(2-01) Jungyeop Kim, Robust Vector Digital Watermarking Using Angles and A Random Table
Diunggah oleh
conanconan5599Deskripsi Asli:
Judul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
(2-01) Jungyeop Kim, Robust Vector Digital Watermarking Using Angles and A Random Table
Diunggah oleh
conanconan5599Hak Cipta:
Format Tersedia
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
Robust Vector Digital Watermarking Using Angles and a Random Table
1,
Jungyeop Kim Department of Computer Science, Universit of Missouri, Columbia, USA, jyfloo@gmail.com
doi:10.4156/aiss.vol2. issue4.9
Abstract
In this paper I propose a new digital watermarking method using angles. Angles like distance are not changed easily in vector data. Because of this, the proposed method is robust to scaling. In previous methods there are distortion and topology change. However, this proposed method doesnt have distortion and topology change because I used intersection test. Therefore, the proposed method could be used in various fields to protect the copyright of vector map.
Keywords: Digital Watermarking, Vector Map Data, GIS, Angles, A Random Table 1. Introduction
The Internet and web growth is proceeding very rapidly and many digital contents are distributed by Internet. Although it has the pros that new information is created, pirate copies are generated at the same time [24, 28]. Thus, many people have looked to data embedding methods identifying digital data owners in order to protect copyright [8]. It is difficult to distinguish the pirate copies from the original because there is no difference between the original and the copies. Finally, it causes to violate an owner right of data. Therefore, copyright protection is essential in knowledge based societies [6]. There are encryption and security firewalls to protect copyright. However, if someone deciphers the code or gets through the firewall, it can be useless [8]. Although a digital watermarking adds watermarks which show copyright into the original data, the method doesnt damage the original data. Thus, it is a good method to protect copyright when an ownership dispute generates. Digital watermarking is the method of embedding information into a digital content to protect copyright [1, 4, 5, 10, 15, 18, 23, 25, 31]. Digital watermarking has several features. First, the embedding effectiveness is the probability of detection after embedding. Second, the fidelity is the similarity between the original and the watermarked data. Third, a false positive is the detection of watermarks in data that does not contain any watermarks. Fourth, the robustness is the ability to detect the watermarks in watermarked data after several operations [8]. We can classify digital watermarking methods according to several criteria. First, there are nonblind watermarking and blind watermarking method according to using the original data. Non-blind watermarking is the method that does not require original data for watermark extraction, while blind watermarking method does. Figures 1 and 2 show the blind watermarking method briefly.
Figure 1. Watermark embedding process
- 79 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
Figure 2. Watermark extraction process Second, there is frequency domain method and spatial domain method by embedding watermark method. Frequency domain method is to embed watermarks into frequency domain after changing the original data to frequency. This method is known to guarantee robustness. However, it happens not to extract watermark after geometrical attacks like rotation, scaling, and translation [31]. Moreover, it is not easy to control the distortion after embedding watermarks [9]. Third, spatial domain method is to embed watermarks into the original data directly. Although this method is known to be weaker than the frequency domain method in the robustness aspect, it has the advantage of controlling the distortion after embedding watermarks. Particularly, it can be a good method in vector map data because the distortion and position accuracy are very important in map field. Therefore, I proposed vector map digital watermarking in spatial domain. Vector map data are frequently used in GIS (Geographic Information Systems), navigation, and web map services [15]. Because coordinates are acquired only with expensive instruments, aerial photographs, vectorizing or other such means, the accumulation and management of vector map data are both costly and time-consuming processes [9, 19, 20]. GIS entails hardware, software, data, and human resources, among which data acquisition is the major cost. Indeed, this can account for 80% of an overall budget [16]. Vector data are used in several fields including government. And I expect that the value of the vector data is increased. However, illegally distribution and sale dont make a profit and cause distorted market system [17]. Therefore, as already stated, vector map copyright requires effective protection [9, 13, 19, 20, 21, 22]. Vector map data is various compared with other multimedia data such as image, video and audio file formats. Since the vector map data have a floating point data sequence with a precision, it is difficult to apply general multimedia watermarking methods to the vector map data directly [9]. In this paper, a new blind watermarking method for vector maps is proposed using interior angles. Because the angles are not changed easily, the proposed method can be robust and guarantees fidelity.
2. Related works
Generally, watermarking algorithms are categorized into two classes. Algorithms in the frequency domain embed watermarks in the transform coefficient. The main transforms are DFT(Discrete Fourier Transform), DWT(Discrete Wavelet Transformation), and DCT(Discrete Cosine Transform). These watermarking algorithms in the frequency domain are known to be robust to attacks. However, it remains difficult to correct distortions of data after watermarks are embedded. [9], [26] presented a new method by which the 2D (x, y) coordinates of each vertex are combined to construct a complex value (z=x+iy), after which DFT can be applied to that value. The watermarks embedded in Fourier descriptors can be extracted. These methods, however, have some defects. For example, after the embedding of watermarks, the original data is distorted. Also, these methods can extract watermarks only under specific attacks, not any or all attacks. There are other watermarking algorithms that embed watermarks by changing the DWT coefficients in the DWT domain [30]. Again, however, these methods can extract watermarks only under some attacks. [19] presented a blind watermarking algorithm that does not require original data to extract watermarks. The method embeds watermarks utilizing the coordinates within a single object that are highly correlated in the DCT domain. However, this method distorts the original map. Moreover, it, too, can extract watermarks only under certain attacks.
- 80 -
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
Additionally, there are other algorithms that operate in the spatial domain. These algorithms embed watermarks by directly modifying the coordinates. These watermarking methods can, in comparison with algorithms operating in the frequency domain, more easily control the distortion incurred in the embedding of watermarks. [7] and [22] proposed such spatial-domain watermarking algorithms. The main idea behind this kind of algorithm is to partition data into several blocks and to embed watermarks in coordinates within those blocks using PSNR (Peak Signal to Noise Ratio). A watermarked map thus can be created by the direct alteration of those coordinates. [20] proposed a new method based on this principle. Their method partitions data into blocks and then embeds watermarks using the statistics of the coordinates within those blocks. All such methods, however, are limited in that they cannot extract watermarks under certain operations. [3] designed a novel watermarking method. First, coordinates are extracted by the Douglas-Peuker algorithm. Second, watermarks are embedded into coordinates as the correlation between them. Although this method shows good results under some operations, other generalization algorithms can easily remove watermarks generated using this method. Also, rotation and translation could destroy those watermarks. [14] proposed a new method using azimuth with the features of the vector map data. After calculating azimuth, it embedded watermarks into the azimuth. However, this method has the drawback that it requires the original data and preprocessing before extracting watermarks. In this paper, a novel method which doesnt need the original data and preprocessing is proposed. And the proposed method is robust to several attacks unlike other methods.
3. The features of the vector map digital watermarking
Vector map data are frequently used in GIS, navigation, and web map services [13, 14]. The importance of the location information comes to the force recently, and then the vector map is based to the map fields. Vector map data is various compared with other multimedia data such as image, video, and audio file formats. Since the vector map data have a floating point data sequence with a precision, it is difficult to apply general multimedia watermarking methods to the vector map data directly [9]. Therefore, we need to understand the structure of the vector map data. The vector data consist of points and lines, which represent objects. The vector data doesnt have the change of the objects when the data are scaled. And the data are used in mobile fields because the data has low file volume. However, if the position accuracy is not accurate, the position or shape of the road and buildings are inaccurate. Finally, the services based on this location information can be useless. Because of this reason, a vector map watermarking has to have the fidelity. The fidelity and robustness are the trade-off. That is, if the robustness is enhanced, the fidelity becomes weakened. On the contrary, if the fidelity is enhanced, the robustness becomes weakened. So, vector map digital watermarking is very difficult, we should consider what is more important.
4. The scheme of the proposed method
4.1. Calculating angles
Although objects are rotated or translated, the angle is one of the spatial features unchanged values easily. Using this feature, I can propose a robust vector map watermarking method. Unlike the azimuth method used in [14], the proposed method uses interior angles with 3 points. So, a new method doesnt the original data, and then can be a robust method on geometrical attacks. The interior angle can be calculated using the three consecutive points of the object. Watermarks are embedded into the angle, which changes the coordinates. We can calculate the angle with the cosine rule. In figure 3, the interior angle is computed from the angle FAB using F, A, and B points. We can compute the correct interior angle using the cosine rule when the angle is less than 180 . However, when the value is greater than 180, the value is , not angle (figure 3). In this paper, calculating angle is important. Therefore, it is not a problem to use the cosine rule.
- 81 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
Figure 3. Interior angle
4.2. The random table
After calculating angles on each object, we generate a random table. We apply the random table to the vector map data. This random table can be watermark key. Users can use the random table as different data. It can be prevented to attempt to damage watermark by using a random table. And we dont need a original data when watermarks are extracted because of a random table. That is, even though the algorithm of the watermarking is known, the extraction of the watermark is impossible because this random table is used as a watermark key. The random table is used when 0 between 9 is changed a random number and watermarks are generated. Also, because we use the random table as a watermark key, we dont need the original data when watermarks are extracted.
4.3. The intersection test
The change of the coordinates become after watermarks are embedded into the original data. Although the ideal method is that there is no change of the coordinates, it is impossible. So, after embedding watermarks, if the change is within the allowable error, we can say it is not to damage to the vector map. In vector map data, the positional accuracy is very important unlike in general multimedia data. That is, if the positional accuracy is wrong, the map is useless. And if the topology of the vector map is changed after embedding watermarks, it makes a big problem. For example, if two lines are detached or are crossed after embedding watermarks, some problems are generated. Many watermarking on vector map have not considered the topology. In this paper, we return the problem points to the original points using the intersection test. The intersection test can check if the change of the topology after embedding watermark. The intersection test returns values of 1 when two lines intersect, -1 when two lines dont intersect, and 0 when a line includes an end point [12]. Figure 4 shows the state of the two lines. Comparing returned values before and after embedding watermarks, we preserved the topology of the vector map data. There is an important thing that we have to consider. After embedding watermarks, there is a case that the return value is different. However, if the change is within an allowable error, the watermarks remain.
Figure 4. The states of lines
- 82 -
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
5. The realization of the digital watermarking using angles
5.1. Making a random table
In this paper, we used a random table as a watermark key. After calculating each angle of the objects, we changed an integer number of the angle into a new value using a random table. The reason why we use integer number is this proposed method is to embed watermarks in decimal. The new value is used to generate watermarks, not to change real coordinates. An example of the application of the random table is as follows. First, the owner fixes the range of the random table as 20. A random number between 0 and 20 is generated. Then, a number between 0 and 9 is changed to a number between 0 and 20 (Table 1). If the angle is 46.32, it is changed to 167.32. This changed value is used when the calculations are made to generate watermarks. Table 1. Random table
Real value Changed value 0 6 1 13 2 11 3 1 4 16 5 19 6 7 7 5 8 8 9 3
5.2. Making angles
Because vector data consist of points, we can calculate the angle with three points. The angle is not changed easily under general manipulations. The watermarking method using the angles can be good method because the angle is good information to embed watermarks. The angle is obtained using the consecutive three points and the cosine rule. In this experiment, we calculated the angle with the starting point as the center. Therefore, we can get one angle per object. In figure 5, point A is starting point, and then point E, A, and B are consecutive points. We can calculate angle EAB using cosine rule.
Figure 5. Example of objects
5.3. Making the own value
In this paper, the users own value is used when watermarks are generated. This own value make the proposed method to be secure because the own value is needed when the watermarks are extracted. And if the users own value is used, the person who distributes the map can be identified. The users own value becomes G(x) and is used when watermarks are generated. We used the value after changing to ASCII code value. For example, if the own value is HKD, H: 1001000(71), K: 1001011(74), and D: 1000100(67) are changed. Eventually, G(x) becomes 212(71+74+67). This G(x) becomes essential value when watermarks are embedded and extracted.
5.4. Generalization and embedding watermarks
We can generate watermarks using a random table and an angle. The integer of the calculated angle is changed to a new value using a random table. The new value becomes P(x). Using a formula (1), we can get the watermark. For example, if the angle is 113.169546, the integer 113 is changed P(x) 13131
- 83 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
with table 1. When SIK is used as a own value, the value is G(x) 228). Therefore, the watermark is calculated 93 through a formula (1), and then the angle is changed as 113.93. watermark = G(x) - P(x)%G(x) (1)
This changed angle makes the movement of the coordinates as the changed. That is, the difference between the original angle and the changed angle is bisected, and then the bisected-angle is reflected to coordinates. We can calculate the changed coordinates using formula (2). Figure 6 is example which is the part of the object. Figure 7 is to enlarge figure 6. We can the changed coordinates C as the same formula. The procedure of the embedding watermarks is below. Step 1. Calculate angles and a random table. Step 2. Calculate P(x) using a random table. Step 3. Calculate G(x) using the own values. Step 4. Change calculated angles to watermarked angles. Step 5. Calculate watermarked coordinates.
Figure 6. The original object
Figure 7. Enlarged object (2)
5.5. Extracting watermarks
The proposed watermarking algorithm is a blind method that does not need original data to extract watermarks. Only a random table and the users own value are needed as watermark keys. The process
- 84 -
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
of extracting watermarks proposed in this paper is similar to the process of embedding watermarks. After calculating the angle in watermarked data, one obtains new values using the random table. The watermarks are calculated using the users own value, P(x), and G(x). Finally, whether the calculated watermark is reflected in the angle between the three points is confirmed. If it is, in fact, reflected, the data can be regarded as watermarked data. We use CR (Correspondence Ratio) to validate the embedding effectiveness. The number of the objects in the data is the denominator in CR. The numerator, meanwhile, is set as the number of angles checked for an embedded watermark during the watermarking process.
CR the number of the extracted watermark the number of the objects
(3)
The procedure of the extracting watermarks is below. Step 1. Calculate angles in watermarked data. Step 2. Calculate P(x) and G(x) using a random table and an own value. Step 3. Calculate watermarks using formula (1). Step 4. Check if watermarks are embedded or not.
6. Experimental results
6.1. Experimental data and watermarking attacks
In this paper, we used the vector map file. These data, actually building data, are on the 1/1,000 scale. According to the National Geographic Information Institute of Korea, the maximal error allowed in a 1/1,000 scale map is 0.7m. Therefore, if the change is within this range, the proposed method preserves the integrity of maps. Because of this reason, we used a large scale map. An attack in watermarking is an intentional or unintentional operation generated when data is manipulated. Because the structure of the vector data is different from general multimedia data, the character of the attack is different [19]. The attack on vector data in GIS can be classified into three types: geometrical attacks, vertex attacks, and noise attacks [27]. However, almost no information would be lost in geometrical attacks such as rotation, translation, and scaling. On the other hand, vertex attacks make the vector map data unusable [3]. So, it is critical for a watermarking of vector map data to be able to withstand vertex attacks. In this paper, we experimented on vertex attacks with cropping, generalization, and adding objects. Noise attacks are to add noise on vector map. It is not frequent to generate and is not good attacks because these attacks can make loss of the position accuracy [27]. However, we examined noise attacks as adding noise separately in this paper.
6.2. Embedding watermarks
Position accuracy and topology are very important in vector maps. If the accuracy is reduced or topology is changed after embedding watermarks, the value of the map is lost. We categorized topology as falling into three distinct types, as shown in figure 4. A difference in the intersection test results before and after the embedding of watermarks would indicate a change in the topology due to the embedding of the watermarks. Through the intersection test, we can check whether fidelity is changed. In this paper, there was no such difference. We tested RMSE (Root Mean Squared Error). The result shows that RMSE is 0.0004. We examined whether embedded watermarks were extracted from the watermarked data to check the embedding effectiveness. In the case of the proposed method, CR was 100%. Therefore, the proposed method preserved the integrity of the map and the topology. Figure 8 is the original data and the watermarked data.
- 85 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
Figure 8. Original data(up) and watermarked data(down)
6.3. The robustness tests
We tested the attacks of the three types to check the robustness in this paper. First, geometrical attacks use a map without changing point numbers, and include translation and scaling attacks. Table 2 shows the CR of these attacks. The translation attack moves all objects a certain distance. And the scaling attack is not changing scale in map field. We enlarged and reduced map data with considering the map data as an image. We proved the proposed method doesnt have any problem with geometrical attacks through the result of the experiment. Next, we extracted watermarks under vertex attacks. We experimented on the vector data with cropping and generalization. We used generalization based on Douglas-Peuker algorithm and changed threshold 1m, 10m, and 100m. The experiment proved that this method can extract embedded watermarks. Noise attacks are those that add noise into the data. In this paper, we moved the coordinates in each certain area within the allowable error. And we moved and rotated the vector map data with minute distance and angle. The experimental result shows the proposed method is robust to the noise attacks.
Figure 9. Adding objects
- 86 -
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
Figure 10. Cropping
Generalization 1
Generalization 2
Generalization 3
Figure 11. Generalization
6.4. Experimental analysis
The goal of this work is to develop a new vector watermarking method that is robust to secure a copyright and preserve the fidelity of watermarking data. We embedded and extracted watermarks using angles which are one of the spatial features. The experimental results show that the fidelity is good. That is, RMSE is 0.07 with no change in topoogy. We examined several attacks on the vector map to test the robustness. In geometrical attacks, we extracted every watermark for translation and scaling. However, we couldnt extract every watermark under the vertex attacks because a watermarked coordinate is eliminated under a vertex deletion attack. Also, the CR value was not 100% since added coordinates dont have any watermark. Under the noise attacks, the CR value was very high. So, we proved that this method is robust digital watermarking. Table 3 shows the estimate of the proposed method according to the features of the watermarking.
- 87 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
Table 2. CR Results
Attack range Geometrical attacks 1 translation 10 100 Scaling factor 0.5 Scaling factor 0.8 scaling Scaling factor 1.2 Scaling factor 1.5 Vertex attacks 1 generalization 5 10 Adding objects Noise attacks 0.1 By rotation 0.01 0.001 0.1m By translation 0.01m 0.001m First Adding noise per area Second 100% 96% 99% 100% 100% 100% 100% 100% 85% 97% 84% 95% 100% 100% 100% 100% 100% 100% 100% CR
Table 3. Evaluation based on watermarking features
Watermarking features Method The proposed method Embedding Fidelity effectiveness Robustness False positive rate
7. Conclusions and future work
We proposed new digital watermarking using angles. To embed watermarks, we calculated angles and changed the angles. The proposed method is blind watermarking, which extracts watermarks using a method similar to that used to embed them. The experimental results show that this method has fidelity that is vital to map data and is robust to attacks. In this paper, we embedded watermarks into a
- 88 -
Advances in Information Sciences and Service Sciences Volume 2, Number 4, December 2010
spatial domain with reflecting the features of spatial objects. Through the intersection test, we can preserve the topology of the map data. This is a condition for a vector map digital watermarking method. However, this method has a weak point that we cannot extract watermarks if the interior angles are changed. Future work will include improving this weak point using several spatial features.
8. References
[1] A.A. Mohammad, and A.A, Sameer, An Improved SVD -based Watermarking Scheme for Protecting Rightful Ownership, Signal Processing, vol.88, no.9, pp.2158 -2180, 2008 [2] B.S.Kim and J.G.Choi, Image Watermarking Robust to Geometrical Attacks based on Normalizat ion using Invariant Centroid, Journal of KIISE, vol. 31, no. 3, pp.243 -251, 2004 [3] C.Y Shao, H.L. Wang, X.M. Niu, and X.T. Wang, A Shape -preserving Method for Watermarking 2D Vector Maps based on Statistic Detection, Proceedings of IEICE -Transactions on Information and Systems, pp. 1290-1293, 2006 [4] G. Voyatzis, and I. Pitas, Digital Image Wwatermarking using Mixing Systems, Computers & Graphics, vol.22, no.4, pp.405-416, 1998 [5] H.C. Wu, and C.C. Chang, A Novel Digital Image Watermarking Scheme based on the Vector Quantization Technique, Computers & Security, vol.24, no.6, pp.460 -471, 2005 [6] H.H. Song, Robust Image Watermarking Algorithm Using DWT and Fuzzy Inference, Doctor Thesis, Mokwon University, 2004. [7] H.I. Kang, K.I. Kim, and J.U. Choi, A vector watermarking using the generalized square mask, Proceedings of International Conference on Information Technology: Coding and Computing, pp.234-236, 2001 [8] H.S. Kim, Digital Watermarking. Green, Korea, 2005 [9] I. Kitamura, S. Kanai, and T. Kishinami, Copyright Protection of Vector map using Digital Watermarking Method based on Discrete Fourier Transform, Proceedings of the IEEE 2001 International Symposium on Geoscience and Remote Sensing Symposium, vol. 3, pp.1191-1193, 2001 [10] J. Cong, Affine Invariant Watermarking Algorithm using Feature Matching, Digital Signal Processing, vol.16, no.3, pp.247-254, 2006 [11] J.H.Lee, Blind watermarking using wavelet coefficient exchange, Doctor Thesis, Dongshin University, 2005 [12] J.K. Lee, Algorithm with C, SeHwa, Korea, 2000 [13] J.Y.Kim, Digital watermarking for 2D vector map data in spatial domain, Doctor Theis, Inha University, 2008 [14] J.Y. Kim and S.H. Park, Vector Map Data Watermarking Method using Binary Notation, The Journal of Geographic Information System Association of Korea, vol. 15, no. 4, pp.385-395, 2007 [15] K.S. Jonathan, H.Frank, and G.Bernd, Digital Wwatermarking of Text, Image, and Video Documents, Computers & Graphics, vol.22, no.6, pp.687 -695, 1998 [16] L. Carlos, Wetermarking of digital geospatial datasets: a review of technical, legal and copyright issues, International Journal of Geographical Information Science, vol. 16, no. 6, pp.589 -607, 2002 [17] M. Hu, A Study on the Application of Copyright of Digital Maps, Doctor Theis, Imha Iniversity, 2007 [18] M.C. Hu, D.C. Lou, and M.C. Chang, Dual-wrapped Digital Watermarking Scheme for Image Copyright Protection, Computers & Security, vol.26, no.4, pp.319 -330, 2007 [19] M. Voigt, B. Yang, and C. Busch, Reversible Watermarking of 2D -Vector Data, Proceedings of the 2004 Multimedia and Security Workshop on Multimedia and security, pp.160-165, 2004 [20] M. Voigt, and C. Busch. Feature-based Watermarking of 2D Vector Data, Proceedings of the SPIE-Security and Watermarking of Multimedia Content, vol. 5020, pp. 359-366, 2003 [21] R. Ohbuchi, H. Ueda, S. Endoh, Watermarking 2D Vector Maps in the Mesh-Spectral Domain, Proceedings of International Conference on Shape Modeling and Applications, pp.216-225, 2003 [22] R. Ohbuchi, H. Ueda, and S. Endoh, Robust Watermarking of Vector Digital Maps, Proce edings of IEEE International Conference on Multimedia and Expo, vol. 1, pp. 577-580, 2002
- 89 -
Robust Vector Digital Watermarking Using Angles and a Random Table Jungyeop Kim
[23] S.H. Joo, Y.H. Suh, J.H. Shin, and H. Kikuchi, A New Robust Watermark Embedding into Wavelet DC Components, ETRI Journal, vol.24, no.5, pp.401 -404, 2002 [24] S.J.Jang, A robust watermarking algorithm for RST attacks, Doctor Thesis, Kangwon National University, 2003 [25] T.V. Nguyen, and J.C. Patra, A Simple ICA-based Digital Image Watermarking Scheme, Digital Signal Processing, vol.18, no.5, pp.762-776, 2008 [26] V. Solachidis, N. Nikolaidis, and I. Pitas, Fourier descriptors watermarking of vector graphics images, Proceedings of the International Conference on Image Processing, vol. 3, pp.9 -12, 2000 [27] X.M. Niu, A Survey of Digital Vector Map Watermarking, International Journa l of Innovative Computing, Information and Control, vol. 2, no. 6, pp.1301-1316, 2006 [28] Y.H.Kim, The adaptive digital watermarking using block -based statistical casting scheme, Doctor Thesis, Kwangwoon University, 2001 [29] Y.H. Ko, Object -oriented watermarking method based on PSADT(Polar coordinates Shape Adaptive Discrete Transform) and two-layer watermarking method, Doctor Thesis, Korea Advanced Institute of Science and Technology, 2002. [30] Y.Y. Li, and L.P. Xu, A Blind Watermarking of Vector Graphics Images, Proceedings of the Fifth International Conference on Computational Intelligence and Multimedia Applications, pp.424-429, 2003 [31] Z. Jian, and K. Eckhard, A Generic Digital Watermarking Model, Computer & GRaphics, vol. 22, no.4, pp.397-403, 1998
- 90 -
Anda mungkin juga menyukai
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- INOI 2012 Question PaperDokumen6 halamanINOI 2012 Question PaperShourya BoseBelum ada peringkat
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5795)
- Force Plates: Pressure TransducerDokumen9 halamanForce Plates: Pressure Transduceramit_pt021Belum ada peringkat
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Summative Test Ist (2nd G)Dokumen2 halamanSummative Test Ist (2nd G)Rosell CabalzaBelum ada peringkat
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- A Lightweight Secure Data Sharing SchemeDokumen7 halamanA Lightweight Secure Data Sharing SchemeGopi KrishnaBelum ada peringkat
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Exemplar Gr1 Maths Diagnostic Assessment - Term 2 - 2021Dokumen4 halamanExemplar Gr1 Maths Diagnostic Assessment - Term 2 - 2021Liandra'Lulu'VdMerweBelum ada peringkat
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
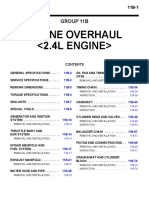
- Engine Overhaul : Group 11BDokumen80 halamanEngine Overhaul : Group 11BДмитрий100% (1)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- Dosing Technology: eco-CONTROL EC200-KDokumen2 halamanDosing Technology: eco-CONTROL EC200-KMario Vargas VegaBelum ada peringkat
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- Bgy. Poblacion SwaDokumen33 halamanBgy. Poblacion SwaKim simyunnBelum ada peringkat
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- AlkylationDokumen42 halamanAlkylationRafi Algawi100% (1)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- fronius-informationDokumen13 halamanfronius-informationcontactoBelum ada peringkat
- Unit QuestionsDokumen155 halamanUnit QuestionsSanya KhanBelum ada peringkat
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- Invers Transf LaplaceDokumen13 halamanInvers Transf LaplaceMeriska AhmadBelum ada peringkat
- Nexus 1450 Energy Meter Brochure - E171702Dokumen12 halamanNexus 1450 Energy Meter Brochure - E171702Edulatin AcademicBelum ada peringkat
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- Chapter 3 Digital ForensicsDokumen5 halamanChapter 3 Digital ForensicsAbhinav GadekarBelum ada peringkat
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- Differentiation Questions and AnswerDokumen10 halamanDifferentiation Questions and AnswerNazurah Kamaruzzaman KamariBelum ada peringkat
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- User AgentDokumen2 halamanUser AgenthuongBelum ada peringkat
- PDMS Attributes ListDokumen48 halamanPDMS Attributes Listsspatilsp100% (1)
- Breaker King Obsolete Book PDFDokumen30 halamanBreaker King Obsolete Book PDFPatrick OlmosBelum ada peringkat
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- CR EstimateDokumen307 halamanCR EstimateGani AnosaBelum ada peringkat
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Metoda Securiti Pada DNP3 ProtokolDokumen16 halamanMetoda Securiti Pada DNP3 ProtokolDeny AriefBelum ada peringkat
- Compliance Statement - FormDokumen16 halamanCompliance Statement - Formaqil khanBelum ada peringkat
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Ha400 PDFDokumen1 halamanHa400 PDFZacharias Pavlos50% (2)
- Fastener NoteDokumen8 halamanFastener NoteAmit PrajapatiBelum ada peringkat
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- Chapter 1Dokumen10 halamanChapter 1Moon LytBelum ada peringkat
- Embedded Linux Course SlidesDokumen571 halamanEmbedded Linux Course SlidesKuan Xing Li100% (2)
- CEH PRACTICAL NOTES - Pratik KaranDokumen23 halamanCEH PRACTICAL NOTES - Pratik Karanproton infosecBelum ada peringkat
- SMAC Actuators User ManualDokumen52 halamanSMAC Actuators User ManualGabo DuarBelum ada peringkat
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Flatpack2 IntegratedDokumen2 halamanFlatpack2 IntegratedNeil BaillieBelum ada peringkat
- 2003 - Serriano - Form Follows SoftwareDokumen21 halaman2003 - Serriano - Form Follows SoftwareMina Hazal TasciBelum ada peringkat
- Rangkaian Om Telolet OmDokumen5 halamanRangkaian Om Telolet Omwalid suwalidBelum ada peringkat
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)