Types of Cyber Crimes Cyber Law India Nov11
Diunggah oleh
Shankar Jii UppariHak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Types of Cyber Crimes Cyber Law India Nov11
Diunggah oleh
Shankar Jii UppariHak Cipta:
Format Tersedia
Security Corner
Adv. Prashant Mali, B.Sc. (Physics), M.Sc.( Comp. Science), LLB
Cyber Law & Cyber Security Expert. Email: prashant.mali@cyberlawconsulting.com
IT Act 2000
Types of Cyber Crimes & Cyber Law in India
(Part-I)
What is a cyber crime?
Cyber crime is a generic term that
refers to all criminal activities done using
the medium of computers, the Internet,
cyber space and the worldwide web.
There isnt really a fixed definition for
cyber crime. The Indian Law has not given
any definition to the term cyber crime. In
fact, the Indian Penal Code does not use
the term cyber crime at any point even
after its amendment by the Information
Technology (amendment) Act 2008, the
Indian Cyber law. But Cyber Security
is defined under Section (2) (b) means
protecting
information,
equipment,
devices computer, computer resource,
communication device and information
stored therein from unauthorized access,
use, disclosure, disruption, modification or
destruction.
What is Cyber Law?
Cyber law is a term used to
describe the legal issues related to use of
communications technology, particularly
cyberspace, i.e. the Internet. It is less of a
distinct field of law in the way that property
or contract are, as it is an intersection of
many legal fields, including intellectual
property, privacy, freedom of expression,
and jurisdiction. In essence, cyber law
is an attempt to apply laws designed for
the physical world, to human activity on
the Internet. In India, The IT Act, 2000 as
amended by The IT (Amendment) Act,
2008 is known as the Cyber law. It has a
separate chapter XI entitled Offences
in which various cyber crimes have been
declared as penal offences punishable
with imprisonment and fine.
1. Hacking
What is Hacking?
Hacking is not defined in The
amended IT Act, 2000.
According to wiktionary, Hacking
means unauthorized attempts to
bypass the security mechanisms of an
information system or network. Also, in
simple words Hacking is the unauthorized
access to a computer system, programs,
data and network resources. (The term
hacker originally meant a very gifted
programmer. In recent years though, with
easier access to multiple systems, it now
has negative implications.)
Law
&
Punishment:
Under
Information Technology (Amendment)
Act, 2008, Section 43(a) read with
section 66 is applicable and Section 379
& 406 of Indian Penal Code, 1860 also
are applicable. If crime is proved under
IT Act, accused shall be punished for
imprisonment, which may extend to three
years or with fine, which may extend to
five lakh rupees or both. Hacking offence
is cognizable, bailable, compoundable
with permission of the court before which
the prosecution of such offence is pending
and triable by any magistrate.
2. Data Theft
What is Data Theft?
According to Wikipedia, Data Theft is
a growing problem, primarily perpetrated
by office workers with access to technology
such as desktop computers and handheld devices, capable of storing digital
information such as flash drives, iPods
and even digital cameras. The damage
caused by data theft can be considerable
with todays ability to transmit very large
files via e-mail, web pages, USB devices,
DVDstorage and other hand-held devices.
According to Information Technology
(Amendment) Act, 2008, crime of data
theft under Section 43 (b) is stated as If any person without permission of the
owner or any other person, who is in
charge of a computer, computer system
of computer network - downloads, copies
or extracts any data, computer data base
or information from such computer,
computer system or computer network
including information or data held or
stored in any removable storage medium,
then it is data theft.
Law
&
Punishment:
Under
Information Technology (Amendment)
Act, 2008, Section 43(b) read with
Section 66 is applicable and under Section
379, 405 & 420 of Indian Penal Code,
1860 also applicable. Data Theft offence
is cognizable, bailable, compoundable
with permission of the court before which
the prosecution of such offence is pending
and triable by any magistrate.
3. Spreading Virus or Worms
What is spreading of Virus or
Worms?
In most cases, viruses can do any
amount of damage, the creator intends
them to do. They can send your data to a
third party and then delete your data from
your computer. They can also ruin/mess
up your system and render it unusable
without a re-installation of the operating
system. Most have not done this much
damage in the past, but could easily do
this in the future. Usually the virus will
install files on your system and then will
change your system so that virus program
is run every time you start your system.
It will then attempt to replicate itself by
sending itself to other potential victims.
Law
&
Punishment:
Under
Information Technology (Amendment)
Act, 2008, Section 43(c) & 43(e) read
with Section 66 is applicable and under
Section 268 of Indian Penal Code, 1860
also applicable. Spreading of Virus offence
is cognizable, bailable, compoundable
with permission of the court before which
the prosecution of such offence is pending
and triable by any magistrate.
4. Identity Theft
What is Identity Theft?
According to wikipedia Identity theft
is a form of fraud or cheating of another
persons identity in which someone
pretends to be someone else by assuming
that persons identity, typically in order
to access resources or obtain credit and
other benefits in that persons name.
Information Technology (Amendment)
Act, 2008, crime of identity theft under
Section 66-C, whoever, fraudulently or
dishonestly make use of the electronic
signature, password or any other unique
identification feature of any other person
known as identity theft.
Identity theft is a term used to refer
to fraud that involves stealing money or
getting other benefits by pretending to be
someone else. The term is relatively new
Contd. on pg.34
CSI Communications | November 2011 | 33
Happenings@ICT
H R Mohan
Chairman, Div. IV CSI, AVP (Systems), The Hindu, Chnenai.
Email: hrmohan.csi@gmail.com
ICT news briefs in October 2011
The following are the India specific ICT news and headlines in
Oct 2011. They have been compiled from various news & Internet
sources including the financial dailies The Hindu Business Line,
Economic Times.
Voices & Views
The tablet market to touch 2.75 lakh units in year 2011,
according to CyberMedia Research,
The continued political unrest in AP is affecting the business
sentiments of the IT companies and its customers based in
the region, Nasscom.
Nasscom estimates 16-18% annual growth in the IT sector
and terms the industry outlook positive.
Nasscom forecasts independent testing services in India to
grow to $13-15 b by 2020 at a CAGR of over 20%.
The sales of PCs - desktops, notebooks and Netbooks to
cross 12.6 m units during 2011-12 -- MAIT.
Smartphone users spend more time on content than voice,
SMS. -- Nielsen Informate Mobile.
Cybercriminals exploit Steve Jobs death by offering free
iPads & MacBook Pros in memory of Jobs.
Worms is the single biggest problem in the country
affecting 38.3% of all infected computers - over three times
the worldwide average. -- Microsoft.
India has climbed 10 positions in the global ranking of IT
competitiveness and stands at 34 while China is ranked at
39.
eBay census: Delhi is No.1 e-commerce hub closely followed
by Mumbai, Bangalore, Jaipur and Chennai.
Indian corporate data highly susceptible to Duqu-like
malware Symantec.
Telecom, Govt, Policy, Compliance
The EU has raised concerns against the proposed telecom
manufacturing policy on grounds that it may flout WTO
norms.
BSNL offers to surrender broadband spectrum; seeks refund
of Rs. 9000 cr. paid as fee
The draft national policy on electronics proposes creation
of a Electronic Development Fund (of size Rs. 5000 cr)
to promote innovation and R&D (aiming for 2,500 PhDs
annually by 2020.) in the electronics systems design and
manufacturing space.
The proposed draft IT policy aims big it wants to increase
revenue from the IT and BPO industry to $300 b by 2020
from $88 b now, and raise the export turnover to $200 b,
from the current $59 b. It targets the creation of 10 m skilled
tech hands by 2020 compared to 2.5 m employed currently.
Draft telecom policy allows free roaming, unrestricted Net
telephony. Telcos to lose $500 m.
The worlds cheapest tablet PC named Aakash, priced at just
Rs 2,276, was launched by the Indian Govt.
The Electronic Service Delivery Bill which mandates all
govt. orgns to deliver public services through electronic
mode will be sent for Cabinet approval soon.
2G: Charges framed against Raja, Kanimozhi and 15 others.
Cabinet approves scheme for National Optical Fibre Network
n
Contd. from pg.33
and is actually a misnomer, since it is not
inherently possible to steal an identity,
only to use it. The person whose identity
is used can suffer various consequences
when they are held responsible for the
perpetrators actions. At one time the only
way for someone to steal somebody elses
identity was by killing that person and
taking his place. It was typically a violent
crime. However, since then, the crime
has evolved and todays white collared
criminals are a lot less brutal. But the
ramifications of an identity theft are still
scary.
Law
&
Punishment:
Under
Information Technology (Amendment)
Act, 2008, Section 66-C and Section 419
of Indian Penal Code, 1860 also applicable.
Identity Theft offence is cognizable,
bailable, compoundable with permission
of the court before which the prosecution
of such offence is pending and triable by
any magistrate.
5. E-Mail Spoofing
What is Email Spoofing?
According to wikipedia, e-mail
spoofing is e-mail activity in which the
sender addresses and other parts of
the e-mail header are altered to appear
as though the e-mail originated from
a different source. E-mail spoofing is
sending an e-mail to another person in
such a way that it appears that the e-mail
was sent by someone else. A spoof email
is one that appears to originate from one
source but actually has been sent from
another source. Spoofing is the act of
electronically disguising one computer
as another for gaining as the password
system. It is becoming so common that
you can no longer take for granted that the
e-mail you are receiving is truly from the
person identified as the sender.
Email spoofing is a technique used
by hackers to fraudulently send email
messages in which the sender address and
CSI Communications | November 2011 | 34
other parts of the email header are altered
to appear as though the email originated
from a source other than its actual source.
Hackers use this method to disguise the
actual email address from which phishing
and spam messages are sent and often use
email spoofing in conjunction with Web
page spoofing to trick users into providing
personal and confidential information.
Law
&
Punishment:
Under
Information Technology (Amendment)
Act, 2008, Section 66-D and Section417,
419 & 465of Indian Penal Code, 1860
also applicable. Email spoofing offence is
cognizable, bailable, compoundable with
permission of the court before which the
prosecution of such offence is pending
and triable by any magistrate.
Bibliography:
Authors upcoming book on Cyber Law
and Cyber Crimes
To be continued in Part II, which will be
published in the next CSIC issue.
www.csi-india.org
Anda mungkin juga menyukai
- IT Project LLMDokumen23 halamanIT Project LLMsoumilBelum ada peringkat
- The International Telecommunications Regime: Domestic Preferences And Regime ChangeDari EverandThe International Telecommunications Regime: Domestic Preferences And Regime ChangeBelum ada peringkat
- Study On Cyber Law's of IndiaDokumen7 halamanStudy On Cyber Law's of IndiaIJRASETPublicationsBelum ada peringkat
- America, Aristotle, and the Politics of a Middle ClassDari EverandAmerica, Aristotle, and the Politics of a Middle ClassBelum ada peringkat
- Unit 4 and Unit 5 Class Notes - Cyber Security - 1518766008 PDFDokumen12 halamanUnit 4 and Unit 5 Class Notes - Cyber Security - 1518766008 PDFkushwah_7701455660% (2)
- Cyber Law Updated-V1Dokumen1 halamanCyber Law Updated-V1Akheela KhanumBelum ada peringkat
- Dissertation Synopsis ReportDokumen12 halamanDissertation Synopsis Reportsanjana raoBelum ada peringkat
- Data Protection Laws in IndiaDokumen6 halamanData Protection Laws in IndiaApoorv NagpalBelum ada peringkat
- 18A037 - Cybercrime and InvestigationDokumen9 halaman18A037 - Cybercrime and InvestigationFavi SinglaBelum ada peringkat
- A Special Project On: "Cyber Tort"Dokumen24 halamanA Special Project On: "Cyber Tort"preetBelum ada peringkat
- Full TextDokumen47 halamanFull TextDhandapani ParasuramanBelum ada peringkat
- MASUKA Draft BillDokumen11 halamanMASUKA Draft BillThe Quint100% (1)
- Internet As A Human RightDokumen24 halamanInternet As A Human RightthepavlomalBelum ada peringkat
- CASE IT ActDokumen5 halamanCASE IT Actvivek singhBelum ada peringkat
- Cyber Crimes An Overview PDFDokumen11 halamanCyber Crimes An Overview PDFMAHANTESH GBelum ada peringkat
- Division-B PRN - 16010323154 BA LLB (2016-2021)Dokumen9 halamanDivision-B PRN - 16010323154 BA LLB (2016-2021)Shreya Ghosh DastidarBelum ada peringkat
- Mats Front LawDokumen7 halamanMats Front LawSHOAIB MEMONBelum ada peringkat
- Crimes in CyberspaceDokumen28 halamanCrimes in CyberspacegautamBelum ada peringkat
- Cyber Crime Scenario in India and Judicial ResponseDokumen5 halamanCyber Crime Scenario in India and Judicial ResponseEditor IJTSRDBelum ada peringkat
- Right To Be ForgottenDokumen5 halamanRight To Be ForgottenShubhra BaghelBelum ada peringkat
- Data Protection Law in IndiaDokumen3 halamanData Protection Law in IndiaNaveen SihareBelum ada peringkat
- Cyber LawDokumen15 halamanCyber LawPravesh AgarwalBelum ada peringkat
- Information Technology 1Dokumen16 halamanInformation Technology 1Shailesh KumarBelum ada peringkat
- Cyber Crimes in The IPC and IT Act - An Uneasy Co-ExistenceDokumen10 halamanCyber Crimes in The IPC and IT Act - An Uneasy Co-ExistenceManoj R.KBelum ada peringkat
- Property Law Twinkle RajpalDokumen18 halamanProperty Law Twinkle RajpalTwinkle RajpalBelum ada peringkat
- Paper On Cyber SecurityDokumen13 halamanPaper On Cyber SecurityAmudha MonyBelum ada peringkat
- Presentation On Hacking and CrackingDokumen15 halamanPresentation On Hacking and CrackingsrinivasBelum ada peringkat
- (IT PPT) ISP LiabilityDokumen26 halaman(IT PPT) ISP LiabilityNaveen SihareBelum ada peringkat
- Copyright Issues in CyberspaceDokumen43 halamanCopyright Issues in CyberspaceAvishek Pathak100% (1)
- Women and Cyber CrimesDokumen9 halamanWomen and Cyber Crimessowmya kBelum ada peringkat
- DissertationDokumen41 halamanDissertationGAUTAM MATORIABelum ada peringkat
- An International Perspective On Cyber CrimeDokumen15 halamanAn International Perspective On Cyber CrimeTariqul IslamBelum ada peringkat
- Cyber LawDokumen11 halamanCyber LawTAJ AHAMED100% (1)
- Information TechnologyDokumen14 halamanInformation TechnologyAditya SaxenaBelum ada peringkat
- Mats Front LawDokumen8 halamanMats Front Lawjassi7nishadBelum ada peringkat
- To Be PrintedDokumen85 halamanTo Be PrintedDevanand PandeyBelum ada peringkat
- Socio-Economic Offences (WCC)Dokumen176 halamanSocio-Economic Offences (WCC)utsavsinghofficeBelum ada peringkat
- IT Amendment Act, 2008 - An Act To Amend The IT Act 2000Dokumen3 halamanIT Amendment Act, 2008 - An Act To Amend The IT Act 2000sbhatlaBelum ada peringkat
- Cyber Law in BangladeshDokumen12 halamanCyber Law in BangladeshShaekh Maruf Skder 1912892630100% (1)
- Jurisdictional Issues in Internet DisputesDokumen35 halamanJurisdictional Issues in Internet DisputesTalwant SinghBelum ada peringkat
- Data Protection IndiaDokumen8 halamanData Protection IndiaEugenia MarweinBelum ada peringkat
- Data Protection in India: Justice B. N. Srikrishna Report: Law of Privacy ID No. 214126Dokumen7 halamanData Protection in India: Justice B. N. Srikrishna Report: Law of Privacy ID No. 214126Shefalika NarainBelum ada peringkat
- Intellectual Property Issues in CyberspaceDokumen15 halamanIntellectual Property Issues in Cyberspaceshubham kumarBelum ada peringkat
- IT ACT 2000 Scope and ImpactsDokumen9 halamanIT ACT 2000 Scope and Impactspintu ramBelum ada peringkat
- Cyber Law Project Lokesh NigamDokumen21 halamanCyber Law Project Lokesh Nigamlokesh4nigamBelum ada peringkat
- Aryan Babele - Cyber Crimes Against Women and ChildrenDokumen9 halamanAryan Babele - Cyber Crimes Against Women and Childrenaryan babeleBelum ada peringkat
- The Motor Vehicle Act, 1988Dokumen14 halamanThe Motor Vehicle Act, 1988Hiba AmmuBelum ada peringkat
- The Protection of Women From Domestic Violence ActDokumen23 halamanThe Protection of Women From Domestic Violence ActPaanchajanya Narasimha NeelamrajuBelum ada peringkat
- Seminar Paper OF: Cyber Terrorism in India: An OverveiwDokumen28 halamanSeminar Paper OF: Cyber Terrorism in India: An Overveiwaruba ansariBelum ada peringkat
- Child Pornograhy Laws in IndiaDokumen1 halamanChild Pornograhy Laws in Indiashakti ranjan mohantyBelum ada peringkat
- Paper III CYBER CRIMESDokumen38 halamanPaper III CYBER CRIMESSiddhant SinghBelum ada peringkat
- Cyber Cafe Pune CaseDokumen9 halamanCyber Cafe Pune CaseOne PlusBelum ada peringkat
- Chanakya National Law University, PatnaDokumen18 halamanChanakya National Law University, PatnaGunjan SinghBelum ada peringkat
- Cyber Defamation in IndiaDokumen5 halamanCyber Defamation in IndiaHitesh BansalBelum ada peringkat
- 0 l6 Cyber Crim in IndiaDokumen24 halaman0 l6 Cyber Crim in Indiame_chBelum ada peringkat
- 2 DIGITAL SIGNATURE and INFORMATION TECHNOLOGY LAWDokumen27 halaman2 DIGITAL SIGNATURE and INFORMATION TECHNOLOGY LAWShazaf KhanBelum ada peringkat
- Law of Crimes Study MaterialDokumen35 halamanLaw of Crimes Study Material23 Waystokill0% (1)
- 1500+ Research TopicsDokumen47 halaman1500+ Research TopicsrishikBelum ada peringkat
- Research On Legal Protection of Personal Data Privacy of E Commerce Platform UsersDokumen8 halamanResearch On Legal Protection of Personal Data Privacy of E Commerce Platform UsersEditor IJTSRDBelum ada peringkat
- IT Recruiter ResumeDokumen2 halamanIT Recruiter ResumeShankar Jii UppariBelum ada peringkat
- Financial ServicesDokumen21 halamanFinancial ServicesShankar Jii Uppari100% (1)
- Notes ON: (An E-Initiative by KCL)Dokumen4 halamanNotes ON: (An E-Initiative by KCL)Shankar Jii UppariBelum ada peringkat
- Shruti CV 081210Dokumen4 halamanShruti CV 081210Shankar Jii UppariBelum ada peringkat
- Case Name Topic Case No. ǀ Date Ponente Doctrine: USA College of Law Sobredo-1FDokumen1 halamanCase Name Topic Case No. ǀ Date Ponente Doctrine: USA College of Law Sobredo-1FAphrBelum ada peringkat
- DOX440 Gun Setup Chart Rev 062019Dokumen4 halamanDOX440 Gun Setup Chart Rev 062019trọng nguyễn vănBelum ada peringkat
- Executive Summary: Source of Commission: PMA Date of Commission: 16 March 2009 Date of Rank: 16 March 2016Dokumen3 halamanExecutive Summary: Source of Commission: PMA Date of Commission: 16 March 2009 Date of Rank: 16 March 2016Yanna PerezBelum ada peringkat
- Federalisms of US and IndiaDokumen3 halamanFederalisms of US and IndiaTanya TandonBelum ada peringkat
- Case 20Dokumen6 halamanCase 20Chelle Rico Fernandez BOBelum ada peringkat
- 00 Introduction ATR 72 600Dokumen12 halaman00 Introduction ATR 72 600destefani150% (2)
- Reducing Samples of Aggregate To Testing Size: Standard Practice ForDokumen5 halamanReducing Samples of Aggregate To Testing Size: Standard Practice FormickyfelixBelum ada peringkat
- Live2D Cubism 320 and Euclid Editor 131 Win PDFDokumen3 halamanLive2D Cubism 320 and Euclid Editor 131 Win PDFDavidBelum ada peringkat
- Shrimp Specialists V Fuji-TriumphDokumen2 halamanShrimp Specialists V Fuji-TriumphDeaBelum ada peringkat
- (Azizi Ali) Lesson Learnt From Tun Daim E-BookDokumen26 halaman(Azizi Ali) Lesson Learnt From Tun Daim E-BookgabanheroBelum ada peringkat
- IMO Online. AdvtDokumen4 halamanIMO Online. AdvtIndiaresultBelum ada peringkat
- Scenes From The Last Days of Communism in West Bengal by INDRAJIT HAZRADokumen22 halamanScenes From The Last Days of Communism in West Bengal by INDRAJIT HAZRAdonvoldy666Belum ada peringkat
- Boskalis Position Statement 01072022Dokumen232 halamanBoskalis Position Statement 01072022citybizlist11Belum ada peringkat
- Preamble 1Dokumen2 halamanPreamble 1api-273002310Belum ada peringkat
- 2015-08-24 065059 4.blood RelationsDokumen20 halaman2015-08-24 065059 4.blood Relationsჯონ ფრაატეეკBelum ada peringkat
- Rosalina Buan, Rodolfo Tolentino, Tomas Mercado, Cecilia Morales, Liza Ocampo, Quiapo Church Vendors, For Themselves and All Others Similarly Situated as Themselves, Petitioners, Vs. Officer-In-charge Gemiliano c. Lopez, JrDokumen5 halamanRosalina Buan, Rodolfo Tolentino, Tomas Mercado, Cecilia Morales, Liza Ocampo, Quiapo Church Vendors, For Themselves and All Others Similarly Situated as Themselves, Petitioners, Vs. Officer-In-charge Gemiliano c. Lopez, JrEliza Den DevilleresBelum ada peringkat
- Gujranwala Electric Power Company: C A R E E R O P P O R T U N I T I E SDokumen3 halamanGujranwala Electric Power Company: C A R E E R O P P O R T U N I T I E SABDUL HASEEBBelum ada peringkat
- Controlled Parking Zones Within Tower HamletsDokumen1 halamanControlled Parking Zones Within Tower Hamletsmoshkur.chowdhuryBelum ada peringkat
- Uy Tong V CADokumen3 halamanUy Tong V CAcmv mendozaBelum ada peringkat
- Rainforest Foundation - 2016.04 - Conservation and IPs in The Congo Basin PDFDokumen144 halamanRainforest Foundation - 2016.04 - Conservation and IPs in The Congo Basin PDFLaraBelum ada peringkat
- Learning Module: Community Colleges of The PhilippinesDokumen41 halamanLearning Module: Community Colleges of The PhilippinesGianina De LeonBelum ada peringkat
- Special Release 2020 CPH Population Counts July 13 2021 - 2Dokumen10 halamanSpecial Release 2020 CPH Population Counts July 13 2021 - 2AshBelum ada peringkat
- Chapter 10 State and Local Government ExpendituresDokumen34 halamanChapter 10 State and Local Government ExpendituresGabriel RegoBelum ada peringkat
- How To Instantly Connect With AnyoneDokumen337 halamanHow To Instantly Connect With AnyoneF C100% (2)
- PreviewDokumen9 halamanPreviewVignesh LBelum ada peringkat
- Posting and Preparation of Trial Balance 1Dokumen33 halamanPosting and Preparation of Trial Balance 1iTs jEnInOBelum ada peringkat
- A Guide To: Commons in ResearchDokumen7 halamanA Guide To: Commons in ResearchAna PaulaBelum ada peringkat
- Passing Off Action Under Trade Mark LawDokumen15 halamanPassing Off Action Under Trade Mark LawPappu KumarBelum ada peringkat
- 04 Dam Safety FofDokumen67 halaman04 Dam Safety FofBoldie LutwigBelum ada peringkat
- D6677Dokumen2 halamanD6677Robby DíazBelum ada peringkat
- For the Thrill of It: Leopold, Loeb, and the Murder That Shocked Jazz Age ChicagoDari EverandFor the Thrill of It: Leopold, Loeb, and the Murder That Shocked Jazz Age ChicagoPenilaian: 4 dari 5 bintang4/5 (97)
- Reasonable Doubts: The O.J. Simpson Case and the Criminal Justice SystemDari EverandReasonable Doubts: The O.J. Simpson Case and the Criminal Justice SystemPenilaian: 4 dari 5 bintang4/5 (25)
- Perversion of Justice: The Jeffrey Epstein StoryDari EverandPerversion of Justice: The Jeffrey Epstein StoryPenilaian: 4.5 dari 5 bintang4.5/5 (10)
- Dean Corll: The True Story of The Houston Mass MurdersDari EverandDean Corll: The True Story of The Houston Mass MurdersPenilaian: 4 dari 5 bintang4/5 (29)
- Hunting Whitey: The Inside Story of the Capture & Killing of America's Most Wanted Crime BossDari EverandHunting Whitey: The Inside Story of the Capture & Killing of America's Most Wanted Crime BossPenilaian: 3.5 dari 5 bintang3.5/5 (6)
- The Killer Across the Table: Unlocking the Secrets of Serial Killers and Predators with the FBI's Original MindhunterDari EverandThe Killer Across the Table: Unlocking the Secrets of Serial Killers and Predators with the FBI's Original MindhunterPenilaian: 4 dari 5 bintang4/5 (112)
- Lady Killers: Deadly Women Throughout HistoryDari EverandLady Killers: Deadly Women Throughout HistoryPenilaian: 4 dari 5 bintang4/5 (155)
- The Edge of Innocence: The Trial of Casper BennettDari EverandThe Edge of Innocence: The Trial of Casper BennettPenilaian: 4.5 dari 5 bintang4.5/5 (3)
- The Killer Across the Table: Unlocking the Secrets of Serial Killers and Predators with the FBI's Original MindhunterDari EverandThe Killer Across the Table: Unlocking the Secrets of Serial Killers and Predators with the FBI's Original MindhunterPenilaian: 4.5 dari 5 bintang4.5/5 (456)
- The Death of Punishment: Searching for Justice among the Worst of the WorstDari EverandThe Death of Punishment: Searching for Justice among the Worst of the WorstBelum ada peringkat
- A Warrant to Kill: A True Story of Obsession, Lies and a Killer CopDari EverandA Warrant to Kill: A True Story of Obsession, Lies and a Killer CopPenilaian: 4 dari 5 bintang4/5 (21)
- Ice and Bone: Tracking an Alaskan Serial KillerDari EverandIce and Bone: Tracking an Alaskan Serial KillerPenilaian: 3.5 dari 5 bintang3.5/5 (7)
- O.J. Is Innocent and I Can Prove It: The Shocking Truth about the Murders of Nicole Brown Simpson and Ron GoldmanDari EverandO.J. Is Innocent and I Can Prove It: The Shocking Truth about the Murders of Nicole Brown Simpson and Ron GoldmanPenilaian: 4 dari 5 bintang4/5 (2)
- Conviction: The Untold Story of Putting Jodi Arias Behind BarsDari EverandConviction: The Untold Story of Putting Jodi Arias Behind BarsPenilaian: 4.5 dari 5 bintang4.5/5 (16)
- The Secret Barrister: Stories of the Law and How It's BrokenDari EverandThe Secret Barrister: Stories of the Law and How It's BrokenPenilaian: 4.5 dari 5 bintang4.5/5 (12)
- Just Mercy: a story of justice and redemptionDari EverandJust Mercy: a story of justice and redemptionPenilaian: 4.5 dari 5 bintang4.5/5 (175)
- The Only Story That Has Not Been Told About OJ: What if he wasn't guilty?Dari EverandThe Only Story That Has Not Been Told About OJ: What if he wasn't guilty?Belum ada peringkat
- I Don't Like Mondays: The True Story Behind America's First Modern School ShootingDari EverandI Don't Like Mondays: The True Story Behind America's First Modern School ShootingPenilaian: 5 dari 5 bintang5/5 (1)
- Kidnapped by a Client: The Incredible True Story of an Attorney's Fight for JusticeDari EverandKidnapped by a Client: The Incredible True Story of an Attorney's Fight for JusticePenilaian: 3 dari 5 bintang3/5 (1)
- Innocent Blood: A True Story of Obsession and Serial MurderDari EverandInnocent Blood: A True Story of Obsession and Serial MurderPenilaian: 4.5 dari 5 bintang4.5/5 (72)
- What's Prison For?: Punishment and Rehabilitation in the Age of Mass IncarcerationDari EverandWhat's Prison For?: Punishment and Rehabilitation in the Age of Mass IncarcerationBelum ada peringkat
- Life Sentence: The Brief and Tragic Career of Baltimore’s Deadliest Gang LeaderDari EverandLife Sentence: The Brief and Tragic Career of Baltimore’s Deadliest Gang LeaderPenilaian: 4.5 dari 5 bintang4.5/5 (16)
- Wolf Boys: Two American Teenagers and Mexico's Most Dangerous Drug CartelDari EverandWolf Boys: Two American Teenagers and Mexico's Most Dangerous Drug CartelPenilaian: 4.5 dari 5 bintang4.5/5 (61)
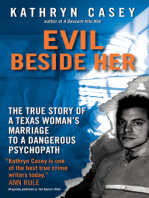
- Evil Beside Her: The True Story of a Texas Woman's Marriage to a Dangerous PsychopathDari EverandEvil Beside Her: The True Story of a Texas Woman's Marriage to a Dangerous PsychopathPenilaian: 4 dari 5 bintang4/5 (47)