Automatic Access Control System Using Student Identification Card Based On Rfid Technology
Diunggah oleh
thgnguyen0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
381 tayangan100 halamanAutomatic Access Control System Using Student Identification Card Based on Rfid Technology
Judul Asli
Automatic Access Control System Using Student Identification Card Based on Rfid Technology
Hak Cipta
© © All Rights Reserved
Format Tersedia
PDF, TXT atau baca online dari Scribd
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniAutomatic Access Control System Using Student Identification Card Based on Rfid Technology
Hak Cipta:
© All Rights Reserved
Format Tersedia
Unduh sebagai PDF, TXT atau baca online dari Scribd
0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
381 tayangan100 halamanAutomatic Access Control System Using Student Identification Card Based On Rfid Technology
Diunggah oleh
thgnguyenAutomatic Access Control System Using Student Identification Card Based on Rfid Technology
Hak Cipta:
© All Rights Reserved
Format Tersedia
Unduh sebagai PDF, TXT atau baca online dari Scribd
Anda di halaman 1dari 100
AUTOMATIC ACCESS CONTROL SYSTEM USING STUDENT
IDENTIFICATION CARD BASED ON RFID TECHNOLOGY
GEOFFREY CHUA TIONG SING
UNIVERSITI TEKNOLOGI MALAYSIA
PSZ l9:l 6 (Pind. I /07)
lf the lhesis is coNFIDENTAL or RESTRtCTED, pteose
ofioch with the tetter from
the orgonizotion wiih period ond reosons for confidentiolity or restriction.
UNIVERSITI TEKNOTOGI MATAYSIA
DECTARATION OF THESIS
/
UNDERGRADUATE PROJECT PAPER AND COPYRIGHT
Author's full nome
Dote of birih
Title
GEOFFREY CHUA TIONG SING
4/tt/1984
AUTOMATIC ACCESS CONTROL SYSTEM USING STUDENT
IDENTIFICATION CARD BASED ON RFID TECHNOLOGY
20tt/2012
declore
tl
[]
E
thot this thesis is clossified os :
CONFIDENTIAI (Conloins confidentiol informotion under the Officiot Secrel
Acl 1972)*
RESTRICTED (Conioins reslricted informotion os specified by the
orgonizotion where reseorch wos done)*
OPEN ACCESS I ogree thol my thesis to be published
os online open occess
(fulltext)
I ocknowledged thot UniversiliTeknologi Moloysio reseryes the right os follows:
'1.
The thesis is lhe property
of UniversiliTeknologiMoloysio.
2. The Librory of UniversitiTeknologi Moloysio hos the righl to moke copies for ihe purpose
of reseorch only.
3. The Librory hos the right to moke copies of lhe lhesis for ocodemic exchonge.
Acodemic Session:
841104-13-5513
(NEW tC NO.
/PASSPORT NO.)
Dote : s'h JULY 2012
SIGNATURE OF SUPERVISOR
P.M DR. SULAIMAN BIN NOR
NAME OF SUPERVISOR
Dote : 5th JULY 2012
NOTES :
"I hereby declare that I have read this thesis and in my opinion
this thesis is sufhcient in terms of scope and quality for the award of the
Degree of Bachelor of Engineering (Electrical
-
Computer)"
Signature
)
Name of Supervisor
Date
P.M Dr. Sulaiman BinNor
5
JqLY ?orr.
AUTOMATIC ACCESS CONTROL SYSTEM USING STUDENT
IDENTIFICATION CARD BASED ON RFID TECHNOLOGY
GEOFFREY CHUA TIONG SING
A thesis submitted in fulfillment of the requirements for the award of the degree of
Bachelor of Engineering (Electrical Computer)
Faculty of Electrical Engineering
Universiti Teknologi Malaysia
JULY 2012
I declare that this thesis entitled "Automatic Access Control System Using Student
Identification Card Based On RFID Technolog,t" is the result of my own research
except as cited in the references. The thesis has not accepted for any degree and is
not concurrently submitted in candidature of any other degree.
Signature
Name
Date
cssffreylhgs_Tlg! g S in g
5th Julv 2012
iii
Dedicated with love to my family members especially my beloved parent,
Mr. Chua Tien Ing and Madame Toh Mi Hua
For their infinite and unfading love, sacrifice, patience, encouragement and endless
support.
iv
ACKNOWLEDGEMENTS
Many people contributed to this project and, I would like to thank them all. I
first want to express my deep appreciation to P.M. Dr. Sulaiman Bin Nor for his
invaluable advice, guidance and his enormous patience throughout the development
of the research. I will be forever grateful for his professionalism, knowledge and
experience sharing in this study. This thesis would not have been the same as
presented here without his.
Finally, I would also like to express my gratitude to my loving parent and my
fellow friends who had helped, support and given me encouragement to face this
challenging project until to the end.
v
ABSTRACT
RFID, Radio Frequency Identification is an inexpensive technology, can be
implemented for several applications such as security, asset tracking, people tracking,
inventory detection, access control applications. RFID technology which is a
matured technology that has been widely deployed by various organizations as part
of their automation systems. The main objective of this project is to design and
implement an RFID automatic access control system which student need to use their
student identification card to access the door where only authentic person can be
entered or record the attendance during the class. This system consists of two main
parts which include: the hardware and the software. The hardware consists of the PIC
16F877A microcontroller, relay, magnetic lock, switch, LCD display, RFID reader
and power supply circuit. The USB serial communication will communicate to the
host computer where it was interfaced with the PIC 16F877A send the data to the
host computer. Therefore, graphic user interface program provides the provides the
functionalities of the overall system such as displaying live ID tags transactions,
registering ID, deleting ID, recording attendance and other minor functions which it
was developed using visual basic 2010. Besides that, it also was implemented a
security system containing door locking system using passive type of RFID which
can activate, authenticate, and validate the user and unlock the door in real time for
secure access. The advantage of using passive RFID is that it functions without a
battery and passive tags are lighter and are less expensive than the active tags. The
door locking system functions in real time as the door open quickly when user put
their tag in contact of reader. The system also creates a log containing check-in and
check-out of each user along with basic information of user.
vi
ABSTRAK
RFID, Pengenalan Frekuensi Radio merupakan teknologi yang murah, boleh
dilaksanakan untuk beberapa aplikasi seperti keselamatan, pengesanan aset, orang
menjejaki, inventori pengesanan, aplikasi kawalan akses. Teknologi RFID yang
merupakan satu teknologi yang matang yang telah banyak digunakan oleh pelbagai
organisasi sebagai sebahagian daripada sistem automasi mereka. Objektif utama
projek ini ialah untuk merekabentuk dan melaksanakan RFID automatik akses
kawalan sistem yang pelajar perlu menggunakan kad pengenalan pelajar untuk
mengakses pintu di mana hanya orang yang sahih boleh dimasukkan atau
merekodkan kehadiran semasa kelas. Sistem ini terdiri daripada dua bahagian utama
yang termasuk: perkakasan dan perisian. Perkakasan terdiri mikropengawal PIC
16F877A, geganti, kunci magnet, suis, paparan LCD, pembaca RFID dan litar
bekalan kuasa. Komunikasi USB siri akan berkomunikasi dengan komputer hos di
mana ia adalah diantaramukakan dengan PIC 16F877A menghantar data kepada
komputer hos. Oleh itu, program antara muka pengguna grafik menyediakan
menyediakan kefungsian keseluruhan sistem seperti memaparkan transaksi tags ID
hidup, mendaftar ID, ID memotong, merekodkan kedatangan dan lain-lain fungsi
kecil yang dibangunkan dengan menggunakan 2010 asas visual. Selain itu, ia juga
telah melaksanakan sistem keselamatan yang mengandungi sistem mengunci pintu
menggunakan jenis pasif RFID yang boleh mengaktifkan, mengesahkan, dan
mengesahkan pengguna dan membuka pintu dalam masa nyata untuk akses selamat.
Kelebihan menggunakan pasif RFID adalah bahawa ia berfungsi tanpa tag bateri dan
pasif lebih ringan dan kurang mahal daripada tag aktif. Sistem ini juga mewujudkan
log yang mengandungi daftar masuk dan daftar keluar setiap pengguna bersama-
sama dengan maklumat asas pengguna.
vii
TABLE OF CONTENTS
CHAPTER TITLE PAGE
TITLE PAGE i
DECLARATION ii
DEDICATION iii
ACKNOWLEDGEMENTS iv
ABSTRACT v
ABSTRAK vi
TABLE OF CONTENTS vii
LIST OF TABLES x
LIST OF FIGURES xi
LIST OF ABBREVIATIONS xiv
LIST OF APPENDICES xv
1 INTRODUCTION 1
1.1 Background of the Study 1
1.2 Problem Statement 3
1.3 Objectives of Project 4
1.4 Scope of Project 4
1.4.1 Hardware Part 5
1.4.2 Software Development 5
1.5 Report Outline 6
1.6 Project Planning 6
viii
2 LITERATURE REVIEW 8
2.1 Introduction 8
2.2 Radio Frequency Identification (RFID) 9
2.3 The Principle of RFID Technology 11
2.4 RFID Reader 13
2.5 RFID Tag 14
2.5.1 Passive Tag 15
2.5.2 Semi Passive 16
2.5.3 Active 16
2.6 RFID Frequencies 17
2.6.1 Operating Frequency 18
2.6.2 Range 18
2.6.3 Memory Capacity 18
2.7 Conventional Door Security System 19
2.8 Key Interlock Conventional 19
2.9 Microcontroller 22
2.9.1 PIC 16F877A 24
2.10 USART (Universal Synchronous Asynchronous
Transmitter) 25
2.11 Serial Communication Interface 26
2.11.1 UC00A USB to UART Converter 27
2.12 Microsoft Visual Basic 2010 28
3 METHODOLOGY 29
3.1 Introduction 29
3.2 Hardware Implementation 31
3.2.1 RFID Tag and Reader 31
3.2.2 Programming a Microcontroller 35
3.2.3 Power Supply Circuit 37
3.2.4 Push Button as input for PIC microcontroller 37
3.2.5 Relay circuit 38
3.2.6 Interface LCD Display circuit with PIC16F877A 39
ix
3.2.7 Interface WIEGAND RFID reader with
PIC16F877A 41
3.2.8 ICSP for programming PIC microcontroller 42
3.3 Software Implementation 42
3.3.1 Programming in Microsoft Visual Basic 2010 42
4 RESULTS AND DISCUSSIONS 44
4.1 Introduction 44
4.2 Hardware System 45
4.2.1 Door Access System Mode 46
4.2.2 Class Attendance System Mode 48
4.3 Software System 49
4.3.1 Graphic User Interface 49
4.3.2 Admin 50
4.3.3 Main Menu 51
4.3.4 Database 52
4.3.5 Edit 53
4.3.6 Database Record 54
4.3.7 Door Record 55
4.3.8 Class Record 56
5 CONCLUSIONS AND RECOMMENDATIONS 57
5.1 Conclusions 57
5.2 Future Work and Improvement 58
REFERENCES 60
Appendices A-B 61-82
x
LISTS OF TABLES
TABLE NO. TITLE PAGE
2.1 Comparison between RFID systems with others technology
systems 11
2.2 Type of frequency range for RFID system 19
3.1 LCD connection pin and function of each pin 40
3.2 Wires description of RFID Reader 41
xi
LISTS OF FIGURES
FIGURE NO. TITLE PAGE
1.1 Gantt chart final year project 1 for smester one 7
1.2 Gantt chart of final year project 2 for smester two 7
2.1 Transponder and Reader of RFID system 10
2.2 Typical RFID Tag 12
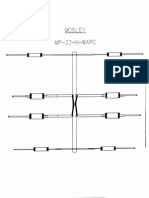
2.3 Operating principle of a simple key interlock mechanism 21
2.4 Pin Diagram PIC 16F877A 25
2.5 UC00A USB to UART converter 27
3.1 The complete block diagram of RFID system 30
3.2 Wiegand 125 kHz RFID reader 32
3.3 RFID tag (86 x 54 x 1.05mm) 32
3.4 Setting the HyperTerminal properties 34
3.5 Writing a program using MPLAB 35
xii
3.6 PICkit 2 Programming Software 36
3.7 Power supply circuit 37
3.8 Push button circuit 38
3.9 Relay circuit 39
3.10 LCD Display circuit 40
3.11 RFID wiegand connection circuit 41
3.12 Connection between PIC16F876A and programmer 42
4.1 RFID automatic door access control circuit 45
4.2 Place the tag on the reader by user for door access system 47
4.3 User ID didnt match with the ID saved 47
4.4 User ID found and match with ID saved 48
4.5 Place the tag on the reader by user for class attendance access
system 49
4.6 Login in window form 50
4.7 Main menu window form 51
4.8 Search user profile by admin 52
4.9 Edit user profile by admin 53
xiii
4.10 Student record information from database system 54
4.11 Record the door access of user information to the database system 55
4.12 Record the class attendance of user information to the database
system 56
xiv
LIST OF ABBREVIATIONS
ASCII - American Standard Code for Information Interchange
CMOS - Complementary Metal Oxide Semiconductor
CPU - Central Processing Unit
DBMS - Database Management System
EEPROM - Electrically Erasable Programming ROM
GUI - Graphical User Interface
HF - High Frequency
I/O - Input/Output
IC - Integrated Circuit
ID - Identification
LCD - Liquid Crystal Display
LED - Light Emitting Diode
LF - Low Frequency
MCU - Microcontroller Unit
PIC - Peripheral Interface Controller
RAM - Random Access Memory
RFID - Radio Frequency Identification
ROM - Read Only Memory
UHF - Ultra High Frequency
USART - Universal Synchronous Asynchronous Receiver Transmitter
VB - Microsoft Visual Basic 2010
xv
LIST OF APPENDIX
APPENDIX TITLE PAGE
A Program coding of RFID automatic door access control system
using MPLAB v8.3 61
B Source Code of Visual Basic 2010 for GUI Program 72
CHAPTER 1
INTRODUCTION
1.1 Background of the Study
In our real life, security system plays an important role to prevent unknown user
or robbery entry secured place without authorized from owner. The security system was
basically divided into two types: used normal door lock key and used electronic
automatic identification system. In general, locks are very simplistic device that are
employed to address very a straightforward problem. Basically, lock was easy be hacked
by unwanted people allowing unauthorized people in. The lock system was not real
practical used in security system and easy explores to high risk enable thieves hack this
system.
Therefore, there was several automatic identification technology including bar
code, magnetic stripe and Radio-frequency identification (RFID) applied in security
system. Radio-frequency identification (RFID) is an emerging technology and one of
most rapidly growing segments of todays automatic identification data collection
industry. RFID usage is steadily increasing and companies across many industries are
2
now looking at RFID to streamline operations, meet regulatory requirements and prevent
the introduction of counterfeit product into the supply chain to protect both consumer
safety and company profitability.
Industry experts view RFID not as competition with, but as a complement to
barcode technology in many case such as tracking pallets, cartons and cases in a
warehouse which both technology are used. RFID technology, in fact, overcomes certain
limitations found in some barcode applications. Because it is not an optical technology
like bar coding, no inherent line of sight is required between the reader and the tagged
RFID objects. In addition, RFID transmits data wirelessly and is a read/write
technology, so it can update or change the data encoded in the tag during the tracking
cycle.
Since, the RFID technology used widely based on the business requirements of
the organization for end users. This project will implement the RFID technology to
replace the conventional lock system to tighten the security system in UTM. This RFID
system monitor the incoming and outgoing people when they entry any door in UTM.
All of UTM stuffs and student will be given RFID tag which is their identification cards
know as a smart cards. The RFID reader transmits a signal that is received by an antenna
intergraded and the chip is activated only when an RFID reader scans it. It will send the
unique identifier number to the application of the host computer. The host computer will
compare the details is valid or not in the database. The host computer application will
display the user information if the tags is valid.
3
1.2 Problem Statement
The criminal rate inside UTM was increased every year as reported by the police
office UTM stuffs. A lot of student is complaint to the security department when they
were lost their handphone and laptop although they lock the room door in their hostels.
The UTM police find difficult to track the thieves after the students make police report.
This is due the poor security system monitor the traffic when they go out or go inside
their own hostel room. Besides that, most of the hostel room still using the conventional
lock system and it will explore treat for those who stay at hostel. The thieve easy
duplicate room key and open the door to stole money, handphone or laptop because this
is the most expensive thing own by student.
Meanwhile, the UTM stuff also facing problem when the expensive lab machine,
equipment or material put inside the lab or store was not secured and easy stole by the
thieve. The main reason behind of this case was UTM applied the conventional lock
system everywhere either using in lab, office or store room. Even through UTM
currently using CCTV system monitor the incoming people enter the restrict area but its
look hard to prevent the thieves stole their valuable machine or equipment.
However, the automatic access control system using student identification card
based on RFID system was proposed after concerning the UTM security and problem
face by all users when they enter the door. This RFID system can detect the valid card of
user to entry the door and monitor, record the people who access the door without using
the key.
Meanwhile, lecturers also face some problem of the class attendance system
since the lecturer need manual print out the paper to let the student to sign their
4
attendance during the class. The attendance sign using the paper is not user friendly
environment and its hard to keep a long period of time in the good condition as a record
attendance for the lecture to keep it.
1.3 Objective of Project
The objective of this project was to design and develop RFID system which
utilizes the usage of RFID technology replace the conventional lock system in order to
improve effective and efficient security system exist in UTM. Following are specific
objectives need to achieved in order to complete this project.
i. To design and build an RFID based door access system and class
attendance system using student ID for the access
ii. To design and develop Graphical User Interface (GUI) software to input
student profile which is stored in a database and can be used by the door
access system and class attendance system.
1.4 Scope of project
This project is divided to two main parts to design the automatic access control
system using student identification card based on RFID technology. There are hardware
part and software part. The scope of this project will explain as below:
5
1.4.1 Hardware part
This project can be further divided into three parts which is input, control system
and output. The RFID reader and tag are the devices used as the input. The control
system was developed using PIC16F877A microcontroller and it connects with the
database system. Meanwhile, the 2x16 LCD display chosen as output of the electronic
hardware parts.
1.4.2 Software development
The PIC microcontroller needs to be programmed first before it can be used in
the electronic hardware. The C programming language is chosen to program the
PIC16F877A microcontroller under MPLAB IDE. Correct and functional code ensure
the microcontroller to work properly and accordingly. The functionality of the code is
verified using MPLAB SIM, one of the components included in MPLAB IDE and PIC
Simulator IDE. Protel DXP is used to draw the schematic diagram and design the layout
for the printed circuit Board. The layout of the printed circuit board is designed by using
manual routing of the connections of each electronic component involved in developing
the system.
Besides that, the system requirements a database to store all the user information
so that the database was constructed using service based SQL database. After that, the
programming to monitor the system is formed by using Microsoft Visual Basic 2010.
Lastly, to comprehensive this project, interface between the RFID system and the host
computer was completed using serial interface.
6
1.5 Report Outline
Chapter 1 reviews the background of the security system and continues with the
objective of this project. Then, it follows by the problem statement of this project to
determine the title of this project, the scope of the project and the grant chart to complete
this project. Chapter 2 was start from the literature review which has related previous
work or fact was involved. Chapter 3 was discussed the research methodology to
achieve the purpose of this project. Chapter 4 was discussed the result of RFID
automatic access control system based on RFID technology and visual basic interface
with database system. Chapter 5 was explained the expected outcome achieve on the
final year project 2 which is the complete the RFID automatic access control system
with database system.
1.6 Project Planning
The project was scheduled by allocating into several jobs. The period of each job
has been prepared and it has been designated in Gantt chart below.
7
Figure 1.1: Gantt chart final year project 1 for smester one
Figure 1.2: Gantt chart of final year project 2 for smester two
8
CHAPTER 2
LITERATURE REVIEW
2.1 Introduction
The growing number of illegal entry cases over the years, require of many
companies encouraged to design and production for automated door security systems.
Door security systems are intended to look after houses, shops, offices and additional
buildings from enforced entry and reduced the chances of theft. Door security systems
can be install on dissimilar types of entries such as metal, wood, plastic, glass and
fiberglass. They are existing in different conditions to outfit the security necessities of
different types of buildings. Home security systems may contain of a PIN enabled
electronic securing device, whereas top door security systems are regularly combine
with invader alarms and security combination lock to offer greater security.
This chapter reviews some of the journal or studies which associated with this
topic such as show effective use RFID technologies now generations in some application
and reputation of a RFID system in security system .Besides, this chapter analyses some
principles for the important device used in this project. Therefore, some conventional
door security system was explained here.
9
2.2 Radio Frequency Identification (RFID)
According to Harvey Lehpamer in studies of RFID design principles where
Radio frequency identification (RFID) technology is interesting extensive attention as an
accompaniment or even substitute for bar code because of the substantial range, speed
and unattended reading advantages it affords. However, users should expect more than
improved analysis before participating in an RFID system. RFID has read/write ability,
and users can reveal the full worth and benefits of the expertise by taking advantage of
the capability to add and change data on the tag in real time. Read/write RFID creates
many new applications in the supply chain and helps accommodate changes in business
processes, customer requirements or standards.
RFID is expected to become persistent and universal, as it can be embedded into
everyday items as smart labels. A typical RFID system comprises of a base radio
transmitter/receiver, or reader, RF transponders or tags and the back-end database that
associates records with tag data collected by readers. The RFID reader consists of an
antenna, a radio interface, and a control unit that has an ability to interrogate and display
electronic code held in a remote device, transponder and thus identify any item with
which the transponder is associated. The reader control unit will execute the
communication protocol with the tags and then interprets the data received from the
tags. While the radio interface will perform detection, modulation and demodulation of
the readers signal and the tags replies. The readers communicate wirelessly with the
tags to obtain the information stored on them. The data sent by the reader is modulated
and backscattered from a number of tags.
RFID system is always made up of two components (Refer to Figure 2.1):
The transponder, which is located on the object to be identified.
10
The interrogator or reader, which depending upon the design and the
technology used, may be a read or write/read device.
A reader typically contains a radio frequency module (transmitter and receiver),
a control unit and a coupling element to the transponder. In addition, many readers are
fitted with an additional interface (RS 232, RS 485, etc) to enable them to forward the
data received to another system (PC, robot control system, etc).
Figure 2.1: Transponder and Reader of RFID system
The transponder, which represents the actual data-carrying device of an RFID
system, normally consists of a coupling element and an electronic microchip. When the
transponder, which does not usually possess its own voltage supply (battery), is 5 not
within the interrogation zone of a reader it is totally passive. The power required to
activate the transponder is supplied to the transponder through the coupling unit
(contactless), as are the timing pulse and data.
RFID system has better characteristic in identification system compared to others
technology. Table 2.1 shows the advantages of RFID system according to system
parameters given.
11
Table 2.1: Comparison between RFID systems with others technology systems
2.3 The Principle of RFID Technology
The RFID tag is essentially a memory device with a means of revealing and
communicating its memory contents, when prompted (scanned) to do so. The memory
consist of a plurality of binary (two state) digits, also known as bits, and the
12
communication comprises RF reception and transmissions means. The binary data (bits)
are formed into binary words comprising typically 8, 16 or 32 bits that can make up
letters and numbers in the same manner as in computing, the Internet and texts on a
mobile phone. The tag may comprise an electronic circuit (printed circuit board) with its
own power supply an active device; or be a very low power integrated circuit that is
able to gain enough energy from the scanner/reader RF signal to actually power itself for
long enough to transmit the contents of its memorya so called passive device. In its
passive embodiment RFID tag transmission power is very low and measured in
millionths of a watt i.e. microwatts (W). Figure 2.2 shows diagrammatically one of the
latter style devices which may be found on products, particularly consumer durables.
Figure 2.2: Typical RFID Tag
The typical RFID tag portrayed in Figure 2.2, comprises a host substrate which is
typically but not exclusively, a flexible (polymer), with an attached flexible etched
aluminum alloy or conductive antenna, plus a small (few millimeters square) attached
integrated circuit connected to the antenna. The whole assembly is typically 30
millimeters square, a fraction of a millimeter thick and is encapsulated so that it forms a
13
flexible durable, attachable label. The data in the RFID tag memory may be pre-loaded
(determine at time of manufacture) as Read Only Memory (ROM), or may be
dynamically variable (Static Random Access Memory) and take up the status of the last
write/read cycle. The data is always read out serially so that it can be correctly parsed.
The information contained in the RFID tag memory is deliberately kept to a minimum
and typically, dependent upon the data format (its syntax, numerical format decimal,
hexadecimal etc.) requires translating into a human readable form via host system.
2.4 RFID Reader
The RFID reader sends a pulse of radio energy to the tag and listens for the tags
response. The tag detects this energy and sends back a response that contains the tags
serial number and possibly other information as well. In simple RFID systems, the
readers pulse of energy functioned as an on-off switch; in more sophisticated systems,
the readers RF signal can contain commands to the tag, instructions to read or write
memory that the tag contains, and even passwords. Historically, RFID reader were
designed to read only a particular king of tag, but so-called multimode readers that can
read many different kinds of tags are becoming increasingly popular.
RFID readers are usually on, continually transmitting radio energy and awaiting
any tags that enter their field of operation. However, for some applications, this is
unnecessary and could be undesirable in battery-powered devices that need to conserve
energy. Thus, it is possible to configure an RFID reader so that it sends the radio pulse
only in response to an external event. For example, most electronic toll collection
systems have the reader constantly powered up so that every passing car will be
recorded. On the other hand, RFID scanners used in veterinarians offices are frequently
14
equipped with triggers and power up the only when the trigger is pulled. Like the tag
themselves, RFID readers come in many size. The largest readers might consist of a
desktop personal computer with a special card through shielded cable. Such A reader
would typically have a network connection as well so that it could report tags that it
reads to other computers. The smallest readers are the size of a postage stamp and are
designed to be embedded in mobile telephones.
Nowadays lot of RFID reader sold with multiple brands such as Mifare, Hitachi,
and Philip. Because of the major application used in worldwide, many systems require
the simultaneous use of more than one operating frequency. Most systems available on
the world market at present operate at one of the following frequencies or frequency
ranges: below 135 kHz (125 kHz, 134.2kHz for example), 13.56MHz, UHF (860/960
MHz), 2.45GHz and 5.8GHz. The operating and control characteristics are different for
each of these frequencies, and therefore each of them is more appropriate for certain
types of application or certain countries.
2.5 RFID Tag
The tag, also known as the transponder (derived from the terms transmitter and
responder), holds the data that is transmitted to the reader when the tag is interrogated by
the reader. The most common tags today consist of an Integrated Circuit with memory,
essentially a microprocessor chip. Other tags are chipless and have no onboard
Integrated circuit. Chipless tags are more effective in applications where simpler range
of functions is all that is required; although they can help achieve more accuracy and
better detection range, at potentially lower cost than their Integrated Circuit-based
counterparts. From here on out, we will use the term tag to mean Integrated Circuit-
15
based tag. We will refer to chipless tags explicitly, when needed. RFID tags come in two
general varieties which are passive and active tag. Passive tags require no internal power
source, thus being pure passive devices (they are only active when a reader is nearby to
power them), whereas active tags require a power source, usually a small battery.
2.5.1 Passive Tag
Passive RFID tags have no internal power supply. The minute electrical current
induced in the antenna by the incoming radio frequency signal provides just enough
power for the CMOS integrated circuit in the tag to power up and transmit a response.
Most passive tags signal by backscattering the carrier signal from the reader. This means
that the antenna has to be designed to both collect powers from the incoming signal and
also to transmit the outbound backscatter signal. The response of a passive RFID tag is
not necessarily just an ID number; the tag chip can contain non-volatile EEPROM for
storing data. The lack of an onboard power supply means that the device can be quite
small: commercially available products exist that can be embedded in a sticker, or under
the skin in the case of low frequency RFID tags.
The advantages of a passive tag are:
a) The tag functions without a battery; these tags have a useful life of twenty
years or more.
b) The tag is typically much less expensive to manufacture
c) The tag is much smaller (some tags are the size of a grain of rice). These tags
have almost unlimited applications in consumer goods and other areas.
16
2.5.2 Semi Passive
It is similar to passive tag, the only difference is it have addition of a small
battery. This battery allows the tag IC to be constantly powered which removes the need
of an aerial to be designed to collect power from the incoming signal. As semi passive
tag is preenergized, they can be read more reliably in this more difficult environment.
2.5.3 Active
Active tag has their own internal power source which is used to power any ICs
that generate the outgoing signal. They are more reliable and sophisticated (fewer errors)
due to the ability for active tag to conduct a session with a reader. Because of their
onboard power supply also transmit at higher power level than passive tags, allowing
them to be more effective in RF challenged environments such as water, metal or at
longer distances. Active tags have on board battery for power to transmit data signal
over a greater distance and power random access memory (RAM) giving them the
ability to store up to 32,000 bytes of data. A battery can live up to 10 years and have
practical ranges of hundreds of meters. Types of tags that were used in the RFID system
are ISO card, clamshell card and also soft label. Tag used in this project is passive tag
and the model of RFID reader is RFIDIDR-232N.
Benefits of RFID tag:
a) Tags can be read from a distance and from any orientation.
b) Capabilities of read and write, which allow data to be changed dynamically at
any time.
17
c) Multiple tags can be read simultaneously and in bulk very quickly.
d) RF tags can easily embed into any non-metallic product. This feature allows
the tag to work in harsh environment providing permanent identification for the
life of the product.
2.6 RFID Frequencies
RFID operates in several frequency bands. The exact frequency is controlled by
the Radio Regulatory Body in each country. The generic frequencies for RFID are
shown below:
LF (125-134 kHz)
HF (13.56 MHz)
UHF (400-930 MHz)
Hyper Frequency (2.45 GHz)
5.8 GHz
Each of the frequency bands has advantages and disadvantages. The lower
frequency 125-134 kHz and 13.56 MHz work much better near water or human than do
the higher frequency tags. Comparing with the passive tags, lower frequency has less
range and slower data transfer rate. There has been an enormous upsurge in the
popularity of RFID systems in recent years and it is difficult for a specialist to retain an
overview of the range of RFID systems currently on offer. Therefore, it is not always
easy for user to select the system best suited to their needs.
18
2.6.1 Operating Frequency
RFID systems that use frequencies between approximately 100 kHz and 30 MHz
operate using inductive coupling. By contrast, microwave systems in the frequency
range 2.45-5.8 GHz are coupled using electromagnetic fields.
2.6.2 Range
The required range of an application is dependent upon several factors:
1. The positional accuracy of the transponder.
2. The minimum distance between several transponders in practical operation.
3. The speed of the transponder in the interrogation zone of the reader.
2.6.3 Memory Capacity
The chip size of the data carrier and thus the price class is primarily determined
by its memory capacity. If data is to be written back to the transponder, a transponder
with EEPROM or RAM memory technology is required. EEPROM memories are
primarily found in inductively coupled systems. Memory capacities of 16 bytes to 8K
bytes are available.
19
Table 2.2: Type of frequency range for RFID system
Range Class LF HF UHF
Frequency Range 120-135 KHz 13.56 MHz 868-956 MHz
Maximum Range? 3 meters 3 meters 10 meters
Typical Range 10-20 centimeters 10-20 centimeters 3 meters
2.7 Conventional Door Security System
Conventional key interlock system is the wells known system in the previous
year. In this era, the manufacturer found the new alternatives for door security system
such as electronic access control system. There are much kind of electronic access
control system for security door such as magnetic stripe card, smart card and keypad
system.
2.8 Key Interlock Conventional
An interlock system is a most well-known security for over past year and it also
is a series of key interlocks applied to associated equipment in such a manner as to allow
operation of the equipment only in a prearranged sequence. Interlocks are applicable to
practically any field where in human life or protecting property, by an improper
20
operation or improper sequence of operations. It is necessary to fully appreciate how a
keyed interlock operates and how it works in conjunction with the equipment on which
is mounted.
A typical keyed interlock is comprised of a lock cylinder, support housing, a
moveable locking bolt, and a cam arranged to move the bolt in response to operation of
the correct key. Various styles of interlock housings are available and each style is
designed to mount in a different way depending upon the equipment to which the
interlock is to be installed.
One of the most important features a keyed interlock is that key cannot be
removed from all position of the lock bolt. A conventional lockset may allow free
removal of the key regardless of the position of the lock bolt. The function of an
interlock, however, dictates that key be held in the lock cylinder unless the lock bolt is in
a predetermined position. Possession of the key ensures that the associated device has
been locked in a known safe position.
About the operating principle of interlock system, there are four steps to unlock
the lock. Figure 2.4 illustrates how an individual interlock typically works in
conjunction with the equipment to which it is installed. In figure 2.3 (a), the controlled
device (such as a switch) cannot move from its normal position (whether open or closed)
because of the position of the lock bolt. When the key is turned to withdraw the lock bolt
(figure 2.3 (b) ), the key becomes trapped and the controlled device is moved, the key
remains held because the lock bolt can no longer be physically extended so as to free the
key (figure 2.3 (c)) .
21
Figure 2.3: Operating principle of a simple key interlock mechanism
The typically controlled device has two operating positions. If the intent is to
lock the controlled device in either position, the arrangement of figure 2.3(a) may
instead provide a recess on two opposite sides of the rotating member. In this manner,
the lock bolt can be extended and the key released with the controlled device in either of
two positions. Such an arrangement is described as (L-O-C) locked open or closed (see
figure 2.3(d)).
22
2.9 Microcontroller
A microcontroller is programmable single-chip integrated circuit (IC) that
controls the operation of a system. A microcontroller contains memory for program
information and data. It has logic for programmed reading inputs, manipulating data and
sending outputs. In other words, it has built-in interfaces for input/output (I/O) as well as
a central processing unit (CPU). A microcontroller is normally known as a
Microcontroller Unit (MCU).
Microcontrollers must contain at least two primary components random access
memory (RAM), and an instruction set. RAM is a type of internal logic unit that stores
information temporarily. RAM contents disappear when the power is turned off. While
RAM is used to hold any kind of data, some RAM is specialized, referred to as registers.
The instruction set is a list of all commands and their corresponding functions. During
operation, the microcontroller will step through a program (the firmware). Each valid
instruction set and the matching internal hardware that differentiate one microcontroller
from another.
Most microcontrollers also contain read-only memory (ROM), programmable
read-only memory (PROM), or erasable programmable read-only memory (EPROM).
Al1 of these memories are permanent: they retain what is programmed into them even
during loss of power. They are used to store the firmware that tells the microcontroller
how to operate. They are also used to store permanent lookup tables. Often these
memories do not reside in the microcontroller; instead, they are contained in external
ICs, and the instructions are fetched as the microcontroller runs. This enables quick and
low-cost updates to the firmware by replacing the ROM.
23
Where would a microcontroller be without some way of communicating with the
outside world? This job is left to input/output (I/O) port pins. The number of I/O pins per
controllers varies greatly, plus each I/O pin can be programmed as an input or output (or
even switch during the running of a program). The load (current draw) 18 that each pin
can drive is usually low. If the output is expected to be a heavy load, then it is essential
to use a driver chip or transistor buffer.
Most microcontrollers contain circuitry to generate the system clock. This square
wave is the heartbeat of the microcontroller and all operations are synchronized to it.
Obviously, it controls the speed at which the microcontroller functions. All that needed
to complete the clock circuit would be the crystal or RC components. We can, therefore
precisely select the operating speed critical to many applications.
To summarize, a microcontroller contains (in one chip) two or more of the
following elements in order of importance:
i. Instruction set
ii. RAM
iii. ROM,PROM or EPROM
iv. I/O ports
v. Clock generator
vi. Reset function
vii. Watchdog timer
viii. Serial port
ix. Interrupts
x. Timers
xi. Analog-to-digital converters
xii. Digital-to-analog converters
24
2.9.1 PIC 16F877A
PIC stands for Peripheral Interface Controller, general instrument as small, fast,
inexpensive embedded microcontroller with strong input/output capabilities. The
PIC18F877A is CMOS Flash-based 8 bit microcontroller. It packs into 40-pin package
with 3 ports for input/output which are Port A, Port B, Port C and Port D.
In this project, PIC16F877A will be use. PIC16F877A is in either baseline core
or mid-range core devices in the PICs family core architecture. PIC16F877A also have
enhanced core features, eight-level deep stack, and multiple internal and external
interrupt sources.
PIC18F877A has been chosen because of its USART (Universal Serial
Asynchronous Receiver Transmitter) function. In this project, USART is used to
communicate between hardware and PC serial port. The details explanation of USART
function will be discussed in the next sub-chapter. Besides, this microcontroller also has
input/output port just enough for the project application where figure 2.4 shows Pin
Diagram for PIC18F877A.
25
Figure 2.4: Pin Diagram PIC 16F877A
2.10 USART (Universal Synchronous Asynchronous Transmitter)
USART (Universal Synchronous Asynchronous Transmitter) USART stands for
Universal Synchronous Asynchronous Receiver Transmitter. It is sometimes called the
Serial Communications Interface or SCI. Synchronous operation uses a clock and data
line while there is no separate clock accompanying the data for Asynchronous
transmission. Since there is no clock signal in asynchronous operation, one pin can be
used for transmission and another pin can be used for reception. Both transmission and
reception can occur at the same time, this is known as full duplex operation.
Transmission and reception can be independently enabled. However, when the serial
port is enabled, the USART will control both pins and one cannot be used for general
purpose I/O when the other is being used for transmission or reception. The USART is
most commonly used in the asynchronous mode. The most common use of the USART
in asynchronous mode is to communicate to a PC serial port using the RS-232 protocol.
26
2.11 Serial Communication Interface
Serial communication is a very common protocol for device communication that
is standard on almost every PC. Most computers include two serial ports. Serial
communication is also a common communication protocol that is used by many devices
for instrumentation, numerous GPIB-compatible devices also come with a serial
communication port. Furthermore, serial communication can be used for data acquisition
in conjunction with a remote sampling device. Serial communication only sends or
receives a single bit at a time. Although this is slower than parallel communication,
which allows the transmission of an entire byte at once, it is simpler and can be used
over longer distances.
Serial communication has two types which are asynchronous and synchronous
communications. Synchronous communication requires more complex interface and
clock is sent along with data with higher rate than asynchronous communication.
Synchronous communication requires that each end of an exchange of communication
respond in turn without initiating a new communication. A typical activity that might
use a synchronous protocol would be a transmission of files from one point to another.
As each transmission is received, a response is returned indicating success or the need to
resend.
On the other hand, asynchronous communication is usually for a situation where
data can be transmitted intermittently rather than in a steady stream. For example, a
telephone conversation is asynchronous because both parties can talk whenever they
like. If the communication were synchronous, each party would be required to wait a
specified interval before speaking. The difficulty with asynchronous communications is
that the receiver must have a way to find the end of talks of the other side so that one
starts to speak. In computer communications, this is usually accomplished through
27
special bits to indicate the beginning and the end of each piece of data. Asynchronous
communication, therefore, has simpler interface and does not send clock, but requires
start and stop bits.
2.11.1 UC00A USB to UART Converter
Serial communication is most popular interface between device and this applies
to microcontroller and computer. UART is one of those serial interfaces. Classically,
most serial interface from microcontroller to computer is done through serial port (DB9).
However, since computer serial port used RS232 protocol and microcontroller used TTL
UART, a level shifter is needed between these interfaces. Recently, serial port of
computer have been phase out, it have been replaced with USB. Of course most
developer chooses USB to serial converter to obtain virtual serial port. The level shifter
is still necessary for UART interface.
Figure 2.5: UC00A USB to UART converter
28
2.12 Microsoft Visual Basic 2010
Microsoft Visual Basic 2010 is another milestone version of the most popular
programming language for building windows and web application. In modern software
development, however the language is only one of the components we use to build
applications. The most important component is the .NET Framework, which is an
indispensable component of every application and its actually more important than the
language itself.
The Framework contains all the functionality of the operating system and makes
it available to the application through methods. Methods are very similar to functions
which extend the basic capabilities of a language. The framework is a huge collection of
such methods, organized in units according to their role and in a way that makes it fairly
easy to locate the methods for the task at hand. The language and the Framework are the
two programming components absolutely necessary to build windows applications. Its
possible to develop applications with these two components alone, but the process would
be awfully slow.
The software development process relies on numerous tools that streamline the
coding experience. The third component is an integrated environment that hosts those
tools, enabling to perform many common tasks with point and click operations. Its
basically an environment in which it can design the forms with visual tools and write
code as well. This environment provided by visual studio is known as an integrated
development environment or IDE. It can actually design a functional data-driven
application without writing a single line of code. It can use similar tools in the same
environment to design a fancy data-driven web page without a single line of code.
Visual basic even provides tool for manipulating databases and allow switch between
tasks all in the same streamlined environment.
29
CHAPTER 3
RESEARCH METHODOLOGY
3.1 Introduction
The development of this system is divided in 2 main parts; the hardware and the
software. The hardware system consists of 2 main components; the RFID reader and tag,
and the microcontroller. Other components like, push buttons, LCD display and LEDs
will be integrated together as the inputs and the output of the microcontroller. The
hardware system can be placed at door located inside the UTM building.
For software implementation, Microsoft Visual Basic 2010 is used to operate as a
database and a GUI systems. Administrator can login into the system and able to check
necessary data which keeps a log of the ID, time and date of every user that enters the
system. It also can register new user according to their ID code of each tag. This
software system will be installed in a PC which is located inside the administration
office.
30
To connect the RFID reader between the PC and the hardware system, UART is
incorporated by using RS-232 (Serial Port) cable. This complete system can be placed at
both entrance and exit path.
Figure 3.1: The complete block diagram of RFID system
31
3.2 Hardware Implementation
3.2.1 RFID Tag and Reader
In this project, RFID 125 kHz tag and reader are used. The original plan to use
13.56 MHz RFID system was canceled due to high cost and high budget. However 125
kHz RFID system is affordable for this project. As long the RFID system can transmit
data to microcontroller and computer, it is assumed that the overall system can work
equally well with the 13.56 MHz RFID system.
The antenna technology 125 kHz RFID uses air-core or ferrite-core coil. Hence
the cost of each tag is very cheap (< RM 2.00) if we buy it in a big quantity. However,
the tag must be very near to the reader (> 5cm) for communication. It is similar with the
Touch n Go technology which is widely used in many type of transportation system,
especially at every toll plaza system in Malaysia. Since the RFID reader only reads
unique identification code from each tag, this LF tag is very suitable because it has less
memory and small data transfer rate (10kbit/s). The main advantage of using this LF tag
is that data transmitted between the tag and the reader is not affected by water or human
contact.
To simplify the understanding of using LF RFID system, the use of this
frequency is usually justified if:
The bit rate is not too high or not critical
The EMC problems are difficult to resolve
The operating range is medium (15cm, 30cm)
32
Figure 3.2: Wiegand 125 kHz RFID reader
Figure 3.3: RFID tag (86 x 54 x 1.05mm)
Wiegand is plug and play RFID reader. It has been designed with capabilities and
features of:
Low cost solution for reading passive RFID transponder tags.
Industrial grade casing for better outlook and protection.
Integrated RFID reader, antenna, LED, power cable and data cable.
33
Every reader has been tested before is being shipped.
9600 baud RS-232 serial interface (output only) to PC.
Fully operation with 5VDC power supply.
Buzzer as sound indication of activity.
Bi-color LED for visual indication of activity.
Standard RS-232 serial cable (Female) ready to plug to desktop PC or Laptop.
PS2 as power source from desktop PC.
2cm Reading range.
0.1s Response time.
Operating frequency: 125 kHz
The hardware connection must be setup before wiegand can be used. After
providing power to wiegand as seen in previous section, the LED will light ON with the
red / yellow colour. However, the communication line has to be connected to serial port
of PC. After both power and communication line are connected, the HyperTerminal
(software) have to be configured according to figure 3.4:
a) Open HyperTerminal
b) Choose COM1 (if connect to COM1)
c) Configure the properties of COM1 to:
a. Baud rate (Bits per second) = 9600
b. Data bits = 8
c. Parity = None
d. Stop bits = 1
e. Flow control = None
34
Figure 3.4: Setting the HyperTerminal properties
Wiegand is ready to read address of a 125 KHz passive tag. The tag can be
moved slowly towards RFID reader at approximately 2cm from the casing. Then, the
buzzer will sound, LED will turn to green and HyperTerminal will show the tags ID in
ASCII code. All the procedures mentioned above are important to identify either the
RFID reader is operating and sending the right tags ID to the microcontroller and PC.
3.2.2 Programming a Microcontroller
MPLAB IDE software and UIC00A (USB ICSP PIC Programmer) are used as
the hardware to program the microcontroller from PC to the microcontroller itself.
35
MPLAB IDE is a free, integrated GCC-based toolset for the development of embedded
applications employing Microchips PIC and dcPIC microcontrollers. The MPLAB IDE
runs as a 32-bit application on Microsoft Word, and includes several free software
components for application development, hardware simulation and debugging. MPLAB
also serves as a single, unified graphical user interface for additional Microchip and
third party software and hardware development tools. Both Assembly and C
programming language can be used with MPLAB. Figure 3.6 shows the image of a
program written using MPLAB IDE.
Figure 3.5: Writing a program using MPLAB
PICkit 2 Programming Software is a software which is used to write a program
directly to the targeted microcontroller together with the UIC00A. By importing a HEX
36
file that contains a specific program for desired microcontroller, this software will
automatically recognized the type of the targeted microcontroller and easily program it
by clicking the Write button. Details on how to program a microcontroller can be
referred at Cytron Malaysia Official Website. Figure 3.9 shows the detail of each
function inside the PICkit 2 Programming Software.
Figure 3.6: PICkit 2 Programming Software
37
3.2.3 Power Supply Circuit
Higher input voltage will produce more heat at LM7805 voltage regulator.
Typical voltage is 12V. Anyhow, LM7805 will still generate some heat at 12V. There
are two type of power connector for the circuit, DC plug (J1) and 2510-02 (Power
Connector). Normally AC to DC adaptor can be plugged to J1 type connector. Refer to
Figure 3, the D1 is use to protect the circuit from wrong polarity supply. C1 and C2 is
use to stabilize the voltage at the input side of the LM7805 voltage regulator, while the
C3 and C4 is use to stabilize the voltage at the output side of the LM7805 voltage
supply. LED is a green LED to indicate the power status of the circuit. R1 is resistor to
protect LED from over current that will burn the LED.
Figure 3.7: Power supply circuit
3.2.4 Push Button as input for PIC microcontroller
One I/O pin is needed for one push button as input of PIC microcontroller. The
connection of the push button to the I/O pin is shown in Figure 3. The I/O pin should be
38
pull up to 5V using a resistor (with value range 1K- 10K) and this configuration will
result an active-low input. When the button is being pressed, reading of I/O pin will be
in logic 0, while when the button is not pressed, reading of that I/O pin will be logic 1.
Figure 3.8: Push button circuit
3.2.5 Relay circuit
A relay is a simple electromechanical switch made up of an electromagnet and a
set of contacts. Current flow through the coil of the relay creates a magnetic field which
attracts a lever and changes the switch contacts. The coil current can be ON or OFF so
relay have two switch positions and they are double throw (changeover) switches.
Relays allow one circuit to switch a second circuit which can be completely separate
from the first. For example a low voltage battery circuit can use a relay to switch a 230V
AC mains circuit. There is no electrical connection inside the relay between the two
circuits; the link is magnetic and mechanical. The coil of a relay passes a relatively large
39
current, typically 30mA for a 12V relay, but it can be as much as 100mA for relays
designed to operate from lower voltages. Most ICs (chips) cannot provide this current
and a transistor is usually used to amplify the small IC current to the larger value
required for the relay coil. Relays are usually Single Pole Double Throw (SPDT) or
Double Pole Double Throw (DPDT) but they can have many more sets of switch
contacts, for example relays with 4 sets of changeover contacts are readily available.
Figure 3.9: Relay circuit
3.2.6 Interface LCD Display circuit with PIC16F877A
The MCC162A4-5 dot-matrix liquid crystal display controller and driver LSI
displays alphanumeric, Japanese kana characters, and symbols. It can be configured to
drive a dot-matrix liquid crystal display under the control of a 4-bit or 8-bit
microprocessor. Since all the functions such as display RAM, character generator, and
liquid crystal driver, required for driving a dot-matrix liquid crystal display are internally
provided on one chip, a minimal system can be interfaced with this controller/driver. A
single MCC162A4-5 can display up to 16 characters in two lines. LCD display consists
40
of 16 pins and the connection of LCD to PIC16F877A microcontroller is shown in
Figure 3.10. The function of each pin is shown in Table 3.1.
Figure 3.10: LCD Display circuit
Table 3.1: LCD connection pin and function of each pin
41
3.2.7 Interface WIEGAND RFID reader with PIC16F877A
For this project, it has to connect the wire of RFID reader to a 2510-04 female
connector. There are 6 output wire of RFID reader, only 4 are used in this project. This
circuits connect only four (green, white, red and black) of the wire to 2510-04 female
connector according to the colour of the wire.
Figure 3.11: RFID wiegand connection circuit
Table 3.2: Wires description of RFID Reader
42
3.2.8 ICSP for programming PIC microcontroller
MCLR, RB6 and RB7 need to be connected to the USB In Circuit Programmer
(UIC00A) to program the PIC microcontroller. PIC Kit software is used to download the
*.hex file into the microcontroller. So, a simple circuit is built to connect PIC to the
programmer. After connect programmer to the computer and give supply to the simple
circuit, the PIC Kit window is open. It will detect the type of PIC microcontroller
automatically. Then the *.hex file can be downloaded into the PIC.
Figure 3.12: Connection between PIC16F876A and programmer
3.3 Software Implementation
3.3.1 Programming in Microsoft Visual Basic 2010
The Visual Basic 2010 software is used to design and program the Graphical
User Interface (GUI). The VB program will be designed so that the access time of the
43
user will be recorded to the database system once the user entered or exits the door. The
VB program will interact with two hardware of the system which is RFID reader and
serial communication port for the controller circuit. The VB program will initialize the
RFID reader and start reading the RFID tag of the user. Once the RFID unique code
detected, the VB program will call the database system to check whether the code stored
in the current database or not. If the code already exists in the database system, the VB
program will send an appropriate signal to the serial communication port to ON the
green LED. The LCD will display the tag ID and user name for the granted user. At the
same time, the details of the user will appear on the VB interface and get recorded.
Users Details is the database table to store the users information such as Name,
Tag ID, IC Number, course, category, date, check in time, check out time and photo as
well. The Record database would record down the time for all granted users who are
entering the area. The program would take the tag ID and match it with the Users Details
list to retrieve the users name and their personal information into the record list based
on the time they access it.
44
CHAPTER 4
RESULTS AND DISCUSSIONS
4.1 Introduction
In this chapter, all the result of experiments carries out in this project and
interpretation experiments both on the hardware and software part. This RFID automatic
access control system was successful integrated with graphic user interface system to
produce desired result which it fulfill this project objective.
From the previous chapter, this system has successful applied visual basic 2010
where it consists of admin form, database form, main menu form, door record form,
class record form, edit form and database record form interface using USB UART serial
communication with PIC 16F877A microcontroller. Based on the result, this system has
two main functions which were door access control system and class attendance system.
Both of this system can function well when the student use their own identification card
to enter door or to record the class attendance during the class. Everything regarding of
this final result and discussion on this system will further discuss detail in this chapter.
45
4.2 Hardware System
In this project, this PIC 16F877A based project is designed to develop automatic
access control system where its combination with RFID reader, relay circuit, power
supply circuit and LCD display circuit show in figure 4.1. This automatic access control
system consists of two main functions which were door access mode as a default mode
and class attendance mode. Admin can select which mode they want to switch either in
door access system or class attendance system depend on the functionality choose by
them.
Figure 4.1: RFID automatic door access control circuit
46
4.2.1 Door Access System Mode
Based on the hardware description above, RFID automatic access control system
will turn to door access system mode as a default mode where this system in initial state
wait for the student to put their ID on the RFID reader. The LCD will display a message
Place your ID tag on the reader while waiting for an input from the RFID Reader show
in figure 4.2. When the student ID tag is place near to RFID reader, the reader can read
student tag ID and further send the student tag ID to the PIC microcontroller. After PIC
microcontroller process the data, either this student ID match on the ID where its being
program inside the PIC16F877A. If the PIC did not found the match ID tag, the LED
will display User not found on the LCD screen show in figure 4.3. After a few second,
the LCD will display welcome note Place your ID tag on the reader again.
Besides that, if the PIC found the match ID tag, the tag ID will display on LCD
in decimal number and it show User Identified shows in figure 4.4. At the same time, it
will send the data to the GUI program which it create using visual basic 2010 to record
the student ID, name, date and the time at database system through USB serial
communication. After a few second, the LCD will display the welcome note Place your
ID tag on the reader again. It will repeat continuously. Lastly, the admin can check the
record of user time in and time out when they access the door at GUI program.
47
Figure 4.2: Place the tag on the reader by user for door access system
Figure 4.3: User ID didnt match with the ID saved
48
Figure 4.4: User ID found and match with ID saved
4.2.2 Class Attendance System Mode
The class attendance system mode is almost the same function with door access
control system mode where this system is work exactly the same based on the door
access control system description show in figure 4.5. Therefore, the admin just need
select the switch 1 to access this mode and it will show same functionality from door
access control system. The admin can check the record the attendance student at the GUI
program where its interact with USB serial communication and the PIC
microcontroller.
49
Figure 4.5: Place the tag on the reader by user for class attendance access system
4.3 Software System
4.3.1 Graphic User Interface
The graphic user interface is created by visual basic 2010 which it consists of the
database system used to store all the student detail, date and time record. There are three
table built in service based SQL database to store the student information. There are
seven frames designed in visual basic which are frame admin, main menu, database,
50
edit, database record, class record and door record. The detail of the each GUI will
further discuss below.
4.3.2 Admin
The login window is built with tighten security which allows the authority person
to access this system show in figure 4.6. The administrator needs to create own user
name and password to log in this system. Therefore, the administrator needs to key in
the correct username and password to access this system and they can exit this system by
click the cancel button to turn off this system.
Figure 4.6: Login in window form
51
4.3.3 Main Menu
The main menu will pop up after the admin success key in the username and
password. The main menu window consist database, door record, class record and the
exit option show in figure 4.7. The admin can search, add or delete the student
information when the admin select the database button. Besides that, the door record
button is used to view the entry record where the students access the door using their
student ID card. Meanwhile, the class record button is used to view the attendance
record when the students attend the class. Lastly, the admin can exit to the login in
window by click the exit button.
Figure 4.7: Main menu window form
52
4.3.4 Database
This database system is created by serviced based database where the admin can
add or delete student information show in figure 4.8. Therefore, admin can view the
student details such likes name, NRIC, gender, race, matric No., faculty, course, college,
room no. and handphone. Besides that, admin can use the search navigator function to
search student information. The search navigator will find the student detail according to
the student name. Furthermore, it will appear the student information if the student name
is matched with the record student store at database system. It helps admin easy to get
any student information by using the search navigator function.
Figure 4.8: Search user profile by admin
53
4.3.5 Edit
This database system can store a lot of student information where admin used to
add, delete and save the student details show in figure 4.9. The admin can easy
recognized the student by view the student picture either the student give the correct
information where they need to store the student into this database system. Therefore,
admin can search the student information by click next or previous button. The admin
used the first record button to find the first student record and the last student record by
click the last record button. However, the admin can easy know how many record being
save into this database system without count the one by one from the database record
system at the top left of the edit window. Lastly, it will return to the database window
when the admin click the exit button.
Figure 4.9: Edit user profile by admin
54
4.3.6 Database Record
The database record window was used to view all the student information is up
to date after admin done the edit on the edit window show in figure 4.10. Therefore,
admin can search all the student detail by click the next and previous button.
Furthermore, admin can easy know how many records was store in the database system
by viewing at the bottom of the database record window.
Figure 4.10: Student record information from database system
55
4.3.7 Door Record
This door record window is used to record the student information into the
database system when the students access the door show in figure 4.11. First, admin
needs to activate the port by click the port open to measure that it can receive the signal
from PIC microcontroller through USB serial communication. It will ask the user to
place their student ID after the port was activated. The student information will record in
the database system if the student ID is match after user scan their student ID on the
reader and all the record will appear at the time log. Hence, admin can easy trace the
student who was access the door according to the student name, date and the time.
However, admin can use the print button to print the time log record of the student
access information. Therefore, admin can deactivate the port after they click the port
close button which it will not communicate through the USB serial communication.
Lastly, admin can view how many record being saved in the time log at the top left of
the door record window.
Figure 4.11: Record the door access of user information to the database system
56
4.3.8 Class Record
This class record window is used to record the student attendance into the
database system when the students attend the class show in figure 4.12. The class record
window is the same function with door record window but with different purpose. First,
admin need to activate the port by click the port open to measure that it can receive the
signal from PIC microcontroller through USB serial communication. It will ask the user
to place their student ID after the port was activated. The student attendance will record
in the database system if the student ID is match after user scan their student ID on the
reader and all the record will appear at the time log. Hence, admin can easy trace the
student who was attended the class according to the student name, date and the time.
However, admin can use the print button to print the time log record of the student
attendance information. Therefore, admin can deactivate the port after they click the port
close button which it will not communicate through the USB serial communication.
Lastly, admin can view how many record being saved in the time log at the top left of
the door record window.
Figure 4.12: Record the class attendance of user information to the database system
57
CHAPTER 5
CONCLUSION
5.1 Conclusion
The RFID automatic access control system prototype has been created and
successfully provided electronic access to the magnetic lock based on user identification,
logged the activity of users and records the student attendance into the database system
during the class. Besides that, GUI has been successfully designed to store or retrieve
data from the database system. The development of this project is plan according to the
grant chart and it was success to get desired result from this project.
In this project, it was divided into to two main parts which are hardware part and
software part. For the hardware part, the RFID automatic access control system consist
LCD display, relay, power supply, the reader and switch circuit where it needs to
interface with PIC 16F877A to produce desired outcome for this project. The reader
being able to read the tag ID to indicate the student for this system where the PIC
16F877A had successful to program using MPLAB v8.3. The magnetic lock system has
success function when the authority person can access the door after the user scan their
58
tag ID. The host computer also successful interfaces with USB serial communication
where it success receive the student information from the tag ID match with the database
system. For the software part, the GUI program is created using the visual basic where
its can store and retrieve data from the database system. Furthermore, the GUI program
success compare the student ID either its match with the database system and display
all the information at time log. Besides that, the GUI program can automatic record the
user detail either it function in door access control system mode or class attendance
system mode.
In conclusion, this RFID automatic access control system was success meet the
objective and requirement of this project. This RFID automatic access control system
can function as a door access control system or class attendance system where it brings
to the benefit to the lecturer, student and the administrator of UTM stuff.
5.2 Future Work and Improvement
The RFID automatic access control system has some restriction in certain part of
this system although it success produce the desired outcome of the project where some
further work can be done to improve this system in the future.
The replacement the RFID wired reader with wireless reader where the RFID
wireless reader is easy to place at any door inside UTM without do the installation cable
connect to the PIC microcontroller. The wireless ready version provides all the
advantage of RFID with built in wireless technology that can be switched ON when
the user are ready for real-time online features that are provided with the wireless on-
59
line system. Besides that, the built in NFC compatibility in the RFID reader use NFC
enabled cell phone as user identification card to access the door or record the student
class attendance.
Finally, this RFID automatic access control system can apply the internet based
RFID database system for collecting and sending information from the computer server
instead using the GUI program created by visual basic 2010. By applying this project in
the real life in this university, the process of getting the entry record and class attendance
record becomes much more effective and efficient where it is easy to manage by the
administrator at the internet based RFID database system.
60
REFERENCE
1. Harvey Lehpamer RFID Design Principles, Artech House, Inc. (2008).
2. Stephen B.Miles, sanjay E.Sarma and John R.Williams RFID Technology and
Applications, Cambridge University Press (2008).
3. Klaus Finkenzeller RFID Handbook, John Wiley & Sons, Ltd (2010).
4. Gyanendra K Verma A Digital Security System with Door Lock System Using
RFID Technology, International Journal of Computer Applications (0975-8887)
Volume 5-No.11, August 2010.
5. Gilbert Thio, Tham Kok Foong, Rajparthiban Kumar, L.K. Moey Design of
RFID Proximity Security Door Lock, School of Engineering, UCSI.
6. Geetha Govindan, Suresh Kumar Balakrishnan, Rejith Lalitha Ratheendran, Saji
Koyippurathu Sivadasan Real time Security Management using RFID, Biometric
and Smart Messages, Medical College Campus Thiruvananthapuram, Kerala,
India.
7. Yossef Oren and Adi Shamir, Remote Password Extraction from RFID Tags,
IEEE Transactions On Computers, VOL. 56, 2007.
8. Zhang, L., 2005. An Improved Approach to Security and Privacy of RFID
application System. Wireless Communications, Networking and Mobile
Computing. International Conference. (2): 1195- 1198.
9. John Iovine, PIC Microcontroller Project Book, McGraw-Hill / TAB
Electronics, 2004.
10. Evangelos Petroutsos, Mastering Visual Basic 2010, Wiley Publishing 2010.
61
APPENDIX A
Program coding of RFID automatic door access control system using MPLAB v8.3
//==============================================================
// Author : Geoffrey Chua
// Project : RFID Automatic Access Control System using
StudentIdentification Card based on RFID Technology
//==============================================================
#include <pic.h>
//configuration
__CONFIG ( 0x3F32 ); //configuration for the microcontroller
// define
#definers RA0
#definee RC5
#defineb_light RC4
#define relay RA1
#definelcd_data PORTB
#defineled RC3
#define data0 RC1
#define data1 RC2
#define sw1 RA4
#define sw2 RA5
#define RX_PIN RC7
#define TX_PIN RC6
//function prototype (every function must have a function prototype)
//==============================================================
void init(void);
void delay(unsigned long data);
void send_config(unsigned char data);
void send_char(unsigned char data);
void send_dec(unsigned long data,unsigned char num_dig);
void e_pulse(void);
void lcd_goto(unsigned char data);
void lcd_clr(void);
void send_string(const char *s);
unsigned char uart_rec(void);
void uart_write(unsigned char data);
62
// main function (main fucntion of the program)
//==============================================================
void main(void)
{
unsigned char i, repeat, a, b, database, c;
unsigned char rec_data;
unsigned char data[26];
unsigned char convert1=0;
unsigned int convert2=0;
unsigned char mode=0;
unsigned char id1[2]={229,0};
unsigned int id2[2]={55051,0};
init(); //initialization
lcd_clr(); //clear the lcd
id1[1]=0; //clear second id1 in the array, first id1 is intialized
id2[1]=0; //clear second id2 in the array, first id2 is intialized
b_light=1; //on the back light
lcd_goto(0);
send_string (" RFID door");
lcd_goto(20);
send_string (" security");
for(repeat=12; repeat>0; repeat--)
{
delay(1000000);
}
while(1)
{
convert1=0;
convert2=0;
lcd_clr();
lcd_goto(0);
send_string ("Place your tag");
lcd_goto(20);
send_string ("on the reader");
while(mode==0)
{
if((data0==0)||(data1==0)) mode=1;
else if(sw1==0) mode=2;
else if(sw2==0) mode=3;
}
while(mode==1)
{
63
if((data0==0)&&(data1==1))
{
data[i]=0;
while((data0==0)&&(data1==1));
}
else if ((data0==1)&&(data1==0))
{
data[i]=1;
while((data0==1)&&(data1==0));
}
i+=1;
while(i<26)
{
while((data0==1)&&(data1==1));
if((data0==0)&&(data1==1))
{
data[i]=0;
while((data0==0)&&(data1==1));
}
else if ((data0==1)&&(data1==0))
{
data[i]=1;
while((data0==1)&&(data1==0));
}
i+=1;
}
mode=0;
i=0;
lcd_clr();
for(i=0;i<8;i++)
{
convert1=(convert1<<1)|data[i+1];
}
}
for(i=0;i<16;i++)
{
convert2=(convert2<<1)|data[i+9];
}
for(b=0;b<2;b++)
{
if((convert1==id1[b])&&(convert2==id2[b])) database=1;
}
lcd_clr();
}
while(mode==3)
64
{
lcd_clr();
lcd_goto(0);
send_string (" Save mode ");
lcd_goto(20);
send_string (" Place your tag");
while(i<26)
{
while((data0==1)&&(data1==1));
if((data0==0)&&(data1==1))
{
data[i]=0;
while((data0==0)&&(data1==1));
}
else if ((data0==1)&&(data1==0))
{
data[i]=1;
while((data0==1)&&(data1==0));
}
i+=1;
}
mode=0;
i=0;
lcd_clr();
for(i=0;i<8;i++)
{
convert1=(convert1<<1)|data[i+1];
}
for(i=0;i<16;i++)
{
convert2=(convert2<<1)|data[i+9];
}
id1[1]=convert1;
id2[1]=convert2;
database=2;
lcd_clr();
}
while(mode==2)
{
lcd_clr();
65
lcd_goto(0);
send_string ("Class Attendance");
lcd_goto(20);
send_string (" Place your tag");
while(i<26)
{
while((data0==1)&&(data1==1));
if((data0==0)&&(data1==1))
{
data[i]=0;
while((data0==0)&&(data1==1));
}
else if ((data0==1)&&(data1==0))
{
data[i]=1;
while((data0==1)&&(data1==0));
}
i+=1;
}
mode=0;
i=0;
lcd_clr();
for(i=0;i<8;i++)
{
convert1=(convert1<<1)|data[i+1];
}
}
for(i=0;i<16;i++)
{
convert2=(convert2<<1)|data[i+9];
}
for(b=0;b<2;b++)
{
if((convert1==id1[b])&&(convert2==id2[b]))
database=3;
}
lcd_clr();
}
switch(database)
{
case 1:
relay=1;
66
led=0;
lcd_goto(0);
send_string("ID no: ");
lcd_goto(7);
send_dec(convert1,3);
lcd_goto(10);
send_dec(convert2,5);
lcd_goto(20);
send_string("User identified. ");
for(repeat=12; repeat>0; repeat--)
{
delay(1000000);
}
lcd_clr();
lcd_goto(0);
send_string("Door lock will");
lcd_goto(20);
send_string("be locked in ");
for(a=5;a>0;a--)
{
lcd_goto(34);
send_dec(a, 1);
for(repeat=10; repeat>0; repeat--)
{
delay(1000000);
}
}
break;
case 2:
relay=1;
led=0;
lcd_clr();
lcd_goto(0);
send_string("ID no: ");
lcd_goto(7);
send_dec(convert1,3);
lcd_goto(10);
send_dec(convert2,5);
lcd_goto(20);
send_string("User ID saved.");
break;
67
case 3:
relay=0;
led=0;
lcd_goto(0);
send_string("ID no: ");
lcd_goto(7);
send_dec(convert1,3);
lcd_goto(10);
send_dec(convert2,5);
lcd_goto(20);
end_string("User identified.");
break;
default:
relay=0;
led=1;
lcd_goto(0);
send_string("ID no: ");
lcd_goto(7);
send_dec(convert1,3);
lcd_goto(10);
send_dec(convert2,5);
lcd_goto(20);
send_string("User not found.");
break;
}
for(repeat=12; repeat>0; repeat--)
{
delay(1000000);
}
i=0;
led=0;
database=0;
relay=0;
convert1=0;
convert2=0;
}
}
// Initailization
void init()
{
//SET PORT A AS DIGITAL
68
ADCON1 = 0X06;
TRISA = 0b00111100;
TRISB = 0b00000000;
TRISC = 0b10000111;
send_config(0b00000010);
send_config(0b00000110);
send_config(0b00001100);
send_config(0b00111000);
//function
b_light=0;
delay(5000);
led=0;
relay=0;
TXSTA = 0b00100100;
RCSTA = 0b10010000;
SPBRG = 129; //set baud rate to 9600 for 20Mhz
}
// LCD functions
void delay(unsigned long data)
{
int i;
for( i = data; i>0; i--);
}
void send_config(unsigned char data)
{
rs=0;
lcd_data=data;
delay(400);
e_pulse();
}
void send_char(unsigned char data)
{
rs=1;
lcd_data = data;
delay(400);
e_pulse();
}
void send_dec(unsigned long data,unsigned char num_dig)
{
69
if(num_dig>=10)
{
data=data%10000000000;
send_char(data/1000000000+0x30);
}
if(num_dig>=9)
{
data=data%1000000000;
send_char(data/100000000+0x30);
}
if(num_dig>=8)
{
data=data%100000000;
send_char(data/10000000+0x30);
}
if(num_dig>=7)
{
data=data%10000000;
send_char(data/1000000+0x30);
}
if(num_dig>=6)
{
data=data%1000000;
send_char(data/100000+0x30);
}
if(num_dig>=5)
{
data=data%100000;
send_char(data/10000+0x30);
}
if(num_dig>=4)
{
data=data%10000;
send_char(data/1000+0x30);
}
if(num_dig>=3)
{
data=data%1000;
send_char(data/100+0x30);
}
if(num_dig>=2)
{
data=data%100;
send_char(data/10+0x30);
}
if(num_dig>=1)
70
{
data=data%10;
send_char(data+0x30);
}
}
//pulse e to confirm the data
void e_pulse(void)
{
e=1;
delay(300);
e=0;
delay(300);
}
//set the location of the lcd cursor
void lcd_goto(unsigned char data)
{
if(data<16)
{
send_config(0x80+data);
}
else
{
data=data-20;
send_config(0xc0+data);
//clear the lcd
void lcd_clr(void)
{
send_config(0x01);
delay(350);
}
//send a string to display in the lcd
void send_string(const char *s)
{
while (s && *s)send_char (*s++);
}
//receive uart value
unsigned char uart_rec(void)
{
unsigned char rec_data;
while(RCIF==0); //wait for data
rec_data = RCREG;
71
return rec_data; //return the data received
}
//write a value to uart
void uart_write(unsigned char data)
{
while(TXIF==0); //only send the new data after
TXREG=data; //the previous data finish sent
}
72
APPENDIX B
Source Code of Visual Basic 2010 for GUI Program
Login form of GUI
Public Class Admin
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
Me.Close()
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
If TextBox1.Text = "UTM" And TextBox2.Text = "Door1" Then
Me.Hide()
MainMenu.Show()
Else
MsgBox("Incorrect username or password")
End If
End Sub
End Class
73
Main Menu form of GUI
Public Class MainMenu
Private Sub Button4_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button4.Click
Me.Hide()
Admin.Show()
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
Me.Hide()
Database.Show()
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
Me.Hide()
DoorRecord.Show()
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
Me.Hide()
ClassRecord.Show()
End Sub
End Sub
End Class
74
Database form of GUI
Public Class Database
Dim Count As Integer = 0
Private Sub Database_Load(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles MyBase.Load
Me.StudentTableAdapter.Fill(Me.StudentDataSet.Student)
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
Me.Hide()
MainMenu.Show()
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
Me.Hide()
Edit.Show()
End Sub
Private Sub Button4_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button4.Click
Me.Hide()
DatabaseRecord.Show()
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
Try
StudentTableAdapter.Name(Me.StudentDataSet.Student, TextBox1.Text)
Catch ex As System.Exception
System.Windows.Forms.MessageBox.Show(ex.Message)
End Try
End Sub
End Class
75
Edit form of GUI
Public Class Edit
Dim Count As Integer = 0
Private Sub StudentBindingNavigatorSaveItem_Click(ByVal sender As System.Object,
ByVal e As System.EventArgs) Handles StudentBindingNavigatorSaveItem.Click
Me.Validate()
Me.StudentBindingSource.EndEdit()
Me.TableAdapterManager.UpdateAll(Me.StudentDataSet)
End Sub
Private Sub Edit_Load(ByVal sender As System.Object, ByVal e As System.EventArgs)
Handles MyBase.Load
Me.StudentTableAdapter.Fill(Me.StudentDataSet.Student)
Timer1.Start()
loadpic()
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
Me.StudentBindingSource.AddNew()
loadpic()
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
Me.Validate()
Me.StudentBindingSource.EndEdit()
Me.TableAdapterManager.UpdateAll(Me.StudentDataSet)
loadpic()
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
Me.StudentBindingSource.RemoveCurrent()
loadpic()
End Sub
Private Sub Button4_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button4.Click
StudentBindingSource.MoveNext()
loadpic()
End Sub
76
Private Sub Button5_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button5.Click
StudentBindingSource.MovePrevious()
loadpic()
End Sub
Private Sub Button6_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button6.Click
StudentBindingSource.MoveFirst()
loadpic()
End Sub
Private Sub Button7_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button7.Click
StudentBindingSource.MoveLast()
loadpic()
End Sub
Private Sub Button8_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button8.Click
StudentBindingSource.RemoveFilter()
StudentBindingSource.CancelEdit()
loadpic()
End Sub
Private Sub Button9_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button9.Click
Me.Hide()
Database.Show()
End Sub
Private Sub Timer1_Tick(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Timer1.Tick
Count = StudentBindingSource.Count
Label1.Text = "There are " & Count & " record found"
Label4.Text = TimeOfDay
Label5.Text = DateString
If Count > 1 And 2 Then
Button2.Visible = True
Button3.Visible = True
End If
If Count <= 1 And 2 Then
Button2.Visible = False
Button3.Visible = False
End If
End Sub
77
Sub loadpic()
Dim Name As String = ""
Dim LastN As String = ""
Dim fileName As String = ""
Name = NameTextBox.Text
fileName = Name & ".jpg"
Try
PictureBox1.Image = Image.FromFile(fileName)
Catch
PictureBox1.Image = Image.FromFile("default.jpg")
End Try
End Sub
End Class
78
Database record form of GUI
Public Class DatabaseRecord
Dim Count As Integer = 0
Private Sub StudentBindingNavigatorSaveItem_Click(ByVal sender As System.Object,
ByVal e As System.EventArgs) Handles StudentBindingNavigatorSaveItem.Click
Me.Validate()
Me.StudentBindingSource.EndEdit()
Me.TableAdapterManager.UpdateAll(Me.StudentDataSet)
End Sub
Private Sub DatabaseRecord_Load(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles MyBase.Load
Me.StudentTableAdapter.Fill(Me.StudentDataSet.Student)
Timer1.Start()
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
StudentBindingSource.MoveNext()
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
StudentBindingSource.MovePrevious()
End Sub
Private Sub Timer1_Tick(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Timer1.Tick
Count = StudentBindingSource.Count
Label1.Text = "There are " & Count & " record found"
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
Me.Hide()
Database.Show()
End Sub
End Class
79
Door record form of GUI
Imports System
Imports System.ComponentModel
Imports System.Runtime.CompilerServices
Public Class DoorRecord
Dim Count As Integer = 0
Dim No As String
Dim saveNow As DateTime = DateTime.Now
Delegate Sub ChangeTextDelegate(ByVal ctrl As Control, ByVal str As String)
Private Sub ChangeText(ByVal ctrl As Control, ByVal str As String)
If ctrl.InvokeRequired Then
ctrl.Invoke(New ChangeTextDelegate(AddressOf ChangeText), New Object()
{ctrl, str})
Return
End If
ctrl.Text = str
End Sub
Private Sub StudentBindingNavigatorSaveItem_Click(ByVal sender As System.Object,
ByVal e As System.EventArgs) Handles StudentBindingNavigatorSaveItem.Click
Me.Validate()
Me.StudentBindingSource.EndEdit()
Me.TableAdapterManager.UpdateAll(Me.StudentDataSet)
End Sub
Private Sub DoorRecord_Load(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles MyBase.Load
Me.DoorRecordTableAdapter.Fill(Me.RecordDataSet.DoorRecord)
Me.StudentTableAdapter.Fill(Me.StudentDataSet.Student)
Timer1.Start()
End Sub
Private Sub Timer1_Tick(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Timer1.Tick
Count = DoorRecordBindingSource.Count()
Label6.Text = "There are " & Count & " record found"
Label4.Text = TimeOfDay
Label5.Text = DateString
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
80
DoorRecordBindingSource.MoveNext()
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
DoorRecordBindingSource.MovePrevious()
End Sub
Private Sub Button4_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button4.Click
Me.Hide()
MainMenu.Show()
End Sub
Private Sub Button5_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button5.Click
Try
RS232.Open()
Catch ex As Exception
System.Windows.Forms.MessageBox.Show(ex.Message)
End Try
MsgBox("Please Scan Your Tag At The Reader")
End Sub
Private Sub Button6_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button6.Click
Try
RS232.Close()
Catch ex As Exception
System.Windows.Forms.MessageBox.Show(ex.Message)
End Try
MsgBox("Port is Disconnect")
End Sub
Private Sub RS232_DataReceived(ByVal sender As Object, ByVal e As
System.IO.Ports.SerialDataReceivedEventArgs) Handles RS232.DataReceived
No = RS232.ReadExisting
loaddata()
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
PrintForm1.PrintAction = Printing.PrintAction.PrintToPreview
PrintForm1.Print(Me, PowerPacks.Printing.PrintForm.PrintOption.FullWindow)
End Sub
End Class
81
Class record form of GUI
Imports System
Imports System.ComponentModel
Imports System.Runtime.CompilerServices
Public Class ClassRecord
Dim Count As Integer = 0
Dim No As Integer
Dim saveNow As DateTime = DateTime.Now
Delegate Sub ChangeTextDelegate(ByVal ctrl As Control, ByVal str As String)
Private Sub ChangeText(ByVal ctrl As Control, ByVal str As String)
If ctrl.InvokeRequired Then
ctrl.Invoke(New ChangeTextDelegate(AddressOf ChangeText), New Object()
{ctrl, str})
Return
End If
ctrl.Text = str
End Sub
Private Sub ClassRecordBindingNavigatorSaveItem_Click(ByVal sender As
System.Object, ByVal e As System.EventArgs) Handles
ClassRecordBindingNavigatorSaveItem.Click
Me.Validate()
Me.Class1BindingSource.EndEdit()
Me.TableAdapterManager1.UpdateAll(Me.Class2DataSet)
End Sub
Private Sub ClassRecord_Load(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles MyBase.Load
Me.Class1TableAdapter.Fill(Me.Class2DataSet.Class1)
Me.ClassRecordTableAdapter.Fill(Me.ClassDataSet.ClassRecord)
Timer1.Start()
End Sub
Private Sub Timer1_Tick(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Timer1.Tick
Count = Class1BindingSource.Count()
Label6.Text = "There are " & Count & " record found"
Label4.Text = TimeOfDay
Label5.Text = DateString
End Sub
Private Sub Button5_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button5.Click
82
Try
RS.Open()
Catch ex As Exception
System.Windows.Forms.MessageBox.Show(ex.Message)
End Try
MsgBox("Please Scan Your Tag At The Reader")
End Sub
Private Sub Button6_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button6.Click
Try
RS.Close()
Catch ex As Exception
System.Windows.Forms.MessageBox.Show(ex.Message)
End Try
MsgBox("Port is Disconnect")
End Sub
Private Sub Button1_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button1.Click
Class1BindingSource.MoveNext()
End Sub
Private Sub Button2_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button2.Click
Class1BindingSource.MovePrevious()
End Sub
Private Sub Button4_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button4.Click
Me.Hide()
MainMenu.Show()
End Sub
Private Sub RS_DataReceived(ByVal sender As Object, ByVal e As
System.IO.Ports.SerialDataReceivedEventArgs) Handles RS.DataReceived
No = RS.ReadExisting
loaddata()
End Sub
Private Sub Button3_Click(ByVal sender As System.Object, ByVal e As
System.EventArgs) Handles Button3.Click
Me.Print.PrintAction = Printing.PrintAction.PrintToPreview
Me.Print.Print(Me, PowerPacks.Printing.PrintForm.PrintOption.FullWindow)
End Sub
End Class
Anda mungkin juga menyukai
- Butcher N Blackbird - Brynne WeaverDokumen303 halamanButcher N Blackbird - Brynne WeaverXt Olla83% (6)
- Figurative Language WorkbookDokumen33 halamanFigurative Language Workbookbuzuleacnadya100% (5)
- CZERNY - Practical Method For BeginnersDokumen56 halamanCZERNY - Practical Method For BeginnersPaul Mcagnin86% (14)
- HATZ 2g30Dokumen284 halamanHATZ 2g30CARLOS SALVADORBelum ada peringkat
- Harvard Style GuideDokumen30 halamanHarvard Style Guidefredy2212Belum ada peringkat
- UAV System Design - IntroductionDokumen47 halamanUAV System Design - IntroductionVijayanandh RBelum ada peringkat
- Carolyn Graham Small Talk More Jazz ChantsDokumen97 halamanCarolyn Graham Small Talk More Jazz Chantsmedimaro100% (4)
- Kenny Dorham InterviewDokumen16 halamanKenny Dorham InterviewNiallCade100% (1)
- Access Control IPAK-2Dokumen63 halamanAccess Control IPAK-2Ajas NazarudeenBelum ada peringkat
- Instruction Manuals For Installation and Maintainance PDFDokumen36 halamanInstruction Manuals For Installation and Maintainance PDFlhphong021191Belum ada peringkat
- Flowcode5Booklet 2 PDFDokumen14 halamanFlowcode5Booklet 2 PDFgrovlhus0% (1)
- Proposal Final Year Project 2Dokumen15 halamanProposal Final Year Project 2Amirul Azha SharuddinBelum ada peringkat
- Sil 00 028 040Dokumen164 halamanSil 00 028 040Angel PalaciosBelum ada peringkat
- Thesis Mcrl01e Menoza A Mendoza J Perante Mallari 3Dokumen57 halamanThesis Mcrl01e Menoza A Mendoza J Perante Mallari 3Edgar PeBelum ada peringkat
- CCTV Camera Systems and Project EngineeringDokumen8 halamanCCTV Camera Systems and Project Engineeringnadeem_skBelum ada peringkat
- SOP For Microwave Swap v0.7Dokumen83 halamanSOP For Microwave Swap v0.7Ronie MarxistBelum ada peringkat
- 40-Pin IDE Flash Module Installation GuideDokumen1 halaman40-Pin IDE Flash Module Installation GuideSergioMesquita01Belum ada peringkat
- MasteriTower1 OccupantsDokumen126 halamanMasteriTower1 OccupantsNguyen LuanBelum ada peringkat
- ACTUATION SYSTEMS Unit 2Dokumen40 halamanACTUATION SYSTEMS Unit 2RamanathanDurai100% (1)
- Mosley - MP 33 N WARCDokumen19 halamanMosley - MP 33 N WARCpepepe78100% (1)
- Rfid Based Car Parking Security System Using Microcontroller Ic89c52 IJERTV4IS031045Dokumen5 halamanRfid Based Car Parking Security System Using Microcontroller Ic89c52 IJERTV4IS031045Tummuri ShanmukBelum ada peringkat
- Proposal For Final Year ProjectDokumen7 halamanProposal For Final Year ProjectAmirul Azha Sharuddin100% (1)
- QN-H618 Remote Master User ManualDokumen19 halamanQN-H618 Remote Master User Manualdra6an100% (2)
- Integrated Burglar Alarm SystemDokumen50 halamanIntegrated Burglar Alarm Systemmanvi SinghBelum ada peringkat
- PPU-3 - Designers Reference HandbookDokumen96 halamanPPU-3 - Designers Reference HandbookCatalin PelinBelum ada peringkat
- Tamrock Especificaciones PDFDokumen3 halamanTamrock Especificaciones PDFIvan Sepulveda ReyesBelum ada peringkat
- Castillo Reaction Paper PLC and SCADADokumen2 halamanCastillo Reaction Paper PLC and SCADALaurence CastilloBelum ada peringkat
- Power VisionDokumen12 halamanPower Visiongustavofx21Belum ada peringkat
- 08 - S7-200 Getting Started Sample ProgramDokumen15 halaman08 - S7-200 Getting Started Sample ProgramguerrezBelum ada peringkat
- Material List For PLC ProjectsDokumen1 halamanMaterial List For PLC ProjectsEngr Muhib KhÅñBelum ada peringkat
- Deposit LockerDokumen6 halamanDeposit LockerbondocdexterBelum ada peringkat
- FlexSimHC 5.0 UserManual PDFDokumen413 halamanFlexSimHC 5.0 UserManual PDFJulio Mojica HerazoBelum ada peringkat
- Ihp Unit 6: Pneumatic CircuitsDokumen35 halamanIhp Unit 6: Pneumatic CircuitsAkash MarkhaleBelum ada peringkat
- ATS Control Panel-EnGDokumen4 halamanATS Control Panel-EnGRobertoSoares100% (1)
- Basic Pneumatics: Module 5: Double Acting CylinderDokumen14 halamanBasic Pneumatics: Module 5: Double Acting Cylinderاحمد السيدBelum ada peringkat
- Digital Bike Operating System Sans Key by I. Udaya BhaskarDokumen11 halamanDigital Bike Operating System Sans Key by I. Udaya Bhaskariudaya_bhaskarBelum ada peringkat
- Phy 308 Electronics IDokumen310 halamanPhy 308 Electronics ISuresh LBelum ada peringkat
- 01 Autodesk Inventor User InterfaceDokumen26 halaman01 Autodesk Inventor User Interfacegian_rosas0% (1)
- Arduino Based Greenhouse: Block Diagram of Green House Monitoring and Controlling SystemDokumen3 halamanArduino Based Greenhouse: Block Diagram of Green House Monitoring and Controlling SystemSanjana SinghBelum ada peringkat
- 84460006air Hydraulic ActuatorsDokumen20 halaman84460006air Hydraulic ActuatorsteruretefuBelum ada peringkat
- PLC Based Sequential Batch Process Control SystemDokumen11 halamanPLC Based Sequential Batch Process Control SystemAmol PawarBelum ada peringkat
- Electro Pneumatic Technology 2Dokumen29 halamanElectro Pneumatic Technology 2Victor Al100% (1)
- QSG-RD77MS Simple Motion Module Programming Example With Module LabelDokumen35 halamanQSG-RD77MS Simple Motion Module Programming Example With Module LabelGrucito Konfy100% (1)
- Web-Based Student Attendance System Using Rfid Technology: Krest Technologies, Beside Image Hospital, AmeerpetDokumen3 halamanWeb-Based Student Attendance System Using Rfid Technology: Krest Technologies, Beside Image Hospital, AmeerpetFrancisca SarzaBelum ada peringkat
- AbhiDokumen4 halamanAbhiEshan SBelum ada peringkat
- Mahatma Gandhi Institute of Technology: CertificateDokumen66 halamanMahatma Gandhi Institute of Technology: CertificateYashwanth LokamBelum ada peringkat
- AJSN Access Control System To Tourism Resort RFID IoT Suputra Cs 2023Dokumen9 halamanAJSN Access Control System To Tourism Resort RFID IoT Suputra Cs 2023SuputraBelum ada peringkat
- RFID and Wi-Fi Based Home Automation: Ojashwi Paudel (19BCE2552) Samyogita Bhandari (19BCE2537) Aravindaan S (19BCE0144)Dokumen27 halamanRFID and Wi-Fi Based Home Automation: Ojashwi Paudel (19BCE2552) Samyogita Bhandari (19BCE2537) Aravindaan S (19BCE0144)aravindaan saravananBelum ada peringkat
- RFID Based Attendance SystemDokumen5 halamanRFID Based Attendance SystemNyashadzashe ChikarakaraBelum ada peringkat
- Abstract Report of Door Lock - Team 04Dokumen4 halamanAbstract Report of Door Lock - Team 04Jayan SamaBelum ada peringkat
- Access Control SystemDokumen19 halamanAccess Control SystemKavyashree M.K ECBelum ada peringkat
- Iot Mini Projject ReportDokumen16 halamanIot Mini Projject Reportrudra.pvt.afBelum ada peringkat
- Research Review of Related LiteratureDokumen9 halamanResearch Review of Related LiteratureBless beljBelum ada peringkat
- PreviewDokumen13 halamanPreviewBharath kanaparthiBelum ada peringkat
- RFID Based Security and Access Control System Using ARDUINODokumen3 halamanRFID Based Security and Access Control System Using ARDUINOIJMTST-Online Journal100% (1)
- RFID Based Smart Lock Implementation: Computer Engineering Department, College of Engineering, Al-Iraqia University, IraqDokumen5 halamanRFID Based Smart Lock Implementation: Computer Engineering Department, College of Engineering, Al-Iraqia University, IraqAliBelum ada peringkat
- RFID Based Attendance System Project Circuit and WorkingDokumen5 halamanRFID Based Attendance System Project Circuit and WorkinglkjhBelum ada peringkat
- RFID Based Attendance Management System: International Journal of Electrical and Computer Engineering (IJECE)Dokumen7 halamanRFID Based Attendance Management System: International Journal of Electrical and Computer Engineering (IJECE)Glenn MaramisBelum ada peringkat
- Rfid Systems SecurityDokumen120 halamanRfid Systems SecuritytybriousBelum ada peringkat
- ReferatDokumen4 halamanReferatGeorgeBelum ada peringkat
- RFID-Based Digital Door Locking SystemDokumen6 halamanRFID-Based Digital Door Locking Systemreal.lucifer.007Belum ada peringkat
- Security System Using RFID: A Project ReportDokumen30 halamanSecurity System Using RFID: A Project Reportdnadar881Belum ada peringkat
- VarshuthDokumen31 halamanVarshuthGeetuBelum ada peringkat
- Tech SeminarDokumen27 halamanTech SeminarAISHWARYA PANDITBelum ada peringkat
- On Rfid Based Attendance System: Internet of Things Project ReportDokumen36 halamanOn Rfid Based Attendance System: Internet of Things Project ReportNaveen KumarBelum ada peringkat
- Paper3 PDFDokumen7 halamanPaper3 PDFShravani GNBelum ada peringkat
- Sustainable and No Contact Attendance SystemDokumen6 halamanSustainable and No Contact Attendance SystemIJRASETPublicationsBelum ada peringkat
- Rfid Based Security Access Control System: NAME:-VISHAL MANIKPURI (0213CS201104) NAME: - VIKAS GUPTA (0213CS201103)Dokumen17 halamanRfid Based Security Access Control System: NAME:-VISHAL MANIKPURI (0213CS201104) NAME: - VIKAS GUPTA (0213CS201103)Vishal DPBelum ada peringkat
- 5.chapter 1Dokumen4 halaman5.chapter 1thethtet87Belum ada peringkat
- Laprak Kendali Servo Menggunakan RfidDokumen23 halamanLaprak Kendali Servo Menggunakan RfidGilang Pratama Putra SiswantoBelum ada peringkat
- An Enhanced RFID-Based Authentication Protocol Using PUF For Vehicular Cloud ComputingDokumen18 halamanAn Enhanced RFID-Based Authentication Protocol Using PUF For Vehicular Cloud Computing0dayBelum ada peringkat
- L D A E W C C: Inear Ifferential Lgebraic Quations ITH Onstant OefficientsDokumen8 halamanL D A E W C C: Inear Ifferential Lgebraic Quations ITH Onstant OefficientsthgnguyenBelum ada peringkat
- Balanced Device Characterization PDFDokumen46 halamanBalanced Device Characterization PDFthgnguyenBelum ada peringkat
- Exporting C++ From DllsDokumen6 halamanExporting C++ From DllsthgnguyenBelum ada peringkat
- Allegro Platform System Requirements: Product Version 17.2-2016 April 2016Dokumen19 halamanAllegro Platform System Requirements: Product Version 17.2-2016 April 2016thgnguyenBelum ada peringkat
- CMT Python Setup GuideDokumen2 halamanCMT Python Setup GuidethgnguyenBelum ada peringkat
- Exact Amplitude Distributions of Sums of Stochastic SinusoidalsDokumen14 halamanExact Amplitude Distributions of Sums of Stochastic SinusoidalsthgnguyenBelum ada peringkat
- Cadence Sigrity 2017 Release Installation Guide: Product Version Sigrity 2017 December 2016Dokumen42 halamanCadence Sigrity 2017 Release Installation Guide: Product Version Sigrity 2017 December 2016thgnguyenBelum ada peringkat
- Cadence Sigrity 2017 Release Installation Guide: Product Version Sigrity 2017 December 2016Dokumen42 halamanCadence Sigrity 2017 Release Installation Guide: Product Version Sigrity 2017 December 2016thgnguyenBelum ada peringkat
- S - 1 - 1 p1 - p2..S (1,1) S - 1 - 2 p1 - p2..S (1,2) S - 1 - 3 p1 - p3..S (1,2)Dokumen1 halamanS - 1 - 1 p1 - p2..S (1,1) S - 1 - 2 p1 - p2..S (1,2) S - 1 - 3 p1 - p3..S (1,2)thgnguyenBelum ada peringkat
- PortsDokumen6 halamanPortsuam22Belum ada peringkat
- Excitation of Waveguides PozarDokumen11 halamanExcitation of Waveguides PozarthgnguyenBelum ada peringkat
- Jitter and Phase NoiseDokumen62 halamanJitter and Phase NoisethgnguyenBelum ada peringkat
- Microwave Amplifiers: Eee 194 RFDokumen11 halamanMicrowave Amplifiers: Eee 194 RFShubhra SinhaBelum ada peringkat
- Hey DudeDokumen3 halamanHey DudethgnguyenBelum ada peringkat
- The Quasi-Kronecker Form For Matrix PencilsDokumen33 halamanThe Quasi-Kronecker Form For Matrix PencilsthgnguyenBelum ada peringkat
- Cas CodeDokumen4 halamanCas CodethgnguyenBelum ada peringkat
- Making A Semi Log Graph in ExcelDokumen3 halamanMaking A Semi Log Graph in ExcelthgnguyenBelum ada peringkat
- Cambridge Books OnlineDokumen3 halamanCambridge Books OnlinethgnguyenBelum ada peringkat
- Plotting Basic Lab Data With ExcelDokumen2 halamanPlotting Basic Lab Data With ExcelthgnguyenBelum ada peringkat
- (Discussion) Taylor Expansion of Matrix InverseDokumen12 halaman(Discussion) Taylor Expansion of Matrix InversethgnguyenBelum ada peringkat
- XModDokumen8 halamanXModthgnguyenBelum ada peringkat
- Ana WhyDokumen6 halamanAna WhythgnguyenBelum ada peringkat
- A Descriptor System Approach To H Inf Control of Linear Time-Delay SystemsDokumen18 halamanA Descriptor System Approach To H Inf Control of Linear Time-Delay SystemsthgnguyenBelum ada peringkat
- Electromagnetic Theory: A. B. LahanasDokumen16 halamanElectromagnetic Theory: A. B. LahanasRohit BhardwajBelum ada peringkat
- Time Domain Analog Circuit SimulationDokumen16 halamanTime Domain Analog Circuit SimulationthgnguyenBelum ada peringkat
- A Broad-Band TL Model For A Rectangular Microstrip AntennaDokumen10 halamanA Broad-Band TL Model For A Rectangular Microstrip AntennathgnguyenBelum ada peringkat
- Measurements and Nonlinear ModelingDokumen9 halamanMeasurements and Nonlinear ModelingthgnguyenBelum ada peringkat
- United States Radio Frequency Allocation ChartDokumen1 halamanUnited States Radio Frequency Allocation ChartJason Bentley100% (2)
- Generalized State Space Realizations of Non-Proper Rational Transfer FunctionsDokumen7 halamanGeneralized State Space Realizations of Non-Proper Rational Transfer FunctionsthgnguyenBelum ada peringkat
- Tên Địa chỉ City, State Zip Trinh Ly Huan Le & Thao Nguyen RuppertDokumen4 halamanTên Địa chỉ City, State Zip Trinh Ly Huan Le & Thao Nguyen RuppertthgnguyenBelum ada peringkat
- Biff-E-Breeze Spring 2010Dokumen16 halamanBiff-E-Breeze Spring 2010jliouBelum ada peringkat
- Fpga 4 FunsDokumen4 halamanFpga 4 FunsFilipe BrendlerBelum ada peringkat
- Chromatic II VsDokumen14 halamanChromatic II VsJermaine Ray100% (1)
- Californication PDFDokumen2 halamanCalifornication PDFlorenzoBelum ada peringkat
- Nokia RM-504 5530XpressMusic Service Manual L1L2v7.0Dokumen0 halamanNokia RM-504 5530XpressMusic Service Manual L1L2v7.0Jorge Martin Doroteo RojasBelum ada peringkat
- Gypsy Music - Eastern EuropeDokumen19 halamanGypsy Music - Eastern EuropeitseldaivyBelum ada peringkat
- Chapter Five - Rhythm: Short TOC Long TOC Help IndexesDokumen31 halamanChapter Five - Rhythm: Short TOC Long TOC Help IndexesTTCYoga BatchBelum ada peringkat
- Creative Arts in IndiaDokumen67 halamanCreative Arts in IndiaMashumi SankheBelum ada peringkat
- Reyes Vs Tang Soat IngDokumen11 halamanReyes Vs Tang Soat IngArkhaye SalvatoreBelum ada peringkat
- Hook Up Diagram S3Dokumen1 halamanHook Up Diagram S3jonathan gongora riveraBelum ada peringkat
- SOAL UAS Bhs Inggris XDokumen10 halamanSOAL UAS Bhs Inggris XbBelum ada peringkat
- Spectators and Spectator Comfort in Roman Entertainment Buildings: A Study in Functional Design Author(s) : Peter RoseDokumen33 halamanSpectators and Spectator Comfort in Roman Entertainment Buildings: A Study in Functional Design Author(s) : Peter RoseBuga Screams KranželićBelum ada peringkat
- La Nave Del Olvido: Version Julio IglesiasDokumen1 halamanLa Nave Del Olvido: Version Julio IglesiasMagdalenaBelum ada peringkat
- Doj Opinion No 40Dokumen2 halamanDoj Opinion No 40Alexandra Zoila Descutido UlandayBelum ada peringkat
- Wireless Tone Generator Troubleshooting: Technical SupportDokumen1 halamanWireless Tone Generator Troubleshooting: Technical SupportsolomonBelum ada peringkat
- LG 29fu6rl (-l5) Chassis Cw62dDokumen22 halamanLG 29fu6rl (-l5) Chassis Cw62dHENDI SUHAENDIBelum ada peringkat
- CinderellaDokumen2 halamanCinderellaBaymaxBelum ada peringkat
- DuckTales - PERCUSSIONDokumen12 halamanDuckTales - PERCUSSIONsportadenoBelum ada peringkat
- The Chart Below Shows The Male and Female Internet Users Aged 15-24 in Canada in 2000Dokumen2 halamanThe Chart Below Shows The Male and Female Internet Users Aged 15-24 in Canada in 2000minakshiminsBelum ada peringkat