Quality of Service in WSNs - 17042006
Diunggah oleh
Khizar SalmanDeskripsi Asli:
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Quality of Service in WSNs - 17042006
Diunggah oleh
Khizar SalmanHak Cipta:
Format Tersedia
1
Quality of Service in Wireless Sensor Networks
Hwee-Xian Tan hweexian@comp.nus.edu.sg Department of Computer Science National University of Singapore
Abstract Wireless Sensor Networks (WSNs) comprise of groups of tiny sensor nodes that are deployed for collaborative missions such as environmental monitoring, target tracking and surveillance. Due to the miniature size of the nodes, they are typically deployed in large numbers and communicate via multiple hops through a wireless shared communication channel. The successful implementation of such networks is dependent on the enabling technologies (such as digital electronics and wireless communications), as well as the provisioning of Quality of Service (QoS) in the network. While there have been many efforts in QoS provisioning in traditional networks such as the Internet and Mobile Ad Hoc Networks (MANETs), these networks have very different characteristics from that of WSNs. Consequently, the QoS models and protocols that have been designed for the Internet and MANETs cannot be directly applied to WSNs. In this paper, we look at some of the existing QoS mechanisms in the networking literature, and the inherent characteristics of WSNs which make it challenging to provision for QoS in the network. We then identify some key performance metrics for WSN QoS and outline some mechanisms to achieve QoS in the sensor network. Finally, we propose WISER a framework to enhance QoS in WIreless SEnsoR networks. Index Terms Wireless Sensor Networks, Quality of Service, Network Lifetime, Coverage, Spatial Accuracy, Delay, Topology Management.
I. INTRODUCTION
Wireless Sensor Networks (WSNs) are envisioned to be the next generation of networks which will form an integral part of mans lives. The sensor nodes are usually small in size, with multi-modal sensing capabilities which allows them to collect raw data of various physical parameters such as temperature, salinity, humidity, light intensity, pressure, sound, radiation, etc. They are equipped with wireless interfaces, enabling them to communicate with each other via multiple hops using Radio Frequency (RF) techniques. Due to the miniature size of these nodes, sensor networks can be densely deployed in a distributed manner in any terrain; therefore the
nodes need to have self-organizing and self-configuring capabilities, as like in ad hoc networks. With advances in wireless communications, the applications of sensor networks are no longer limited to that of periodic monitoring of the environment. Wireless sensor networks can be used for a wide array of applications spanning multiple domains healthcare, biometrics, home networking, military, automotives, as well as construction and manufacturing industries. The sensor nodes typically obtain raw data from the environment in which they are deployed, and then send the collected information back to a centralized sink (or repository) where more complex processing and real-time analysis can be performed on the data. In some heterogeneous network which have actuators (also known as SANETs Sensor and Actuator NETworks), the collated data may be used to trigger the actuators in the network to perform some form of collaborative missions or tasks. Hence, sensor networks can now be used for the following purposes: (i) data acquisition the collection of data from the environment; (ii) data dissemination the delivery of information to other nodes in the network; (iii) data distribution the delivery of information or instructions from the centralized sink to one or more sensor nodes in the network; and (iv) M2M (Machine-to-Machine) communication [1] the provision of a platform for interactions between machines and the environment, without unnecessary human intervention. The successful implementation and deployment of such intelligent wireless sensor networks requires several enabling technologies, such as Micro-Electro-Mechanical Systems (MEMS), digital electronics and wireless communications [2], as well as the provisioning of Quality of Service (QoS) support to the applications that run on top of the network. While different applications may have specific QoS requirements, some of the more commonly used QoS metrics used to measure network performance are delay, throughput, bandwidth and efficiency
of the protocol in use. There has been much effort invested into QoS support in the Internet and MANETs (Mobile Ad Hoc NETworks) within the last decade, leading to the proliferation of Internet QoS models such as Integrated Services (IntServ) [3] and Differentiated Services (DiffServ) [4], and MANET QoS models such as the Flexible QoS Model for MANETs (FQMM) [5] and integrated MANET QoS (iMAQ) model [6]. However, as these networks have fundamentally different characteristics from that of wireless sensor networks, the protocols and algorithms that are used to provide QoS in the Internet and MANETs cannot be directly applied to sensor networks. In addition, in such networks with higher resource availability and predictability, providing QoS beyond best effort is already a challenge. It is therefore even more difficult to achieve QoS in wireless sensor networks, which have unpredictable and limited resources. In this paper, we first take a look at the various QoS mechanisms that exist today, and present an overview of the challenges and issues that exist in the deployment of wireless sensor networks. We then look at the how QoS can be achieved in these networks which are characterized by multi-hop communications, dynamic environments and limited resources. The rest of this paper is organized as follows: The next section describes the related work and the motivation for QoS provisioning in WSNs. Section III details the multi-faceted challenges involved when considering QoS support in wireless sensor networks. Section IV presents some of the key performance metrics that can be used in WSN QoS and outlines some mechanisms which can be used to achieve QoS in the network. In Section V, we propose WISER, which is a framework to enhance QoS in WIreless SEnsoR networks. We conclude with directions for future work in Section VI.
II. RELATED WORK AND MOTIVATION
There is evidence of increasing research efforts in QoS provisioning in the networking literature; however, majority of the related work are targeted at cellular mobile telephony, wired Internet and MANETs. A few definitions for QoS in varying networks have also emerged in recent years Crawley et al in [6] define QoS (in the Internet) as a set of service requirements to be met by the network, while transporting a flow while Nikaein et al in [8] propose that QoS (in a MANET) is the provision of a set of parameters in order to adapt the applications to the quality of the network while routing them through the network. Despite the slightly varying definitions that have been proposed for different types of networks, the QoS of any particular network can generally be considered to be its ability to deliver a guaranteed level of service to its users and/or applications. The service requirements can be specified in the form of performance metrics, which are typically computed in one of the three following ways: (i) concave (e.g. minimum bandwidth along each link); (ii) additive (e.g. total delay along a path); and (iii) multiplicative (e.g. packet delivery ratio along the entire route). Although some performance metrics such as throughput, delay, jitter (delay variance), bandwidth, packet delivery ratio (PDR), reliability, etc are more widely used than other metrics, each application has its own unique set of service parameters to be satisfied, while possibly compromising on other sets of metrics. Loss-tolerant applications such as multimedia applications are not adversely affected by occasional data loss, but are highly sensitive to delay and bandwidth. In contrast, other applications involving sensitive data integrity, such as electronic mail and banking transactions, require fully reliable data transfer, but may not require stringent delay constraints and can work with elastic bandwidth.
A. Existing QoS Mechanisms
The existing QoS mechanisms can be classified into two main categories: (i) resource reservation; and (ii) traffic classification. In resource reservation, network resources such as bandwidth are allocated according to the QoS requirements of the application. This necessitates the presence of a signaling or handshaking protocol such as RSVP [9], to reserve the required resources in each node along the path of the data packet, before the application is actually allowed to run. In addition, a call admission control protocol such as that proposed by Iraqi and Boutaba in [10] which regulates the permissible number of connections that can be allowed into the system while still fulfilling the QoS requirements of the application is required. Traffic classification involves the categorization of data packets into different levels of priority, or classes of service (CoS), based on the application requirements. These data packets are marked with their respective classes at the edge of the network, and preferential treatment is then given to the traffic classes with higher priority as they pass through each hop along the path. Traffic prioritization can be in the form of congestion management schemes such as scheduling [11], congestion avoidance or rate limiting. In general, data packets with lower priority are usually dropped at a higher rate than those with higher priority; this allows data flows with higher priority to have better QoS performance metrics such as reliability, end-to-end delay and throughput.
B. QoS Provisioning in the Internet
There are currently two Internet QoS models: 1) Integrated Services (IntServ): IntServ provides per-flow end-to-end guarantees through resource reservation mechanisms [3]. It is a service model that incorporates best effort service,
real-time service and controlled link sharing into the basic Internet architecture. IntServ is realized via a framework comprising of four components: (i) packet scheduler; (ii) admission control routine; (iii) classifier; and (iv) reservation protocol. Due to the large amount of state information that is required to be stored, IntServ is hardly scalable and therefore not suitable for use in distributed and autonomous systems like wireless sensor networks. 2) Differentiated Services (DiffServ): DiffServ provides per-class service differentiation via traffic differentiation and prioritization [4]. Services and applications are classified in a simple and coarse method, thus avoiding the scalability problem that is inherent in IntServ. A traffic prioritization mechanism is used to classify network traffic into different classes of service, and preferential treatment is allocated to classes that are identified as having more stringent requirements. Per-flow state and other sophisticated classifications, marking, policing and shaping operations are pushed to the network edge. Each data packet is treated on an aggregate basis, which is also known as the Per-Hop-Behavior (PHB).
C. QoS Provisioning in MANETs
Mobile Ad Hoc Networks (MANETs) are a class of multi-hop networks with self-organizing and self-configuring properties. There is neither central administration nor fixed infrastructure in the network; each node acts as both a host and a router to forward packets to other nodes in the network. The current Internet QoS models such as IntServ are unsuitable for use in MANETs because of the vast differences in characteristics between the two types of networks. Due to the mobility of the nodes in a MANET, as well as the inherent erratic behavior of the wireless channel, MANETs are characterized by dynamic topology, complex route maintenance, temporal link connectivity as well as unpredictable and varying resource availability [12][13]. Consequently, QoS provisioning in MANETs is a multi-faceted problem which requires the
cooperation and integration of the various networking layers [14], viz. physical layer, Medium Access Control (MAC) layer, network layer, transport layer and application layer. The existing developments in MANET QoS can be broadly classified into QoS models, QoS resource reservation signaling, QoS routing and QoS MAC.
D. QoS Provisioning in WSNs
Wireless sensor networks have been envisioned for a wide range of applications, some of which may involve the collection of sensitive or critical data. For example, if underwater sensor nodes are thrown into the sea to monitor seismic activities and forewarn the possible occurrence of an earthquake or tsunami, the sensor network is not very useful if it is unable to inform the sink in time, on the impending natural disaster. Although delay is not a very crucial factor in sensor network applications such as periodic monitoring, shorter delays will nevertheless, be much desired over higher delays. Future WSNs may also be able to capture videos or snapshots of the physical environment and transmit these images (or videos) back to the sink for real-time data analysis. As such, there is a demand for QoS support in WSNs; however, existing Internet QoS and MANET QoS mechanisms are not directly applicable to WSNs due to the difference in the characteristics of such networks. In addition, there is currently no standardization in the networking community, on a framework and/or general guidelines on how QoS can be achieved in WSNs. This motivates the need for more research work and efforts in QoS provisioning in WSNs.
III. WIRELESS SENSOR NETWORKS CHARACTERISTICS, ISSUES AND CHALLENGES
In this section, we describe some of the unique characteristics of wireless sensor networks which make them different from conventional wireless ad hoc networks. We then look into some of the issues and challenges that are involved in the deployment of sensor networks.
A. Network Characteristics
1) Autonomous: As like ad hoc networks, sensor networks can be deployed in an autonomous manner without the need for existing infrastructure. They can be set up anytime, anywhere without the need for any central administration. As such, each node in the network has to act both as a host, as well as a router to forward data packets to the sink (or other nodes in the network). 2) Dense and random deployment: Due to the tiny size of the sensor nodes and the nature of the applications, the network is expected to be quite densely and randomly deployed, covering several hundreds or even thousands of sensor nodes in the terrain. As compared to ad hoc nodes which typically have 4-8 neighbours, each sensor node can have up to tens of neighbours [15]. Consequently, there is also higher spatial correlation among the nodes as more than one node will be sensing the same physical phenomenon or event. 3) Limited resources: As sensor nodes are typically small in size and battery-powered, they have limited processing power, memory storage and energy supply. In addition, as these nodes are usually deployed in hostile or unreachable terrains, they cannot be easily retrieved for the purpose of replacing or recharging the batteries, and the lifetime of the network is usually limited. The use of a wireless mode of communication between the nodes also puts a constraint on the amount of bandwidth that can be used for data forwarding.
4) Susceptibility to failures: The physical environment in which the sensor networks are deployed is usually harsh, such as in battlefields, large warehouses or even on the ocean floor. Sensor nodes are more susceptible to failures because they are in close contact with both the physical phenomenon to be monitored, as well as the physical environment. For example, sensor nodes that are deployed in the open areas may be tampered by humans or wildlife, and sensors that are thrown in large numbers into chemically contaminated fields may corrode and become faulty. 5) Topological changes: As the sensor nodes have limited power supplies and are susceptible to node failures, they may die and cause the network topology to change. Although most sensor networks are assumed to be relatively static, a sensor node may still deviate from its initial deployed location under the influence of its physical surroundings such as winds, currents, or even wildlife which also causes the topology to change. 6) Data-centric: In contrast with ad hoc networks which are address-centric, sensor networks are usually data-centric. Instead of point-to-point communications between individual nodes in the network, the flow of data in a sensor network is predominantly unilateral, towards a centralized sink. 7) Application specific: The types of applications that can be supported by sensor networks span across many different domains and have varying application requirements. It is unlikely that any particular protocol design or solution is suitable for all the different types of application scenarios [16]. Therefore, protocols and algorithms that are designed for wireless sensor networks are likely to be application-specific.
B. Issues and Challenges
The design of a sensor network is influenced by many factors, such as its characteristics and
10
other physical constraints. Here, we highlight some of the issues that must be taken into consideration when designing protocols for use in wireless sensor networks. 1) Self-configuration and self-maintenance: One of the main rationales for deploying sensor networks is to enable remote sensing with minimal human intervention. In addition, sensor networks are usually randomly deployed in hostile terrains in large numbers. As such, it is almost impossible to manually configure each and every one of the sensor nodes; these nodes must thus be equipped with self-configuration and self-maintenance capabilities. 2) Scalability: As sensor nodes are often deployed in large numbers over very large physical terrains, protocols for sensor networks must be able to scale; the performance of the network must not deteriorate significantly even if the number of nodes in the network increases. 3) Energy efficiency: Sensor nodes expend energy during data sensing and communication with the other nodes in the network. When the energy of a node depreciates, the node will die and this may cause the network to become partitioned a situation whereby communication gaps exist in the network such that some nodes may be unable to communicate with each other. The presence of network partitions will usually render a sensor network useless, because some parts of the network will no longer be under coverage; hence, some researchers consider that the sensor network lifetime has expired when the network becomes partitioned. Sensor network protocols must therefore be energy-efficient so as to extend the network lifetime and usefulness of the network [17].
11
4) Fault tolerance: Due to the limited energy of the nodes, as well as harshness and hostility of the environment in which the nodes are deployed in, the sensor nodes are prone to failures. With fault tolerance, the sensor network should be able to continue with its network functionalities (such as sensing and communication) even in the presence of node failures. This helps to increase the robustness of the sensor network and improves its QoS delivery to the applications. 5) Adaptability: The network topology and characteristics of a sensor node may be quite dynamic due to the influence of the physical environment that the network is deployed in. As such, the sensor network should demonstrate adaptability to the prevailing network conditions and physical environment in order to provide good network performance. 6) Transmission media: Sensor nodes typically communicate over a shared wireless transmission medium because the environment in which they are deployed in does not allow for infrastructure (such as centralized base stations or wires) to be setup easily. Depending on the environment that the sensor nodes operate in, different transmission media may be used. Terrestrial sensor networks typically make use of radio links while underwater sensor networks utilize acoustic links for communications; each of these transmission media have their own characteristics, such as the optimum operating frequency, permissible transmission range, etc. 7) Security: The openness of the physical environment and the transmission media subjects sensor networks to a multitude of security attacks ranging from Denial of Service (DoS) to malicious attempts to modify sensitive data information. Consequently, it is quintessential to ensure that sensor networks incorporate security mechanisms into their protocols to protect the integrity of the data collected.
12
8) Data processing: Sensor nodes are expected to have low computing powers and hence, unable to do complex processing on-board. However, if each sensor node is able to do some simple data processing such as data aggregation before forwarding the sensed data to the sinks, this may improve the overall network performance because it lowers the contention of the data packets and improves the packet delivery ratio. In SANETs, on-board data processing may also help to improve the response time of the network to changes in the physical environment. 9) Data storage: In large scale wireless sensor networks, the content of the sensed data collected is more important than the identity of the node that gathers them. Hence, making effective use of the enormous amounts of collected data requires scalable, self-organizing and energy-efficient algorithms. Using this approach, the data must be named and communication abstractions must use these naming conventions rather than the network address of the node. By making use of efficient and novel data storage algorithms such as Data-Centric Storage (DCS) [18], relevant data can be stored by name at nodes within the sensor network. In this way, queries for data of a particular name can be sent to the node storing the named data, without having to go through the flooding process which is used in some data-centric routing proposals. 10) Hardware constraints: According to [2], a sensor node comprises of a sensing unit, a processing unit, a transceiver unit and a power unit. As each of these components must fit into a small sensor node, it is unlikely that they have stringent constraints such as low computational power, low data rates and limited power source. The sensor network must be able to work with these hardware constraints in mind and protocols must not assume the capabilities of complex mathematical processing on-board.
IV. QOS IN WIRELESS SENSOR NETWORKS
In the previous section, we have highlighted some of the main characteristics of wireless
13
sensor networks, and elaborated on how these features may provide challenges when designing protocols for use in the network. In this section, we will look into the challenges of QoS provisioning in WSNs and some of the existing developments in QoS mechanisms for WSNs.
A. Difficulties of QoS provisioning in WSNs
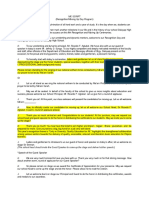
The successful deployment of QoS in WSNs is a challenging task because it depends on both the inherent properties of the network, as well as the physical hardware constraints of the sensor nodes. According to I. F. Akyildiz et al in [2], the sensor network protocol stack comprises more than that of a simple multi-layered protocol stack which already includes the physical layer, data link layer, network layer, transport layer and application layer. It also involves three additional planes which are perpendicular to the multi-layer stack; viz. task management plane, mobility management plane and power management plane (see Figure 1).
Figure 1 Sensor networks protocol stack (Source: I. F. Akyildiz et al, Wireless Sensor Networks: A Survey, Computer Networks 38, 2002)
B. QoS Performance Metrics in WSNs
Unlike the Internet and MANETs which can be used for a multitude of applications ranging from file transfer to multimedia applications, each WSN is usually deployed for a specific
14
application such as environmental monitoring or target tracking. In addition, each of these networks has their own unique characteristics and constraints; consequently, the QoS performance metrics in WSNs may differ significantly from those that are used in the Internet and MANETs. Some of the key performance metrics that should be considered in QoS provisioning in WSNs are as follows: 1) Energy efficiency: The energy limitation in WSNs is one of the most challenging aspects involved when designing protocols and considering QoS support in the network, because it is directly related to the lifetime of the network. A sensor node that fails due to lack of energy is unable to sense the physical environment or communicate with its neighbours. This may lead to network partitions, which in turn affects the network lifetime. The network lifetime has been defined in many ways in the literature. [20][21][22][23] refer to network lifetime as the maximum time before any node in the network drains up its energy. Although this definition is commonly used, it does not portray an accurate overview of the network lifetime from the perspective of the application (or user). Due to the high density in which nodes are usually deployed, the sensed data is highly correlated; therefore, even if a particular node fails after expending all its energy, a neighbouring node may still be able to perform the required functionalities of sensing and communication in that spatial location. As such, network lifetime cannot be considered based on the energy consumption of the nodes alone, but must also take into account the topological location of the nodes. We therefore adopt the more generic definition of network lifetime as that proposed by Kumar et al in [24], which is the time period during which the network continuously satisfies the application requirements, where application requirements may be specified in terms of coverage or delay and may vary depending on the specifications of each application.
15
2) Coverage: The diversity of sensor network applications has led to a range of interpretations of sensor network coverage [25]. Despite the discrepancies in the definitions, the main objective of coverage is somewhat consistent to ensure that each physical region in the space of interest in within the sensing (and/or communication) range of at least one sensor node [26]. The coverage of the sensor network is closely correlated with the denseness of the node deployment. A sparse network results in a sparse coverage, whereby the space of interest is partially covered by sensors. Dense networks result in dense coverage, whereby the space of interest is (almost) fully covered by the sensors. In very dense networks which have redundant coverage [27], the space of interest is covered by multiple sensors, resulting in high spatial correlation in the data that is observed by nodes which have geographical proximity. As a QoS metric, we define the coverage of a sensor network as the ratio of the space that is covered by the sensor nodes to the total space of interest. 3) Spatial accuracy: Wireless sensor nodes are usually deployed in a large terrain, and each sensor node is able to sense data from only a certain part of the space of interest. The sink, which collects the sensed data from the sensor nodes via multi-hop communications, is able to make logical deductions of the observations only if it has spatial (or locality) information of each data that is collected. For wireless sensor networks that are deployed outdoors, Global Positioning System (GPS) can be used to provide the location of each node, which will attach this information to its sensed data before forwarding it to the sink. Unfortunately, GPS is expensive and cannot be used indoors; therefore localization techniques such as those proposed in [29][30][31][32] have to be used as an alternative to obtain the (relative) locations of the nodes and provide spatial accuracy of the sensed data. The type of localization technique being employed determines the granularity of the location information can be fine (high spatial
16
accuracy) or coarse (low spatial accuracy). However, as high spatial accuracy usually results in higher overheads than low spatial accuracy, the appropriate level of spatial accuracy should also be based on the application requirements of the network. 4) Temporal accuracy: As like spatial accuracy, temporal accuracy is required in wireless sensor networks to ascertain the time period during which an event occurs. In wired and centralized networks such as the Internet, it is possible to achieve high temporal accuracy because of the high propagation speed of the communication medium. However, wireless sensor networks typically communicate in a distributed, multi-hop manner, via a shared communication channel. In terrestrial networks, the wireless links are prone to high bit error rates (BER), resulting in high link instability. In underwater networks where sensor nodes utilize acoustic waves instead of radio waves for communication, the speed of propagation is five orders of magnitude slower than that in terrestrial networks [33]. Such factors like link instability and slow propagation speed makes it difficult to achieve time synchronization in the network thus leading to low temporal accuracy. An accurate time synchronization protocol in the network, such as that proposed in [34], is hence necessary to achieve high temporal accuracy. 5) Delay: Sensor network applications can be classified into two domains periodic applications such as environmental monitoring, or event-driven applications such as target tracking. Event-driven applications tend to have stricter delay constraints; the sink must be able to receive notification that a particular event has occurred in a particular region of the network within a short time period after the occurrence so that it can react appropriately. However, as demonstrated by the authors in [35], stringent delay requirements can severely deteriorate the network lifetime. Henceforth, tradeoffs are involved when designing protocols for use in sensor networks.
17
C. Mechanisms to Achieve QoS in WSNs
In this section, we describe some existing mechanisms that have been proposed in the literature, which allow WSNs to achieve QoS. 1) Topology Management: Most of the energy that is expended by a node is through transmission and sensing. To reduce the amount of energy that is consumed by a sensor node in the network, the nodes can be put to sleep mode when they are not required to sense or transmit data to their neighbouring nodes. Topology management can be used to achieve this dual goal of coordinating the sleep schedules of all the nodes, such that data can still be forwarded efficiently to the sink [36]. It is able to do this by exploiting the high nodal density and high spatial correlation of the sensed data. As such, topology management helps to increase energy efficiency (and thus network lifetime) at the expense of higher latency, because nodes that are required for the data forwarding process may be in sleep mode during the transmission. 2) Localization: Localization provides an alternative mechanism of finding the physical locations of the sensor nodes in the network instead of making use of GPS, which is costly and infeasible indoors. It usually involves two phases [31]: (i) ranging, which is the distance estimation of the node from the sink or other nodes in the network using techniques such as signal strength, angle-of-arrival (AoA), etc; and (ii) iterative multilateration, which makes use of the range measurements from the previous phase to calculate a new location estimate. Hence, localization increases spatial accuracy, at the cost of higher overheads (and transmissions) which will reduce energy efficiency. 3) Controlled Mobility: One of the main causes of performance deterioration in wireless sensor networks is node mobility (due to influence from the environment) and random deployment of nodes (due to the denseness which nodes are usually deployed). As such, the
18
resulting network topology is usually not optimized for the protocols which are designed for the network. To incorporate QoS in the sensor network, controlled mobility [37] using mobile nodes or Unmanned Autonomous Vehicles (UAVs) can be used to deploy sensor nodes more efficiently to enhance connectivity and/or coverage. 4) Data Aggregation and/or Fusion: In data aggregation [39], data which is coming from different sources en route is combined into a single data packet. This helps to reduce redundancy caused by spatial correlation of the sensed data and minimize the number of transmissions required to forward the data back to the sink. However, as data processing is required at some (or all) of the sensor nodes in order to do aggregation, this could potentially result in higher latency, which should be taken into consideration when designing data aggregation algorithm for use in sensor networks. Data fusion is similar to data aggregation in that data of different modalities (such as pressure, temperature and salinity) are combined before data transmission. 5) Network Topology: Conventional wireless sensor networks have a single centralized sink that is usually placed in a corner of the network, and all the source nodes have to send data to the sink in a predominantly unilateral direction. As a result, sensor nodes that are near the sink have to perform more data forwarding and packet transmissions, which leads to two undesired behaviors: (i) increased contention and collisions near the sink; and (ii) nodes that are near the sink will drain up their energy faster, resulting in shorter network lifetime. Subsequently, Seah and Tan in [40] consider the use of more than one sink in a virtual multi-sink multi-path network architecture, which provides spatially diverse routes in the network such that source nodes will avoid sending all the data to one direction and cause network deterioration. This helps to improve the load distribution of the network and increases the network lifetime, at the expense of the physical deployment of more sinks.
19
6) Cross-Layer Designs: Although traditional networking paradigms promote the usage of a multi-layered protocol stack in which the different layers have minimal impact on each other, this does not lead to optimal performance. Cross layered designs such as that proposed by Chen et al in [41] can help to improve network performance by sharing information across the different layers, at the cost of eliminating the interdependency between adjacent layers.
V. WISER A FRAMEWORK TO ENHANCE QOS IN WIRELESS SENSOR NETWORKS
Although there have been significant research efforts in the various mechanisms to achieve QoS in WSNs, such as topology management, localization, etc, there is currently no standardization on a QoS model or framework in wireless sensor network. In addition, there is also little work which attempts to relate all these issues together to present an overall guideline on how QoS can be achieved in wireless sensor network. Sanli et al [42] propose a two phase protocol, EQos for the purpose of providing QoS in the network while achieving energy efficiency. However, they only consider QoS metrics such as coverage, connectivity and delay, which does not reflect the full application requirements of a WSN. We hence propose WISER, which is a framework to enhance QoS in WIreless SEnsoR networks (see Figure 2). It comprises of the a few components such as topology management, localization, data aggregation, etc, all of which aim to improve at least one of the QoS performance metrics that has been identified in the previous section. Each of the different components in WISER may span across a few different networking layers of the protocol stack, and they also interoperate with each other to improve the network performance. As each of these components will result in tradeoffs in network performances, it is important to consider the impact of the entire framework as a whole.
20
Topology Management
Data aggregation and/or fusion Controlled Mobility
Localization Quality of Service in Wireless Sensor Network Security Cross Layer Design Time Synchronization Network Topology
Figure 2 WISER a framework to achieve QoS in WIreless SEnsoR networks
A. Network Model and Assumptions
We assume a heterogeneous network which has three types of nodes with different capabilities: (i) wireless sensor nodes which are deployed randomly in possibly large numbers; (ii) one or more sinks which are placed in strategic locations in the network; and (iii) Unmanned Autonomous Vehicles (UAVs) which are deployed in lesser numbers due to their cost. The UAVs are expected to have higher processing capabilities than the sensor nodes, and are also able to move about independently. It is not necessary for the network to have UAVs, but if these nodes do exist, then the total number of sensor nodes must be greater than the number of UAVs.
21
All the nodes in the network (sensor nodes and UAVs) communicate via a wireless shared channel. For simplicity, it is assumed that the sensing range of each node is the same as the transmission range, although these values may be different in real life. In addition, the transmission range of each node is relatively small as compared to the size of the physical terrain; hence it is expected that nodes will have to communicate via multiple hops. A node is either in the sleep or wake mode at any one time. If the node is awake, its radio is either in the idle state, receive state or transmit state. A node may also sense data only if it is awake; i.e. if the node is in the sleep mode, it can neither communicate with its neighbours nor sense any physical phenomenon in the environment. The sensor network is also expected to support both periodic and event-driven applications. For periodic applications, each sensor node senses its environment at periodic time intervals and forwards the data back to the sink(s). Event-driven applications are classified into two main categories: (i) sink-initiated; or (ii) sensor node-initiated. In the latter case, a sensor node upon sensing an unknown (or pre-specified) physical phenomenon, will send the sensed data back to the sink immediately. In sink-initiated applications, the sink will send data request messages to one or more groups of sensor nodes to request for specific data. We assume that event-driven applications have more stringent delay constraints than the periodic applications, and that both types of applications need temporal and spatial information, as well as full spatial coverage. No other assumptions are made with respect to the application requirements.
22
B. Network Initialization
During the initial deployment of the network, there is a network initialization period during which nodes perform various functions such as authentication (for security purposes), time synchronization (to achieve temporal accuracy), localization (to achieve spatial accuracy) and route establishment (to the sinks). This initialization phase is triggered by the sink(s) immediately after the nodes have been distributed in the network. To obtain authentication, time synchrony and location information, the nodes in the network need to exchange periodic update messages. To reduce the number of messages that are being exchanged, it is assumed that each of these messages contain the required information for authentication, time synchronization, localization and route establishment, i.e. each node does not need to send four separate messages to perform these four functionalities. After the initialization phase, each node will still need to send periodic update messages to one another this is one of the self-configuring and selfmaintenance features of the WISER. With the use of these periodic messages, nodes can easily tell if the neighbouring nodes are in sleep or wake mode, or if the neighbouring node has already failed. Initially, all the nodes are in the wake mode.
C. Network Components
Depending on the application requirements of the sensor network, different algorithms for each of the network components may be deployed. For example, if the application does not require high spatial accuracy, then the network can deploy a coarse-grained granularity localization algorithm which usually incurs fewer overheads (and other costs) as compared to a fine-grained granularity localization algorithm. It is also not necessary for the network to have each and every component that is in the proposed framework if network lifetime is not an issue
23
in the network, it need not make use of a topology management scheme to increase energy efficiency. However, as mentioned in the previous subsection, the minimum application requirement is spatial and temporal accuracy; therefore, localization and time synchronization must are the minimum components of the framework which must be implemented in the network. The functionalities of each of the different components in the framework are as follows: � Topology management coordinates sleep/wake schedules of the nodes in the network to achieve energy efficiency; � Localization provides location information of the nodes without the use of GPS to achieve spatial accuracy; � Cross-layer design facilitates information sharing among the different layers in the networking protocol stack by message passing, so as to achieve better performance; � Time synchronization provides a common time base for all the nodes to achieve temporal accuracy; � Network topology optimizes the topology of the network, possibly with the aid of more sinks or better node placements; � Security provides authentication of the nodes in the network; � Controlled mobility optimizes the topology of the network for better system performance, possibly with the aid of UAVs; and � Data aggregation and/or fusion combines data packets or data with different modalities together, to reduce the number of required transmissions and to improve the energy efficiency of the nodes in the network.
24
VI. CONCLUSION AND FUTURE WORK
While many diverse applications have been envisioned for use in wireless sensor networks, there are still many issues that need to be worked on before Quality of Service can be supported in these networks. In this paper, we have looked at the existing mechanisms to provide QoS in different networks and also examined some of the constraints in WSNs which makes it difficult to provision for QoS. We have also proposed WISER a framework which aims to enhance QoS in WIreless SEnsoR Networks. WISER is made up of a few different network components; however, it is not quintessential for the wireless sensor network to implement all the modules in the framework. Only certain components in the framework can be implemented, depending on the specific application requirements. In addition, as sensor networks are typically applicationspecific, we have attempted to make WISER as generic as possible by not putting constraints on the different protocols that have to be used for each component. As part of future work, we will verify the correctness and completeness of WISER in provisioning for QoS in wireless sensor networks. Furthermore, we will also evaluate the efficiency of WISER as a framework to provide QoS support in the network, by considering the QoS performance metrics that we have identified earlier on, viz. coverage, temporal accuracy, spatial accuracy, etc.
25
REFERENCES
[1] G. Venkatesh, M2M: Now Everything Can Talk, Industrial Automation Asia, Oct/Nov 2004. [2] I. F. Akyildiz, W. Su, Y. Sankarasubramaniam and E. Cayirci, Wireless Sensor Networks: A Survey, Computer Networks Vol. 38, Mar 2002. [3] B. Braden, D. Clark and S. Shenker, Integrated Services in the Internet Architecture: An Overview, IETF RFC1633, Jun 1994. [4] S. Blake, D. Black, N. Carlson, E. Davies, Z. Wang and W. Weiss, An Architecture for Differentiated Services, IETF RFC 2475, Dec 1998. [5] H. Xiao, W. K. G. Seah, A. Lo and K. C. Chua, A Flexible Quality of Service Model for Mobile Ad-Hoc Networks, Proceedings of IEEE 51st Vehicular Technology Conference, Tokyo, Japan, May 2000. [6] K. Chen, S. H. Shah and K. Nahrstedt, Cross-Layer Design for Data Accessibility in Mobile Ad Hoc Networks, Journal of Wireless Personal Communications, Special Issue on Multimedia Network Protocols and Enabling Radio Technologies, Kluwer Academic Publishers, Vol. 21, pp. 49-75, 2002. [7] E. Crawley, R. Nair, B. Rajagopalan and H. Sandick, A Framework for QoS-based Routing in the Internet, IETF RFC 2386, Aug 1998. [8] N. Nikaein, C. Bonnet, Y. Moret and I. A. Rai, 2LQoS Two-Layered Quality of Service Model for Reactive Routing Protocols for Mobile Ad Hoc Networks, Proceedings of 6th World Multiconference on Systemics, Cybernetics and Informatics (SCI 2002), USA, Orlando, 2002. [9] R. Braden, L. Zhang, S. Berson, S. Herzog and S. Jamin, Resource ReSerVation Protocol (RSVP), IETF RFC 2205, Sep 1997. [10] Y. Iraqi and R. Boutaba, A Novel Distributed Call Admission Control for Wireless Mobile Multimedia Networks, Proceedings of ACM International Workshop on Wireless Mobile Multimedia (WoWMoM00), Boston, Massachusetts, USA, Aug 2000. [11] Y. C. Wang, S. R. Ye and Y.-C. Tseng, A Fair Scheduling Algorithm with Traffic Classification in Wireless Networks, Computer Communications, Vol. 28, 2005. [12] S. Chakrabarti and A. Mishra, QoS Issues in Ad Hoc Wireless Networks, IEEE Communications Magazine, Feb 2001. [13] K. Wu and J. Harms, QoS Support in Mobile Ad Hoc Networks, Crossing Boundaries GSA Journal of University of Alberta, Vol. 1, No. 1, Nov 2001. [14] Winston K. G. Seah, Quality of Service in Mobile Ad Hoc Networks Myth or Reality?, Keynote presentation, Australian Telecommunication Networks and Applications Conference (ATNAC 2004), Sydney, Australia, Dec 8-10, 2004. [15] R. Min, M. Bhardwaj, S. Cho, Nathan Ickes, E. Shih, A. Sinha, A. Wang, and A. P. Chandrakasan, Energycentric enabling technologies for wireless sensor networks, IEEE Wireless Communications, Vol. 9, No. 4, pp. 28-39, Aug 2002.
26
[16] H. Karl and A. Willig, A short survey of wireless sensor networks, Technical Report TKN-03-018, Telecommunication Networks Group, Technische Universitt Berlin, Oct 2003. [17] N. Heo and P. K. Varshney, Energy-Efficient Deployment of Intelligent Mobile Sensor Networks, IEEE Transactions on Systems, Man and Cybernetics, Vol. 35, No. 1, Jan 2005. [18] S. Ratnasamy, B. Karp, L. Yin, F. Yu, D. Estrin, R. Govindan and S. Shenker, GHT: A Geographic Hash Table for Data-Centric Storage, Proceedings of the ACM Workshop on Sensor Networks and Applications, Atlanta, Georgia, USA, Sep 2002. [19] D. Ganesan, A. Cerpa, W. Ye, Y. Yu, J. Zhao and D. Estrin, Networking Issues in Wireless Sensor Networks, Journal of Parallel and Distributed Computing (JPDC), Special Issue on Frontiers in Distributed Sensor Networks, Elsevier Publishers, Dec 2003. [20] Y. T. Hou, Y. Shi and H. D. Sherali, Rate Allocation in Wireless Sensor Networks with Network Lifetime Requirement, Proceedings of the 5th ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc 04), Roppongi, Japan, May 24 26, 2004. [21] C. Schurgers and M. B. Srivastava, Energy Efficient Routing in Wireless Sensor Networks, Proceedings of MILCOM 01, Vienna, VA, Oct 28 31, 2001. [22] I. Kang and R. Poovendran, Maximizing Network Lifetime of Broadcasting Over Wireless Stationary Ad Hoc Networks, Mobile Networks and Applications, Special Issue: Energy Constraints and Lifetime Performance in Wireless Sensor Networks, Vol. 10, No. 6, Dec 2005. [23] K. Kalpakis, K. Dasgupta and P. Namjoshi, Maximum Lifetime Data Gathering and Aggregation in Wireless Sensor Networks, Proceedings of the 2002 IEEE International Conference on Networking (ICN 02), Atlanta, Georgia, Aug 26 29, 2002. [24] S. Kumar, A. Arora and T. H. Lai, On the Lifetime Analysis of Always-On Wireless Sensor Network Applications, Proceedings of the 2nd IEEE International Conference on Mobile and Ad Hoc Sensor Systems (MASS), Washington, D.C., Nov 7 10, 2005. [25] S. Meguerdichian, F. Koushanfar, M. Potkonjak and M.B. Srivastava, Coverage Problems in Wireless Ad-Hoc Sensor Networks, Proceedings of the 20th Annual Joint Conference of the IEEE Computer and Communications Societies (INFOCOM 2001), Apr 22 26, 2001. [26] M. Cardei and J. Wu, Energy-Efficient Coverage Problems in Wireless Ad Hoc Sensor Networks, Journal of Computer Communications on Sensor Networks, 2005. [27] K. Romer and F. Mattern, The Design Space of Wireless Sensor Networks, IEEE Wireless Communications, Vol. 11, No. 6, Dec 2004. [28] I. F. Akyildiz, M. C. Vuran and O. B. Akan, On Exploiting Spatial and Temporal Correlation in Wireless Sensor Networks, Proceedings of WiOpt 04: Modeling and Optimization in Mobile, Ad Hoc and Wireless Networks, Mar 2004. [29] L. Hu and D. Evans, Localization for Mobile Sensor Networks, Proceedings of the 10th Annual International Conference on Mobile Computing and Networking (ACM Mobicom 04), Philadelphia, PA, USA, 26 Sep 1 Oct, 2004.
27
[30] N. B. Priyantha, H. Balakrishnan, E. Demaine and S. Teller, Mobile-Assisted Localization in Wireless Sensor Networks, Proceedings of the 24th Annual Joint Conference of the IEEE Computer and Communications Societies (INFOCOM 2005), Miami, FL, Mar 13 17, 2005. [31] A. Savvides, C.-C. Han and M. B. Srivastava, Dynamic Fine-Grain Localization in Ad-Hoc Networks of Sensors, Proceedings of the 7th Annual ACM/IEEE International Conference on Mobile Computing and Networking (Mobicom 01), 2001. [32] D. Moore, J. Leonard, D. Rus and S. Teller, Robust distributed network localization with noisy range measurements, Proceedings of the ACM Symposium on Networked Embedded Systems, 2004. [33] I. F. Akyildiz, D. Pompili and T. Melodia, Underwater Acoustic Sensor Networks: Research Challenges, Journal of Ad Hoc Networks (Elsevier), Article in Press, 2005. [34] J. Elson and D. Estrin, Proceedings of the 2001 International Parallel and Distributed Processing Symposium (IPDPS), Workshop on Parallel and Distributed Computing Issues in Wireless and Mobile Computing, San Francisco, California, USA. Apr 2001. [35] S. Adlakha, S. Ganeriwal, C. Schurgers and M. B. Srivastava, Density, Accuracy, Delay and Lifetime Tradeoffs in Wireless Sensor Networks A Multidimensional Design Perspective, Proceedings on the 1st International Conference on Embedded Networked Sensor Systems (SenSys 2003), Los Angeles, California, USA, Nov 5 7, 2003. [36] C. Schurgers, V. Tsiatsis, S. Ganeriwal and M. Srivastava, Topology Management for Sensor Networks: Exploiting Latency and Density, Proceedings of the 3rd ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc 02), EPFL, Lausanne, Switzerland, Jun 9 11, 2002. [37] W. K. G. Seah, Z. Liu, J. G. Lim, S. V. Rao and M. H. Ang, Jr., TARANTULAS: Mobility-enhanced Wireless Sensor-Actuator Networks, to appear in the Proceedings of the IEEE International Conference on Sensor Networks, Ubiquitous, and Trustworthy Computing (SUTC 2006), Taichung, Taiwan, Jun 5 7, 2006. [38] S. Nath, P. Gibbons and S. Seshan, Synopsis Diffusion for Robust Aggregation in Sensor Networks, Proceedings of the ACM Symposium on Networked Embedded Systems, 2004 [39] B. Krishanamachari, D. Estrin and S. Wicker, The Impact of Data Aggregation in Wireless Sensor Networks, International Workshop of Distributed Event Based Systems (DEBS), Vienna, Austria, Jul 2002. [40] W. K. G. Seah and H. P. Tan, Multipath Virtual Sink Architecture for Wireless Sensor Networks in Harsh Environments, 1st International Conference on Integrated Internet, Ad Hoc and Sensor Networks (InterSense 2006), May 29-31, 2006, Nice, France. [41] K. Chen, S. H. Shah and K. Nahrstedt, Cross-Layer Design for Data Accessibility in Mobile Ad Hoc Networks, Journal of Wireless Personal Communications, Special Issue on Multimedia Network Protocols and Enabling Radio Technologies, Kluwer Academic Publishers, Vol. 21, pp. 49-75, 2002. [42] H. O. Sanli, H. am and X. Cheng, EQoS: An Energy Efficient QoS Protocol for Wireless Sensor Networks, Proceedings of the 2004 Western Simulation MultiConference (WMC 04), San Diego, CA, USA, Jan 18 21, 2004.
Anda mungkin juga menyukai
- Beyond Technique - Painting With Passion - Alvaro CastagnetDokumen133 halamanBeyond Technique - Painting With Passion - Alvaro Castagnetra5kl91% (35)
- Communications-Based Train Control (CBTC) Is ADokumen18 halamanCommunications-Based Train Control (CBTC) Is AchaithanBelum ada peringkat
- Owners Manual For Colombia - Daewoo ManualDokumen333 halamanOwners Manual For Colombia - Daewoo ManualEdgar Gonzalez100% (1)
- Qos Support in Wireless Sensor Networks: A SurveyDokumen7 halamanQos Support in Wireless Sensor Networks: A Surveyirfan_ali_49Belum ada peringkat
- Quality of Service of Routing Protocols in Wireless Sensor Networks: A ReviewDokumen26 halamanQuality of Service of Routing Protocols in Wireless Sensor Networks: A ReviewlupsumetroBelum ada peringkat
- Survey ZakariaDokumen28 halamanSurvey Zakariasamaaan8215Belum ada peringkat
- WirelessNetworks Journal 162Dokumen10 halamanWirelessNetworks Journal 162icang09Belum ada peringkat
- Mobile Ad Hoc Networks: A Comparative Study of Qos Routing ProtocolsDokumen5 halamanMobile Ad Hoc Networks: A Comparative Study of Qos Routing ProtocolsKrishna ChaitanyaBelum ada peringkat
- Qos Support in Wireless Sensor Networks: A SurveyDokumen7 halamanQos Support in Wireless Sensor Networks: A SurveyAngel MooreBelum ada peringkat
- A Review of Qos in Wireless Sensor Networks: Jaswanth Bhargav PadigalaDokumen6 halamanA Review of Qos in Wireless Sensor Networks: Jaswanth Bhargav PadigalaKhizar SalmanBelum ada peringkat
- Congestion Control For Wireless Cellular Systems With Applications To UMTSDokumen2 halamanCongestion Control For Wireless Cellular Systems With Applications To UMTSChristopher AiyapiBelum ada peringkat
- Mobility & QoSDokumen15 halamanMobility & QoSsriperlBelum ada peringkat
- Providing End-To-End Qos in 4G NetworksDokumen8 halamanProviding End-To-End Qos in 4G NetworksAngel Nuñez PachecoBelum ada peringkat
- Agent Based Qos Provisioning For NGMN (Lte) : Prof.D.Jayaramaiah,, A.Prasanth, A.Viswanatha Reddy, DR - Anirban BasuDokumen11 halamanAgent Based Qos Provisioning For NGMN (Lte) : Prof.D.Jayaramaiah,, A.Prasanth, A.Viswanatha Reddy, DR - Anirban Basuأبو أيوب تافيلالتBelum ada peringkat
- Dependable QosDokumen7 halamanDependable Qosthiyagu1968Belum ada peringkat
- Qos Manet LayoutDokumen9 halamanQos Manet LayoutAshish PatelBelum ada peringkat
- 4G - Technologies: AbstractDokumen9 halaman4G - Technologies: AbstractParidhi AggarwalBelum ada peringkat
- Internet QoS Signaling SurveyDokumen26 halamanInternet QoS Signaling SurveyLuka ŠpanićBelum ada peringkat
- Assignment 1: Advance Wireless NetworksDokumen4 halamanAssignment 1: Advance Wireless NetworksJunaid_572Belum ada peringkat
- Using 5G Qos Mechanisms To Achieve Qoe-Aware Resource AllocationDokumen9 halamanUsing 5G Qos Mechanisms To Achieve Qoe-Aware Resource Allocationzayyanu yunusaBelum ada peringkat
- A Survey On QoS Protocols For Mission-Critical Applications in Wireless Sensor NetworksDokumen12 halamanA Survey On QoS Protocols For Mission-Critical Applications in Wireless Sensor NetworksAnonymous Ul4cHOSBelum ada peringkat
- (4G Tehnology-A Sensation: This Paper Describes An Architecture For Differentiation of QualityDokumen17 halaman(4G Tehnology-A Sensation: This Paper Describes An Architecture For Differentiation of QualityshazaadaBelum ada peringkat
- Challenges and Approches For WSNDokumen23 halamanChallenges and Approches For WSNNisumba SoodhaniBelum ada peringkat
- Ijesat 2011 01 01 02Dokumen3 halamanIjesat 2011 01 01 02Ijesat JournalBelum ada peringkat
- COMSATS University Islamabad Abbottabad Campus: Department of Computer ScienceDokumen7 halamanCOMSATS University Islamabad Abbottabad Campus: Department of Computer ScienceMehkiiBelum ada peringkat
- A Metering Infrastructure For Heterogenous Mobile NetworksDokumen8 halamanA Metering Infrastructure For Heterogenous Mobile NetworksLuisa CatalinaBelum ada peringkat
- Performance Analysis of Delay in Wireless Sensor Networks: Jayashree C. Pasalkar Vivek S. DeshpandeDokumen4 halamanPerformance Analysis of Delay in Wireless Sensor Networks: Jayashree C. Pasalkar Vivek S. Deshpandeteferi kassaBelum ada peringkat
- An Overview of Context-Aware Vertical Handover Schemes in Heterogeneous NetworksDokumen12 halamanAn Overview of Context-Aware Vertical Handover Schemes in Heterogeneous NetworksijcsesBelum ada peringkat
- Mbowe Oreku QoS in WSN 2014Dokumen9 halamanMbowe Oreku QoS in WSN 2014selvarasuBelum ada peringkat
- A Qos-Oriented Distributed Routing Protocol For Hybrid Wireless NetworksDokumen16 halamanA Qos-Oriented Distributed Routing Protocol For Hybrid Wireless NetworksNYIRIKUTOBelum ada peringkat
- Good PaperDokumen6 halamanGood PaperOmar AltradBelum ada peringkat
- An Energy-Aware Qos Routing Protocol For Wireless Sensor NetworksDokumen9 halamanAn Energy-Aware Qos Routing Protocol For Wireless Sensor NetworksSiddaling B AlandBelum ada peringkat
- Hierarchical Wireless Network Architecture For Distributed ApplicationsDokumen6 halamanHierarchical Wireless Network Architecture For Distributed ApplicationsabojablBelum ada peringkat
- Research Article: A Fuzzy Preprocessing Module For Optimizing The Access Network Selection in Wireless NetworksDokumen10 halamanResearch Article: A Fuzzy Preprocessing Module For Optimizing The Access Network Selection in Wireless NetworksDaniela HossuBelum ada peringkat
- Ubicc Dwmsn-Ems 466Dokumen7 halamanUbicc Dwmsn-Ems 466Ubiquitous Computing and Communication JournalBelum ada peringkat
- Research Article: A Fuzzy Preprocessing Module For Optimizing The Access Network Selection in Wireless NetworksDokumen10 halamanResearch Article: A Fuzzy Preprocessing Module For Optimizing The Access Network Selection in Wireless NetworksDaniela HossuBelum ada peringkat
- Security Issues and Quality of Services Challenges in Mobile Ad-Hoc NetworksDokumen4 halamanSecurity Issues and Quality of Services Challenges in Mobile Ad-Hoc NetworksIJERDBelum ada peringkat
- Software-Defined Cyber-Physical Multinetworks: Zhijing Qin, Ngoc Do, Grit Denker, Nalini VenkatasubramanianDokumen5 halamanSoftware-Defined Cyber-Physical Multinetworks: Zhijing Qin, Ngoc Do, Grit Denker, Nalini VenkatasubramanianBoopathy PandiBelum ada peringkat
- Overview of QoS in GeneralDokumen6 halamanOverview of QoS in GeneralVũ LongBelum ada peringkat
- Multiclass Queueing Network Modeling and Traffic Flow Analysis For SDN Enabled Mobile Core Networks With Network SlicingDokumen14 halamanMulticlass Queueing Network Modeling and Traffic Flow Analysis For SDN Enabled Mobile Core Networks With Network Slicingsamaa adelBelum ada peringkat
- Link Stability Based Handoff For Qos Provisioning in 4G NetworkDokumen9 halamanLink Stability Based Handoff For Qos Provisioning in 4G NetworkInternational Journal of Application or Innovation in Engineering & ManagementBelum ada peringkat
- 1.7 Literature Review: Habitant Monitoring Assessing The "Health" of Machines, Aerospace Vehicles, and CivilDokumen8 halaman1.7 Literature Review: Habitant Monitoring Assessing The "Health" of Machines, Aerospace Vehicles, and CivilJoy WilsonBelum ada peringkat
- DDI Book Chapter IntroDokumen10 halamanDDI Book Chapter IntroMuhammad AteeqBelum ada peringkat
- CNC 04Dokumen18 halamanCNC 04AIRCC - IJCNCBelum ada peringkat
- Mobility and Handoff Management in Wireless Networks: Chapter ManuscriptDokumen26 halamanMobility and Handoff Management in Wireless Networks: Chapter ManuscriptAtthippattu Srinivasan MuralitharanBelum ada peringkat
- Dynamic Routing For Knowledge Integrity and Delay Differentiate Services in WSNDokumen5 halamanDynamic Routing For Knowledge Integrity and Delay Differentiate Services in WSNKumara SBelum ada peringkat
- Adaptive Bandwidth Management Model For Wireless Mobile Ad-Hoc NetworkDokumen16 halamanAdaptive Bandwidth Management Model For Wireless Mobile Ad-Hoc NetworkAIRCC - IJCNCBelum ada peringkat
- Research On Self-Organizing Software Radio Network: Xiungquun Zheng, Wei QingchunDokumen5 halamanResearch On Self-Organizing Software Radio Network: Xiungquun Zheng, Wei QingchunRavi Kumar DubeyBelum ada peringkat
- Qos and Network Performance: Computer NetworksDokumen6 halamanQos and Network Performance: Computer NetworksljjbBelum ada peringkat
- INSIGNIA: An IP-Based Quality of Service Framework For Mobile Ad Hoc NetworksDokumen33 halamanINSIGNIA: An IP-Based Quality of Service Framework For Mobile Ad Hoc NetworksdokimquyBelum ada peringkat
- AdhocDokumen17 halamanAdhocSripriya GunaBelum ada peringkat
- IOSR JournalsDokumen6 halamanIOSR JournalsInternational Organization of Scientific Research (IOSR)Belum ada peringkat
- Energy Based Multipath Routing Protocols For Wireless Sensor NetworksDokumen8 halamanEnergy Based Multipath Routing Protocols For Wireless Sensor NetworksJournal of Computer ApplicationsBelum ada peringkat
- Over ProvisioningDokumen3 halamanOver ProvisioningscribdslaskBelum ada peringkat
- Virtueman: A Software-Defined Network Architecture For Wifi-Based Metropolitan ApplicationsDokumen5 halamanVirtueman: A Software-Defined Network Architecture For Wifi-Based Metropolitan ApplicationsAllan LeandroBelum ada peringkat
- SDN Based Mobile Networks: Concepts and Benefits: Slavica Tomovic Igor RadusinovicDokumen16 halamanSDN Based Mobile Networks: Concepts and Benefits: Slavica Tomovic Igor RadusinovicapatiyehBelum ada peringkat
- An Energy-Aware Technique To Improve The Lifetime of Cell Phone Based Wsns Using Isa100.11ADokumen7 halamanAn Energy-Aware Technique To Improve The Lifetime of Cell Phone Based Wsns Using Isa100.11AInternational Journal of Application or Innovation in Engineering & ManagementBelum ada peringkat
- Performance Evaluation of AODV, DSDV & DSR Routing Protocol in Grid EnvironmentDokumen8 halamanPerformance Evaluation of AODV, DSDV & DSR Routing Protocol in Grid EnvironmentkanjaiBelum ada peringkat
- Design of A QoS-aware Routing Mechanism ForDokumen6 halamanDesign of A QoS-aware Routing Mechanism ForNoopur SharmaBelum ada peringkat
- Efficient Allocation of Mobile Resources Using Fuzzy Systems For A Qos PlanningDokumen6 halamanEfficient Allocation of Mobile Resources Using Fuzzy Systems For A Qos PlanninguliweylBelum ada peringkat
- End-To-End Qos Support For Ip and Multimedia Traffic in Heterogeneous Mobile NetworksDokumen12 halamanEnd-To-End Qos Support For Ip and Multimedia Traffic in Heterogeneous Mobile NetworksmaniahmadBelum ada peringkat
- Modeling and Dimensioning of Mobile Wireless Networks: From GSM to LTEDari EverandModeling and Dimensioning of Mobile Wireless Networks: From GSM to LTEBelum ada peringkat
- Requirement EngineeringDokumen40 halamanRequirement EngineeringKhizar SalmanBelum ada peringkat
- CS718 Spring 2008 Assignment 1Dokumen2 halamanCS718 Spring 2008 Assignment 1Khizar SalmanBelum ada peringkat
- A Review of Qos in Wireless Sensor Networks: Jaswanth Bhargav PadigalaDokumen6 halamanA Review of Qos in Wireless Sensor Networks: Jaswanth Bhargav PadigalaKhizar SalmanBelum ada peringkat
- BW Valley Hotel Case Study 030409Dokumen2 halamanBW Valley Hotel Case Study 030409Khizar SalmanBelum ada peringkat
- Global E-Business How Businesses Use Information SystemsDokumen52 halamanGlobal E-Business How Businesses Use Information SystemsKhizar SalmanBelum ada peringkat
- Cobb George Linus. Piano Music. 58 Scores + MidiDokumen194 halamanCobb George Linus. Piano Music. 58 Scores + Midipippo.2017100% (1)
- Lesson GGG - Seventh Chords - (Version 03) PDFDokumen9 halamanLesson GGG - Seventh Chords - (Version 03) PDFElsachristineBelum ada peringkat
- Alice Munro The EyeDokumen8 halamanAlice Munro The EyeIon Valentin CeaușescuBelum ada peringkat
- Major Scales Cello 2Dokumen5 halamanMajor Scales Cello 2sonny stittBelum ada peringkat
- Becky Gartner Website CV 2015Dokumen3 halamanBecky Gartner Website CV 2015api-284523107Belum ada peringkat
- HWD-usb Flash Drives CatalogDokumen21 halamanHWD-usb Flash Drives Catalogapi-19966285Belum ada peringkat
- Tugas Penilaian 1, MK B - Ing PGSDDokumen2 halamanTugas Penilaian 1, MK B - Ing PGSDevidewisartika610Belum ada peringkat
- (R&B) Circle:: Khammam: Sl. No. Division/ Ees Sub-Division/ Dy - Ees Sectins-Aee'S Roads Alloted 1 2 3 4 5Dokumen8 halaman(R&B) Circle:: Khammam: Sl. No. Division/ Ees Sub-Division/ Dy - Ees Sectins-Aee'S Roads Alloted 1 2 3 4 5devallasarmaBelum ada peringkat
- Kerinduan: Bob TutupolyDokumen8 halamanKerinduan: Bob TutupolyBintang HidayahBelum ada peringkat
- Postgraduate Scholarships, Studentships and Bursaries at Bangor UniversityDokumen17 halamanPostgraduate Scholarships, Studentships and Bursaries at Bangor UniversityJefry Gunawan MrgBelum ada peringkat
- Graziela Bortz: Rhythm in The Music of Brian Ferneyhough, Michael Finnissy, and Arthur KampelaDokumen127 halamanGraziela Bortz: Rhythm in The Music of Brian Ferneyhough, Michael Finnissy, and Arthur KampelaAriel Magno da CostaBelum ada peringkat
- Klotz - Sounds in Black & WhiteDokumen42 halamanKlotz - Sounds in Black & WhiteHosking RafaelBelum ada peringkat
- Etudes Op.100 (Giuliani) - Marieh 2018 CopyleftDokumen61 halamanEtudes Op.100 (Giuliani) - Marieh 2018 CopyleftumitBelum ada peringkat
- A Note On The Sound Radiation From The Classical Guitar Influence of Energy Input Via The String Termination at The FretDokumen4 halamanA Note On The Sound Radiation From The Classical Guitar Influence of Energy Input Via The String Termination at The FretAmaury Jamir Meza PérezBelum ada peringkat
- MC Script 4 RecogDokumen2 halamanMC Script 4 RecogArjel DantesBelum ada peringkat
- Optical Transport NetworksDokumen18 halamanOptical Transport Networksshahramkarimi76Belum ada peringkat
- Notes On The Troubleshooting and Repair of Television SetsDokumen250 halamanNotes On The Troubleshooting and Repair of Television SetsAlfian MangadjibBelum ada peringkat
- Trumpet Valve ManifoldDokumen4 halamanTrumpet Valve Manifoldmahonde100% (1)
- Acer Al2002w PDFDokumen60 halamanAcer Al2002w PDFAldo TonatoBelum ada peringkat
- Jobs and OccupationsDokumen2 halamanJobs and OccupationsmemoinrealifeBelum ada peringkat
- General Training Reading and Writing Test: Section 1 Questions 1-14Dokumen7 halamanGeneral Training Reading and Writing Test: Section 1 Questions 1-14Matrika OberoiBelum ada peringkat
- A40-10-112 06a FAADokumen3 halamanA40-10-112 06a FAAPolkaboy2Belum ada peringkat
- RSNR Sample ValDokumen597 halamanRSNR Sample ValrawatumedBelum ada peringkat
- Subsynchronous Resonance in Series Compensated LinesDokumen10 halamanSubsynchronous Resonance in Series Compensated LinesBrian HeadBelum ada peringkat
- Đáp Án Perfect Listening 1Dokumen6 halamanĐáp Án Perfect Listening 1Ngo Thuy KieuBelum ada peringkat
- Roger PDFDokumen82 halamanRoger PDFjimBelum ada peringkat
- W ON LY: Cover The Earth (E, 71 BPM, 4/4) Cover The EarthDokumen3 halamanW ON LY: Cover The Earth (E, 71 BPM, 4/4) Cover The EarthDanilo Choir StuffBelum ada peringkat