#280 BBB 04-29-10 128
Diunggah oleh
bmoak0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
8 tayangan1 halamanScammers lurk on auction sites offering deals that appear too good to be true. ''Keylogging'' Passworo Charity ''phishing'': e mail messages are credit card iofonnation and then sent from the user's e mail account to their entire donor identities. "Ransomware'': these contain links that auto matically install malware on mers act as virtual kidnappers computers to steal personal by hijacking computer files and encrypting them
Deskripsi Asli:
Hak Cipta
© Attribution Non-Commercial (BY-NC)
Format Tersedia
PDF, TXT atau baca online dari Scribd
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniScammers lurk on auction sites offering deals that appear too good to be true. ''Keylogging'' Passworo Charity ''phishing'': e mail messages are credit card iofonnation and then sent from the user's e mail account to their entire donor identities. "Ransomware'': these contain links that auto matically install malware on mers act as virtual kidnappers computers to steal personal by hijacking computer files and encrypting them
Hak Cipta:
Attribution Non-Commercial (BY-NC)
Format Tersedia
Unduh sebagai PDF, TXT atau baca online dari Scribd
0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
8 tayangan1 halaman#280 BBB 04-29-10 128
Diunggah oleh
bmoakScammers lurk on auction sites offering deals that appear too good to be true. ''Keylogging'' Passworo Charity ''phishing'': e mail messages are credit card iofonnation and then sent from the user's e mail account to their entire donor identities. "Ransomware'': these contain links that auto matically install malware on mers act as virtual kidnappers computers to steal personal by hijacking computer files and encrypting them
Hak Cipta:
Attribution Non-Commercial (BY-NC)
Format Tersedia
Unduh sebagai PDF, TXT atau baca online dari Scribd
Anda di halaman 1dari 1
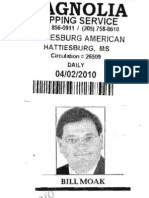
MAGNOLIA
CLIPPING SERVICE
(601) 856·0911 I (205) 758·8610
SUN SENTINEL
CHARLESTON, MS
Circulation = 2442
WEEKLY
04/01/2010
1111111111111111111111111111111111111
Be aware ofonline
scamming threats
Special , ~~ Sun-Sentinel riever receive any employ
ment offers.
RIDGELAND- The Bet ~.~ Auction Sites: Scammers
ter Business Bureau (BBB) lurk on auction sites offering
Serving Mississippi ofiefs tfie deals that appear too gOQd to
following cyber scam warn be true. Often these purchases
ings: never reach the purchasers:.
• Charity ''Phishing'': E • "Keylogging" Passworo
mail messages from' what Stealing: Thieves use low
appear to be legitimate chari cost tools to uncover pass
table organizations. These words by using malware that
contain Web sites that are records keystrokes. Com
designed to steal donations, monly, spam messages are
credit card iofonnation and then sent from the user's e
donor identities. mail account to their entire
• Fake Invoices: Bogus contact list/address book.
invoices and delivery notifi • E-mail Banking: Fake
cations sent via e-mail official-looking e-mail mes
requesting credit card iofor sages are sent from financial
mation or opening an online institutions that ask for verifi
invoice to pay for shipment. cation of account ioforma
• Social Networking tion. They further threaten to
"Friending": ''New Friend make accounts invalid if the
Request" E-mails are sent consumer does not furnish the
from social networking sites. requested iofonuation.
These contain links that auto • ''Ransomware'': Scam-'
matically install malware on mers act as virtual kidnappers
computers to steal personal by hijacking computer files
iofonuation. and encrypting them so that
• Job Searches: High-pay they become unreadable
ing jobs and work-from and/or inaccessible. They
home opportunities are then hold the files ransom by
offered. Interestedjob seekers demanding payment in
submit their infonnation and exchange for the return of the
pay their set-up fees and then flles.
Anda mungkin juga menyukai
- What Is CybercrimeDokumen5 halamanWhat Is CybercrimeJusnisalBelum ada peringkat
- Data security and protection from internet fraud and phishingDokumen8 halamanData security and protection from internet fraud and phishingsmaniya5707Belum ada peringkat
- SCAM Presentation 010216.Ppt Read OnlyDokumen16 halamanSCAM Presentation 010216.Ppt Read OnlyBhaktiBelum ada peringkat
- Fraud Email and Social Media PresentationDokumen34 halamanFraud Email and Social Media PresentationRogel CabatinBelum ada peringkat
- WARNING: Internet Scams Can APPEAR Very Genuine, and They Can Fool Almost Anyone !Dokumen10 halamanWARNING: Internet Scams Can APPEAR Very Genuine, and They Can Fool Almost Anyone !Adi ProphecyBelum ada peringkat
- Etc PresentationDokumen19 halamanEtc PresentationyasinBelum ada peringkat
- Little Black Book of Scams - Pocket-Sized GuideDokumen38 halamanLittle Black Book of Scams - Pocket-Sized Guidefarai mokinaBelum ada peringkat
- Internet Fraud DocuDokumen3 halamanInternet Fraud DocuCristian PalorBelum ada peringkat
- ICO $4 Billion Phishing Scam: Divya Kumari Ankita Ranjane Sandhya Mishra Ankit Kumar Yadav Kushal Kadam Ani KhanDokumen14 halamanICO $4 Billion Phishing Scam: Divya Kumari Ankita Ranjane Sandhya Mishra Ankit Kumar Yadav Kushal Kadam Ani KhansandhyaBelum ada peringkat
- Onlinescamsfrauds 150408064645 Conversion Gate01Dokumen35 halamanOnlinescamsfrauds 150408064645 Conversion Gate01Ever MontoyaBelum ada peringkat
- Banking Fraud PresentationDokumen14 halamanBanking Fraud PresentationPRANAY DUBEYBelum ada peringkat
- Types of Cyber Frauds and Evolution of Fraud Techniques Over TimeDokumen45 halamanTypes of Cyber Frauds and Evolution of Fraud Techniques Over TimeRESHMI J URK19ISD011Belum ada peringkat
- FraudDokumen35 halamanFraudparkerroach21Belum ada peringkat
- NCSAM Cyberattack Awareness InfographicDokumen1 halamanNCSAM Cyberattack Awareness Infographicagp agpBelum ada peringkat
- Online ScamsDokumen41 halamanOnline Scamsremisisdulawan22Belum ada peringkat
- Presented By:: Rupali Nayak and Swetalina Mohanty Under Guidance: K.K. AcharyaDokumen18 halamanPresented By:: Rupali Nayak and Swetalina Mohanty Under Guidance: K.K. Acharyanur atyraBelum ada peringkat
- 3 Dangerous Internet Scams and How To Avoid ThemDokumen2 halaman3 Dangerous Internet Scams and How To Avoid Themaarticle12Belum ada peringkat
- Identity Theft WebquestDokumen2 halamanIdentity Theft Webquestapi-256439838Belum ada peringkat
- How to Avoid Phishing ScamsDokumen21 halamanHow to Avoid Phishing ScamsGoofykiller2003 2033Belum ada peringkat
- Budol AlertDokumen3 halamanBudol AlertEDUKALIDAD ACAD COMMISSIONBelum ada peringkat
- Project Viva 2Dokumen53 halamanProject Viva 2Nidhi DasBelum ada peringkat
- Banking Ombudsman - Quick Guides 2Dokumen5 halamanBanking Ombudsman - Quick Guides 2atty_denise_uyBelum ada peringkat
- Unit 2 - Cyber SecurityDokumen9 halamanUnit 2 - Cyber SecurityPradmohan Singh TomarBelum ada peringkat
- Reading 2 - Digital and Online Banking FraudsDokumen20 halamanReading 2 - Digital and Online Banking Fraudsxayog34575Belum ada peringkat
- Cyber Money Laundering PDFDokumen19 halamanCyber Money Laundering PDFjatin sanehiBelum ada peringkat
- The Lazy Person's Guide To Internet Hoaxes, Myths and LegendsDokumen5 halamanThe Lazy Person's Guide To Internet Hoaxes, Myths and LegendsErick NuescaBelum ada peringkat
- Identity Theft WebquestDokumen2 halamanIdentity Theft Webquestapi-256416574Belum ada peringkat
- Most Used Internet ScamsDokumen11 halamanMost Used Internet ScamsD Abdi Ali100% (1)
- LK Fraud Awareness PDFDokumen3 halamanLK Fraud Awareness PDFCaine RodrigoBelum ada peringkat
- Protect Yourself from Phishing Scams with These TipsDokumen14 halamanProtect Yourself from Phishing Scams with These TipsEury GonzalezBelum ada peringkat
- Phishing, Spoofing, Spamming and Security: How To Protect YourselfDokumen14 halamanPhishing, Spoofing, Spamming and Security: How To Protect Yourselfraed messaoudiBelum ada peringkat
- VishingDokumen10 halamanVishingvinayaartalaBelum ada peringkat
- Online FraudDokumen14 halamanOnline FraudSiddu HalashettiBelum ada peringkat
- #280 BBB 01-28-10 82Dokumen1 halaman#280 BBB 01-28-10 82bmoakBelum ada peringkat
- Phishing - MKDokumen27 halamanPhishing - MKManish KumarBelum ada peringkat
- Phishing PDDokumen22 halamanPhishing PDAyush DargarBelum ada peringkat
- Financial Identity Theft: Understanding the Risks and How to Protect YourselfDokumen20 halamanFinancial Identity Theft: Understanding the Risks and How to Protect YourselfMECHERAK THANINABelum ada peringkat
- Fraud Know It Before It Knows You PDFDokumen2 halamanFraud Know It Before It Knows You PDFKarthikBelum ada peringkat
- #280 BBB 01-22-09 6Dokumen1 halaman#280 BBB 01-22-09 6bmoakBelum ada peringkat
- Online Dating ScamsDokumen1 halamanOnline Dating ScamsJessicaBelum ada peringkat
- January 2021 Newsletter: Fraud & Tax Scam PreventionDokumen3 halamanJanuary 2021 Newsletter: Fraud & Tax Scam PreventionWestSeattleBlogBelum ada peringkat
- Identity Theft WebquestDokumen2 halamanIdentity Theft Webquestapi-256417191Belum ada peringkat
- Risks and Frauds in Online Banking: Project ReportDokumen14 halamanRisks and Frauds in Online Banking: Project ReportklhthBelum ada peringkat
- What is Cyber CrimeDokumen11 halamanWhat is Cyber Crimecsk_0220Belum ada peringkat
- 12-11-08 - Leland Progress - Leland, MSDokumen1 halaman12-11-08 - Leland Progress - Leland, MSbmoakBelum ada peringkat
- Identity Theft WebquestDokumen2 halamanIdentity Theft Webquestapi-256424548Belum ada peringkat
- FraudDokumen29 halamanFraudRufino Gerard MorenoBelum ada peringkat
- Fraud PD&D ConsolidatedDokumen106 halamanFraud PD&D ConsolidatedWilliam Andrew Gutiera BulaqueñaBelum ada peringkat
- Financial Abuse Presentation Final VersionDokumen38 halamanFinancial Abuse Presentation Final VersionNeil Villas100% (1)
- It Pays To Stop and Think: Protect Yourself From Financial FraudDokumen5 halamanIt Pays To Stop and Think: Protect Yourself From Financial FraudHamza AbbasBelum ada peringkat
- Shopping Fraud - G2Dokumen16 halamanShopping Fraud - G2Mohit Prakash SrivastavaBelum ada peringkat
- Advance Fee Fraud SchemesDokumen6 halamanAdvance Fee Fraud Schemeshouessiononfiace468Belum ada peringkat
- Scammers Faked Hundreds of Charity Websites For UkraineDokumen6 halamanScammers Faked Hundreds of Charity Websites For UkraineWajeeha ShahnawazBelum ada peringkat
- 10 Most Common Types of ScamDokumen11 halaman10 Most Common Types of ScamAmer Talastasin100% (1)
- Fraud and Scam - Consumer ProtectionDokumen9 halamanFraud and Scam - Consumer ProtectionClarisse EsporlasBelum ada peringkat
- #280 BBB 10-29-09 111Dokumen1 halaman#280 BBB 10-29-09 111bmoakBelum ada peringkat
- Fraud Cases in ItiDokumen11 halamanFraud Cases in ItiDEVAVRAT SINGHBelum ada peringkat
- Loan Scam Using A Mississippi AddressDokumen1 halamanLoan Scam Using A Mississippi AddressbmoakBelum ada peringkat
- BBB Welcomes Chad Redding Insurance Agency, LLC/ AllstateDokumen1 halamanBBB Welcomes Chad Redding Insurance Agency, LLC/ AllstatebmoakBelum ada peringkat
- SAT Prep Company Stops Claiming Big Point BoostDokumen1 halamanSAT Prep Company Stops Claiming Big Point BoostbmoakBelum ada peringkat
- Nirvana Health, PLLC, Herrington Chiropractic Accredited by BBBDokumen1 halamanNirvana Health, PLLC, Herrington Chiropractic Accredited by BBBbmoakBelum ada peringkat
- BBB Census Alert: Know The FactsDokumen1 halamanBBB Census Alert: Know The FactsbmoakBelum ada peringkat
- BBB Consumer Alert: Select Account Passwords CarefullyDokumen1 halamanBBB Consumer Alert: Select Account Passwords CarefullybmoakBelum ada peringkat
- Use Caution While Participating in Ongoing 2010 National CensusDokumen1 halamanUse Caution While Participating in Ongoing 2010 National CensusbmoakBelum ada peringkat
- Parents, Don't Let Children Run Wild On Social Networking Internet SitesDokumen1 halamanParents, Don't Let Children Run Wild On Social Networking Internet SitesbmoakBelum ada peringkat
- BBB Welcomes Cherokee KennelsDokumen1 halamanBBB Welcomes Cherokee KennelsbmoakBelum ada peringkat
- Shipping Scams Exposed by AGDokumen1 halamanShipping Scams Exposed by AGbmoakBelum ada peringkat
- #280 BBB 04-29-10 58Dokumen1 halaman#280 BBB 04-29-10 58bmoakBelum ada peringkat
- Five Steps To Protect Your Business in Online BankingDokumen1 halamanFive Steps To Protect Your Business in Online BankingbmoakBelum ada peringkat
- Advance Fee Loan Scam Using Mississippi AddressDokumen1 halamanAdvance Fee Loan Scam Using Mississippi AddressbmoakBelum ada peringkat
- BBB Census Alert - Know The FactsDokumen1 halamanBBB Census Alert - Know The FactsbmoakBelum ada peringkat
- BBB Census Alert: Know The FactsDokumen1 halamanBBB Census Alert: Know The FactsbmoakBelum ada peringkat
- #280 BBB 04-29-10 93Dokumen1 halaman#280 BBB 04-29-10 93bmoakBelum ada peringkat
- #280 BBB 04-29-10 95Dokumen1 halaman#280 BBB 04-29-10 95bmoakBelum ada peringkat
- #280 BBB 04-29-10 82Dokumen1 halaman#280 BBB 04-29-10 82bmoakBelum ada peringkat
- #280 BBB 04-29-10 94Dokumen1 halaman#280 BBB 04-29-10 94bmoakBelum ada peringkat
- #280 BBB 04-29-10 129Dokumen1 halaman#280 BBB 04-29-10 129bmoakBelum ada peringkat
- #280 BBB 04-29-10 128Dokumen1 halaman#280 BBB 04-29-10 128bmoakBelum ada peringkat
- #280 BBB 04-29-10 104Dokumen1 halaman#280 BBB 04-29-10 104bmoakBelum ada peringkat
- #280 BBB 04-29-10 143Dokumen1 halaman#280 BBB 04-29-10 143bmoakBelum ada peringkat
- BBB Offers Checklist Response To Charity Telemarketing StateDokumen1 halamanBBB Offers Checklist Response To Charity Telemarketing StatebmoakBelum ada peringkat
- #280 BBB 04-29-10 164Dokumen1 halaman#280 BBB 04-29-10 164bmoakBelum ada peringkat
- #280 BBB 04-29-10 155Dokumen1 halaman#280 BBB 04-29-10 155bmoakBelum ada peringkat
- #280 BBB 04-29-10 144Dokumen1 halaman#280 BBB 04-29-10 144bmoakBelum ada peringkat
- #280 BBB 04-29-10 145Dokumen1 halaman#280 BBB 04-29-10 145bmoakBelum ada peringkat
- #280 BBB 04-29-10 177Dokumen1 halaman#280 BBB 04-29-10 177bmoakBelum ada peringkat
- #280 BBB 04-29-10 176Dokumen1 halaman#280 BBB 04-29-10 176bmoakBelum ada peringkat