HK - Baseline IT Security Policy PDF
Diunggah oleh
sivextienJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
HK - Baseline IT Security Policy PDF
Diunggah oleh
sivextienHak Cipta:
Format Tersedia
The Office of the Government Chief Information Officer
BASELINE IT SECURITY POLICY [S17]
Version : 4.0
December 2009
The Government of the Hong Kong Special Administrative Region
COPYRIGHT NOTICE
2009 by the Government of the Hong Kong Special Administrative Region Unless otherwise indicated, the copyright in the works contained in this publication is owned by the Government of the Hong Kong Special Administrative Region. You may generally copy and distribute these materials in any format or medium provided the following conditions are met (a) the particular item has not been specifically indicated to be excluded and is therefore not to be copied or distributed; (b) the copying is not done for the purpose of creating copies for sale; (c) the materials must be reproduced accurately and must not be used in a misleading context; and (d) the copies shall be accompanied by the words copied/distributed with the permission of the Government of the Hong Kong Special Administrative Region. All rights reserved. If you wish to make copies for purposes other than that permitted above, you should seek permission by contacting the Office of the Government Chief Information Officer.
BASELINE IT SECURITY POLICY
CONTENTS
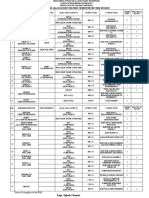
TABLE OF CONTENTS
1. 2.
PURPOSE ............................................................................................................................................................. 1-1 SCOPE .................................................................................................................................................................. 2-1 2.1. 2.2. GOVERNMENT INFORMATION SECURITY MANAGEMENT FRAMEWORK ......................................................... 2-1 IT SECURITY DOCUMENT OVERVIEW ............................................................................................................ 2-4
3.
REFERENCE ....................................................................................................................................................... 3-1 3.1. 3.2. STANDARDS AND GUIDELINES ....................................................................................................................... 3-1 OTHER REFERENCES...................................................................................................................................... 3-1
4.
DEFINITIONS AND CONVENTIONS ............................................................................................................. 4-1 4.1. 4.2. DEFINITIONS .................................................................................................................................................. 4-1 CONVENTIONS ............................................................................................................................................... 4-2
5.
DEPARTMENTAL IT SECURITY ORGANISATION ................................................................................... 5-1 5.1. 5.2. 5.3. 5.4. 5.5. 5.6. 5.7. 5.8. 5.9. SENIOR MANAGEMENT .................................................................................................................................. 5-1 DEPARTMENTAL IT SECURITY OFFICER (DITSO) ......................................................................................... 5-2 DEPARTMENTAL SECURITY OFFICER (DSO) .................................................................................................. 5-2 DEPARTMENTAL INFORMATION SECURITY INCIDENT RESPONSE TEAM (ISIRT) COMMANDER ..................... 5-2 IT SECURITY ADMINISTRATORS .................................................................................................................... 5-3 INFORMATION OWNERS ................................................................................................................................. 5-3 LAN/SYSTEM ADMINISTRATORS ................................................................................................................... 5-4 APPLICATION DEVELOPMENT & MAINTENANCE TEAM ................................................................................. 5-4 USERS OF INFORMATION SYSTEMS ................................................................................................................ 5-4
6.
MANAGEMENT RESPONSIBILITIES ........................................................................................................... 6-1 6.1. 6.2. 6.3. 6.4. GENERAL MANAGEMENT .............................................................................................................................. 6-1 OUTSOURCING SECURITY .............................................................................................................................. 6-1 CONTINGENCY MANAGEMENT ...................................................................................................................... 6-1 HUMAN RESOURCES SECURITY ..................................................................................................................... 6-2
7.
PHYSICAL SECURITY ...................................................................................................................................... 7-1 7.1. 7.2. 7.3. ENVIRONMENT .............................................................................................................................................. 7-1 EQUIPMENT SECURITY................................................................................................................................... 7-1 PHYSICAL ACCESS CONTROL......................................................................................................................... 7-1
8.
ACCESS CONTROL SECURITY...................................................................................................................... 8-1 8.1. 8.2. 8.3. 8.4. 8.5. 8.6. 8.7. 8.8. DATA ACCESS CONTROL ............................................................................................................................... 8-1 AUTHENTICATION .......................................................................................................................................... 8-1 PRIVACY ........................................................................................................................................................ 8-1 USER IDENTIFICATION ................................................................................................................................... 8-1 USER PRIVILEGES MANAGEMENT .................................................................................................................. 8-1 PASSWORD MANAGEMENT ............................................................................................................................ 8-2 NETWORK ACCESS CONTROL ........................................................................................................................ 8-2 LOGGING ....................................................................................................................................................... 8-2
9.
DATA SECURITY ............................................................................................................................................... 9-1 9.1. 9.2. OVERALL DATA CONFIDENTIALITY ............................................................................................................... 9-1 INFORMATION BACKUP.................................................................................................................................. 9-1 APPLICATION SECURITY ........................................................................................................................ 10-1 APPLICATION DEVELOPMENT & MAINTENANCE .......................................................................................... 10-1 i-1
10. 10.1.
Ref. No. : S17
BASELINE IT SECURITY POLICY
CONTENTS
10.2. 11. 11.1. 11.2. 11.3. 11.4. 11.5. 11.6. 12. 12.1. 12.2. 13. 13.1. 13.2.
CONFIGURATION MANAGEMENT & CONTROL ............................................................................................. 10-1 NETWORK & COMMUNICATION SECURITY .................................................................................... 11-1 GENERAL NETWORK PROTECTION............................................................................................................... 11-1 INTERNET SECURITY.................................................................................................................................... 11-1 EMAIL SECURITY ......................................................................................................................................... 11-2 PROTECTION AGAINST COMPUTER VIRUS AND MALICIOUS CODE ............................................................... 11-2 SOFTWARE AND PATCH MANAGEMENT ....................................................................................................... 11-3 WIRELESS SECURITY ................................................................................................................................... 11-3 SECURITY RISK ASSESSMENT & AUDITING ..................................................................................... 12-1 SECURITY RISK ASSESSMENT ...................................................................................................................... 12-1 SECURITY AUDITING.................................................................................................................................... 12-1 SECURITY INCIDENT MANAGEMENT ................................................................................................. 13-1 SECURITY INCIDENT MONITORING .............................................................................................................. 13-1 SECURITY INCIDENT RESPONSE ................................................................................................................... 13-1
Ref. No. : S17
i-2
BASELINE IT SECURITY POLICY
PURPOSE
1.
PURPOSE
This document constitutes a Baseline Information Technology (IT) Security Policy that all HKSAR Government's bureaux and departments shall observe and follow. The policy statements are developed for all levels of staff acting in different roles within bureaux and departments, including management staff, IT administrators, and general IT end users. In order to help readers quickly identify policy statements that are of most concerns to their roles, a tag is attached to the end of each policy statement (section 6 to section 13) for ease of identification. Multiple tags can be attached to a single policy statement if that statement is applicable to multiple roles. The following tagging convention with three different roles is used: [M]: [A]: [U]: Management IT Administrator or Application Development Staff Computer End-User
Nevertheless, it is the responsibility for ALL staff to read through the entire document to understand and follow IT security policies accordingly.
Ref. No. : S17
1-1
BASELINE IT SECURITY POLICY
SCOPE
2.
SCOPE
This document addresses security considerations in the following eight areas: Management responsibilities; Physical security; Access control security; Data security; Application security; Network & communication security; Security risk assessment & auditing; and Security incident management
2.1.
Government Information Security Management Framework
In coordinating and promoting IT security in the Government, an Information Security Management Framework comprising the following four parties has been established : Information Security Management Committee (ISMC) IT Security Working Group (ITSWG) Government Information Security Incident Response Office (GIRO) Bureaux/Departments
Information Security Management Committee (ISMC)
Government Information Security Incident Response Office (GIRO)
IT Security Working Group (ITSWG)
Bureaux / Departments
Departmental IT Security Officer (DITSO)
Departmental Information Security Incident Response Team (ISIRT)
Government IT Security Management Framework The roles of each party are explained in details in the following sections.
Ref. No. : S17 2-1
BASELINE IT SECURITY POLICY
SCOPE
2.1.1.
Information Security Management Committee (ISMC)
A central organisation, Information Security Management Committee (ISMC), was established in April 2000 to oversee the IT security within the whole government. The committee meets on a regular basis to: Review and endorse changes to the Government IT security related regulations, policies and guidelines; Define specific roles and responsibilities relating to IT security; and Provide guidance and assistance to bureaux and departments in the enforcement of IT security related policies, through the IT Security Working Group (ITSWG).
The core members of ISMC comprise representatives from: Office of the Government Chief Information Officer (OGCIO) Security Bureau (SB)
Representative(s) from other bureaux/departments will be co-opted into the Committee on a need basis, in relation to specific subject matters. 2.1.2. IT Security Working Group (ITSWG)
The IT Security Working Group (ITSWG) serves as the executive arm of the Information Security Management Committee (ISMC) in the promulgation and compliance monitoring of Government IT security related regulations, policies and guidelines. The ITSWG was established in May 2000 and its responsibilities are to: Co-ordinate activities aimed at providing guidance and assistance to bureaux and departments in the enforcement of IT security related regulations, policies and guidelines; Monitor the compliance with the Baseline IT Security Policy at bureaux and departments; Define and review the IT security related regulations, policies and guidelines; and Promote IT security awareness within the Government.
The core members of ITSWG comprise representatives from: Office of the Government Chief Information Officer (OGCIO) Security Bureau (SB) Hong Kong Police Force (HKPF) Chief Secretary for Administrations Office (CSO) Information Technology User-Managers Group (ITUG)
Representative(s) from other bureaux/departments will be co-opted into the Working Group on a need basis, in relation to specific subject matters.
Ref. No. : S17 2-2
BASELINE IT SECURITY POLICY
SCOPE
2.1.3.
Government Information Security Incident Response Office (GIRO)
To handle information security incidents occurring in bureaux/departments, an Information Security Incident Response Team (ISIRT) should be established in each bureau/department. Meanwhile, the Government Information Security Incident Response Office (GIRO) provides central co-ordination and support to the operation of individual ISIRTs of bureaux/departments. The GIRO has the following major functions: Disseminate security alerts on impending and actual threats to DITSOs; Maintain a central inventory and oversee the handling of all information security incidents in the Government; Prepare periodic statistics reports on Government information security incidents; Act as a central office to coordinate the handling of multiple-point security attacks (i.e. simultaneous attacks on different Government information systems); Act as a bridge between the HKCERT and the Government regarding Government's information security incidents; and Enable experience sharing and information exchange related to information security incident handling among ISIRTs of different bureaux/departments, and the HKCERT.
The core members of GIRO comprise representatives from: Office of the Government Chief Information Officer (OGCIO) Security Bureau (SB) Hong Kong Police Force (HKPF) 2.1.4. Bureaux / Departments
Bureaux/departments are responsible for the security protection of their information systems and computer facilities. The roles and responsibilities of IT security staff within a bureau/department are detailed in Section 5 - DEPARTMENTAL IT SECURITY ORGANISATION.
Ref. No. : S17
2-3
BASELINE IT SECURITY POLICY
SCOPE
2.2.
IT Security Document Overview
The following diagram describes the relationship of various IT security documents within the Government:
IT Security Documents
Ref. No. : S17
2-4
BASELINE IT SECURITY POLICY
SCOPE
The purpose and overview of the five core IT security documents are described below: Baseline IT Security Policy : (S17) A top-level directive statement that sets the minimum standards of a security specification for all bureaux / departments. It states what aspects are of paramount importance to a bureau / department. Thus, the Baseline IT Security Policy can be treated as basic rules which must be observed as mandatory while there can still be other desirable measures to enhance the security. Introduces general concepts relating to Information Technology Security and elaborates interpretations on the Baseline IT Security Policy. It also provides readers some guidelines and considerations in defining security requirements. Acts as a supplementary document to IT Security Guidelines to provide general guidelines on Internet gateway security. These guidelines represent what are regarded as best practices to maintain security risks at an acceptable level under the Internet open platform. It is intended for staff who are involved in the operational and technical functions of Internet gateway services. Acts as a supplementary document to IT Security Guidelines to give an introduction to a generic model for IT security risk assessment and security audit. This document does not focus on how to conduct a security risk assessment or audit. Rather, it provides a reference model to facilitate the alignment on the coverage, methodology, and deliverables of the services to be provided by independent security consultants or auditors. Acts as a supplementary document to IT Security Guidelines to provide a reference for the management, administration and other technical and operational staff to facilitate the development of security incident handling plan, and to be used for preparation for, detection of, and responding to information security incidents.
IT Security Guidelines : (G3)
Internet Gateway Security Guidelines : (G50)
Security Risk Assessment & Audit Guidelines : (G51)
Information Security Incident Handling Guidelines : (G54)
Ref. No. : S17
2-5
BASELINE IT SECURITY POLICY
REFERENCE
3. 3.1.
REFERENCE Standards and Guidelines
a) Information Technology Security Techniques Information security management systems Requirements, ISO/IEC 27001:2005, dated October 2005
3.2.
Other References
a) Government of Hong Kong Special Administrative Region, Security Regulations b) Civil Service Branch Circular No. 17/94 Integrity Checking
Ref. No. : S17
3-1
BASELINE IT SECURITY POLICY
DEFINITIONS AND CONVENTIONS
4. 4.1.
DEFINITIONS AND CONVENTIONS Definitions
a) Information System an electronic information system that processes data electronically through the use of information technology including but is not limited to: computer systems, servers, workstations, terminals, storage media, communication devices and network resources. only authorised persons are allowed to know or gain access to the information stored or processed by Information Systems in any aspects. only authorised persons are allowed to make changes to the information stored or processed by Information Systems in any aspects. Information Systems should be available to users at any given or specified period of time. a documented list of management instructions that describe in detail the proper use and management of computer and network resources with the objective to protect these resources as well as the information stored or processed by Information Systems from any unauthorised disclosure, modifications or destruction. refers to the categories of information classified in accordance with the Security Regulations. persons employed by the Government irrespective of the employment period and terms. a centralised data processing facility that houses Information Systems and related equipment. A control section is usually provided that accepts work from and releases output to users. a dedicated room for housing computer equipment. programs that cause undesirable effect to the Information Systems. Examples of malicious codes include computer viruses, network worms, trojan horses, logic bombs, and spyware etc.
b) Confidentiality
c) Integrity
d) Availability
e) IT Security Policy
f)
Classified Information
g) Staff
h) Data Centre
i) j)
Computer Room Malicious Codes
Ref. No. : S17
4-1
BASELINE IT SECURITY POLICY
DEFINITIONS AND CONVENTIONS
4.2.
Conventions
4.2.1. The following is a list of conventions used in this Manual Shall Should May the use of the word shall indicates a mandatory requirement. the use of the word should indicates a requirement for good practice, which should be implemented whenever possible. the use of the word may indicates a desirable requirement.
Ref. No. : S17
4-2
BASELINE IT SECURITY POLICY
DEPARTMENTAL IT SECURITY ORGANISATION
5.
DEPARTMENTAL IT SECURITY ORGANISATION
This section explains the individual role and responsibility of a departmental IT Security organisation. Multiple roles can be assigned to a single staff depending on resource availability. The following diagram describes a sample Departmental IT Security organisational framework:
Senior Management
Departmental IT Security Officer
Departmental Security Officer
Departmental ISIRT Commander
IT Security Administrators
Information Owners
LAN/System Administrators
Application Development & Maintenance Team
Users
An Example Organisation Chart for Departmental IT Security Management1
5.1.
Senior Management
The senior management of bureaux/departments shall have an appreciation of IT security, its problems and resolutions. His / her responsibilities include: Direct and enforce the development of security measures; Provide the necessary resources required for the measures to be implemented; and Ensure participation at all levels of management, administrative, technical and operational staff, and provide full support to them.
1 The actual IT Security Management structure may vary according to the circumstances of each organisation.
Ref. No. : S17
5-1
BASELINE IT SECURITY POLICY
DEPARTMENTAL IT SECURITY ORGANISATION
5.2.
Departmental IT Security Officer (DITSO)
Head of bureau/department shall appoint a Departmental IT Security Officer (DITSO) to be responsible for IT security. The roles and responsibilities of DITSO shall be clearly defined which include but are not limited to the following: Establish and maintain an information protection program to assist all employees in the protection of the information they use; Lead in the establishment, maintenance and implementation of information security policies, standards, guidelines and procedures; Coordinate with other bureaux and departments on IT security issues; Disseminate security alerts on impending and actual threats from the GIRO to responsible parties within the bureau/department; Ensure information security risk assessments and audits are performed as necessary; and Initiate investigations and rectification in case of breach of security.
5.3.
Departmental Security Officer (DSO)
According to the Security Regulations, the Department Head will appoint a Departmental Security Officer to perform the departmental security related duties. A Departmental Security Officer will take the role as an executive to: Discharge responsibilities for all aspects of security for the Bureau / Department; and Advise on the set up and review of the security policy.
The Departmental Security Officer may take on the role of the Departmental IT Security Officer. Alternatively, in those bureaux/departments where someone else is appointed, the Departmental IT Security Officer shall collaborate with the DSO to oversee the IT security of the bureau/department.
5.4.
Departmental Information Security Incident Response Team (ISIRT) Commander
The ISIRT is the central focal point for coordinating the handling of information security incidents occurring within the respective bureau/department. Head of bureau/department should designate an officer from the senior management to be the ISIRT Commander. The ISIRT Commander should have the authority to appoint core team members for the ISIRT. The responsibilities of an ISIRT Commander include: Provide overall supervision and co-ordination of information security incident handling
5-2
Ref. No. : S17
BASELINE IT SECURITY POLICY
DEPARTMENTAL IT SECURITY ORGANISATION
for all Information Systems within the bureau/department; Make decisions on critical matters such as system recovery, the engagement of external parties and the extent of involvement, and service resumption logistics after recovery etc.; Trigger the departmental disaster recovery procedure where appropriate, depending on the impact of the incident on the business operation of the bureau/department; Provide management endorsement on the provision of resources for the incident handling process; Provide management endorsement in respect of the line-to-take for publicity on the incident; Collaborate with GIRO in the reporting of information security incidents for central recording and necessary follow up actions; and Facilitate experience and information sharing within the bureau/department on information security incident handling and related matters.
5.5.
IT Security Administrators
IT Security Administrators are responsible for providing security and risk management related support services. They assist in identifying system vulnerabilities and performing security administrative work of the system. His / her responsibilities also include: Maintain control and access to the system; Check and manage audit logs; and Promote security awareness within the bureau/department.
The IT Security Administrator may or may not be a technical person, but he/she should not be the same person as the System Administrator. There should be segregation of duties between the IT Security Administrator and the System Administrator
5.6.
Information Owners
Information Owners are the collators and the owners of information stored in databases and data files. Their primary responsibility is to: Determine the security requirements and security classifications, usage and protection of the information.
Ref. No. : S17
5-3
BASELINE IT SECURITY POLICY
DEPARTMENTAL IT SECURITY ORGANISATION
5.7.
LAN/System Administrators
LAN/System Administrators are responsible for the day-to-day administration, operation and configuration of the computer systems and network in bureaux/departments, whereas Internet System Administrators are responsible for the related tasks for their Internet-facing Information Systems. Their responsibilities include: Implement the security mechanisms in accordance with procedures/guidelines established by the Departmental IT Security Officers.
5.8.
Application Development & Maintenance Team
The Application Development & Maintenance Team is responsible for producing the quality systems in the use of quality procedures, techniques and tools. Their responsibilities include: Liaise with the Information Owner in order to agree on system security requirements; and Define the solutions to implement these security requirements.
5.9.
Users of Information Systems
Users of Information Systems are the staff who actually use the information and shall be accountable for all their activities on the Information Systems. Responsibilities of an information system user include: Know, understand, follow and apply all the possible and available security mechanisms to the maximum extent possible; and Prevent unauthorised access to their computers and workstations at his/her best effort.
Ref. No. : S17
5-4
BASELINE IT SECURITY POLICY
MANAGEMENT RESPONSIBILITIES
6. 6.1.
MANAGEMENT RESPONSIBILITIES General Management
6.1.1. 6.1.2. 6.1.3. 6.1.4. Review of information security policies, standards, guidelines and procedures shall be conducted periodically. [M] Bureaux/departments shall ensure that security protection is responsive and adaptive to changing environment and technology. [M] Bureaux/departments shall ensure that the provision for necessary security safeguards and resources are covered in their budgets. [M] Bureaux/departments shall ensure that an inventory of hardware assets, software assets, valid warranties and maintenance service agreements are properly kept and maintained. [M] Bureaux/departments shall apply sufficient segregation of duties to avoid execution of all security functions of an Information System by a single individual. [M] Bureaux/departments shall enforce the least privilege principle when assigning resources and privileges of Information Systems to users. [M] Bureaux /departments shall ensure the confidentiality, integrity and availability of information and all other security aspects of Information Systems under their control including outsourced systems. [M] Bureaux /departments shall promulgate and enforce their own IT Security Policy. They shall use the Baseline IT Security Policy document as a basis for their own policy document. [M]
6.1.5. 6.1.6. 6.1.7.
6.1.8.
6.2.
Outsourcing Security
6.2.1. Outsourcing or third party service providers shall observe and comply with bureaux/departments' own departmental IT security policy and other information security requirements issued by the Government. [M] Bureaux/departments shall monitor and review with the outsourcing or third party service providers to ensure that security operations are managed properly. [M]
6.2.2.
6.3.
Contingency Management
6.3.1. Plans for emergency response and disaster recovery of mission critical Information Systems shall be fully documented, regularly tested and tied in with the Business Continuity Plan. [M] [A]
Ref. No. : S17
6-1
BASELINE IT SECURITY POLICY
MANAGEMENT RESPONSIBILITIES
6.4.
Human Resources Security
6.4.1. Information security is the responsibility of every member of the staff in the Government. As such, bureaux/departments shall educate users about the IT Security Policy and strengthen their security awareness. [M][U] Staff shall be educated and trained in order to enable them to discharge their responsibilities and perform their duties relating to IT security. [M] Bureaux/departments shall include in their IT Security Policy a provision advising staff that if they contravene any provision of the Policy they may be subjected to disciplinary action under the Public Service (Administration) Order (see Civil Service Regulations 410, available on the Central Cyber Government Office site), and that different levels of disciplinary action may be instigated depending on the severity of the breach. [M] Bureaux/departments shall also include in their IT Security Policy a provision advising all non-Civil Service contract employees that if they contravene any provision of the Policy, their employment contracts may be terminated depending on the severity of the breach. [M] Staff who use or have unescorted access to Information Systems and resources shall be carefully selected and they shall be made aware of their own responsibilities and duties. They shall be formally notified of their authorisation to access Information Systems. [M] Bureaux/departments shall advise all staff of their IT security responsibilities upon being assigned a new post, and periodically throughout their term of employment. [M] Staff handling classified systems or systems containing classified information shall undergo an integrity check as stipulated in CSB Circular 17/94. The type of checking (Appointment Checking / Normal Checking / Extended Checking) shall commensurate with the sensitivity level of the information / system that staff will handle. [M] External consultants, contractors, outsourced staff, and temporary staff who are engaged in Government work shall be subject to the same information security requirements, and have the same information security responsibilities, as Government staff. [M]
6.4.2. 6.4.3.
6.4.4.
6.4.5.
6.4.6. 6.4.7.
6.4.8.
Ref. No. : S17
6-2
BASELINE IT SECURITY POLICY
PHYSICAL SECURITY
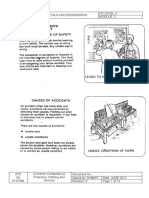
7. 7.1.
PHYSICAL SECURITY Environment
7.1.1. Careful site selection and accommodation planning of a purpose-built computer installation shall be conducted. Reference to the security specifications for construction of special installation or office as standard should be made. [M] [A] Data centres and computer rooms shall have good physical security and strong protection from disaster and security threats, whether natural or caused by other reasons, in order to minimise the extent of loss and disruption. [M] [A] Backup media containing business essential and/or mission critical information shall be sited at a safe distance from the main site in order to avoid damage arising from a disaster at the main site. [A] Data centres and computer rooms shall conform to Level II1 security if the Information System housed involves handling of CONFIDENTIAL information and conform to Level III1 security for handling of TOP SECRET / SECRET information. [M] [A]
7.1.2.
7.1.3.
7.1.4.
7.2.
Equipment Security
7.2.1. 7.2.2. All Information Systems shall be placed in a secure environment or attended by staff to prevent unauthorised access. [A] Staff in possession of laptop, portable computer, personal digital assistant, or mobile computing devices for business purposes shall safeguard the equipment in his/her possession, and shall not leave the equipment unattended without proper security measures. [U] IT equipment shall not be taken away from sites without proper control. [M] [A]
7.2.3.
7.3.
Physical Access Control
7.3.1. A list of persons who are authorised to gain access to data centres, computer rooms or other areas supporting critical activities, where computer equipment and data are located or stored, shall be kept up-to-date and be reviewed periodically. [A] All access keys, cards, passwords, etc. for entry to any of the computer systems and networks shall be physically secured or subject to well-defined and strictly enforced security procedures. [A] All visitors to data centres or computer rooms shall be monitored at all times by an authorised Government staff member. [A]
7.3.2.
7.3.3.
1 For detailed security specifications on Level I/II/III security, please refer to the document Guidelines for Security
Provisions in Government Office Buildings published by the Security Bur eau.
Ref. No. : S17
7-1
BASELINE IT SECURITY POLICY
PHYSICAL SECURITY
7.3.4.
Automatic protection features (e.g. password protected screen saver, keyboard lock) in servers, computer terminals, workstations or microcomputers should be activated if there has been no activity for a predefined period of time to prevent illegal system access attempt. Alternatively, the logon session and connection should be terminated. Also, user workstation should be switched off, if appropriate, before leaving work for the day or before a prolonged period of inactivity. [A] [U] All staff with separate personal offices that can be directly accessed from public area and contain Information System(s) should lock the doors when these offices are not in use. [U] The display screen of an Information System on which classified information can be viewed shall be carefully positioned so that unauthorised persons cannot readily view it. [A] [U]
7.3.5.
7.3.6.
Ref. No. : S17
7-2
BASELINE IT SECURITY POLICY
ACCESS CONTROL SECURITY
8. 8.1.
ACCESS CONTROL SECURITY Data Access Control
8.1.1. 8.1.2. 8.1.3. 8.1.4. Access to information shall not be allowed unless authorised by the relevant information owners. [A] [U] Data access rights shall be granted to users based on a need-to-know basis. [A] [U] Data access rights shall be clearly defined and reviewed periodically. [A] Access to an Information System containing CONFIDENTIAL or above classification information shall be restricted by means of logical access control. [A]
8.2.
Authentication
8.2.1. 8.2.2. 8.2.3. Access to classified information without appropriate authentication shall not be allowed. [A] [U] Authentication shall be performed in a manner commensurate with the sensitivity of the information to be accessed. [A] Consecutive unsuccessful log-in trials shall be controlled. [A]
8.3.
Privacy
8.3.1. Management reserves the right to examine all information stored in or transmitted by Government Information Systems in compliance with the Personal Data (Privacy) Ordinance. [M] [U]
8.4.
User Identification
8.4.1. Each user identity (user-ID) shall uniquely identify only one user. Shared or group user-IDs are not permitted unless explicitly approved by the Departmental IT Security Officer. [A] [U] Users are responsible for all activities performed with their user-IDs. [U]
8.4.2.
8.5.
User Privileges Management
8.5.1. 8.5.2. 8.5.3. All accounts shall be revoked after a pre-defined period of inactivity. [A] User privileges shall be reviewed periodically. [A] At the time that a member of the staff is transferred or ceases to provide services to the Government, all related Information Systems privileges shall be promptly terminated.
Ref. No. : S17
8-1
BASELINE IT SECURITY POLICY
ACCESS CONTROL SECURITY
The outgoing officer shall be responsible for the handover of computer resources to his/her supervisor or the incoming officer for business continuity. [M] [A] [U] 8.5.4. The use of special privileges shall be restricted and controlled. [A]
8.6.
Password Management
8.6.1. Bureaux/departments shall define a strict password policy that details at least, minimum password length, initial assignment, restricted words and format, password life cycle, and include guidelines on suitable system and user password selection. [M] [A] Passwords shall not be shared or divulged unless necessary (e.g., helpdesk assistance, shared PC and shared files). The risk of sharing passwords is that it increases the probability of security being compromised. If passwords must be shared, explicit approval from the Departmental IT Security Officer must be obtained. Besides, the shared passwords should be changed promptly when the need no longer exists and should be changed frequently if sharing is required on a regular basis. [A] [U] Passwords shall always be well protected when held in storage. Passwords shall be encrypted when transmitted over an un-trusted communication network. Compensating controls shall be applied to reduce the risk exposure of Information Systems to an acceptable level if encryption is not implementable. [A] Staff are prohibited from capturing or otherwise obtaining passwords, decryption keys, or any other access control mechanism, which could permit unauthorised access. [U] All vendor-supplied default passwords shall be changed before any Information System is put into operation. [A] [U] All passwords shall be promptly changed if they are suspected of / are being compromised, or disclosed to vendors for maintenance and support. [A] [U]
8.6.2.
8.6.3.
8.6.4. 8.6.5. 8.6.6.
8.7.
Network Access Control
8.7.1. Prior approval from the Departmental IT Security Officer is required to connect a departmental Information System with another Information System under the control of another bureau/department. The security level of the Information System being connected shall not be downgraded. [A]
8.8.
Logging
8.8.1. Bureaux/departments shall define policies relating to the logging of activities of Information Systems under their control according to the business needs and data classification. [M] [A] Any log kept shall provide sufficient information to support comprehensive audits of the effectiveness of, and compliance of security measures. [A]
8.8.2.
Ref. No. : S17
8-2
BASELINE IT SECURITY POLICY
ACCESS CONTROL SECURITY
8.8.3.
Logs shall be retained for a period commensurate with their usefulness as an audit tool. During this period, such logs shall be secured such that they cannot be modified, and can only be read by authorised persons. [A] Logs shall not be used to profile the activity of a particular user unless it relates to a necessary audit activity supported by the Departmental IT Security Officer. [A] [U] Regular checking on log records, especially on system/application where classified information is processed/stored, shall be performed, not only on the completeness but also the integrity of the log records. All system and application errors which are suspected to be triggered as a result of security breaches shall be reported and logged. [M] [A] [U] Clock synchronisation should be configured to keep clocks of Information Systems in sync. [A]
8.8.4. 8.8.5.
8.8.6.
Ref. No. : S17
8-3
BASELINE IT SECURITY POLICY
DATA SECURITY
9. 9.1.
DATA SECURITY Overall Data Confidentiality
9.1.1. Information about Information Systems that may compromise the security of those systems shall not be disclosed to users, or any other third parties, except on a need-to-know basis and only if authorised by the Departmental IT Security Officer. [A] Staff shall not disclose information about the individuals, bureaux/departments or specific systems that have suffered from damages caused by computer crimes and computer abuses, or the specific methods used to exploit certain system vulnerabilities, to any people other than those who are handling the incident and responsible for the security of such systems, or authorised investigators involving in the investigation of the crime or abuse. [U] Staff shall not disclose to any unauthorised persons the nature and location of the Information Systems, and the information system controls that are in use or the way in which they are implemented. [U] All stored information classified as CONFIDENTIAL or above shall be encrypted. [A] [U] Bureaux/departments shall comply with the Security Regulations in relation to Information Systems security including, but not limited to, storage, transmission, processing, and destruction of classified information. [M] [A] [U] Personal Data (Privacy) Ordinance (Cap. 486) shall be observed when handling personal data. [M] [A] [U]
9.1.2.
9.1.3.
9.1.4. 9.1.5.
9.1.6.
9.2.
Information Backup
9.2.1. 9.2.2. 9.2.3. 9.2.4. Backup and recovery procedures shall be well documented, properly implemented, and tested periodically. [A] Backups shall be carried out at regular intervals. [A] Backup activities shall be reviewed regularly. [A] Integrity copies of backups shall be stored at a remote distance from the system and be protected. Backup media should also be protected against unauthorised access, misuse or corruption during transportation. [A]
Ref. No. : S17
9-1
BASELINE IT SECURITY POLICY
APPLICATION SECURITY
10. 10.1.
APPLICATION SECURITY Application Development & Maintenance
10.1.1. Application development staff shall include security planning and implement the appropriate security measures and controls for system under development according to the systems' security requirements. [A] 10.1.2. Documentation and listings of applications shall be properly maintained and restricted on a need-to-know basis. [A] 10.1.3. Formal testing and review on the security controls shall be performed prior to implementation. [A] 10.1.4. The integrity of an application shall be maintained with appropriate security controls such as version control mechanism and separation of environments for development, system testing, acceptance testing, and live operation. [A] 10.1.5. Application development staff shall not be permitted to access production information unless necessary. [A]
10.2.
Configuration Management & Control
10.2.1. Change control procedures for requesting and approving program/system changes shall be documented. [A] 10.2.2. Changes affecting existing security protection mechanisms shall be carefully considered. [A] 10.2.3. Installation of all computer equipment and software shall be done under control and audit. [A] 10.2.4. Bureaux/departments shall ensure that staff are formally advised of the impact of security changes and usage on Information Systems. [M] [A]
Ref. No. : S17
10-1
BASELINE IT SECURITY POLICY
NETWORK & COMMUNICATION SECURITY
11. 11.1.
NETWORK & COMMUNICATION SECURITY General Network Protection
11.1.1. Internal network addresses, configurations and related system or network information shall be properly maintained and shall not be publicly released without the approval of the concerned bureau/department. [A] 11.1.2. All internal networks with connections to other Government networks or publicly accessible computer networks shall be properly protected. [A] 11.1.3. Security measures shall be in place to prevent unauthorised remote access to the systems and data. [A] 11.1.4. Staff are prohibited from connecting workstations to external network by means of communication device, such as dial-up modem, wireless interface, or broadband link, if the workstations are simultaneously connected to a local area network (LAN) or another internal communication network, unless with the approval of the concerned bureau/department. [U] 11.1.5. Staff shall not connect any unauthorised Information System device to a Government Information System without prior approval as designated by the bureau/department. [U] 11.1.6. Proper configuration and administration of information / communication systems is required and shall be reviewed regularly. [A] 11.1.7. Connections and links made to other network shall not compromise the security of information processed at another, and vice versa. [A] 11.1.8. Connecting privately owned computer resources to Government internal network requires approval from the Departmental IT Security Officer. Bureaux and departments shall ensure that such usage of personal computer resources conform to the same IT security policy. [U] 11.1.9. CONFIDENTIAL / RESTRICTED information shall be encrypted when transmitted over an un-trusted communication network. [A] [U] 11.1.10. TOP SECRET / SECRET information shall be transmitted only under encryption and inside an isolated LAN approved by the Government Security Officer subject to the technical endorsement of OGCIO. [A] [U]
11.2.
Internet Security
11.2.1. All Internet access shall be either through centrally arranged Internet gateways or bureau/departments own Internet gateway conforming to OGCIO security standards. In circumstances where this is not feasible or having regard to the mode of use1,
1 Such modes of use may include, for example, Internet surfing, email exchange, and the use of official, portable computers while on business. The relevant standalone machines must still be protected by any applicable security mechanisms.
Ref. No. : S17
11-1
BASELINE IT SECURITY POLICY
NETWORK & COMMUNICATION SECURITY
bureaux/departments may consider allowing Internet access through stand-alone machines, provided that there is an approval and control mechanism at appropriate level in the bureaux/departments. [A] 11.2.2. Bureaux/departments should consider the value versus inconvenience of implementing technologies to blocking non-business websites. The ability to connect with a specific website does not in itself imply that users of systems are permitted to visit that site. [M] 11.2.3. Each bureau/department shall clearly define and communicate to users its policy in relation to acceptable Internet usage. [M] 11.2.4. All software and files downloaded from the Internet shall be screened and verified with anti-virus software. [A] [U] 11.2.5. Staff should not execute mobile code or software downloaded from the Internet unless the code is from a known and trusted source. [U]
11.3.
Email Security
11.3.1. Each bureau/department shall clearly define and communicate to users its policy in relation to acceptable email usage. [M]
11.3.2. Systems administrators shall establish and maintain a systematic process for the recording, retention, and destruction of electronic mail messages and accompanying logs. [A] 11.3.3. Incoming/outgoing email shall be screened for computer viruses and malicious codes. [A] [U] 11.3.4. Internal email address lists containing entries for authorised users or Government sites shall be properly maintained and protected from unauthorised access and modification. [A] 11.3.5. Email transmission of classified information shall be transmitted only on an Information System approved by the Government Security Officer subject to the technical endorsement of OGCIO. Email transmission of TOP SECRET / SECRET information shall also follow the condition as stipulated in 11.1.10. [U] 11.3.6. Emails from suspicious sources should not be opened or forwarded. [U]
11.4.
Protection Against Computer Virus and Malicious Code
11.4.1. Anti-virus software shall always be enabled on all local area network servers and personal computers, and computers connecting to the Government internal network via remote access channel. [A] [U] 11.4.2. Bureaux/departments shall protect their Information Systems from computer viruses and malicious codes. Virus signatures, malicious code definitions as well as their detection and repair engines shall be updated regularly and whenever necessary. [A] [U]
Ref. No. : S17
11-2
BASELINE IT SECURITY POLICY
NETWORK & COMMUNICATION SECURITY
11.4.3. Storage media and files from unknown source or origin shall not be used unless the storage media and files have been checked and cleaned for computer viruses and malicious codes. [U] 11.4.4. Users shall not intentionally write, generate, copy, propagate, execute or involve in introducing computer viruses or malicious codes. [U] 11.4.5. Bureaux/departments shall implement proper measures to protect their wireless or mobile computing devices against computer viruses and malicious codes. [A] [U]
11.5.
Software and Patch Management
11.5.1. Computers and networks shall only run software that comes from trustworthy sources. [U] 11.5.2. No unauthorised application software shall be loaded onto a Government Information System without prior approval from officer as designated by the bureau/department. [A] [U] 11.5.3. Bureaux/departments shall protect their Information Systems from known vulnerabilities by applying the latest security patches recommended by the product vendors or implementing other compensating security measures. [A] [U] 11.5.4. Before security patches are applied, proper risk evaluation and testing should be conducted to minimise the undesirable effects to the Information Systems. [A] [U]
11.6.
Wireless Security
11.6.1. Bureaux/departments shall document, monitor, and control wireless networks with connection to Government internal network. [A] 11.6.2. Proper authentication and encryption security controls shall be employed to protect data communication over wireless networks with connection to Government internal network. [A] [U]
Ref. No. : S17
11-3
BASELINE IT SECURITY POLICY
SECURITY RISK ASSESSMENT & AUDITING
12. 12.1.
SECURITY RISK ASSESSMENT & AUDITING Security Risk Assessment
12.1.1. Information Systems security risk assessments for information systems and production applications shall be performed at least once every two years. A security risk assessment shall also be performed before production, and prior to major enhancements and changes associated with these systems or applications. [M] 12.1.2. Use of software and programs for security risk assessment analysis shall be restricted and controlled. [A]
12.2.
Security Auditing
12.2.1. Information Systems shall be periodically evaluated by auditors of an independent and trusted party to determine the minimum set of controls required to reducing risk to an acceptable level. [M] 12.2.2. Auditing of compliance of IT security policies shall be performed periodically. [A] 12.2.3. Use of software and programs for security audit analysis shall be restricted and controlled. [A]
Ref. No. : S17
12-1
BASELINE IT SECURITY POLICY
SECURITY INCIDENT MANAGEMENT
13. 13.1.
SECURITY INCIDENT MANAGEMENT Security Incident Monitoring
13.1.1. Bureaux/departments shall establish an incident detection and monitoring mechanism to detect, contain and ultimately prevent security incidents. [M] 13.1.2. Bureaux/departments shall ensure that system logs and other supporting information are retained for the proof and tracing of security incidents. [A]
13.2.
Security Incident Response
13.2.1. Bureaux/departments shall establish, document and maintain a security incident handling/reporting procedure for their Information Systems. [M] 13.2.2. Staff shall be made aware of the security incident handling/reporting procedure that is in place and shall observe and follow it accordingly. [M] 13.2.3. All network or systems software malfunctions, information security alerts, warnings, suspected vulnerabilities, and the like, and suspected network security problems, shall be reported immediately only to the responsible party according to the incident handling procedure. [A] [U] 13.2.4. Immediate follow-up actions are required on suspected system intrusion according to security incident handling/reporting procedures. [A]
*** End ***
Ref. No. : S17
13-1
Anda mungkin juga menyukai
- Data Loss Prevention DLP Complete Self-Assessment GuideDari EverandData Loss Prevention DLP Complete Self-Assessment GuideBelum ada peringkat
- It Security GuidelinesDokumen143 halamanIt Security GuidelinesTeam LeaderBelum ada peringkat
- Network Assessment ChecklistDokumen2 halamanNetwork Assessment ChecklistHanumant ShindeBelum ada peringkat
- Information Security Policy TemplateDokumen2 halamanInformation Security Policy TemplategfbBelum ada peringkat
- IT Policies, Procedures and Standards v1Dokumen176 halamanIT Policies, Procedures and Standards v1Jimmy UkoboBelum ada peringkat
- Policy Document IT Access Policy: (Date)Dokumen10 halamanPolicy Document IT Access Policy: (Date)bedorlehackerBelum ada peringkat
- IT Security Incident ManagementDokumen3 halamanIT Security Incident ManagementBrianEarlBelum ada peringkat
- Network Security and ManagementDokumen4 halamanNetwork Security and Managementrashid1986Belum ada peringkat
- Network Assessment ChecklistDokumen3 halamanNetwork Assessment ChecklistslasslasBelum ada peringkat
- IT Security PoliciesDokumen10 halamanIT Security Policiesapexauditsystem67% (3)
- SCCM Security ChecklistDokumen4 halamanSCCM Security Checklistnia17Belum ada peringkat
- IT Infrastructure MapDokumen16 halamanIT Infrastructure Mapnovember ag100% (3)
- Information Security Policy ChecklistDokumen2 halamanInformation Security Policy ChecklistRead Rule100% (6)
- Backup PolicyDokumen3 halamanBackup PolicypeacebabatundeBelum ada peringkat
- 11.IT Polcies-Internet Usage PolicyDokumen5 halaman11.IT Polcies-Internet Usage PolicyrajagopalansankarBelum ada peringkat
- ArmyTech ISMS PresentationDokumen25 halamanArmyTech ISMS Presentationlaliaga30100% (1)
- Disaster Recovery PolicyDokumen21 halamanDisaster Recovery PolicyLavhonte Antonio Davis50% (2)
- Customer Name Here: Technical Run Book Network DocumentationDokumen10 halamanCustomer Name Here: Technical Run Book Network DocumentationMyrvin FernandezBelum ada peringkat
- ISO 27001 - OperationsDokumen13 halamanISO 27001 - OperationsSasikala ManiBelum ada peringkat
- Firewall Policy: Prepared byDokumen8 halamanFirewall Policy: Prepared byChristine MbinyaBelum ada peringkat
- IT Security Policy Word TemplateDokumen29 halamanIT Security Policy Word Templateapi-373663686% (7)
- Information Security Policy DocumentDokumen84 halamanInformation Security Policy DocumentbendahlBelum ada peringkat
- InformationSecurityGuidelineV1 1Dokumen111 halamanInformationSecurityGuidelineV1 1Diego Fernando Quiceno CortesBelum ada peringkat
- Aquisition Assessment PolicyDokumen2 halamanAquisition Assessment PolicyConstantin TomaBelum ada peringkat
- IT Daily Activities ChecklistDokumen5 halamanIT Daily Activities Checklisterjem26350% (2)
- 03 Information Security and Acceptable Use of ICT Policy v3 0Dokumen16 halaman03 Information Security and Acceptable Use of ICT Policy v3 0proftechitspecialistBelum ada peringkat
- Network Documentation Series Network Sheets Template V0.0.0Dokumen42 halamanNetwork Documentation Series Network Sheets Template V0.0.0Javier Redome100% (1)
- 1 - Acceptable Usage Policy (00000002)Dokumen15 halaman1 - Acceptable Usage Policy (00000002)Shailkh YabaaBelum ada peringkat
- It PolicyDokumen4 halamanIt PolicyRoen AbeBelum ada peringkat
- 18 DataCenter Security OverviewDokumen22 halaman18 DataCenter Security Overviewrnaveed01Belum ada peringkat
- Firewall Audit Checklist WEBDokumen10 halamanFirewall Audit Checklist WEBBharti SangwanBelum ada peringkat
- Information Security Incident ManagementDokumen8 halamanInformation Security Incident ManagementcaliagarBelum ada peringkat
- FEWA - ISMS - Access Control Policy v1.10Dokumen13 halamanFEWA - ISMS - Access Control Policy v1.10tabishasifiBelum ada peringkat
- Network Documentation and NetdotDokumen37 halamanNetwork Documentation and NetdotislamBelum ada peringkat
- Security Incident Management ProcessDokumen8 halamanSecurity Incident Management ProcessHiren DhadukBelum ada peringkat
- Data Protection PolicyDokumen3 halamanData Protection PolicyHarsh DhamapurkarBelum ada peringkat
- Identity and Access Management OverviewDokumen53 halamanIdentity and Access Management OverviewSailesh Rao100% (2)
- Mobile Application & Cloud VA - PT Proposal - CashifyDokumen4 halamanMobile Application & Cloud VA - PT Proposal - CashifyApoorva AroraBelum ada peringkat
- Information Security PolicyDokumen16 halamanInformation Security PolicyCarlosMakkemFrangosBelum ada peringkat
- WP Creating Maintaining Soc PDFDokumen16 halamanWP Creating Maintaining Soc PDFgeo36Belum ada peringkat
- PR11 LogReviewProcedureDokumen7 halamanPR11 LogReviewProcedureThakur Narsing SinghBelum ada peringkat
- It Infrastructure ReportDokumen4 halamanIt Infrastructure ReportumarburneyBelum ada peringkat
- 10-Cisa It Audit - BCP and DRPDokumen27 halaman10-Cisa It Audit - BCP and DRPHamza NaeemBelum ada peringkat
- Information Classification and Management Policy TemplateDokumen6 halamanInformation Classification and Management Policy TemplateAhmed AlhassarBelum ada peringkat
- Cloud PoliciesDokumen19 halamanCloud Policiesisaptarshi100% (1)
- ISM3 and Its ObjectivesDokumen21 halamanISM3 and Its ObjectivesBendi Yashwanth0% (1)
- MBCF BIA Template FinalDokumen20 halamanMBCF BIA Template FinaldanirodigicomBelum ada peringkat
- Data Backup PolicyDokumen11 halamanData Backup PolicyOmar Carrillo Quiros0% (1)
- Cyber Security - Defense in DepthDokumen150 halamanCyber Security - Defense in DepthsivextienBelum ada peringkat
- 9-BCP DRPDokumen67 halaman9-BCP DRPRuppee Edward100% (1)
- Information Security PolicyDokumen169 halamanInformation Security PolicyKishor Kumar75% (4)
- Risk MGMT For CComputingDokumen24 halamanRisk MGMT For CComputingGeorge ReyesBelum ada peringkat
- Disaster Recovery Plan Template 02Dokumen34 halamanDisaster Recovery Plan Template 02ryandini fadhilah100% (1)
- Database Security RoadmapDokumen1 halamanDatabase Security Roadmapwaz32195Belum ada peringkat
- A Framerwork of SOCDokumen11 halamanA Framerwork of SOCrizaayhan0% (1)
- EY Security Operations Centers Helping You Get Ahead of CybercrimeDokumen20 halamanEY Security Operations Centers Helping You Get Ahead of Cybercrimeashish100% (1)
- Risk Assessment QuestionnaireDokumen36 halamanRisk Assessment Questionnairemnx4everBelum ada peringkat
- Password PolicyDokumen4 halamanPassword Policynoorulathar100% (2)
- Chapter 5 Incident Response and Business Continuity PDFDokumen74 halamanChapter 5 Incident Response and Business Continuity PDFandy_ipul100% (1)
- It Disaster Recovery PlanningDokumen14 halamanIt Disaster Recovery Planningtarnav86% (7)
- Windows Audit Part 3 - Tracing File Deletions - Michael FirsovDokumen6 halamanWindows Audit Part 3 - Tracing File Deletions - Michael FirsovsivextienBelum ada peringkat
- Enable Bullhorn Integration With EmailDokumen5 halamanEnable Bullhorn Integration With EmailsivextienBelum ada peringkat
- Doctoral Research Project ReportDokumen8 halamanDoctoral Research Project ReportsivextienBelum ada peringkat
- PowerShell CMD Line Conversion Guide ADDokumen4 halamanPowerShell CMD Line Conversion Guide ADManuel Pirez NunezBelum ada peringkat
- Threat and Risk Assessment TemplateDokumen30 halamanThreat and Risk Assessment TemplateMarija PetkovicBelum ada peringkat
- Tailoring ISMS For SMEsDokumen12 halamanTailoring ISMS For SMEssivextienBelum ada peringkat
- Cyber Security - Defense in DepthDokumen150 halamanCyber Security - Defense in DepthsivextienBelum ada peringkat
- Format Guidelines MDokumen17 halamanFormat Guidelines MsmsmbaBelum ada peringkat
- Fred Cohen 50 Ways SeriesDokumen64 halamanFred Cohen 50 Ways SeriessivextienBelum ada peringkat
- Well-Known SID in WindowsDokumen12 halamanWell-Known SID in WindowssivextienBelum ada peringkat
- Skills Assessment Guidelines For ApplicantsDokumen18 halamanSkills Assessment Guidelines For ApplicantsMukesh SharmaBelum ada peringkat
- Useful WMIC QueriesDokumen6 halamanUseful WMIC QueriessivextienBelum ada peringkat
- Cyber Forensic-Computer Security and Incident Response PDFDokumen11 halamanCyber Forensic-Computer Security and Incident Response PDFsivextienBelum ada peringkat
- Microsoft Dynamics GP 2013 - System Admin Guide PDFDokumen110 halamanMicrosoft Dynamics GP 2013 - System Admin Guide PDFsivextienBelum ada peringkat
- Alcatel OmiPCXDokumen192 halamanAlcatel OmiPCXlucian_vatamanuBelum ada peringkat
- Zenoss Core Seminar FinalDokumen28 halamanZenoss Core Seminar Finalparuz842487Belum ada peringkat
- gddr6 Sgram 8gb BriefDokumen22 halamangddr6 Sgram 8gb BriefВладимир ИльиновBelum ada peringkat
- Course Allocation For First Semester 2017/2018 SessionDokumen9 halamanCourse Allocation For First Semester 2017/2018 SessionlivityhotBelum ada peringkat
- En Rhel Deploy Oracle Rac Database 12c Rhel 7Dokumen50 halamanEn Rhel Deploy Oracle Rac Database 12c Rhel 7Alessandro SilveiraBelum ada peringkat
- WAG 9 GM Open 18.10.21Dokumen138 halamanWAG 9 GM Open 18.10.21Sahadeb DasBelum ada peringkat
- Flyback Using Microcontroller AN2122 MicrochipDokumen70 halamanFlyback Using Microcontroller AN2122 MicrochipCarlos Zevallos100% (1)
- Medium-Voltage Surge Arresters US - Catalog HP-AR 25 PDFDokumen47 halamanMedium-Voltage Surge Arresters US - Catalog HP-AR 25 PDFfrostssssBelum ada peringkat
- Python Class ConceptsDokumen16 halamanPython Class ConceptsPhoenix Liebe JeffBelum ada peringkat
- 23 Construction Schedule Templates in Word & ExcelDokumen7 halaman23 Construction Schedule Templates in Word & ExcelnebiyuBelum ada peringkat
- Grp03 Blinking MiniprojectDokumen3 halamanGrp03 Blinking MiniprojectYasin OmaryBelum ada peringkat
- Online Meeting With Clients: Project GuideDokumen16 halamanOnline Meeting With Clients: Project GuideGovindaram RajeshBelum ada peringkat
- 2021 Campus Selection Process & EligibilityDokumen1 halaman2021 Campus Selection Process & EligibilityNishant KumarBelum ada peringkat
- Tutorial 2 - 3Dokumen2 halamanTutorial 2 - 3Ahan TejaswiBelum ada peringkat
- Automation TestingDokumen20 halamanAutomation TestingmaryamBelum ada peringkat
- Custom YTD, PTD in Essbase FormulaDokumen11 halamanCustom YTD, PTD in Essbase Formulaegie72Belum ada peringkat
- T & C Fastener Co, LTD.: Certified Material Test ReportDokumen1 halamanT & C Fastener Co, LTD.: Certified Material Test Reportlady romeroBelum ada peringkat
- CBLM COMMON SMAW - PPE & ToolsDokumen13 halamanCBLM COMMON SMAW - PPE & ToolsESTRELLA PALERBelum ada peringkat
- IBM PowerVM Disk-Tape VirtualizationDokumen23 halamanIBM PowerVM Disk-Tape VirtualizationliuylBelum ada peringkat
- Flair SeriesDokumen2 halamanFlair SeriesSse ikolaha SubstationBelum ada peringkat
- Nguyenvanthinh BKC13107 N01Dokumen35 halamanNguyenvanthinh BKC13107 N01Văn thinh NguyenBelum ada peringkat
- Kmu Cat Rollnoslip 263112Dokumen1 halamanKmu Cat Rollnoslip 263112Saeed AkhtarBelum ada peringkat
- D1 - ModBus Device Importer - LABDokumen11 halamanD1 - ModBus Device Importer - LABGonzo MelaoBelum ada peringkat
- Note: Posted Transactions Until The Last Working Day Are ShownDokumen10 halamanNote: Posted Transactions Until The Last Working Day Are Shownsheikh usmanBelum ada peringkat
- HP-PreFab - Butterfly-DCDokumen9 halamanHP-PreFab - Butterfly-DCanbanandBelum ada peringkat
- Beginning CSharp Programming With Unity MonoDevelopDokumen586 halamanBeginning CSharp Programming With Unity MonoDevelopPanagiotisBelum ada peringkat
- IMN Installation ManualDokumen136 halamanIMN Installation Manualivan.liepalBelum ada peringkat
- Web Programming Lab Manual 2009Dokumen33 halamanWeb Programming Lab Manual 2009Kumar SaurabhBelum ada peringkat
- Practical Earthing Bonding Lightning and Surge ProtectionDokumen16 halamanPractical Earthing Bonding Lightning and Surge ProtectionAHMED YOUSEFBelum ada peringkat
- Sm-A405fn SVC Manual PDFDokumen116 halamanSm-A405fn SVC Manual PDFBojanBelum ada peringkat
- I Will Teach You to Be Rich: No Guilt. No Excuses. No B.S. Just a 6-Week Program That Works (Second Edition)Dari EverandI Will Teach You to Be Rich: No Guilt. No Excuses. No B.S. Just a 6-Week Program That Works (Second Edition)Penilaian: 4.5 dari 5 bintang4.5/5 (14)
- The Millionaire Fastlane, 10th Anniversary Edition: Crack the Code to Wealth and Live Rich for a LifetimeDari EverandThe Millionaire Fastlane, 10th Anniversary Edition: Crack the Code to Wealth and Live Rich for a LifetimePenilaian: 4.5 dari 5 bintang4.5/5 (90)
- Financial Intelligence: How to To Be Smart with Your Money and Your LifeDari EverandFinancial Intelligence: How to To Be Smart with Your Money and Your LifePenilaian: 4.5 dari 5 bintang4.5/5 (540)
- The Millionaire Fastlane: Crack the Code to Wealth and Live Rich for a LifetimeDari EverandThe Millionaire Fastlane: Crack the Code to Wealth and Live Rich for a LifetimePenilaian: 4.5 dari 5 bintang4.5/5 (2)
- Summary: The Psychology of Money: Timeless Lessons on Wealth, Greed, and Happiness by Morgan Housel: Key Takeaways, Summary & Analysis IncludedDari EverandSummary: The Psychology of Money: Timeless Lessons on Wealth, Greed, and Happiness by Morgan Housel: Key Takeaways, Summary & Analysis IncludedPenilaian: 5 dari 5 bintang5/5 (81)
- A Happy Pocket Full of Money: Your Quantum Leap Into The Understanding, Having And Enjoying Of Immense Abundance And HappinessDari EverandA Happy Pocket Full of Money: Your Quantum Leap Into The Understanding, Having And Enjoying Of Immense Abundance And HappinessPenilaian: 5 dari 5 bintang5/5 (159)
- Summary: Trading in the Zone: Trading in the Zone: Master the Market with Confidence, Discipline, and a Winning Attitude by Mark Douglas: Key Takeaways, Summary & AnalysisDari EverandSummary: Trading in the Zone: Trading in the Zone: Master the Market with Confidence, Discipline, and a Winning Attitude by Mark Douglas: Key Takeaways, Summary & AnalysisPenilaian: 5 dari 5 bintang5/5 (15)
- Rich Dad Poor Dad: What the Rich Teach Their Kids About Money That the Poor and Middle Class Do NotDari EverandRich Dad Poor Dad: What the Rich Teach Their Kids About Money That the Poor and Middle Class Do NotBelum ada peringkat
- Quotex Success Blueprint: The Ultimate Guide to Forex and QuotexDari EverandQuotex Success Blueprint: The Ultimate Guide to Forex and QuotexBelum ada peringkat
- Summary: The Gap and the Gain: The High Achievers' Guide to Happiness, Confidence, and Success by Dan Sullivan and Dr. Benjamin Hardy: Key Takeaways, Summary & AnalysisDari EverandSummary: The Gap and the Gain: The High Achievers' Guide to Happiness, Confidence, and Success by Dan Sullivan and Dr. Benjamin Hardy: Key Takeaways, Summary & AnalysisPenilaian: 5 dari 5 bintang5/5 (4)
- Summary of 10x Is Easier than 2x: How World-Class Entrepreneurs Achieve More by Doing Less by Dan Sullivan & Dr. Benjamin Hardy: Key Takeaways, Summary & AnalysisDari EverandSummary of 10x Is Easier than 2x: How World-Class Entrepreneurs Achieve More by Doing Less by Dan Sullivan & Dr. Benjamin Hardy: Key Takeaways, Summary & AnalysisPenilaian: 4.5 dari 5 bintang4.5/5 (24)
- Broken Money: Why Our Financial System Is Failing Us and How We Can Make It BetterDari EverandBroken Money: Why Our Financial System Is Failing Us and How We Can Make It BetterPenilaian: 5 dari 5 bintang5/5 (3)
- Summary of I Will Teach You to Be Rich: No Guilt. No Excuses. Just a 6-Week Program That Works by Ramit SethiDari EverandSummary of I Will Teach You to Be Rich: No Guilt. No Excuses. Just a 6-Week Program That Works by Ramit SethiPenilaian: 4.5 dari 5 bintang4.5/5 (23)
- Bitter Brew: The Rise and Fall of Anheuser-Busch and America's Kings of BeerDari EverandBitter Brew: The Rise and Fall of Anheuser-Busch and America's Kings of BeerPenilaian: 4 dari 5 bintang4/5 (52)
- You Can't Joke About That: Why Everything Is Funny, Nothing Is Sacred, and We're All in This TogetherDari EverandYou Can't Joke About That: Why Everything Is Funny, Nothing Is Sacred, and We're All in This TogetherBelum ada peringkat
- Sleep And Grow Rich: Guided Sleep Meditation with Affirmations For Wealth & AbundanceDari EverandSleep And Grow Rich: Guided Sleep Meditation with Affirmations For Wealth & AbundancePenilaian: 4.5 dari 5 bintang4.5/5 (105)
- Rich Bitch: A Simple 12-Step Plan for Getting Your Financial Life Together . . . FinallyDari EverandRich Bitch: A Simple 12-Step Plan for Getting Your Financial Life Together . . . FinallyPenilaian: 4 dari 5 bintang4/5 (8)
- The Holy Grail of Investing: The World's Greatest Investors Reveal Their Ultimate Strategies for Financial FreedomDari EverandThe Holy Grail of Investing: The World's Greatest Investors Reveal Their Ultimate Strategies for Financial FreedomPenilaian: 5 dari 5 bintang5/5 (8)
- The 4 Laws of Financial Prosperity: Get Conrtol of Your Money Now!Dari EverandThe 4 Laws of Financial Prosperity: Get Conrtol of Your Money Now!Penilaian: 5 dari 5 bintang5/5 (389)
- Love Money, Money Loves You: A Conversation With The Energy Of MoneyDari EverandLove Money, Money Loves You: A Conversation With The Energy Of MoneyPenilaian: 5 dari 5 bintang5/5 (40)
- Fluke: Chance, Chaos, and Why Everything We Do MattersDari EverandFluke: Chance, Chaos, and Why Everything We Do MattersPenilaian: 4.5 dari 5 bintang4.5/5 (20)
- Financial Literacy for All: Disrupting Struggle, Advancing Financial Freedom, and Building a New American Middle ClassDari EverandFinancial Literacy for All: Disrupting Struggle, Advancing Financial Freedom, and Building a New American Middle ClassBelum ada peringkat
- Passive Income Ideas for Beginners: 13 Passive Income Strategies Analyzed, Including Amazon FBA, Dropshipping, Affiliate Marketing, Rental Property Investing and MoreDari EverandPassive Income Ideas for Beginners: 13 Passive Income Strategies Analyzed, Including Amazon FBA, Dropshipping, Affiliate Marketing, Rental Property Investing and MorePenilaian: 4.5 dari 5 bintang4.5/5 (165)
- Meet the Frugalwoods: Achieving Financial Independence Through Simple LivingDari EverandMeet the Frugalwoods: Achieving Financial Independence Through Simple LivingPenilaian: 3.5 dari 5 bintang3.5/5 (67)
- The House at Pooh Corner - Winnie-the-Pooh Book #4 - UnabridgedDari EverandThe House at Pooh Corner - Winnie-the-Pooh Book #4 - UnabridgedPenilaian: 4.5 dari 5 bintang4.5/5 (5)
- Unshakeable: Your Financial Freedom PlaybookDari EverandUnshakeable: Your Financial Freedom PlaybookPenilaian: 4.5 dari 5 bintang4.5/5 (618)