203 Module 2 Wireless Controller
Diunggah oleh
zarandijaHak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
203 Module 2 Wireless Controller
Diunggah oleh
zarandijaHak Cipta:
Format Tersedia
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Fortinet Wireless Course 203
Module 2 Wireless Controller
2012 Fortinet Training Services. This training may not be recorded in any medium, disclosed, copied, reproduced or distributed to anyone without prior written consent of an authorized representative of Fortinet.
Objectives List the components and advantages of the FortiGate integrated wireless controller and the wireless solution Identify the key configuration requirements of an SSID Describe the purpose of the Virtual Access Point in the FortiOS configuration Describe the configuration of security and authentication settings for a wireless LAN Identify the purpose of MAC filtering Identify the managed AP topologies Identify the goals and describe the main phases of the CAPWAP protocol
2
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Objectives Describe the basic access point configuration settings for a simple wireless LAN deployment Perform a wireless network deployment using equipment in a handshands on lab
The Fortinet WiFi Security Solution
Secure Access Points
802.11n compliant Up to 900 Mbps throughput (aggregated traffic)
3x3 MIMO with 3 spatial streams : 450 Mbps / Radio or 2x2 MIMO with 2 spatial streams : 300 Mbps / Radio
Single or Dual concurrent radio 2.4GHz/5GHz
802.11 a/b/g/n
FortiAP Secure AP Single or Dual Radio
Enterprise-Class feature set Dedicated built-in in air monitoring Internal or External Antenna design Highest value at competitive price
FortiGates as Controllers
20+ platforms to meet any requirement Leverages same models already on the market 10Mbps 40Gbps wireless LAN Capacity Programmable control & data planes, Hardware-based Cryptography Centralized management
FortiGate Platforms With Integrated Wireless Controllers
4
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Building the Secure Business Grade Wireless LAN
Secure Wireless Access Points
Infrastructure Security with Integrated Wireless Controller
Business Grade Wireless
Secure Business Grade Wireless
No additional licenses needed
Captive Portal, 802.1xRadius /shared key Assign users and devices (BYOD) to their role
Corporate Wi-Fi
Examines wireless traffic to remove threats Identify applications and destinations of interest True stateful firewall controls users/applications pp Ensures Business traffic has right of way Reports on policy violations, application usage, destinations and PCI DSS
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Extends Security Features to Wi-Fi
Each SSID appears as a Virtual Interface
Thin and Thick APs
FortiWiFi
Standalone Thick AP WiFi radio physically integrated into FortiGate device One WiFi Radio - targeted as AP with background scan or dedicated rogue AP monitor IEEE 802.11 a/b/g/n on 60,80 Runs full FortiOS with VPN Ideal for distributed office Space < 300 sq meters
FortiAP Models
Centrally Managed Thin AP Requires separate FortiGate as wireless controller Single or Dual WiFi radio for simultaneous communication on 2.4Ghz and 5Ghz bands or Simultaneous Air Monitor and AP or Mesh a/b/g/n bands standard Runs thin OS Ideal for larger indoor or outdoor installations, or existing customers looking for WiFi capability from existing FortiGates
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
802.11n Thin AP family
3x3:3 Dual Radio Dual Band
Resiliency Throughput
FAP-320B FAP-223B FAP-222B FAP-221B FAP-220B Singl le Radio
2x2:2
Performance
FAP-210B
1x1:1
FAP-11C Personal
9
FAP-112B Outdoor Indoor
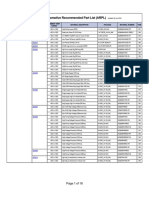
Hardware Overview FortiAP (Local)
FAP-112B Wall mount, Ceiling Mount, indoor/outdoor 1 FAP-210B Wall mount, Ceiling Mount 1 1) 2.4 or 5Ghz, switchable b/g/n or a/n 802.3af 1x2, Single stream, 300 Mbps 2 internal 1x GbE Copper FAP-220B Wall mount, Ceiling Mount 2 1) 2.4 Ghz b/g/n 2) 2.4/5GHz a/b/g/n concurrent 802.3af 2x2 Dual stream, 600Mbps 4 internal 1x GbE Copper FAP221B/223B* Smoke Detector Form Factor 2 1) 2.4 Ghz b/g/n 2) 2.4/5GHz a/b/g/n concurrent 802.3af 2x2 Dual stream, 600Mbps 4 internal 4 external* 1x GbE Copper FAP-222B FAP-320B Wall mount, Ceiling Mount 2 1) 2.4 Ghz b/g/n 2) 2.4/5GHz a/b/g/n concurrent 802.3af 3x3 Triple stream, 900Mbps 6 internal 2x GbE Copper
Form Factor Radio
Outdoor 2 1) 2.4 Ghz b/g/n 2) 5GHz a/n concurrent
Bands
2.4 Ghz b/g/n
PoE Rx / Tx Antennas Ethernet Interfaces
802.3af 1x1, Single stream, 65 Mbps 1 internal 2x FE (one LAN and one WAN)
802.3at 2x2 Dual stream, 600Mbps 4 external 1x GbE Copper
10
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Hardware Overview FortiAP (Remote)
FAP-11C FAP-14C Desktop/Wall mount 1 2.4 Ghz b/g/n FAP-28C Desktop/Wall mount 1 2.4 or 5Ghz, switchable b/g/n or a/n NA 2x2 Dual stream, 2 internal 10x GE
Form Factor Radio Bands PoE Rx / Tx Antennas Ethernet Interfaces
Wall Plug 1 2.4 Ghz b/g/n
NA 1x1, Single stream, 65 Mbps 1 internal 2x FE
NA 1x1, Single stream, 65 Mbps 1 internal 5x FE
FAP-11C
11
FAP-14C
FAP-28C
Wireless Controller Configuration Make sure the FortiGate wireless controller is configured for your geographic location Optionally configure a custom Access Point (AP) profile Configure one or more SSIDs for your wireless network Optionally, configure the user group and users for authentication on the WLAN Configure the firewall policy for the WLAN p y, customize the captive p p portal Optionally, Configure access points.
12
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Wireless Controller Configuration
Security Settings
Virtual Access Point 1
Virtual Access Point 2
Radio Settings
Access Point Profile 1
Physical Access Point Units
13
Configuring SSIDs The Virtual Access Point (VAP) interface is the interface used for traffic tunneled back to the wireless controller and it includes network settings of the interface. interface
14
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Configuring SSIDs The SSID defined is associated with the VAP interface created.
Security mode of the SSID is defined here.
15
Security Mode Wi-Fi Protect Access (WPA)
Provides two methods of authentication:
802.1X 802 1X (WPA-Enterprise) (WPA Enterprise) Pre-shared keys (WPA-Personal)
Encrypt communications
Advance Encryption Standard (AES) Temporal Key Integrity Protocol (TKIP)
WPA2 provides additional security improvements
Captive Portal WEP
Weak hence CLI only.
16
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Wireless Authentication Authentication methods apply to wireless networks the same as they do for wired
User can also be authenticated against local user groups on FortiGate device External authentication servers (RADIUS, LDAP and TACAS+, Windows Active Directory) also available For each wireless LAN, create a user group(s) and add the users who can access the WLAN
17
MAC Filtering Permit or exclude a list of clients based on the MAC address of their computer Should be used in conjunction with other security measures
Unauthorized users could capture MAC addresses from network traffic and use them to impersonate legitimate users
Configured on a SSID/VAP interface basis Used for devices that cannot perform a user authentication, such as a printer or a games console
18
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Virtual Access Points (VAP) A Virtual Access Point defines the security settings that can be applied to one or more physical Access Points Each VAP creates its own a virtual network interface on the FortiGate unit Define DHCP services, firewall policies and other settings for the wireless LAN
19
Virtual Access Point An SSID creates a Virtual Interface of type VAP
This interface can then be used for firewalling, traffic inspection ,QoS,
20
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Intra-SSID Privacy This feature benefits Hotspot users by keeping their traffic private from other users on the same SSID Prevents Man-in-middle Man in middle attacks from other PCs on the same network Undesirable when you have other devices in the SSID you connect to, such as a wireless printer
21
Managed AP Topologies Direct Connection
FortiAP unit is connected directly to the FortiGate unit
Switched Connection
FortiAP unit is connected to the wireless controller on the FortiGate unit by an Ethernet switch Must be a routable path between FortiAP device and the FortiGate unit
Distributed
WLAN mesh model WTP repeat traffic over wireless neighbor nodes
Connection over WAN
The wireless controller is off-site and connected by a VPN to a local AP
22
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Full Mesh
23
Full Mesh LAN Bridge
24
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Full Mesh Mesh SSID replaces wired distribution network between root and leaf APs
Usually backhaul SSID uses a dedicated radio but shared radio is also supported Default SSID fortinet.mesh.vdom The mesh SSID is bridged with the Ethernet port on the root AP
The root AP has a wired connection back to the wireless controller When tunneling traffic back to the FortiGate the leaf APs use the mesh SSID to reach the controller.
25
Full Mesh Automatically created VAP interface and SSID that is dedicated to the backhaul The mesh SSID is enabled on an AP then it will accept requests from other APs configured to use it Wireless clients cannot connect to the mesh-backhaul SSID The default mesh SSID may be deleted and replaced with a new configuration.
26
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Full Mesh AP uplink options
27
Local Bridge Local bridge mode allows SSIDs to be centrally managed without backhauling the traffic to the wireless controller Traffic from the wireless is bridged to the local Ethernet port
VLAN support increases number of bridges from one
Configured per SSID
Bridge and tunnel mode SSIDs on same AP supported
Configured in the Managed AP settings
Local bridge, no DHCP settings in SSID, local DHCP required
Also it is possible to bridge an SSID to local port at the FortiGate device using a softswitch configuration
28
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Local Bridge Local bridge SSID configuration
29
Local Bridge Traffic Flow
edit "SSID-bridge" set vdom "root" set ssid "SSIDBridge" set security wpa-enterprise set auth radius set encrypt TKIP-AES set radius-server radius server "FortiAuth" FortiAuth set local-bridging enable
30
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Local Bridge With VLAN Support
31
Discover and Authorize FortiAP Configure the FortiGate ethernet interface to which the AP will connect Configure DHCP service on the interface to which the AP will connect, if providing APs addresses via DHCP The AP requires its own address, independent of any wireless device connecting to the VAP (SSID) Connect the AP units and let the FortiGate unit discover them Authorize each discovered AP if you want to manage it from that controller, edit to change its automatic settings or create a custom AP profile.
32
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Controller Discovery Broadcast request
Controller and AP in same broadcast domain
Multicast request
Controller and AP do not need to in the same broadcast domain if multicast routing is configured The default multicast destination IP address is 224.0.1.140
Static IP address
Administrator specifies the controllers static IP address on the FortiAP unit Routing must be configured in both directions
DHCP
Identifies controller address when APs IP address is assigned Useful when the AP is on a remote site IP address of the controller must be converted into hexadecimal in the DHCP option field
33
Configuring FortiAP using CLI The FortiAP unit has a CLI through which some configuration options can be set Login with user name admin and no password Display help
cfg h
Make a configuration change
cfg a
Save the configuration g
cfg c
34
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
CAPWAP Wireless Controller and FortiAP Configuration A FortiAP unit can use any of four methods to locate a controller By default, FortiAP units cycle through all four of the discovery method In I most t cases th there iis no need d to t make k configuration fi ti changes h on the th FortiAP unit The next few slides look at these four methods.
35
Static IP By default, the FortiAP unit receives its IP address by DHCP
You can assign the AP unit a static IP address. To assign a static IP address to the FortiAP unit
cfg -a ADDR_MODE=STATIC cfg a AP_IPADDR="192.168.0.100" cfg -a AP_NETMASK="255.255.255.0
The AP unit sends a unicast discovery request message to the controller
Routing must be properly configured in both directions. directions To specify the controllers IP address on a FortiAP unit:
cfg a AC_IPADDR_1="192.168.0.1
36
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Broadcast The AP unit broadcasts a discovery request message to the network and the controller replies The AP and the controller must be in the same broadcast domain domain. No configuration adjustments are required.
37
Multicast The AP unit sends a multicast discovery request and the controller replies with a unicast discovery response message The AP and the controller do not need to be in the same broadcast domain if multicast routing is properly configured The default multicast destination address is 224.0.1.140
It can be changed through the CLI The address must be same on the controller and AP.
38
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Multicast To change the multicast address on the controller
config wireless-controller global set discovery-mc-addr discovery mc addr 224.0.1.250 224 0 1 250 end
To change the multicast address on a FortiAP unit
cfg a AC_DISCOVERY_MC_ADDR="224.0.1.250"
39
DHCP If you use DHCP to assign an IP address to your FortiAP unit, you can also provide the WiFi controller IP address at the same time. When you configure the DHCP server, server configure Option 138 to specify the WiFi controller IP address. You need to convert the address into hexadecimal. Convert each octet value separately from left to right and concatenate them.
For example, 10.10.10.31 converts to 0A0A0A1F.
40
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
DHCP If Option 138 is used for some other purpose on your network, you can use a different option number if you configure the AP units to match. To change the FortiAP DHCP option code
To use option code 139 for example, enter cfg a AC_DISCOVERY_DHCP_OPTION_CODE=139
41
DHCP
42
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
Configuring FortiAP using CLI
43
Configuring FortiAP using CLI
44
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
FortiAP GUI Simplified provisioning for FortiAP with the addition of a GUI
45
Configuring a FortiWiFi unit as a WiFi AP FortiWiFi running FortiOS 4.3 units can also be deployed as managed APs controlled by a FortiGate unit wireless controller.
In the CLI, CLI enter:
config system global set wireless-mode wtp end
The feature was removed in FortiOS 5.0 Unlike FortiAP units, a FortiWiFi unit deployed as an AP does not cycle through y methods. You must select one discovery y method to use. the discovery
config wireless-controller global set ac-discovery-type dhcp
46
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
CAPWAP Protocol Overview The CAPWAP protocol is a generic protocol defining AC (Wireless Controller) and WTP (FortiAP) control and data plane communication via a CAPWAP protocol transport mechanism CAPWAP stands for Control and Provisioning of Wireless Access Points CAPWAP carries control and data traffic via two channels CAPWAP Control messages, and optionally CAPWAP Data messages, are secured using Datagram Transport Layer Security (DTLS) (DTLS).
47
Goals of CAPWAP Centralize the authentication and policy enforcement functions for a wireless network Reduced cost and increase efficiency by applying the capabilities of network processing to the wireless network Move higher-level protocol processing from the WTP (FortiAP) Leave the time-critical applications of wireless control and access in the WTP (FortiAP) The emergence of centralized IEEE 802.11 Wireless Local Area Network (WLAN) architectures Simple IEEE 802.11 WTPs are managed by an Access Controller (FortiOS Wireless Controller).
48
01-05002-RevA-0203-20130520
Course 203 - Fortinet Wireless
Module 2 Wireless Controller
CAPWAP Main Phases
FortiAPs send a discovery request message Any Wireless Controller receiving the message responds with a discovery response message
CAPWAP begins with a discovery phase
The Wireless Controller and FortiAP exchange is complete and the FortiAP is enabled
Configuration exchange occurs
FortiAP may receive provisioning settings FortiAP is enabled for operation
FortiAP selects a Wireless Controller and establishes a secure DTLS session
In tunnel mode client data frames are encapsulated between the FortiAP and the Wireless Controller
49
Lab FortiGate Secure Wireless Configuration using a FortiAP Device
50
01-05002-RevA-0203-20130520
Anda mungkin juga menyukai
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- 8259a Programmable Interrupt ControllerDokumen42 halaman8259a Programmable Interrupt ControllerzarandijaBelum ada peringkat
- HP MSM775 ZL Controller Installation GuideDokumen21 halamanHP MSM775 ZL Controller Installation GuidezarandijaBelum ada peringkat
- 203 Module 5 Custom AP ProfilesDokumen10 halaman203 Module 5 Custom AP Profileszarandija100% (1)
- 203 Module 3 Device IdentificationDokumen9 halaman203 Module 3 Device IdentificationzarandijaBelum ada peringkat
- 203 Lab GuideDokumen17 halaman203 Lab GuidezarandijaBelum ada peringkat
- CatOS To IOS Conversion Catalyst 6500kDokumen46 halamanCatOS To IOS Conversion Catalyst 6500kzarandijaBelum ada peringkat
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- Create DVDrip Like aXXo HowtoDokumen11 halamanCreate DVDrip Like aXXo Howtodonnlee100% (1)
- Peerless-AV LG Solutions UK Oct19Dokumen12 halamanPeerless-AV LG Solutions UK Oct19Hannah EmeryBelum ada peringkat
- 2-Accessories 23 July 2020Dokumen6 halaman2-Accessories 23 July 2020MohamedMahmoudBelum ada peringkat
- Mi TV Bar: AccessoriesDokumen5 halamanMi TV Bar: Accessoriesnitin9860Belum ada peringkat
- Jetspeed Iad Wp2 (SR)Dokumen59 halamanJetspeed Iad Wp2 (SR)akcija_npstefan0% (2)
- Eguide-SDN Line RateDokumen9 halamanEguide-SDN Line RateyassyboyBelum ada peringkat
- GN4-1-SA8T2 Tech Scout - WebRTC2SIP-Gateway - V1.0-FinalDokumen19 halamanGN4-1-SA8T2 Tech Scout - WebRTC2SIP-Gateway - V1.0-FinalMakarius YuwonoBelum ada peringkat
- Codigos ScarlletDokumen4 halamanCodigos ScarlletOsmar BorgesBelum ada peringkat
- 3..optical Packet Switching NetworkDokumen28 halaman3..optical Packet Switching NetworkAnkit MishraBelum ada peringkat
- Author's Complete Style GuideDokumen3 halamanAuthor's Complete Style GuideJaime Humberto Pech CarmonaBelum ada peringkat
- DR6000 MK2 Diversity Receiver Manual, Installation & OperationDokumen39 halamanDR6000 MK2 Diversity Receiver Manual, Installation & Operationoscar horacio floresBelum ada peringkat
- ARPLDokumen18 halamanARPLLily SternBelum ada peringkat
- S1500 MS v00 PDFDokumen140 halamanS1500 MS v00 PDFPhotocopy Sửa Máy PhotocopyBelum ada peringkat
- Computer Science (Elec)Dokumen4 halamanComputer Science (Elec)haaldayBelum ada peringkat
- Samsung ML-1710 Recarga PDFDokumen6 halamanSamsung ML-1710 Recarga PDFarkittoBelum ada peringkat
- DP Sound ADI 15025 DriversDokumen218 halamanDP Sound ADI 15025 DriversJuan Carlos Gonzalez LBelum ada peringkat
- AMC QuotationDokumen3 halamanAMC QuotationSandeep SoniBelum ada peringkat
- Basic Troubleshoot Guide To PrintersDokumen5 halamanBasic Troubleshoot Guide To PrintersCheska LorenaBelum ada peringkat
- Digital Transmission: Solutions To Review Questions and ExercisesDokumen11 halamanDigital Transmission: Solutions To Review Questions and ExercisesAq RaufBelum ada peringkat
- Xerox WorkCentre 7120 7125 System Administrator GuideDokumen160 halamanXerox WorkCentre 7120 7125 System Administrator GuidetangocharliepdxBelum ada peringkat
- DH-SD29204T-GN: 2MP 4x IR PTZ Network CameraDokumen3 halamanDH-SD29204T-GN: 2MP 4x IR PTZ Network Camerakakyo29433Belum ada peringkat
- LG DS325b-Dx325b Rev02Dokumen86 halamanLG DS325b-Dx325b Rev02Fabi PX0% (1)
- Avid Codecs 2.3.7 Download: Codec PackagesDokumen5 halamanAvid Codecs 2.3.7 Download: Codec PackagesjairmrfBelum ada peringkat
- 415 01 PDFDokumen19 halaman415 01 PDFTuan TranBelum ada peringkat
- The ZX Spectrum On Your PC - Second EditionDokumen206 halamanThe ZX Spectrum On Your PC - Second Editionmuie11219569100% (1)
- PrepLogic CCNA Mega GuideDokumen182 halamanPrepLogic CCNA Mega GuideArturo Sierra100% (1)
- Ch05 - Multimedia Element-SoundDokumen40 halamanCh05 - Multimedia Element-Soundsu6a100% (3)
- 1BC58Dokumen2 halaman1BC58Carlos Jose SantanaBelum ada peringkat
- LG 32LC51Dokumen93 halamanLG 32LC51Gabor CsehiBelum ada peringkat
- Kyocera 3035-4035-5035 Firmware Bulletin R22Dokumen50 halamanKyocera 3035-4035-5035 Firmware Bulletin R22iageekBelum ada peringkat