB Official involved in Bank Fraud of Rs. 2 Lakh
July 14, 2008
The cases of credit card frauds do not seem to end. Following the recent case of
an ING Vysya Bank employee, in partnership with others, duping the bank of
crores, a case has been registered against a Punjab National Bank (PNB) in
Chandigarh. Baldev Singh, who works as a cashier-cum-computer operator in
the Kurali branch of PNB, has been remanded to police custody because of
duping the bank to an amount of Rs 2 lakh. According to the investigating
officer, Ravindar Pal Singh, the accused had first defrauded the bank of Rs 1.87
46
Frauds in Indian Banking Sector
lakh; however, after he was caught, he duped 2 more customers to the tune of
Rs 1.1 lakh to clear the banks liability.
The case had come to the Kurali police when the head of PNB,
Chandigarh Circle, had lodged a complaint against Baldev on March 10. That
day the bank had given Rs 8 lakh in cash to Baldev Singh to disburse payments
as cashier-cum-computer operator. However, he had disbursed Rs 6, 12,700 but
failed to deposit back the remaining amount of Rs 1, 87,300.
After the bank authorities had initiated an enquiry against the accused, he
committed to the crime and agreed to pay back the defrauded cash.
However, on March 15, he once again siphoned off Rs 1, 00,500 from the
account of a customer, Balveer Singh. Further enquiry also revealed that he had
duped another customer, Beant Singh, of Rs 10,000 as he withdrew Rs 15,000
from Beants account when the latter had come to withdraw Rs 5,000.
UTI Bank: Phishing Fraud:
Recent fraudulent transactions through phishing resulted in loss of over Rs
20 lakh for a customers.
Friday, June 08, 2007
The Economic Offences Wing, Crime Branch, Delhi Police, received a
complaint from the vice president, Operations, UTI Bank that many customers
of various UTI banks in Delhi, Vishakapatnam, Thane, Nasik, and Ahmedabad
received emails claiming to have originated from the bank.
These emails included a hyperlink within the email itself, and a click on the link
took the recipients to a Web page, which was identical to UTI's Web page. Some
unsuspecting recipients responded to these mails, and gave their login
47
Frauds in Indian Banking Sector
information and passwords. Later on, through Internet banking, a large number
of fraudulent transactions took place. These transactions resulted in loss of over
Rs 20 lakh for customers with bank accounts in Delhi, Vishakapatnam, Thane,
Nasik, and Ahmedabad.
An analysis on those phishing mails revealed that they had originated from
somewhere in Lagos, Nigeria. The UTI phishing site had lifted the UTI logo as
well as the Iconnect symbol from the original UTI site in order to make the fake
site look real. The fake site provided a 'click here' option, which in turn took
victims to a fake customer verification site based in Austria. IP addresses of the
fraudulent transactions indicated transactions had been made from Nigeria,
Atlanta and California.
Investigations:
Upon a complaint of the vice president, UTI Bank, a case registered and taken
up for investigation by a special team. Investigations revealed that Sanjit
Chowdhary, Account No 111010100023959 with UTI Bank, Noida, had
received a disputed credit entry totaling Rs 1.3 lakh through Internet banking
from the account of Lakshmi Narayan Sarkar of Kolkata, who has an account at
UTI Bank, Salt Lake, Kolkota, and from the account of Makaran H Pundalik,
who has an account with the Standard Chartered Bank, Delhi.
It was further revealed that the misappropriated funds had been transferred in
the account of accused Sanjit Chowdhary. The police team laid a trap at UTI
Bank in Noida and the accused Sanjit Chowdhary, who came to the branch to
make enquiries regarding the inactive status of his account, was arrested on
December 7, 2006.On being interrogated, the accused disclosed that he had
48
Frauds in Indian Banking Sector
received money in his bank account consequent to phishing mails sent to
various customers of UTI Bank. Various transaction slips pertaining to the UTI
Bank and ICICI Bank were recovered from his possession. A scrutiny of these
slips revealed that Sanjit Chowdhary had withdrawn funds and deposited the
same in accounts of his other associates, who had accounts in UTI and ICICI
Bank at Mumbai and Trichy.
Till December 2006, a total of twenty complainants had registered their
complaints. All the six beneficiary accounts are in Delhi for these twenty
complainants. Further, ten complaints had been received by UTI branches in
Vishakapatnam, Ahmedabad, Nasik, and Thane, where the beneficiary accounts
are being maintained. An analysis of the accounts of the four arrested Nigerian
nationals revealed that financial transactions worth over Rs 1 crore took place in
an eight-month period.
.Survey Report
Findings:
According the survey conducted by me most of the customers know about bank
frauds. They have a computational idea of frauds taking place in banks.
There are very few, those are not aware of bank frauds.
49
Frauds in Indian Banking Sector
The survey also revealed the types of bank frauds that the customers know
about. The survey included ATM Fraud, Credit card fraud and Online fraud.
The following is the graph revealed:
Due to computerization banks facilities have increased. There has been increase
in frauds also. The following Graph shows the survey on frauds increased or
decreased due to computerization.
Following survey shows the number of customers those have experienced the
frauds in banks either through banks or by others.
50
Frauds in Indian Banking Sector
The suggestions that the survey reveal is that there must be some strict actions
take against the fraudsters. Banks should provide the necessary information
regarding the frauds that the customers can come across. Awareness among the
customers regarding frauds is must.
Conclusion:
The Indian Banking Industry has undergone tremendous growth since
nationalization of 14 banks in the year 1969. There has an almost eight times
increase in the bank branches from about 8000 during 1969 to mote than 60,000
belonging to 289 commercial banks, of which 66 banks are in private sector.
However, with the spread of banking and banks, frauds have been on a constant
increase. It could be a natural corollary to increase in the number of customers
who are using banks these days. In the year 2000 alone we have lost Rs 673
crores in as many as 3,072 number of fraud cases. These are only reported
figures. There were nearly 65,800 bank branches of a total of 295 commercial
banks in India as on June 30, 2001 reporting a total of nearly 3,072 bank fraud
cases.
51
Frauds in Indian Banking Sector
The most important feature of Bank frauds is that ordinarily they do not involve
an individual direct victim. They are punishable because they harm the whole
society. It is clear that money involved in Bank belongs to public.
There must be certain preventive and curative measures to control frauds. The
higher authority of bank must follow strict rules against such fraudsters. The
various new technologies must be adapted by the bank to overcome such frauds.
Thus, a fraud is the game of two, the rule makers and the rule breakers. Fraud is
a phenomenon that cannot be eliminated but can be managed.
ANNEXURES
Questionnaires:
To Understand Frauds in Indian Banking Sector, their prevention and detection
and security against them I visited two different banks:
i) ICICI BANK
ii) AXIS BANK they spared some of their valuable time to
explain in brief about the various mechanics of fraud and their prevention and
answered to some of my questions.
ICICI BANK:
52
Frauds in Indian Banking Sector
1) What are the major types of frauds conducted?
Phising, Forgery altered cheques, fraudulent loans application.
2) What are the general preventive measures taken?
There is a department which looks after fraud and their prevention i.e.
Risk Content Unit (RCU). They go through the fraud conducted and take
necessary steps. Know Your Customer (KYC) is an important tool to prevent
frauds in banks.
3) Do you think that computerization have increased frauds? Why?
No. Because due to computers there has been increase in work. A work
which would take 3hrs is done in 1 1/2hrs, thus providing better service. More
over out of entire customers 2% conduct frauds. Because of this 2%, we cant
avoid providing better services to 98% customers.
4) Effect of fraud on banks?
The customers are affected. The banks reputation is shattered. Many
customers try to avoid the bank branch. Negative views are spread to the
customers.
AXIS BANK:
1) What are types of frauds you have come across?
Property mortgaging in different bank with the help of duplicate
document, Money laundering, credit card fraud, Debit card fraud, DD fraud Bill
discounting fraud.
2) What are the measures taken against frauds?
i) Core Banking Solutions (EXEL report) to find out fraud.
ii) Know the Introducer while opening the account
53
Frauds in Indian Banking Sector
iii) Account should not be opened those coming with DD, Cheques.
iv) Internal Checkings
3) What are the steps taken after the fraud is detected?
Several steps are taken:
In case of Accounts fraud higher authority is reported.
In case of cash authority is consulted and if necessary FIR is registered.
4) How a customer can be made aware the frauds they can come across?
Customers are asset to the banking company. They can be made aware
through E-mails, Advertisements, Posters, etc.
`5) Which frauds are more conducted Internal or by others?
Most of the frauds conducted are by others. Whereas, internal fraud can be
controlled through strict supervision, daily check of the documents, etc.
External frauds are threat to the public as well as banks.
SURVEY FORM
SHRI CHINAI COLLEGE OF COMMERCE AND ECONOMIC
NAME: CONTACT NO: -
AGE:-
Survey for Project on Frauds in Indian Banking Sector
1) Do you know about Bank Frauds?
Yes
No
2) Are you aware of any of the following type of fraud?
ATM fraud
All of the above
Credit Card Fraud
Online Bank Fraud
None of the above
54
Frauds in Indian Banking Sector
3) Do you think Frauds have increased due to online technology?
Yes
No
4) If Yes/ No Why?
5) Have you come across any bank frauds?
Yes
No
6) If yes, which fraud and through which bank?
Suggestions if any:-
Project Guide:Urmila
By:
Signature- ___________
Niddhi K Lakhani
TyBBI Roll no. 24.
ICICI Bank {SAFE BANKING}
We are committed to make your banking with us a safe and wonderful
experience. The guidelines we have set out are simple steps you can take to
ensure that your money is safe and secure. This initiative has been taken us in
form of the Safe Banking campaign, which has been running across media
Print, T.V., online, and outdoor.
55
Frauds in Indian Banking Sector
While you may not have fallen prey to any of them, thankfully, its our
responsibility to make you aware of them so that you are alert of how to protect
your money.
56
Frauds in Indian Banking Sector
57
Frauds in Indian Banking Sector
PROTECT YOUR ACCOUNT:
IF you are using Internet Banking or any other online account, please
read below on how to protect your account.
Never respond to e-mails that request personal information.
Keep your password top secret and change them often.
Make your password difficult to crack.
Never use cyber caf to asses your online accounts.
Keep your computer secure.
Check the website youre visiting is secure.
Validate SSL certificate.
58
Frauds in Indian Banking Sector
BIBLOGRAPHY
www.google.co.in
www.yahoo.com
www.fraudsinindianbankingsector.com
www.icicibank.com
www.axisbank.com
59
Anda mungkin juga menyukai
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- Credit Card HackingDokumen2 halamanCredit Card Hackingmadarauchiha50% (2)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- Test Bank For Personal Finance 5 e 5th Edition Jeff MaduraDokumen22 halamanTest Bank For Personal Finance 5 e 5th Edition Jeff Madurathomasburgessptrsoigxdk100% (20)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- Downloaded DocumentDokumen7 halamanDownloaded DocumentStacie GlanceBelum ada peringkat
- Allen Wu: March 15 - March 31, 2021Dokumen4 halamanAllen Wu: March 15 - March 31, 2021Brandie HamptomBelum ada peringkat
- Rebuttals 5.3Dokumen10 halamanRebuttals 5.3Andrés FlórezBelum ada peringkat
- Bar Ops 2 - 8TH Wave Case DigestsDokumen20 halamanBar Ops 2 - 8TH Wave Case DigestsShane Fernandez JardinicoBelum ada peringkat
- Oracle R12 Payments White PaperDokumen11 halamanOracle R12 Payments White PaperjayapavanBelum ada peringkat
- Table of Contents - Chapter 12: Accounts ReceivableDokumen41 halamanTable of Contents - Chapter 12: Accounts ReceivableMissy MarieBelum ada peringkat
- The Lakeside CompanyDokumen9 halamanThe Lakeside CompanyJULIA CHRIS ROMEROBelum ada peringkat
- KotakDokumen2 halamanKotakHarsh wadhwaBelum ada peringkat
- Blinn College Summ2011 Course ScheduleDokumen62 halamanBlinn College Summ2011 Course ScheduleracinphilBelum ada peringkat
- Strategies To Pay Off DebtDokumen7 halamanStrategies To Pay Off Debtsantiago CanadaBelum ada peringkat
- 2023 CashbackDokumen5 halaman2023 Cashbackrk_mbdBelum ada peringkat
- Ts Grewal Solutions For Class 11 Accountancy Chapter 9 BankDokumen34 halamanTs Grewal Solutions For Class 11 Accountancy Chapter 9 Bankmyankjindal9Belum ada peringkat
- Dutch-Bangla Internet BankingDokumen2 halamanDutch-Bangla Internet BankingMD TARIQUL ALAMBelum ada peringkat
- 2024 21 2 21 47 56 Passbookstmt - 1708532276443Dokumen7 halaman2024 21 2 21 47 56 Passbookstmt - 1708532276443sheeladevi1951Belum ada peringkat
- Animal Thematic 1852 - 2011: Tony BrayDokumen227 halamanAnimal Thematic 1852 - 2011: Tony Braydeepheat_008Belum ada peringkat
- City Bank PresentationDokumen44 halamanCity Bank PresentationAtif ChowdryBelum ada peringkat
- Jimma University Jimma Institute of Technology School OF ComputingDokumen22 halamanJimma University Jimma Institute of Technology School OF ComputingDerara UmetaBelum ada peringkat
- Debt DestroyersDokumen2 halamanDebt DestroyersMark WatneyBelum ada peringkat
- Mail SCRPDokumen2 halamanMail SCRPNOR atifah Binti shahimiBelum ada peringkat
- Similarly God Won't Give Problems Without SolutionsDokumen43 halamanSimilarly God Won't Give Problems Without Solutionsrh_rathodBelum ada peringkat
- Final InstructionsDokumen20 halamanFinal Instructionsjanardhan reddyBelum ada peringkat
- Test Case Document Swiggy PaymentDokumen5 halamanTest Case Document Swiggy Paymentsrimaya.mayaBelum ada peringkat
- Borrower Nightmares: Navy Pension Signed Over As Collateral For Costly Quick CashDokumen7 halamanBorrower Nightmares: Navy Pension Signed Over As Collateral For Costly Quick CashSimply Debt SolutionsBelum ada peringkat
- Chapter 7 BE EX SolutionsDokumen30 halamanChapter 7 BE EX SolutionsThu Ngan NguyenBelum ada peringkat
- KK Bank StatementDokumen5 halamanKK Bank Statementsunil jadhavBelum ada peringkat
- ASKARI COMMERCIAL BANK Internship ReportDokumen179 halamanASKARI COMMERCIAL BANK Internship Reportqaiser mehmood68% (19)
- Thai Behavior About Using E-WalletDokumen58 halamanThai Behavior About Using E-WalletHoward HuyBelum ada peringkat
- Panjab University, ChandigarhDokumen24 halamanPanjab University, ChandigarhSayantanBelum ada peringkat