ATN 905 V200R002C01 Configuration Guide 03 (CLI)
Diunggah oleh
Salman IqbalJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
ATN 905 V200R002C01 Configuration Guide 03 (CLI)
Diunggah oleh
Salman IqbalHak Cipta:
Format Tersedia
ATN 905 Multi-Service Access Equipment
V200R002C01
Configuration Guide (CLI)
Issue
03
Date
2013-11-22
HUAWEI TECHNOLOGIES CO., LTD.
Copyright Huawei Technologies Co., Ltd. 2013. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior written
consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and the
customer. All or part of the products, services and features described in this document may not be within the
purchase scope or the usage scope. Unless otherwise specified in the contract, all statements, information,
and recommendations in this document are provided "AS IS" without warranties, guarantees or representations
of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address:
Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website:
http://www.huawei.com
Email:
support@huawei.com
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
About This Document
About This Document
Purpose
This document provides the basic concepts, configuration procedures, and configuration
examples in different application scenarios of the Lan features supported by the ATN 905 device.
The usage precautions are as follows:
l
A device can store keys in plaintext, reversible algorithm encryption, or irreversible
algorithm encryption mode. The plaintext mode has the low security level, and the
irreversible algorithm encryption mode has the highest security level. Use different storage
modes for different scenarios. Exercise caution when using an insecure storage mode. The
system automatically selects the irreversible algorithm encryption mode to store local user
keys. Generally, the reversible algorithm encryption mode is used to store protocol keys to
meet interworking requirements.
If the plaintext mode is used, a password is stored in plaintext in the configuration file. This
results in high security risks. The plaintext mode applies only to scenarios with special
requirements, such as compatibility and interworking requirements.
Related Version
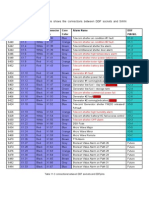
The following table lists the product version related to this document.
Product Name
Version
ATN 905
V200R002C01
Intended Audience
This document is intended for:
l
Commissioning Engineer
Data Configuration Engineer
Network Monitoring Engineer
System Maintenance Engineer
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ii
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
About This Document
Symbol Conventions
Symbol
Description
DANGER
WARNING
CAUTION
Indicates a hazard with a high level of risk, which if not
avoided, will result in death or serious injury.
Indicates a hazard with a medium or low level of risk, which
if not avoided, could result in minor or moderate injury.
Indicates a potentially hazardous situation, which if not
avoided, could result in equipment damage, data loss,
performance degradation, or unexpected results.
TIP
Indicates a tip that may help you solve a problem or save
time.
NOTE
Provides additional information to emphasize or supplement
important points of the main text.
Command Conventions
Issue 03 (2013-11-22)
Convention
Description
Boldface
The keywords of a command line are in boldface.
Italic
Command arguments are in italics.
[]
Items (keywords or arguments) in brackets [ ] are optional.
{ x | y | ... }
Optional items are grouped in braces and separated by
vertical bars. One item is selected.
[ x | y | ... ]
Optional items are grouped in brackets and separated by
vertical bars. One item is selected or no item is selected.
{ x | y | ... }*
Optional items are grouped in braces and separated by
vertical bars. A minimum of one item or a maximum of all
items can be selected.
[ x | y | ... ]*
Optional items are grouped in brackets and separated by
vertical bars. Several items or no item can be selected.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iii
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
About This Document
GUI Conventions
Convention
Description
Boldface
Buttons, menus, parameters, tabs, window, and dialog titles
are in boldface. For example, click OK.
>
Multi-level menus are in boldface and separated by the ">"
signs. For example, choose File > Create > Folder.
Change History
Updates between document issues are cumulative. Therefore, the latest document issue contains
all updates made in previous issues.
Changes in Issue 03 (2013-11-22)
This document has the following updates:
Known bugs are fixed.
Changes in Issue 02 (2013-08-15)
This document has the following updates:
Known bugs are fixed.
Changes in Issue 01 (2013-05-30)
This document is the first release of the V200R002C01 version.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iv
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Contents
Contents
About This Document.....................................................................................................................ii
1 Application Scenario Overview..................................................................................................1
1.1 Small-cell Base Station Bearer Scenario........................................................................................................................2
1.2 EDD Scenario.................................................................................................................................................................2
2 Configuration Overview..............................................................................................................5
2.1 Networking Models........................................................................................................................................................6
2.2 Configuration Overview.................................................................................................................................................7
2.2.1 Select Overall Solution..............................................................................................................................................13
2.2.2 Select Management Plane Configuration Solution....................................................................................................14
2.2.3 Select Service Solution..............................................................................................................................................16
2.3 Recommended Solutions..............................................................................................................................................19
3 Solution 1: Native IP VRF Static Route Access......................................................................23
3.1 Scenario Introduction...................................................................................................................................................25
3.2 Logging In to the ATN 905..........................................................................................................................................28
3.2.1 Logging In to the ATN 905 by Using SSH...............................................................................................................28
3.2.2 Logging In to the ATN 905 by Using the Console Interface....................................................................................30
3.3 Configuring Basic Information.....................................................................................................................................33
3.3.1 Configuring an NE Name..........................................................................................................................................34
3.3.2 Configuring the VTY User Interface.........................................................................................................................35
3.3.3 Configuring AAA Users............................................................................................................................................36
3.3.4 Configuring the SNMP..............................................................................................................................................37
3.4 Deploying the Management Plane................................................................................................................................39
3.4.1 Configuration Roadmap............................................................................................................................................40
3.4.2 Data Planning............................................................................................................................................................40
3.4.3 Configuring the Management Plane..........................................................................................................................41
3.5 Deploying VRF Lite Services.......................................................................................................................................41
3.5.1 Configuration Roadmap............................................................................................................................................42
3.5.2 Data Planning............................................................................................................................................................43
3.5.3 Configuring VRF Lite Services.................................................................................................................................46
3.6 Deploying Static Routes...............................................................................................................................................48
3.6.1 Configuration Roadmap............................................................................................................................................48
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Contents
3.6.2 Data Planning............................................................................................................................................................49
3.6.3 Configuring Static Routes.........................................................................................................................................52
3.6.4 Checking Static Route Configurations......................................................................................................................53
3.7 Deploying QoS.............................................................................................................................................................54
3.7.1 Configuring QoS........................................................................................................................................................54
3.8 Deploying the Clock.....................................................................................................................................................55
3.8.1 Configuration Roadmap............................................................................................................................................55
3.8.2 Data Planning............................................................................................................................................................56
3.8.3 Configuring Synchronous Ethernet to Achieve Frequency Synchronization............................................................57
3.8.4 Configuring IEEE 1588v2 to Achieve Time Synchronization..................................................................................58
4 Solution 2: Native IP VRF Dynamic Route Access...............................................................60
4.1 Scenario Introduction...................................................................................................................................................62
4.2 Logging In to the ATN 905..........................................................................................................................................65
4.2.1 Logging In to the ATN by Using SSH......................................................................................................................65
4.2.2 Logging In to the ATN by Using the Console Interface...........................................................................................67
4.3 Configuring Basic Information.....................................................................................................................................70
4.3.1 Configuring NE Information.....................................................................................................................................71
4.3.2 Configuring the VTY User Interface.........................................................................................................................72
4.3.3 Configuring AAA Users............................................................................................................................................73
4.3.4 Configuring the SNMP..............................................................................................................................................74
4.4 Configuring the Management Plane.............................................................................................................................76
4.4.1 Configuring the Management Plane..........................................................................................................................76
4.5 Deploying VRF Lite Services.......................................................................................................................................78
4.5.1 Configuration Roadmap............................................................................................................................................78
4.5.2 Data Planning............................................................................................................................................................79
4.5.3 Configuring VRF Lite Services.................................................................................................................................83
4.6 Deploying the IGP........................................................................................................................................................85
4.6.1 Configuring the IS-IS................................................................................................................................................85
4.6.2 Deploying the OSPF..................................................................................................................................................90
4.7 Deploying QoS.............................................................................................................................................................94
4.7.1 Configuring QoS........................................................................................................................................................94
4.8 Deploying the Clock.....................................................................................................................................................95
4.8.1 Configuration Roadmap............................................................................................................................................95
4.8.2 Data Planning............................................................................................................................................................96
4.8.3 Configuring Synchronous Ethernet to Achieve Frequency Synchronization............................................................97
4.8.4 Configuring IEEE 1588v2 to Achieve Time Synchronization..................................................................................98
5 Solution 3: Native Ethernet Access........................................................................................100
5.1 Scenario Introduction.................................................................................................................................................101
5.2 Logging In to the ATN 905........................................................................................................................................103
5.2.1 Logging In to the ATN by Using SSH....................................................................................................................103
5.2.2 Logging In to the ATN by Using the Console Interface.........................................................................................105
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
vi
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Contents
5.3 Configuring Basic Information...................................................................................................................................108
5.3.1 Configuring NE Information...................................................................................................................................109
5.3.2 Configuring the VTY User Interface.......................................................................................................................110
5.3.3 Configuring AAA Users..........................................................................................................................................111
5.3.4 Configuring the SNMP............................................................................................................................................112
5.4 Configuring the Management Plane...........................................................................................................................114
5.4.1 Configuration Roadmap..........................................................................................................................................114
5.4.2 Data Planning..........................................................................................................................................................115
5.4.3 Configuring the Management Plane........................................................................................................................116
5.5 Deploying the serive...................................................................................................................................................117
5.5.1 Configuration Roadmap..........................................................................................................................................117
5.5.2 Data Planning..........................................................................................................................................................118
5.5.3 Configuring Ethernet Services.................................................................................................................................119
5.6 Deploying QoS...........................................................................................................................................................121
5.6.1 Configuring QoS......................................................................................................................................................121
5.7 Deploying the Clock...................................................................................................................................................122
5.7.1 Configuration Roadmap..........................................................................................................................................122
5.7.2 Data Planning..........................................................................................................................................................123
5.7.3 Configuring Synchronous Ethernet to Achieve Frequency Synchronization..........................................................124
5.7.4 Configuring IEEE 1588v2 to Achieve Time Synchronization................................................................................125
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
vii
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
1 Application Scenario Overview
Application Scenario Overview
About This Chapter
ATN 905 is small-sized, light-weighted, and low power-consuming case-shaped equipment. The
application scenarios of ATN 905 are divided into the small-cell base station bearer scenario
and the Ethernet demarcation device (EDD) scenario.
1.1 Small-cell Base Station Bearer Scenario
1.2 EDD Scenario
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
1 Application Scenario Overview
1.1 Small-cell Base Station Bearer Scenario
Application Scenarios
1.
Small-cell base station bearer scenario
Mobile networks are transforming from dominant macro base stations to co-existing macro
and small-cell base stations. In addition, small-cell base stations, with characteristics such
as low cost, wide coverage, and easy installation, will play a more and more important role
in future network construction.
In Huawei's mobile bearer solution, ATN 905 devices are used as small-cell base station
bearer NEs and connected to the access device (the CSG in the figure) at the macro base
station in chain networking mode. As an extension of the IPRAN mobile bearer solution
based on the macro base station, Huawei's mobile bearer solution integrates mobile bearer
clock and maintenance solutions in an end-to-end manner, and features low cost, easy
deployment, and easy O&M. Figure 1 shows the networking diagram of the solution using
the ATN 905 as the bearer device at the small-cell base station.
Figure 1-1 Networking diagram of the small-cell base station bearer solution
Small-cell Base
Station Access
Micro/Pico
Micro/Pico
IPRAN
Macro Cell
BSC
ATN 905
ATN 905
RNC
Micro/Pico
Micro/Pico
CSG
ASG
RSG
MME
/SGW
NOTE
The mobile bearer device at the macro base station may be a third-party device. In this topic, Huawei's
IPRAN solution (ATN + CX networking) on the macro base station side is used as an example to illustrate
the deployment configuration.
1.2 EDD Scenario
Application Scenario Overview
A provider network is large-scale and complex, making management and fault locating difficult.
The Ethernet demarcation device (EDD) is a key element in provider-level Ethernet services,
leased network services, and applications of mobile backhaul networks. By deploying an EDD
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
1 Application Scenario Overview
on the user side and connecting it to the CPE, the provider separates the customer network from
the provider network. As an EDD, Huawei's ATN 905 provides strong link OAM functions,
performs end-to-end fault monitoring and diagnosis, and automatically verifies the service level
agreement (SLA).
1.
Dividing Maintenance Responsibilities for the Provider's Departments
As shown in Figure 1, the provider network is divided into different maintenance domains
based on maintenance responsibilities. These maintenance domains are independent from
each other and do not need to perceive each other. There are boundaries between different
maintenance domains, and the boundaries need to be clearly demarcated to facilitate
maintenance. For example, how to divide maintenance responsibilities for the provider's
wireless and network departments in the case of an argument? An EDD can be deployed
at each base station to obtain information such as the throughput, packet loss rate, latency,
and jitter.
Figure 1-2 Dividing Maintenance Responsibilities for the Provider's Departments
Wireless maintenance territory
MBH maintenance territory
BSC
ASG
EDD
RSG
CSG
RNC
ATN 905
2.
Demarcating the Provider Network and Enterprise Network
As shown in Figure 2, on an enterprise private line network, the enterprise user's CPE
connects to the provider's PE using an optical fiber. However, the CPE is usually far from
the PE, so maintenance responsibilities are difficult to divide in the case of a fault.
Figure 1-3 Enterprise private line network with the EDD
User Network
CPE
Provider Network
EDD
PE
User Network
PE
ATN 905
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
EDD
CPE
ATN 905
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
1 Application Scenario Overview
As shown in Figure 3, an enterprise rents a 100M private line from a provider. However,
the enterprise user considers the bandwidth as lower than 100 M. In the case of a fault on
the enterprise user network, the enterprise user tends to call the provider and complain.
How can the provider divide the maintenance responsibilities? The provider can deploy an
EDD near the CPE and test the throughput using RFC 2544 before the deployment so as
to prove that the bandwidth meets the requirements. After services are provisioned, the
EDD monitors service packets in real time using IP FPM, obtains information such as the
throughput, packet loss rate, latency, and jitter, and periodically provides an SLA to the
enterprise user so as to prove the provider's network quality.
Figure 1-4 Enterprise private line network without the EDD
User Network
Provider Network
CPE
3.
PE
User Network
CPE
PE
Demarcating the Provider Network and Leased Network
As shown in Figure 4, provider B rents a network from provider A. However, faults cannot
be clearly demarcated, so arguments always occur between providers A and B. To resolve
this problem, an EDD can be deployed on provider A's side and deploy OAM functions
such as RFC 2544 and IP FPM based on live network requirements to monitor and measure
information such as the throughput, packet loss rate, latency, and jitter. In this manner,
maintenance responsibilities can be divided.
Figure 1-5 Demarcating the Provider Network and Leased Network
Wholesale Network
Provider Network
EDD
PE
PE
ATN 905
B
A
NOTE
For easy description, the upstream network of the EDD is called aggregation network.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Configuration Overview
About This Chapter
2.1 Networking Models
2.2 Configuration Overview
2.3 Recommended Solutions
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
2.1 Networking Models
Networking Model for the Configuration Example
The application scenarios of the ATN 905 are small-base station bearer and enterprise private
line EDD. From the deployment point of view, the solutions can be classified into the following
types by access technology.
l
Native IP access solution
Native Ethernet access solution
In both solutions, the ATN 905 is connected to the nearby network of the operator. If the
operator's network is regarded as an abstract "cloud", only the deployment and configuration of
the part (marked by the dotted rectangle on the left) on the access network need to be considered.
For the marked part of the access network, the configuration roadmaps and procedures in both
solutions are basically the same. Therefore, this topic only provides detailed configuration
description from the angle of the access technology. That is, scenarios are not differentiated
while only solutions are differentiated. The following typical networking models are provided
for the configuration example.
l
Native IP scenario: Layer 3 IP packets are forwarded between the ATN 905 and CSG.
Micro/Pico
Macro Cell
RNC/SGW
ATN 905
ATN 905
IPRAN
CSG
Micro/Pico
Native IP
Traffic flow
Issue 03 (2013-11-22)
Native Ethernet scenario: Layer 2 Ethernet packets are forwarded between the ATN 905
and CSG.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Micro/Pico
Macro Cell
RNC/SGW
ATN 905
ATN 905
IPRAN
CSG
Micro/Pico
Native Eth
Traffic flow
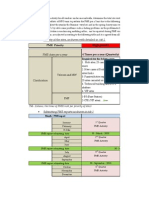
2.2 Configuration Overview
Overall Configuration Roadmap
1.
Overall solution selection: Determine the small-cell base station bearer solution or EDD
bearer solution based on the macro base station mobile bearer solution or aggregation
network bearer solution.
NOTE
Typical networking models are used in the following schematic diagrams, regardless of the small-cell base
station bearer solution or EDD bearer solution. For details, see Networking Models.
Scenario
Overall
Solution
l If a Layer 3 access solution
(such as HVPN) is used on
the macro base station side,
you are advised to deploy
the native IP solution
between the ATN 905 and
cell site gateway (CSG) to
forward services.
Native IP
solution
l If a Layer 3 access solution
(such as MPLS/IP) is used
on the aggregation network,
you are advised to deploy
the native IP solution
between the ATN 905 and
PE to forward services.
Diagram
Macro Cell
Micro/Pico
ATN 905
ATN 905
IPRAN
RNC
CSG
Micro/Pico
Native IP
This solution facilitates end-toend IP-based continuity check
(CC) and performance
monitoring.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Scenario
Overall
Solution
l If a Layer 2 or Layer 2 +
Layer 3 access solution
(such as mixed VPN) is used
on the macro base station
side, you are advised to
deploy the native Ethernet
solution between the ATN
905 and CSG to
transparently transmit
packets from the small-cell
base station.
Native
Ethernet
solution
2 Configuration Overview
Diagram
Macro Cell
Micro/Pico
ATN 905
ATN 905
IPRAN
RNC
CSG
Micro/Pico
Native Eth
l If a Layer 2 access solution
(such as metro Ethernet) is
used on the aggregation
network, you are advised to
deploy the native Ethernet
solution between the ATN
905 and PE to forward
services.
In this solution, the VLAN
information of the small-cell
base station or enterprise
private line user is not
modified. Instead, packets of
the small-cell base station or
enterprise private line user are
transparently transmitted.
2.
Service solution selection: During actual service deployment, multiple feature solutions
are available. The following describes the applicable scenarios of these feature solutions.
You can choose an appropriate solution based on the actual networking requirements.
a.
Select a management plane configuration solution based on the overall solution
selected in step 1 and the actual networking requirements.
Prerequisit
e
Scenario
Managemen
t Plane Mode
Advantage
Disadvantage
Native IP/
Native
Ethernet
solution
The network
scale is small.
Public network
static route
The reliability and stability
are high.
The scalability is poor. When
the network topology
changes, static routes need to
be manually configured again.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Prerequisit
e
2 Configuration Overview
Scenario
Managemen
t Plane Mode
Advantage
1. The
network
scale is
large.
Public network
IGP
1. The scalability is high and IGP configurations need to be
routes are automatically
planned and maintained.
adjusted when the network
topology changes.
2. Upstream
devices
are
managed
using the
public
network
IGP.
Disadvantage
2. The management mode
can be the same as that of
the upstream IPRAN or
aggregation network.
The ATN 905
is networked
with Huawei
products.
Private
network DCN
1. The configuration is
simple and management
routes do not need to be
configured by NE.
The CSG (or PE) must be a
Huawei product.
2. The scalability is high.
When devices are added to
the network, the
management plane
configuration of other
devices does not need to be
modified.
3. The management mode
can be the same as that of
the upstream IPRAN or
aggregation network.
Figure 2-1 Management plane configuration diagram
Micro/Pico
Micro/Pico
Macro Cell
ATN 905
ATN 905
IPRAN
CSG
RNC
Micro/Pico
Micro/Pico
b.
Issue 03 (2013-11-22)
Public network static route/
Public network IGP/
Private network DCN
management flow
Select a service plane access mode based on the overall solution selected in step 1
and the actual networking requirements.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
a.
2 Configuration Overview
If the native IP solution is selected in step 1:
Prerequisite
Scenario
Access Mode
Advantage
Disadvantage
Native IP
solution
Users or
services need
to be
separated.
VRF access
This solution can separate
services.
Configurations for this
solution is complex because a
unique IP route and Interior
Gateway Protocol (IGP)
process need to be planned
and configured for each
virtual routing and
forwarding (VRF) instance as
required.
l This solution can separate
different wireless
operators accessed to a
network using the ATN
905 as the backhaul
device for the small-cell
base station.
l This solution can separate
different enterprise users
accessed to a network
using the ATN 905 as the
EDD.
Users or
services do
not need to be
separated.
Entire public
network
access
The planning and
configuration is simple. A
unique IP route and IGP
process for each VRF
instance can be resolved only
by making public network
channels available.
This solution cannot separate
users or separate services
from the management plane.
IP addresses need to be
planned in a centralized
manner.
Figure 2-2 Native IP service access (VRF access) configuration diagram
VRF1
VRF2
ATN 905
Macro Cell
ATN 905
IPRAN
CSG
VRF2
Issue 03 (2013-11-22)
VRF1
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
RNC
main interface
Dot1q sub-interface
VRF1 service flow
VRF2 service flow
10
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Figure 2-3 Native IP service access (public network access) configuration
diagram
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
RNC
CSG
VRF2
b.
Main interface
VRF1
Service flow
If the native Ethernet solution is selected in step 1:
Prerequisite
Scenario
Access Mode
Advantage
Disadvantage
Native
Ethernet
solution
Users or
services do
not need to be
separated.
Hybrid
interface
access
Extra encapsulation costs are
saved.
VLANs for customers and
operators need to be planned
in a centralized manner.
Figure 2-4 Native Ethernet service access (hybrid interface access) configuration
diagram
port trunk allow-pass vlan 10 to 20
Macro Cell
VLAN10
VLAN20
IPRAN
ATN 905
ATN 905
VLAN20
c.
Issue 03 (2013-11-22)
VLAN10
CSG
RNC
Hybrid interface
Service flow
If the native IP solution is selected in step 1, select a service plane routing mode
based on the actual networking requirements. If the native Ethernet solution is selected
in step 1, skip this step.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Prerequisit
e
Scenario
Service plane
routing mode
Advantage
Disadvantage
Native IP
solution
The network
scale is small.
Static Route
1. The configuration is
simple.
The scalability is poor.
l When a small-cell base
station is added to the
network, static routes
need to be added by hop
for the network segment
from the small-cell base
station to the
corresponding macro
base station.
2. The reliability and
stability are high, and
network flapping caused
by a network topology
change is prevented.
l When a PE is added to the
network, static routes
need to be added by hop
for the network segment
from the PE to the EDD.
The network
scale is large.
IGP route
1. The scalability is high.
When a device is added to
the network, only the
interface configurations
on its adjacent devices
need to be adjusted.
Configurations on other
devices do not need to be
modified.
1. IGP configurations need
to be planned and
maintained.
2. Network flapping may
occur when the network
topology changes.
Figure 2-5 Service plane route configuration diagram
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
Static route / IGP
d.
Issue 03 (2013-11-22)
RNC
Service flow
Select the QoS deployment mode based on the actual networking requirements.
Scenario
QoS Mode
Traffic management is required.
Simple traffic classification
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
e.
2 Configuration Overview
Select the clock deployment mode based on the actual networking requirements.
Scenario
Clock Mode
Frequency synchronization needs to
be achieved between NEs.
Synchronous Ethernet
Time synchronization needs to be
achieved between NEs.
1588v2
2.2.1 Select Overall Solution
Solution Selection Principle
Determine the small-cell base station bearer solution or EDD bearer solution based on the macro
base station mobile bearer solution or aggregation network bearer solution.
Scenario
Overall
Solution
l If a Layer 3 access solution
(such as HVPN) is used on
the macro base station side,
you are advised to deploy
the native IP solution
between the ATN 905 and
cell site gateway (CSG) to
forward services.
Native IP
solution
l If a Layer 3 access solution
(such as MPLS/IP) is used
on the aggregation network,
you are advised to deploy
the native IP solution
between the ATN 905 and
PE to forward services.
Diagram
Macro Cell
Micro/Pico
ATN 905
ATN 905
IPRAN
RNC
CSG
Micro/Pico
Native IP
This solution facilitates end-toend IP-based continuity check
(CC) and performance
monitoring.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Scenario
Overall
Solution
l If a Layer 2 or Layer 2 +
Layer 3 access solution
(such as mixed VPN) is used
on the macro base station
side, you are required to
deploy the native Ethernet
solution between the ATN
905 and CSG to
transparently transmit
packets from the small-cell
base station.
Native
Ethernet
solution
2 Configuration Overview
Diagram
Macro Cell
Micro/Pico
ATN 905
ATN 905
IPRAN
RNC
CSG
Micro/Pico
Native Eth
l If a Layer 2 access solution
(such as metro Ethernet) is
used on the aggregation
network, you are required to
deploy the native Ethernet
solution between the ATN
905 and PE to forward
services.
In this solution, the VLAN
information of the small-cell
base station or enterprise
private line user is not
modified. Instead, packets of
the small-cell base station or
enterprise private line user are
transparently transmitted.
2.2.2 Select Management Plane Configuration Solution
Solution Selection Principle
Select a management plane configuration solution based on the overall solution selected in
step 1 and the actual networking requirements.
Prerequisit
e
Scenario
Managemen
t Plane Mode
Advantage
Disadvantage
Native IP/
Native
Ethernet
solution
The network
scale is small.
Public network
static route
The reliability and stability
are high.
The scalability is poor. When
the network topology
changes, static routes need to
be manually configured again.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Prerequisit
e
2 Configuration Overview
Scenario
Managemen
t Plane Mode
Advantage
1. The
network
scale is
large.
Public network
IGP
1. The scalability is high and IGP configurations need to be
routes are automatically
planned and maintained.
adjusted when the network
topology changes.
2. Upstream
devices
are
managed
using the
public
network
IGP.
The ATN 905
is networked
with Huawei
products.
Disadvantage
2. The management mode
can be the same as that of
the upstream IPRAN or
aggregation network.
the VRF of
Private
network DCN
1. The configuration is
simple and management
routes do not need to be
configured by NE.
The CSG (or PE) must be a
Huawei product.
2. The scalability is high.
When devices are added to
the network, the
management plane
configuration of other
devices does not need to be
modified.
3. The management mode
can be the same as that of
the upstream IPRAN or
aggregation network.
Figure 2-6 Management plane configuration diagram
Micro/Pico
Micro/Pico
Macro Cell
ATN 905
ATN 905
IPRAN
CSG
RNC
Micro/Pico
Micro/Pico
Issue 03 (2013-11-22)
Public network static route/
Public network IGP/
Private network DCN
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
management flow
15
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
2.2.3 Select Service Solution
Overview
The service solution selection involves the following parts:
1.
Selecting the service plane access mode
2.
Selecting the service plane routing mode
3.
Selecting the QoS deployment mode
4.
Selecting the clock deployment mode
Solution Selection Principle
1.
Select a service plane access mode based on the overall solution selected in step 1 and the
actual networking requirements.
a.
If the native IP solution is selected in step 1:
Prerequisite
Scenario
Access Mode
Advantage
Disadvantage
Native IP
solution
Users or
services need
to be
separated.
VRF access
This solution can separate
services.
Configurations for this
solution is complex because a
unique IP route and Interior
Gateway Protocol (IGP)
process need to be planned
and configured for each
virtual routing and
forwarding (VRF) instance as
required.
l This solution can separate
different wireless
operators accessed to a
network using the ATN
905 as the backhaul
device for the small-cell
base station.
l This solution can separate
different enterprise users
accessed to a network
using the ATN 905 as the
EDD.
Users or
services do
not need to be
separated.
Issue 03 (2013-11-22)
Entire public
network
access
The planning and
configuration is simple. A
unique IP route and IGP
process for each VRF
instance can be resolved only
by making public network
channels available.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
This solution cannot separate
users or separate services
from the management plane.
IP addresses need to be
planned in a centralized
manner.
16
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Figure 2-7 Native IP service access (VRF access) configuration diagram
VRF2
VRF1
ATN 905
Macro Cell
ATN 905
IPRAN
RNC
CSG
VRF2
main interface
Dot1q sub-interface
VRF1 service flow
VRF2 service flow
VRF1
Figure 2-8 Native IP service access (public network access) configuration diagram
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
RNC
CSG
VRF2
b.
Main interface
VRF1
Service flow
If the native Ethernet solution is selected in step 1:
Prerequisite
Scenario
Access Mode
Advantage
Disadvantage
Native
Ethernet
solution
Users or
services do
not need to be
separated.
Hybrid
interface
access
Extra encapsulation costs are
saved.
VLANs for customers and
operators need to be planned
in a centralized manner.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Figure 2-9 Native Ethernet service access (hybrid interface access) configuration
diagram
port trunk allow-pass vlan 10 to 20
Macro Cell
VLAN10
VLAN20
IPRAN
ATN 905
ATN 905
VLAN20
2.
VLAN10
CSG
RNC
Hybrid interface
Service flow
If the native IP solution is selected in step 1, select a service plane routing mode based
on the actual networking requirements. If the native Ethernet solution is selected in step 1,
skip this step.
Prerequisit
e
Scenario
Service plane
routing mode
Advantage
Disadvantage
Native IP
solution
The network
scale is small.
Static Route
1. The configuration is
simple.
The scalability is poor.
2. The reliability and
stability are high, and
network flapping caused
by a network topology
change is prevented.
l When a small-cell base
station is added to the
network, static routes
need to be added by hop
for the network segment
from the small-cell base
station to the
corresponding macro
base station.
l When a PE is added to the
network, static routes
need to be added by hop
for the network segment
from the PE to the EDD.
The network
scale is large.
Issue 03 (2013-11-22)
IGP route
1. The scalability is high.
When a device is added to
the network, only the
interface configurations
on its adjacent devices
need to be adjusted.
Configurations on other
devices do not need to be
modified.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
1. IGP configurations need
to be planned and
maintained.
2. Network flapping may
occur when the network
topology changes.
18
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Figure 2-10 Service plane route configuration diagram
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
Static route / IGP
3.
4.
RNC
Service flow
Select the QoS deployment mode based on the actual networking requirements.
Scenario
QoS Mode
Traffic management is required.
Simple traffic classification
Select the clock deployment mode based on the actual networking requirements.
Scenario
Clock Mode
Frequency synchronization needs to be
achieved between NEs.
Synchronous Ethernet
Time synchronization needs to be
achieved between NEs.
1588v2
2.3 Recommended Solutions
Introduction to the Recommended Solutions
Huawei recommends the following solutions based on the common networking modes:
1.
Solution 1: Native IP + public network static management plane + VRF access + static
route
2.
Solution 2: Native IP + DCN private network management plane + VRF access +
dynamic route
3.
Solution 3: Native Ethernet + public network IGP management plane + hybrid
interface access
NOTE
The preceding recommended solutions are only common ones and there are also other combination types.
Issue 03 (2013-11-22)
Solution 1: Native IP + public network static management plane + VRF access + static
route
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
19
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Application Scope
Advantage
Constraint
This solution applies to
small-scale networks that
use a Layer 3 access
solution as the macro base
station bearer solution (or
the aggregation network
bearer solution in the
EDD scenario) in a
mobile bearer solution.
1. The configuration is
simple. The basic native
IP feature is used,
dynamic protocols such
as the IGP are not
involved, and the IGP
does not need to be
planned.
1. This solution does not
apply to large-scale
networks.
2. Users are separated
using the VRF.
3. Interconnection with
third-party equipment is
supported. That is, the
mobile bearer NE (or
PE) on the macro base
station side can be a
third-party NE.
Issue 03 (2013-11-22)
l When a small-cell
base station is added
to the network, static
routes need to be
added by hop for the
network segment
from the small-cell
base station to the
corresponding macro
base station.
l When a PE is added
to the network, static
routes need to be
added by hop for the
network segment
from the PE to the
EDD.
Solution 2: Native IP + DCN private network management plane + VRF access +
dynamic route
Application Scope
Advantage
Constraint
This solution applies to
networks of any scale that
use a Layer 3 access
solution as the macro base
station bearer solution (or
the aggregation network
bearer solution in the
EDD scenario) in a
mobile bearer solution.
1. This solution is
recommended for
relatively large
networks.
1. IGP configurations need
to be planned and
maintained.
NOTE
This solution applies to
networks built with Huawei
equipment only. Equipment
can be managed together
with the upstream
equipment using a DCN
private network, which is
convenient and effective.
2. The scalability is poor.
2. The scalability is high.
When a small-cell base
station is added to the
network, only the
interface configurations
on its adjacent devices
need to be adjusted.
Configurations on other
devices do not need to be
modified.
2. Network flapping may
occur when the network
topology changes.
3. Users are separated
using the VRF.
Solution 3: Native Ethernet + public network IGP management plane + hybrid
interface access
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
20
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
2 Configuration Overview
Application Scope
Advantage
Constraint
This solution applies to
networks of any scale that
use a Layer 2 access
solution as the macro base
station bearer solution (or
the aggregation network
bearer solution in the
EDD scenario) in a
mobile bearer solution.
1. This solution is
especially applicable to
scenarios in which the
ATN 905 is used as the
EDD.
1. A protocol needs to be
configured to prevent
loops and Layer 2
broadcast storms.
2. VLANs for customers
and operators do not
need to be separated.
Overall Configuration Roadmap of the Recommended Solutions
Opti
on
Solution 1: Native IP
+ Public Network
Static Management
Plane + VRF Access +
Static Route
Solution 2: Native IP +
DCN Private Network
Management Plane +
VRF Access + Dynamic
Route
Solution 3: Native
Ethernet + Public
Network IGP
Management Plane +
Hybrid Interface Access
Mana
geme
nt
plane
confi
gurati
on
1. Use Layer 3
subinterfaces
between the ATN
905 and backhaul
device at the macro
base station to
establish public
network IP
connections.
1. Plan and configure an
NE IP address for each
NE.
1. Establish public
network IP
interconnections
between the ATN 905
and the CSG (or PE)
using Layer 3
subinterfaces.
2. Manage the ATN 905
using the DCN
management plane.
2. On the ATN 905,
create a loopback
interface on the ATN
905 and configure a
management IP
address for it.
3. Configure public
static routes leading
from the ATN 905 to
the NMS by hop for
the network segment
from the ATN 905 to
the CSG (or PE).
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
21
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
Opti
on
Solution 1: Native IP
+ Public Network
Static Management
Plane + VRF Access +
Static Route
Solution 2: Native IP +
DCN Private Network
Management Plane +
VRF Access + Dynamic
Route
Solution 3: Native
Ethernet + Public
Network IGP
Management Plane +
Hybrid Interface Access
Servi
ce
confi
gurati
on
1. Establish VRFinstance-based IP
connections between
the ATN 905 and the
CSG (or PE) using
Layer 3
subinterfaces.
1. Establish VRFinstance-based IP
connections between
the ATN 905 and the
CSG (or PE) using
Layer 3 subinterfaces.
1. Switch the AC port of
the ATN 905 to a Layer
2 switching port and
configure a segment of
VLANs that the AC
interface allows to pass
through.
2. Bind the AC port of
the ATN 905 to the
VRF instance that
the directlyconnected small-cell
base station (or CPE)
belongs to.
3. Configure static
routes leading to the
small-base station
and RNC by hop for
the network segment
from the ATN 905 to
the CSG (or PE).
Issue 03 (2013-11-22)
2 Configuration Overview
2. Bind the AC port of the
ATN 905 to the VRF
instance that the
directly-connected
small-cell base station
(or CPE) belongs to.
3. Configure an
independent IGP
process for each VRF
instance between the
ATN 905 and the CSG
(or PE) to learn the
routes leading to the
small-cell base station
(or CPE) and RNC (or
PE) respectively.
2. Switch the NNI of the
ATN 905 to a Layer 2
switching port and add a
segment of VLANs that
each AC interface
allows to pass through.
3. On the access port of the
CSG (or PE), configure
a virtual leased line
(VLL) for each service
VLAN or terminate the
VLAN for Layer 3
forwarding.
QoS
confi
gurati
on
Enable simple traffic classification for each service interface.
Clock
confi
gurati
on
1. Enable synchronous Ethernet and IEEE 1588v2 for each interface.
2. Configure the priority of imported clock sources for the NNI.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
22
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Solution 1: Native IP VRF Static Route
Access
About This Chapter
Native IP VRF static route access is applicable to small-sized networks, and mainly adopts the
Native IP service solution. In this solution, management plane packets are transmitted through
public network static routes, static routes are created between ATN 905 devices and access
devices in a macro base station, and meanwhile, VRF instances are configured to isolate services
of different carriers.
3.1 Scenario Introduction
This section gives a brief introduction about scenarios, including overview, configuration
roadmap, and data planning.
3.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
3.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
3.4 Deploying the Management Plane
The management plane is an exclusive logical channel that is used to transmit management
packets between NEs on an ATN network. Logical channels of the management plane and other
planes, such as the service plane, are separated, so devices can still be managed when the other
planes become abnormal.
3.5 Deploying VRF Lite Services
This topic describes how to deploy VRF Lite services.
3.6 Deploying Static Routes
Static routes, instead of dynamic routes, are sufficient for a simple network to function.
3.7 Deploying QoS
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
23
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
3.8 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
24
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
3.1 Scenario Introduction
This section gives a brief introduction about scenarios, including overview, configuration
roadmap, and data planning.
Overview
Solution 1: Native IP VRF static route access (native IP + public network static
management plane + static route + VRF access)
Figure 3-1 Example network of Native IP VRF static route access
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
VRF2
VRF1
Static route
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
RNC
main interface
Dot1q sub-interface
public network
management plane
VRF1 service flow
VRF2 service flow
25
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Table 3-1 Solution information
Solution Feature
Applicable
Scenario
Solution
Advantage
Solution
Constraint
l Service
configurations
for small-cell
base stations:
Native IP
1. Scenario in which
the carrier
solution on the
macro base
station side
adopts the Layer
3 access solution
1. The
configurations
are very simple
and easy to
understand. Basic
features are
applied to this
solution, and
dynamic routing
protocols, for
example, the
Interior Gateway
Protocol (IGP),
are not included
in this solution.
1. This solution is
not applicable to
large-sized
networks.
l Management
plane:
Public network
static routes
l IP route:
Static routes
l Native IP access:
VRF access
2. Small-sized
network
3. Small-cell base
station providing
access for
multiple wireless
carriers (Services
of different
wireless carriers
are isolated from
each other.)
4. Huawei IPRAN
products or the
third-party NEs
deployed in the
upstream
direction of the
macro base
station
2. VRF instances
are created for
service isolation.
Wireless devices
are insensible to
the VRF
instances. The
VRF instances
are created on
transmission
equipment to
isolate services of
different wireless
users.
2. This solution is of
poor
expansibility.
Specifically, if
the service IP
address of the
small-cell base
station changes,
the static routes
configured on the
backhaul devices
need to be
changed
accordingly.
Configuration Roadmap
l
Configure a management plane (based on public network static routes) between the ATN
905 and the CSG in a macro base station.
Use dot1p sub-interfaces to create VRF-instance-based IP connections between the ATN
905 and the CSG in a macro base station.
NOTE
1. When services need to be isolated at station access devices, create multiple VRFs on the ATN 905
and CSG devices so that different services use their own VRFs. The VRFs must be the same as those
configured on the macro base station.
2. When services do not need to be isolated at station access devices, create and configure only one VRF
on the ATN 905 and CSG devices so that different services use the same VRF.
Issue 03 (2013-11-22)
Hop by hop configure static routes from the ATN 905 and the CSG in a macro base station
to the small-cell base station and the RNC. Configure static routes between ATN 905 and
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
26
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
small-cell base stations that are directly connected to it, between ATN 905 and its
downstream ATN 905, and between ATN 905 and small-cell base stations that are directly
connected to the downstream ATN 905.
l
Deploy simple traffic classification (STC) on the ATN 905.
Deploy Synchronous Ethernet (SyncE) on the ATN 905 to implement frequency
synchronization; deploy IEEE 1588v2 to implement time synchronization.
Data Planning
Item
Planning Guidelines
Basic configuration
parameters:
You are advised to configure the basic configuration parameters
except NE name in the centralized manner based on the entire
network. In this way, these basic configuration parameters are
planned once for all.
l NE name
l User login parameter
l SNMP
l AAA
Small-cell base station
data:
l Voice services IP
address
l Data services IP
address
1. Different VRF instances need to be configured to isolate
services of different wireless carriers. VRF instances are
planned by wireless carriers.
2. A service IP address pool (32-bit mask) needs to be planned.
3. A management IP address pool (32-bit mask) needs to be
planned.
l VRF
ATN 905 data:
1. A service IP address pool (32-bit mask) needs to be planned.
l Management IP
address
2. An IP address pool of links that connect small-cell base
stations to the ATN 905 needs to be planned.
l IP address of the link
that connects the
small-cell base station
to the ATN 905
3. Each AC port of the ATN 905 needs to be added into the
related VRF instance. The dot1q sub-interfaces between the
backhaul devices are bound to different VRF interfaces to
transmit packets hop by hop.
l VRF
Static route:
l Destination IP
address
l Next-hop IP address
1. Static routes from the ATN 905 to the small-cell base station
need to be configured.
2. Static routes from the ATN 905 to the downstream ATN 905
and small-cell base station need to be configured.
3. The default route from the ATN 905 to the RNC needs to be
configured.
4. Static routes are imported into the BGP area configured on the
backhaul device in a macro device.
QoS
Issue 03 (2013-11-22)
STC is deployed on each service interface of the ATN 905.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
27
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Item
Planning Guidelines
Clock
SyncE and 1588v2 functions are enabled on the ATN 905 so that
the ATN 905 traces the clock and time of the upstream device
and transmits the clock signals to base stations.
3.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
3.2.1 Logging In to the ATN 905 by Using SSH
This section describes how to log in to the ATN 905 by using SSH. SSH is a secure remote login
protocol developed based on the traditional Telnet protocol. Compared with Telnet, SSH is
greatly improved in terms of the authentication mode and data transmission security.
Figure 3-2 shows the networking diagram for logging in to the ATN 905 by using SSH.
Figure 3-2 Networking diagram for logging in to the ATN 905 by using SSH
network
SSH Client
SSH Server
Prerequisite
l
The ATN 905 is running properly.
The ATN 905 has been logged in using the console interface and an IP address for each
interface has been configured on the ATN 905.
A direct or reachable route exists between the SSH client and the ATN 905.
NOTE
Perform the following configurations on the ATN 905 that serves as the SSH server. This section describes only
the SSH login by using the PuTTY program.
Procedure
Step 1 As shown in the following figure, set the IP address of the ATN 905 to 192.168.1.1 and the login
protocol to SSH.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
28
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The IP address of the
management network interface Ethernet0/0/0 (the console interface) is 129.0.0.1. If the ATN has accessed
the network when it is powered on for the first time, its IP address 129.0.0.1 will be automatically changed
to the IP address that DHCP obtains during the startup.
Figure 3-3 Login by using the PuTTY program
Step 2 Enter the user name root and the password Changeme_123.
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The user name and
password are root and Changeme_123 respectively. After logging in to the ATN, change the default
password in time.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
29
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Figure 3-4 Login using the PuTTY program
----End
3.2.2 Logging In to the ATN 905 by Using the Console Interface
This section describes how to use the HyperTerminal in Windows on the PC to log in to the
ATN 905 after setting up a local configuration environment with the console interface.
Context
Figure 3-5 shows the networking diagram for logging in to the NE80E/40E by using the console
interface.
Figure 3-5 Networking diagram for logging in to the ATN 905 by using the console interface
PC
ATN
Prerequisite
l
The ATN 905 is running properly.
The PC is connected to the ATN 905 through an asynchronous interface.
Installing terminal emulation program on the PC (such as Windows XP HyperTerminal)
NOTE
Perform the following configurations on the HyperTerminal on the PC.
The console port applies the non-standard serial port communication cable sequence. For more information, see
ATN 905Multi-service Access Equipment Installation Guide.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
30
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Procedure
Step 1 Use a serial cable to connect the serial interface on the PC and the console interface on the ATN
905.
For more information about the console interface, see the ATN 905Multi-service Access
EquipmentHardware Description.
Step 2 Start the HyperTerminal on the PC.
Choose Start > Programs > Accessories > Communications to start the HyperTerminal in
Windows.
Step 3 Set up a connection.
As shown in Figure 3-6, enter the name of the new connection in the Name text box, and select
an icon. Then, click OK.
Figure 3-6 Setting up a connection
Step 4 Set a connection port.
In the Connect To dialog box shown in Figure 3-7, select a port from the drop-down list box
of Connect using according to the port actually used on the PC or terminal. Then, click OK.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
31
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Figure 3-7 Setting a connection port
Step 5 Set communication parameters.
When the COM1 Properties dialog box is displayed as shown in Figure 3-8, set the COM1
properties according to the description in Figure 3-8 or by clicking Restore Defaults.
NOTE
l Setting the COM1 properties according to the description in Figure 3-8 and setting them by clicking
Restore Defaults have the same effect. The default settings of the console interface will be used.
l When you log in to the ATN 905 by using the console interface, ensure that the COM1 properties on
the HyperTerminal are consistent with the interface attribute settings on the ATN 905. Otherwise, the
login will fail. This means that if default settings are not used for the interface attributes on the ATN
905, the COM1 properties on the HyperTerminal must be changed to be consistent with the interface
attribute settings on the ATN 905.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
32
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Figure 3-8 Setting communication parameters
----End
Commissioning Result
After the preceding configurations are complete, press Enter. An initial password is required
for the first login. Set an authentication password. The system automatically saves the set
password.
An initial password is required for the first login via the console.
Set a password and keep it safe! Otherwise you will not be able to login via the
console.
Please configure the login password (6-16)
Enter Password:
Confirm Password:
If the login fails, click Disconnect and then Call. If the login still fails, repeat Step 1 to check
whether the parameters or physical connections are correct. If they are correct, log in to the ATN
905 again.
3.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
33
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
3.3.1 Configuring an NE Name
If multiple devices on a network need to be managed, set equipment names to identify each
device.
Data Planning
An NE name consists of the site name, device model, and device number. Each NE is named in
the format of AA-BB-CC. The following provides the meaning of the letters.
l
AA: device model, for example, ATN 910 or ATN 905
BB: site name, for example, SmallCellSiteA
CC: device number, starting from 001
For example, ATN905-SmallCellSiteA-001 refers to an ATN 905 numbered 001 at site
SmallCellSiteA.
Parameter
Value
Description
sysname
ATN905SmallCellSiteA-001
Indicates the NE name.
NOTE
All the NEs involved in this document are named as shown in the following figure.
Figure 3-9 NE names
SmallCellSiteB1
SmallCellSiteA1
Macro Cell
Micro/Pico
ATN905SmallCellSiteB-002
Micro/Pico
Micro/Pico
ATN905SmallCellSiteA-001
IPRAN
ATN910MacroCellSite-003
RNC
Micro/Pico
SmallCellSiteA2
SmallCellSiteB2
Configuration Process
l
Configure the name of the NE as ATN905-SmallCellSiteA-001.
sysname ATN905-SmallCellSiteA-001
Configure the name of the NE as ATN905-SmallCellSiteB-002.
sysname ATN905-SmallCellSiteB-002
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
34
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Configure the name of the NE as ATN910-MacroCellSite-003.
sysname ATN910-MacroCellSite-003
3.3.2 Configuring the VTY User Interface
To log in to an ATN device remotely, you can configure the virtual type terminal (VTY) user
interface to ensure equipment security.
Data Planning
To log in to an ATN device in telnet or Secure Shell (SSH) mode, you can configure the VTY
user interface to ensure equipment security. The following parameters are involved: the
maximum number of VTY user interfaces, user authentication mode, user privilege, and VTY
attributes.
l
By setting the maximum number of VTY user interfaces, you can limit the number of users
who can log in to the ATN device concurrently.
By setting the user authentication mode, you can enhance the equipment security. The user
authentication mode can be set to AAA authentication or password authentication.
1.
The AAA authentication mode is based on users, ensuring high security. To log in to
the ATN device, you need to enter the user name and password.
2.
The password authentication mode is based on VTY channels, requiring simple
configuration while ensuring high security. You only need to be create a login
password.
By setting the user privilege, you can differentiate the access rights of different users on
the ATN device to enhance the management security. User privileges are divided into 16
levels, which are numbered 0 to 15. A larger value indicates a higher user privilege.
You can configure the VTY attributes of a VTY user interface, such as the timeout interval
of communication failure for login users. Each VTY attribute on the VTY user interface
has a default value on the ATN device. You can re-configure the terminal attributes as
required.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
user-interface
maximum-vty
15
Sets the maximum number of
users that are allowed to log
in to the NE to 15.
NOTE
When the value of this
parameter is set to 0, no user
(even the NMS user) can log in
to the ATN device through the
VTY user interface.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
35
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Parameter
Value
Description
user-interface
vty 0 14
Indicates that the maximum
number of VTY user
interfaces is the total number
of users that have logged in to
the NE through Telnet or
STelnet.
authentication-mode
aaa
Sets the authentication mode
to AAA authentication for
users that attempt to log in to
the NE.
protocol inbound
ssh
Specifies the login protocol
supported by the VTY user
interface to SSH.
user privilege
level 3
Specifies the command level
to level 3.
idle-timeout
50
Sets the timeout interval of
communication failure for
login users.
Configuration Process
Perform the following configurations on all ATN devices:
1.
Set the maximum number of VTY user interfaces.
user-interface maximum-vty 15 //Set the maximum number of VTY user interfaces
that are allowed to log in to the NE at the same time.
2.
Configure VTY attributes.
user-interface vty 0 14 //Perform configurations for VTY 0 to VTY 14.
protocol inbound ssh
authentication-mode aaa
user privilege level 3
idle-timeout 5 0
3.3.3 Configuring AAA Users
If the user authentication mode is set to AAA authentication on an ATN device, you need to
configure user names and passwords on the ATN device to manage and authenticate users.
Data Planning
If the user authentication mode is set to AAA authentication in an ATN device, a user needs to
keep the login user name and password properly, and uses them to log in to the ATN device.
The levels of commands that can be used by users logging in to an ATN device concurrently are
determined by the privileges of these users in the AAA configuration.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
36
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
aaa
Enters the AAA view to
create a user, set a user level,
or configure an
authentication scheme, an
authorization scheme, an
accounting scheme, or a
domain, so that the NE
authenticates users.
local-user XXX
password cipher XXX
USER01
Adds a local user USER01.
local-user level
Sets the user level for the
local user. The system
manages commands by
command level. A user can
use only the commands
whose levels are lower than
or equal to the user level.
local-user xxx
service-type xxx
USER01
Sets the access type of local
users to SSH.
Hello@*#123
ssh
Configuration Process
Perform the following configurations on all ATN devices:
aaa
local-user USER01 password cipher Hello@*#123 //Add a local uer (USER01) and set
the password.
local-user USER01 level 3 //Set the user level of the local user.
local-user USER01 service-type ssh //Set the access type for the user.
NOTE
Requirements on user names and passwords for ATN products are as follows:
l A local user name contains 1 to 253 characters.
l A password must contain eight characters at least.
l A password must contain digits, upper-case and lower-case letters, and special characters, excluding
question marks (?) and spaces.
l The password cannot be the same as the user name or the user name in reverse order.
3.3.4 Configuring the SNMP
After the Simple Network Management Protocol (SNMP) is configured, the NMS can monitor
and manage NEs.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
37
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Data Planning
The SNMP is a standard network management protocol widely used on TCP/IP networks. The
NMS can manage NEs using the SNMP. Specifically, the SNMP defines several device
management operations that can be performed by the NMS and alarms that can be automatically
sent to the NMS when the ATN equipment is faulty. The NMS uses the management information
base (MIB) to identify and manage devices. The SNMP versions include SNMPv1, SNMPv2c,
and SNMPv3, which are all supported by the ATN 905.
The Link Layer Discovery Protocol (LLDP) is a Layer 2 discovery protocol defined in 802.1ab.
When the ATN and its neighbors are all enabled with LLDP, the ATN notifies the neighbors of
its status and obtains the status of the neighbors through LLDP packets. The NMS then can get
information about Layer 2 connection of the ATN. In this manner, the NMS can analyze the
network topology.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Table 3-2 SNMP parameters
Issue 03 (2013-11-22)
Parameter
Value
Description
snmp-agent
Enables the SNMP agent
function. By default, the
SNMP agent function is
disabled.
snmp-agent sys-info
version
all
Configures the system to
adopt all the SNMP versions,
namely, SNMPv1,
SNMPv2c, and SNMPv3.
snmp-agent mib-view
included iso-view
iso
Includes the iso subtree in the
SNMP MIB view.
snmp-agent
community read
cipher
Huawei123!
Sets a read community name.
The NMS can access a device
only when the community
name set on the NMS is the
same as that set on the device.
snmp-agent
community write
cipher
Huawei@123
snmp-agent trap
enable
mib-view iso-view
mib-view iso-view
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Sets a write community
name. The NMS can access a
device only when the
community name set on the
NMS is the same as that set
on the device.
Enables all traps on a device.
38
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Parameter
Value
Description
snmp-agent trap
source
LoopBack0
Configures the LoopBack0
interface as the source
interface that sends trap
messages.
snmp-agent targethost trap
address udp-domain
20.20.20.20
Allows the SNMP agent to
send SNMP trap messages to
the Huawei NMS at
20.20.20.20.
params securityname
Huawei@123 v2c privatenetmanager ext-vb
snmp-agent trap
enable feature-name
lldp
Enables the LLDP trap
function.
snmp-agent extend
error-code
enable
Enables the extended error
code function.
lldp enable
Enables the LLDP function.
Application Process
Perform the following configurations on all ATN devices:
snmp-agent
snmp-agent sys-info version all //Enable SNMP of all versions for the system.
snmp-agent mib-view included iso-view iso //Include the iso subtree SNMP MIB
view.
snmp-agent community read cipher Huawei123! mib-view iso-view
snmp-agent community write cipher Huawei@123 mib-view iso-view //Set the read and
write permissions for the write attributes. When the read entity name and write
entity name are the same, the write attribute command will override the read
attribute command.
snmp-agent trap enable
snmp-agent target-host trap address udp-domain 20.20.20.20 params securityname
Huawei@123 v2c private-netmanager ext-vb //When the management plane is deployed
on public network routes, SNMP trap messages can be sent to the U2000 at management
IP address 20.20.20.20 using entity name Huawei@123. If an NMS provided by Huawei
is used, configure private-netmanager and ext-vb.
snmp-agent trap source LoopBack0 //Set the source interface for trap messages.
snmp-agent trap enable feature-name lldp
snmp-agent extend error-code enable
lldp enable
3.4 Deploying the Management Plane
The management plane is an exclusive logical channel that is used to transmit management
packets between NEs on an ATN network. Logical channels of the management plane and other
planes, such as the service plane, are separated, so devices can still be managed when the other
planes become abnormal.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
39
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
3.4.1 Configuration Roadmap
This topic describes the configuration roadmap for the management plane.
Traditional management and service packets are closely coupled, making equipment
management more and more complex and costly. Therefore, it is more and more important to
separate the management and service planes. A user operates and manages devices using the
management plane and deploys services using other planes, such as the service plane. That is,
the logical channels of the management plane and other planes are separated. When the
management plane becomes abnormal, other planes can still be used; when other planes become
abnormal, devices can still be managed.
The configuration roadmap is as follows:
l
Establish a management plane between the ATN 905 and the CSG based on public network
static routes.
3.4.2 Data Planning
This topic describes data planning for the management plane configuration.
Data Planning
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values and precautions in this example are for reference only.
Figure 3-10 Management plane configuration diagram
GE0/2/0.1 dot1q 1 192.168.1.21/30
Macro Cell
GE0/2/1.1 dot1q 1
192.168.1.9/30
GE0/2/1.1 dot1q 1
192.168.1.10/30
Loopback0
128.4.11.11/32
IPRAN
GE0/2/0
GE0/2/0
Loopback0
128.4.12.12/32
Loopback0
128.4.13.13/32
RNC/SGW
GE0/2/0.1 dot1q 1 192.168.1.22/30
Table 3-3 Interface planning table
NE Name
Interface
IP Address
VPN
ATN905SmallCellSiteA-001
Loopback0
128.4.11.11 32
GigabitEthernet
0/2/1.1
192.168.1.9 30
vlan-type dot1q 1
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
40
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NE Name
Interface
IP Address
VPN
ATN905SmallCellSiteB-002
Loopback0
128.4.12.12 32
GigabitEthernet
0/2/0.1
192.168.1.21 30
192.168.1.10 30
Loopback0
128.4.13.13 32
GigabitEthernet0/2/0.
1
192.168.1.22 30
vlan-type dot1q 1
GigabitEthernet
0/2/1.1
vlan-type dot1q 1
ATN910MacroCellSite-003
vlan-type dot1q 1
3.4.3 Configuring the Management Plane
This topic describes how to configure the management plane.
Configuring ATN905-SmallCellSiteA-001
interface GigabitEthernet0/2/1.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.9 30
Configuring ATN905-SmallCellSiteB-002
interface GigabitEthernet0/2/0.1
description ToNext905
vlan-type dot1q 1
ip address 192.168.1.10 30
interface GigabitEthernet0/2/1.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.21 30
Configuring ATN910-MacroCellSite-003
interface GigabitEthernet0/2/0.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.22 30
3.5 Deploying VRF Lite Services
This topic describes how to deploy VRF Lite services.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
41
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
3.5.1 Configuration Roadmap
This topic describes the configuration roadmap for local VPN routing and forwarding (VRF)
instances.
Usually multiple users share a device. When a user wants to keep the internal network topology
and address allocation plan from other users, network addresses and routing information of
different users need to be separated to ensure security. Logically, each PE can be divided into
multiple virtual routers, that is, multiple VRF instances. Each VRF instance corresponds to a
VPN and has its own routing table, forwarding table, and corresponding interfaces. In this
manner, a PE shared by multiple VPNs is simulated as multiple exclusive PEs and the routing
information exchanged between the PE and CE is related to a specific VPN. In this manner,
VPN routes are separated.
Although VRF instances are usually used with Multiprotocol Label Switching (MPLS), VRF
instances can be used alone. VRF Lite is a typical example. VRF Lite indicates that VRF
instances are supported on the CE. The following provides an example:
Three departments of an enterprise branch are required to be isolated from each other and each
department is connected to the PE through a CE. That is, the enterprise branch requires 3 egress
routers and 3 links leading to the PE, and the PE needs to provide 3 interfaces for the enterprise
branch. In this case, port and link resources are wasted and costs increase. To resolve this
problem, VRF Lite is introduced. That is, VRF instances are configured on the CE. The following
figure shows the networking mode. The enterprise branch needs only 1 CE to connect to the PE,
VRF instances are configured on the CE, and the CE interfaces for the 3 departments are bound
to VRF instances. In addition, the CE connects to the PE through only 1 physical link and
subinterfaces of the CE interface are bound to VRF instances. In this manner, corresponding
VRF instances are logically connected on the CE and PE, so the PE and CE can run a routing
protocol in each VRF instance to exchange VPN routes.
Figure 3-11 L3VPN configuration roadmap
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
VRF2
VRF1
RNC
Main interface
Dot1q sub-interface
VRF1 service flow
VRF2 service flow
The preceding figure shows how to configure VRF instances. The configuration roadmap is as
follows:
l
Issue 03 (2013-11-22)
Use different VPNs to carry data flows of different users and bind AC interfaces on the
ATN 905 to VRF instances.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
42
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NOTE
1. When services need to be isolated at station access devices, create multiple VRFs on the ATN 905
and CSG devices so that different services use their own VRFs. The VRFs must be the same as those
configured on the macro base station.
2. When services do not need to be isolated at station access devices, create and configure only one VRF
on the ATN 905 and CSG devices so that different services use the same VRF.
Configure dotlq subinterfaces for the interfaces connecting the ATN 905 devices and the
CSG and bind these subinterfaces to VRF instances.
3.5.2 Data Planning
This topic describes data planning required for service deployment.
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The following
recommended values in this example are only for reference.
Figure 3-12 Data planning for service deployment
GE0/2/1.2 172.21.1.9/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.9/30 dot1q 3 VRF2
10.182.1.4/32(VRF2)
10.224.1.4/32(VRF2)
10.182.1.1/32(VRF1)
10.224.1.1/32(VRF1)
GE0/2/0.2 172.21.1.21/30 dot1q 2 VRF1
GE0/2/0.3 192.168.1.21/30 dot1q 3 VRF2
Macro Cell
192.168.1.18
172.21.1.6
172.21.1.5
GE0/2/2
192.168.1.17
GE0/2/2
GE0/2/0
GE0/2/1
GE0/2/1
192.168.1.1
GE0/2/3
192.168.1.2
IPRAN
GE0/2/0
GE0/2/3
172.21.1.13
RNC/SGW
172.21.1.14
GE0/2/1.2 172.21.1.10/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.10/30 dot1q 3 VRF2
10.182.1.2/32(VRF2)
10.224.1.2/32(VRF2)
GE0/2/0.2 172.21.1.22/30 dot1q 2 VRF1
GE0/2/0.3 192.168.1.22/30 dot1q 3 VRF2
10.182.1.3/32(VRF1)
10.224.1.3/32(VRF1)
Table 3-4 Network segment planning
Issue 03 (2013-11-22)
Network Segment
Remarks
10.182.1.0/24
IP address of a small-cell wireless base
station for voice services
10.224.1.0/24
IP address of a small-cell wireless base
station for data services
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
43
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Network Segment
Remarks
172.21.1.0/24(VRF1)
IP address of the access link for all small-cell
base stations connected to one macro base
station.
192.168.1.0/24(VRF2)
IP address of the access link for all small-cell
base stations connected to one macro base
station.
Table 3-5 Interface planning
NE Name
NE
Name
Interface
IP Address
VPN
Remarks
SmallCellSi
teA
SmallC
ellSiteA
1
loopback0
10.182.1.1/32
VRF1
IP address of
NE
SmallCellSite
A1 for voice
services
loopback1
10.224.1.1/32
VRF1
IP address of
NE
SmallCellSite
A1 for data
services
loopback0
10.182.1.2/32
VRF2
IP address of
NE
SmallCellSite
A2 for voice
services
loopback1
10.224.1.2/32
VRF2
IP address of
NE
SmallCellSite
A2 for data
services
GigabitEth
ernet
0/2/1.2
172.21.1.9/30
VRF1
NNI on a
backhaul
device
192.168.1.9/30
VRF2
NNI on a
backhaul
device
SmallC
ellSiteA
2
ATN90
5SmallC
ellSiteA
-001
vlan-type
dot1q 2
GigabitEth
ernet
0/2/1.3
vlan-type
dot1q 3
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
44
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
SmallCellSi
teB
NE
Name
SmallC
ellSiteB
1
SmallC
ellSiteB
2
ATN90
5SmallC
ellSiteB
-002
3 Solution 1: Native IP VRF Static Route Access
Interface
IP Address
VPN
Remarks
GigabitEth
ernet 0/2/2
172.21.1.5/30
VRF1
To NE
SmallCellSite
A1
GigabitEth
ernet 0/2/3
192.168.1.1/30
VRF2
To NE
SmallCellSite
A2
loopback0
10.182.1.4/32
VRF2
IP address of
NE
SmallCellSite
B1 for voice
services
loopback1
10.224.1.4/32
VRF2
IP address of
NE
SmallCellSite
B1 for data
services
loopback0
10.182.1.3/32
VRF1
IP address of
NE
SmallCellSite
B2 for voice
services
loopback1
10.224.1.3/32
VRF1
IP address of
NE
SmallCellSite
B2 for data
services
GigabitEth
ernet
0/2/0.2
172.21.1.21/30
VRF1
To Next905
192.168.1.21/3
0
VRF2
To Next905
172.21.1.10/30
VRF1
NNI on a
backhaul
device
vlan-type
dot1q 2
GigabitEth
ernet
0/2/0.3
vlan-type
dot1q 3
GigabitEth
ernet
0/2/1.2
vlan-type
dot1q 2
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
45
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
NE
Name
3 Solution 1: Native IP VRF Static Route Access
Interface
IP Address
VPN
Remarks
GigabitEth
ernet
0/2/1.3
192.168.1.10/3
0
VRF2
NNI on a
backhaul
device
GigabitEth
ernet 0/2/2
192.168.1.17/3
0
VRF2
To NE
SmallCellSite
B1
GigabitEth
ernet 0/2/3
172.21.1.13/30
VRF1
To NE
SmallCellSite
B2
GE0/2/0.2
172.21.1.22/30
VRF1
To Next905
192.168.1.22/3
0
VRF2
To Next905
vlan-type
dot1q 3
MacroCellS
ite
ATN91
0MacroC
ellSite-0
03
vlan-type
dot1q 2
GE0/2/0.3
vlan-type
dot1q 3
Table 3-6 VRF data planning
NE
VPN
Instance
Name
RD
Remarks
ATN905SmallCellSiteA-001
VRF1
100:1
VRF2
100:2
Isolates base station data, and
adds each AC port of ATN 905 to
the specific VRF.
ATN905SmallCellSiteB-002
VRF1
100:1
VRF2
100:2
ATN910MacroCellSite-003
VRF1
200:1
VRF2
200:2
3.5.3 Configuring VRF Lite Services
This topic describes how to configure VRF Lite to carry services.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
46
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Configuring ATN905-SmallCellSiteA-001
1.
Create a VRF instance.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 100:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 100:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/1.2
description NNI
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.9 30
interface GigabitEthernet0/2/1.3
description NNI
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.9 30
interface GigabitEthernet0/2/2
description To SmallCellSiteA1
ip binding vpn-instance VRF1
ip address 172.21.1.5 30
interface GigabitEthernet0/2/3
description To SmallCellSiteA2
ip binding vpn-instance VRF2
ip address 192.168.1.1 30
Configuring ATN905-SmallCellSiteB-002
1.
Create a VRF instance.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 100:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 100:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/0.2
description To Next905
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.21 30
interface GigabitEthernet0/2/0.3
description To Next905
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.21 30
interface GigabitEthernet0/2/1.2
description To SmallCellSite
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.10 30
interface GigabitEthernet0/2/1.3
description To SmallCellSite
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.10 30
interface GigabitEthernet0/2/2
description To SmallCellSiteB1
ip binding vpn-instance VRF2
ip address 192.168.1.17 30
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
47
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
interface GigabitEthernet0/2/3
description To SmallCellSiteB2
ip binding vpn-instance VRF1
ip address 172.21.1.13 30
Configuring ATN910-MacroCellSite-003
1.
Create a VRF instance.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 200:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 200:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/0.2
description NNI
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.22 30
interface GigabitEthernet0/2/0.3
description NNI
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.22 30
3.6 Deploying Static Routes
Static routes, instead of dynamic routes, are sufficient for a simple network to function.
3.6.1 Configuration Roadmap
This topic describes the configuration roadmap for service plane static routes.
Static routes refer to routes that must be manually configured. Static routes are easy to be
configured and have low requirements on the system. On a network with a simple topology,
configuring only static routes allows the network to work properly. However, when the network
undergoes a fault or the network topology changes, static routes will not change automatically
but must be changed by users manually.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
48
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Figure 3-13 Static route configuration diagram
Micro/Pico
Macro Cell
IPRAN
CSG
Micro/Pico
NativeIP
RNC
Configure static routes to
downstream ATN 905 devices, and
to small-cell base stations that are
directly connected to the
downstream ATN 905 devices
Static route
The preceding figure shows how to configure service plane static routes. The configuration
roadmap is as follows:
l
Configure static routes between the ATN 905 and small-cell base stations that are directly
connected to it.
On the ATN 905, configure a static route leading to the downstream ATN 905 and another
one leading to the small-cell base station that is directly connected to the downstream ATN
905. In other words, configure a static route from the ATN905-SmallCellSiteB-002 NE to
the ATN905-SmallCellSiteA-001 NE and configure a static route from the ATN905SmallCellSiteA-001 NE to its connected small-cell base station.
Configure a default route in the upstream direction of the ATN 905.
On the CSG, configure static routes to each small-cell base station.
3.6.2 Data Planning
This topic describes data planning for static route configuration.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
49
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Figure 3-14 Static route configuration diagram
GE0/2/1.2 172.21.1.9/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.9/30 dot1q 3 VRF2
10.182.1.4 32(VRF2)
10.224.1.4 32(VRF2)
10.182.1.1 32(VRF1)
10.224.1.132(VRF1)
GE0/2/0.2 172.21.1.10/30 dot1q 2 VRF1
Configure a GE0/2/0.3 192.168.1.10/30 dot1q 3 VRF2
default route in
the upstream
Macro Cell
direction
192.168.1.18
172.21.1.6
172.21.1.5
GE0/2/2
192.168.1.17
GE0/2/2
GE0/2/1
GE0/2/0
GE0/2/1
192.168.1.1
GE0/2/3
192.168.1.2
GE0/2/0
GE0/2/3
172.21.1.13
Configure a default route
in the upstream direction
RNC/SGW
172.21.1.14
GE0/2/1.2 172.21.1.21/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.21/30 dot1q 3 VRF2
10.182.1.2 32(VRF2)
10.224.1.2 32(VRF2)
IPRAN
GE0/2/0.2 172.21.1.22/30 dot1q 2 VRF1
GE0/2/0.3 192.168.1.22/30 dot1q 3 VRF2
10.182.1.3 32(VRF1)
10.224.1.3 32(VRF1)
Table 3-7 Interface planning table
Issue 03 (2013-11-22)
NE Name
Destination IP
Address
Next Hop
VPN
Remarks
ATN905SmallCellSite
A-001
10.182.1.1/32
172.21.1.6
VRF1
IP address of NE
SmallCellSiteA
1 for voice
services
10.224.1.1/32
172.21.1.6
VRF1
IP address of NE
SmallCellSiteA
1 for data
services
10.182.1.2/32
192.168.1.2
VRF2
IP address of NE
SmallCellSiteA
2 for voice
services
10.224.1.2/32
192.168.1.2
VRF2
IP address of NE
SmallCellSiteA
2 for data
services
0.0.0.0
172.21.1.21
VRF1
VRF1-based
default upstream
route
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
50
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
ATN905SmallCellSite
B-002
Issue 03 (2013-11-22)
3 Solution 1: Native IP VRF Static Route Access
Destination IP
Address
Next Hop
VPN
Remarks
0.0.0.0
192.168.1.21
VRF2
VRF2-based
default upstream
route
10.182.1.3/32
172.21.1.18
VRF1
IP address of NE
SmallCellSiteB2
for voice
services
10.224.1.3/32
172.21.1.18
VRF1
IP address of NE
SmallCellSiteB2
for data services
10.182.1.4/32
192.168.1.14
VRF2
IP address of NE
SmallCellSiteB1
for voice
services
10.224.1.4/32
192.168.1.14
VRF2
IP address of NE
SmallCellSiteB1
for data services
10.182.1.1/32
172.21.1.9
VRF1
IP address of NE
SmallCellSiteA
1 for voice
services
10.224.1.1/32
172.21.1.9
VRF1
IP address of NE
SmallCellSiteA
1 for data
services
10.182.1.2/32
192.168.1.9
VRF2
IP address of NE
SmallCellSiteA
2 for voice
services
10.224.1.2/32
192.168.1.9
VRF2
IP address of NE
SmallCellSiteA
2 for data
services
0.0.0.0
172.21.1.22
VRF1
VRF1-based
default upstream
route
0.0.0.0
192.168.1.22
VRF2
VRF2-based
default upstream
route
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
51
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NE Name
Destination IP
Address
Next Hop
VPN
Remarks
ATN910MacroCellSit
e-003
10.182.1.3/32
172.21.1.21
VRF1
IP address of NE
SmallCellSiteB2
for voice
services
10.224.1.3/32
172.21.1.21
VRF1
IP address of NE
SmallCellSiteB2
for data services
10.182.1.4/32
192.168.1.21
VRF2
IP address of NE
SmallCellSiteB1
for voice
services
10.224.1.4/32
192.168.1.21
VRF2
IP address of NE
SmallCellSiteB1
for data services
10.182.1.1/32
172.21.1.21
VRF1
IP address of NE
SmallCellSiteA
1 for voice
services
10.224.1.1/32
172.21.1.21
VRF1
IP address of NE
SmallCellSiteA
1 for data
services
10.182.1.2/32
192.168.1.21
VRF2
IP address of NE
SmallCellSiteA
2 for voice
services
10.224.1.2/32
192.168.1.21
VRF2
IP address of NE
SmalloCellSite
A2 for carrying
data services
3.6.3 Configuring Static Routes
This topic describes the method of configuring static routes.
Configure NE ATN905-SmallCellSiteA-001
l
Configure static routes to small-cell base stations that are directly connected.
ip route-static vpn-instance VRF1 10.182.1.1 32 172.21.1.6////Sets a static
route with the destination IP address as 10.182.1.1 and the next-hop address
as 172.21.1.6.
ip route-static vpn-instance VRF1 10.224.1.1 32 172.21.1.6
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
52
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
ip route-static vpn-instance VRF2 10.182.1.2 32 192.168.1.2
ip route-static vpn-instance VRF2 10.224.1.2 32 192.168.1.2
Configure a default route in the upstream direction.
ip route-static vpn-instance VRF1 0.0.0.0 0 172.21.1.10
ip route-static vpn-instance VRF2 0.0.0.0 0 192.168.1.10
Configure NE ATN905-SmallCellSiteB-002
l
Configure static routes to small-cell base stations that are directly connected.
ip
ip
ip
ip
vpn-instance
vpn-instance
vpn-instance
vpn-instance
VRF1
VRF1
VRF2
VRF2
10.182.1.3
10.224.1.3
10.182.1.4
10.224.1.4
32
32
32
32
172.21.1.14
172.21.1.14
192.168.1.14
192.168.1.14
Configure static routes to the small-cell base stations that the downstream ATN 905 directly
connected.
ip
ip
ip
ip
route-static
route-static
route-static
route-static
route-static
route-static
route-static
route-static
vpn-instance
vpn-instance
vpn-instance
vpn-instance
VRF1
VRF1
VRF2
VRF2
10.182.1.1
10.224.1.1
10.182.1.2
10.224.1.2
32
32
32
32
172.21.1.9
172.21.1.9
192.168.1.9
192.168.1.9
Configure a default route in the upstream direction.
ip route-static vpn-instance VRF1 0.0.0.0 0 172.21.1.22
ip route-static vpn-instance VRF2 0.0.0.0 0 192.168.1.22
Configure NE ATN910-MacroCellSite-003
l
Configure static routes to the small-cell base stations that the downstream ATN 905 directly
connected.
ip
ip
ip
ip
ip
ip
ip
ip
route-static
route-static
route-static
route-static
route-static
route-static
route-static
route-static
vpn-instance
vpn-instance
vpn-instance
vpn-instance
vpn-instance
vpn-instance
vpn-instance
vpn-instance
VRF1
VRF1
VRF2
VRF2
VRF1
VRF1
VRF2
VRF2
10.182.1.1
10.224.1.1
10.182.1.2
10.224.1.2
10.182.1.3
10.224.1.3
10.182.1.4
10.224.1.4
32
32
32
32
32
32
32
32
172.21.1.21
172.21.1.21
192.168.1.21
192.168.1.21
172.21.1.21
172.21.1.21
192.168.1.21
192.168.1.21
Configure a route to the private network.
bgp 100
ipv4-family vpn-instance IPRAN1
import-route static//Configures BGP to import static routes.
ipv4-family vpn-instance IPRAN2
import-route static
3.6.4 Checking Static Route Configurations
After completing static route configuration, you can check the configurations.
#Query detailed route information.
l
Run display ip routing-table vpn-instance to query the brief information about the IPv4
route table.
Run display ip routing-table vpn-instance verbose to query the detailed information about
the IPv4 route table.
#Use the Ping command to check the connectivity.
Run the ping command on the access device at a macro base station to verify the connectivity.
The destination address ATN905-SmallCellSiteA-001 is the IP address of the interface
connecting the small-cell base station to the macro base station.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
53
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
[HUAWEI]ping -v -vpn-instance VRF1 172.21.1.5
LSP PING FEC: IPV4 PREFIX 172.21.1.5/30 : 100 data bytes, press
Reply from 172.21.1.5: bytes=100 Sequence=1 time = 4 ms Return
1
Reply from 172.21.1.5: bytes=100 Sequence=2 time = 4 ms Return
1
Reply from 172.21.1.5: bytes=100 Sequence=3 time = 4 ms Return
1
Reply from 172.21.1.5: bytes=100 Sequence=4 time = 4 ms Return
1
Reply from 172.21.1.5: bytes=100 Sequence=5 time = 5 ms Return
1
--- FEC: IPV4 PREFIX 172.21.1.5/32 ping statistics --5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 4/4/5 ms
CTRL_C to break
Code 3, Subcode
Code 3, Subcode
Code 3, Subcode
Code 3, Subcode
Code 3, Subcode
3.7 Deploying QoS
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
3.7.1 Configuring QoS
You can configure simple traffic classification to classify data packets into multiple priorities
or service classes, and therefore to provide differentiated services.
Configuration Roadmap
Traditional IP networks in best-effort mode are mainly used to carry data services, and the service
quality seems insignificant. However, with fast development of IP-oriented Internet services and
emerging of various new services (such as VoIP and VPN services), IP networks have changed
from pure data networks to bearer networks with commercial values. Therefore, IP networks
must ensure the quality of each type of service that they carry. Against this backdrop, quality of
service (QoS) is developed.
The ATN 905 functions as a small-cell base station bearer device or enterprise private line
Ethernet demarcation device (EDD). When configured with simple traffic classification, the
ATN 905 can manage the traffic. Priority mapping based on simple traffic classification indicates
that the priority of the packets on a network is mapped into the packets of another network so
that the packets of the first network can be transmitted on the second network based on the
original or user-defined packet priority. That is, on the ingress, the packets obtain the priority
and color for scheduling on the ATN equipment based on the values of the DSCP and 802.1p
fields. After being scheduled on the ATN equipment, the outgoing packets obtain the values of
the priority fields (such as DSCP and 802.1p) for encapsulation based on the above-mentioned
priority and color. In this manner, during traffic management, packets of different services join
different queues, ensuring differentiated scheduling.
To configure simple traffic classification, do as follows:
l
Issue 03 (2013-11-22)
Bind the default DiffServ domain to service interfaces (including main interfaces and
subinterfaces) of the ATN 905 to configure simple traffic classification.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
54
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
Data Planning
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
trust upstream
default
Bind the DiffServ domain to
an interface.
Application Process
l
For ATN905-SmallCellSiteA-001
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN905-SmallCellSiteB-002
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN910-MacroCellSite-003
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
3.8 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
3.8.1 Configuration Roadmap
Synchronization includes frequency synchronization and phase synchronization. In this solution,
you are advised to configure synchronous Ethernet and IEEE 1588v2 on the ATN 905 to achieve
frequency synchronization and phase synchronization respectively.
To ensure that most services run normally on a current communication network, devices on the
entire network should keep the frequency or phase difference within a permitted range. That is,
synchronization, either frequency synchronization or phase synchronization, must be ensured
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
55
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
on the network. Frequency synchronization (also known as clock synchronization) indicates that
signals retain certain relationships with respect to the phase. That is, the phase difference between
signals is constant. Phase synchronization (also known as time synchronization) indicates that
signals have the same frequency and phase. That is, there is no phase difference between signals.
For example, if two watches always indicate the same time, they are in phase synchronization;
if the two watches always have a constant time difference (such as 6 hours), they are in frequency
synchronization. In the IP RAN scenario, the ATN equipment needs to support frequency or
phase synchronization to meet the requirements of base stations.
Mainstream PSN-based synchronization technologies in the industry include IEEE 1588v2 and
synchronous Ethernet. In this solution, you are advised to configure synchronous Ethernet and
IEEE 1588v2 on the ATN 905 to achieve frequency synchronization and phase synchronization
respectively.
Figure 3-15 Networking diagram for clock deployment
Micro/Pico
Micro/Pico
BITS
GE0/2/2
GE0/2/3
pri 20
GE0/2/1
GE0/2/2
GE0/2/1
pri 20
GE0/2/0 GE0/2/0
ASG
pri 10
RSG
GE0/2/3
Clock Tracking Path
pri n
Priority of a reference clock source at a port
The preceding figure shows how to configure a clock. The configuration roadmap is as follows:
l
Enable synchronous Ethernet and IEEE 1588v2 for the ATN 905, so that the ATN 905 can
track the upstream clock information and time information, and send them to base stations.
3.8.2 Data Planning
This topic describes data planning for clock deployment.
l
For synchronous Ethernet, configure clock signal priorities in the local priority list, and
enable synchronization status message (SSM) control.
NOTE
For synchronous Ethernet clock synchronization, a clock source is selected based on the following
descending order of priority: SSM clock quality, local priority setting, and clock source type.
l The SSM clock quality levels are in the following descending order: primary reference clock (PRC),
SSUA, SSUB, SDH equipment clock (SEC), and DNU. A source for which no quality level is defined,
and a clock source with quality level being DNU, are not be selected during source selection.
l The local priority is configured as follows: The value range is 1 to 255, and a smaller value indicates
a higher priority.
l
Issue 03 (2013-11-22)
For IEEE 1588v2, use the best master clock (BMC) algorithm.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
56
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
NOTE
When the BMC algorithm is used by a 1588v2-enabled device for master clock selection, priority1 of each
candidate time source is compared first, then the clock class, clock accuracy, and priority2. If priority1 of
candidate time sources is the same, the clock class is compared, and so on. The time source with the highest
priority is selected as the master clock.
Table 3-8 Data planning for synchronous Ethernet time synchronization
NE Name
Parameter
Value
Remarks
ATN905SmallCellSiteA-001
Local priority
list
20
Clock output
port
GE0/2/2
Connects to a base station.
ATN905SmallCellSiteB-002
ATN910MacroCellSite-003
GE0/2/3
Table 3-9 Data planning for IEEE 1588v2 time synchronization
NE Name
Parameter
Value
Remarks
ATN905-SmallCellSiteA-001
Port delay
measurement
mechanism
delay
The mechanism is
recommended to be
set consistently
networkwide.
NE type
BC
The networkwide BC
mode is
recommended.
Ring network
asymmetry automeasurement
enable
Automatically adjusts
the length difference
between transmit and
receive fibers when
ring network
protection switching
occurs for restoration.
Clock output port
GE0/2/2
Connects to a base
station.
ATN905-SmallCellSiteB-002
ATN910-MacroCellSite-003
GE0/2/3
3.8.3 Configuring Synchronous Ethernet to Achieve Frequency
Synchronization
To achieve frequency synchronization on a network, use synchronous Ethernet.
Configure NE ATN905-SmallCellSiteA-001
clock ethernet-synchronization enable //Enables global synchronous Ethernet in the
system view.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
57
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
clock ssm-control on //Configures SSM for source selection. By default, SSM is
enabled for an ATN NE.
interface GigabitEthernet0/2/1
clock priority 20//Assigns a clock priority to the interface. This will affect
clock selection in the inbound direction on the local end. A smaller value
indicates a higher priority. Assigning the highest priority to each interface on
the shortest path for clock signal transmission is recommended.
clock synchronization enable//Enables synchronous Ethernet for an interface.
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
Configure NE ATN905-SmallCellSiteB-002
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock priority 20
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
interface GigabitEthernet0/2/3
clock synchronization enable
Configure NE ATN910-MacroCellSite-003
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
3.8.4 Configuring IEEE 1588v2 to Achieve Time Synchronization
After frequency synchronization is achieved on a network using synchronous Ethernet, use IEEE
1588v2 to achieve time synchronization on the network.
Configure NE ATN905-SmallCellSiteA-001
ptp enable //Enables global IEEE 1588v2.
ptp device-type bc //Specifies the BC mode for all devices.
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay //Configures the delay measurement mechanism of a
device as delay which calculates the time difference based on the link delay of the
master and slave clocks.
ptp enable //Enables IEEE 1588v2 for the interface.
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN905-SmallCellSiteB-002
ptp enable
ptp device-type bc
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
58
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
3 Solution 1: Native IP VRF Static Route Access
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN910-MacroCellSite-003
ptp enable
ptp device-type bc
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
59
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Solution 2: Native IP VRF Dynamic Route
Access
About This Chapter
Native IP VRF dynamic route access is applicable to large-sized networks, and mainly adopts
the Native IP service solution. In this solution, management plane packets are transmitted
through DCN private network routes, the Interior Gateway Protocol (IGP) is run between ATN
905 devices and access devices in a macro base station, and meanwhile, VRF instances are
configured to isolate services of different carriers.
4.1 Scenario Introduction
This section gives a brief introduction about scenarios, including overview, configuration
roadmap, and data planning.
4.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
4.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
4.4 Configuring the Management Plane
This topic describes the configuration roadmap for the management plane.
4.5 Deploying VRF Lite Services
This topic describes how to deploy VRF Lite services.
4.6 Deploying the IGP
The Interior Gateway Protocol (IGP) can be deployed using either of the intermediate system
to intermediate system (IS-IS) or the Open Shortest Path First (OSPF) protocol.
4.7 Deploying QoS
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
60
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
4.8 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
61
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
4.1 Scenario Introduction
This section gives a brief introduction about scenarios, including overview, configuration
roadmap, and data planning.
Overview
Solution 2: Native IP VRF dynamic route access (native IP + DCN private network
management + dynamic route + VRF access)
Figure 4-1 Example network of native IP VRF dynamic route access
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
VRF2
VRF1
IGP
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
RNC
main interface
Dot1q sub-interface
DCN management
plane
VRF1 service flow
VRF2 service flow
62
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Table 4-1 Solution information
Solution Feature
Applicable
Scenario
Solution
Advantage
Solution
Constraint
l Service
configurations
for small-cell
base stations:
Native IP
1. Scenario in which
the carrier
solution on the
macro base
station side
adopts the Layer
3 access solution
1. This solution is
applicable to
large-sized
networks.
1. The Interior
Gateway Protocol
(IGP) planning
and maintenance
are required for
this solution.
l Management
plane:
Private network
DCN
l IP route:
IGP route
l Native IP access:
VRF access
2. Different-sized
networks
3. Small-cell base
station providing
access for
multiple wireless
carriers (Services
of different
wireless carriers
are isolated from
each other.)
4. Scenario in which
the network
consists of only
Huawei products
and DCN private
network
management is
used in the
upstream
direction of the
macro base
station
2. This solution
features high
expansibility.
When a new
small-cell base
station is
connected to the
ATN 905, only
the interface
configurations of
the neighbor
backhaul devices
need to be
modified.
2. The network
topology changes
may result in
network flapping.
3. VRF instances
are created for
service isolation.
Wireless devices
are insensible to
VRF instances,
and VLANs and
IP addresses are
planned
independently.
Configuration Roadmap
l
Configure a DCN management plane between the ATN 905 and the macro base station.
NOTE
1. When services need to be isolated at station access devices, create multiple VRFs on the ATN 905
and CSG devices so that different services use their own VRFs. The VRFs must be the same as those
configured on the macro base station.
2. When services do not need to be isolated at station access devices, create and configure only one VRF
on the ATN 905 and CSG devices so that different services use the same VRF.
Issue 03 (2013-11-22)
Use dot1p sub-interfaces to create VRF-instance-based IP connections between the ATN
905 and the backhaul device in a macro base station.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
63
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Configure an independent IGP process for each VRF instance between the ATN 905 and
the backhaul device in a macro base station.
Deploy simple traffic classification (STC) on each service interface.
Deploy Synchronous Ethernet (SyncE) on the ATN 905 to implement frequency
synchronization; deploy IEEE 1588v2 to implement time synchronization.
Data Planning
Item
Planning Guidelines
Basic configuration
parameters:
You are advised to configure the basic configuration parameters
except NE name in the centralized manner based on the entire
network. In this way, these basic configuration parameters are
planned once for all.
l NE name
l User login parameter
l SNMP
l AAA
Small-cell base station
data:
l Voice services IP
address
l Data services IP
address
1. Different VRF instances need to be configured to isolate
services of different wireless carriers. VRF instances are
planned by wireless carriers.
2. A service IP address pool (32-bit mask) needs to be planned.
3. A management IP address pool (32-bit mask) needs to be
planned.
l VRF
ATN 905 data:
1. A service IP address pool (32-bit mask) needs to be planned.
l IP address of the link
that connects the
small-cell base station
to the ATN 905
2. An IP address pool of links that connect small-cell base
stations to the ATN 905 needs to be planned.
l Management IP
address
3. Each AC port of the ATN 905 needs to be added into the
related VRF instance. The dot1q sub-interfaces between the
backhaul devices are bound to different VRF interfaces to
transmit packets hop by hop.
l VRF
Routes
l Static route:
destination IP
address, next-hop IP
address
Issue 03 (2013-11-22)
1. Static routes from the ATN 905 to the logical IP address of
the small-cell base station need to be configured.
2. The default route from the ATN 905 to the RNC needs to be
configured.
l IGP: IGP process
number
3. An independent IGP process needs to be configured for each
VRF instance between the ATN 905 and the backhaul device
in a macro base station. Static routes and direct routes are
imported into the IGP area.
QoS
STC is deployed on each service interface of the ATN 905.
Clock
SyncE and 1588v2 functions are enabled on the ATN 905 so that
the ATN 905 traces the clock and time of the upstream device
and transmits the clock signals to base stations.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
64
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
4.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
4.2.1 Logging In to the ATN by Using SSH
This section describes how to log in to the ATN 905 by using SSH. SSH is a secure remote login
protocol developed based on the traditional Telnet protocol. Compared with Telnet, SSH is
greatly improved in terms of the authentication mode and data transmission security.
Figure 4-2 shows the networking diagram for logging in to the ATN 905 by using SSH.
Figure 4-2 Networking diagram for logging in to the ATN 905 by using SSH
network
SSH Client
SSH Server
Prerequisite
l
The ATN 905 is running properly.
The ATN 905 has been logged in using the console interface and an IP address for each
interface has been configured on the ATN 905.
A direct or reachable route exists between the SSH client and the ATN 905.
NOTE
Perform the following configurations on the ATN 905 that serves as the SSH server. This section describes only
the SSH login by using the PuTTY program.
Procedure
Step 1 As shown in the following figure, set the IP address of the ATN 905 to 192.168.1.1 and the login
protocol to SSH.
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The IP address of the
management network interface Ethernet0/0/0 (the console interface) is 129.0.0.1. If the ATN has accessed
the network when it is powered on for the first time, its IP address 129.0.0.1 will be automatically changed
to the IP address that DHCP obtains during the startup.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
65
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-3 Login by using the PuTTY program
Step 2 Enter the user name root and the password Changeme_123.
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The user name and
password are root and Changeme_123 respectively. After logging in to the ATN, change the default
password in time.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
66
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-4 Login using the PuTTY program
----End
4.2.2 Logging In to the ATN by Using the Console Interface
This section describes how to use the HyperTerminal in Windows on the PC to log in to the
ATN 905 after setting up a local configuration environment with the console interface.
Context
Figure 4-5 shows the networking diagram for logging in to the NE80E/40E by using the console
interface.
Figure 4-5 Networking diagram for logging in to the ATN 905 by using the console interface
PC
ATN
Prerequisite
l
The ATN 905 is running properly.
The PC is connected to the ATN 905 through an asynchronous interface.
Installing terminal emulation program on the PC (such as Windows XP HyperTerminal)
NOTE
Perform the following configurations on the HyperTerminal on the PC.
The console port applies the non-standard serial port communication cable sequence. For more information, see
ATN 905Multi-service Access Equipment Installation Guide.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
67
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Procedure
Step 1 Use a serial cable to connect the serial interface on the PC and the console interface on the ATN
905.
For more information about the console interface, see the ATN 905Multi-service Access
EquipmentHardware Description.
Step 2 Start the HyperTerminal on the PC.
Choose Start > Programs > Accessories > Communications to start the HyperTerminal in
Windows.
Step 3 Set up a connection.
As shown in Figure 4-6, enter the name of the new connection in the Name text box, and select
an icon. Then, click OK.
Figure 4-6 Setting up a connection
Step 4 Set a connection port.
In the Connect To dialog box shown in Figure 4-7, select a port from the drop-down list box
of Connect using according to the port actually used on the PC or terminal. Then, click OK.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
68
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-7 Setting a connection port
Step 5 Set communication parameters.
When the COM1 Properties dialog box is displayed as shown in Figure 4-8, set the COM1
properties according to the description in Figure 4-8 or by clicking Restore Defaults.
NOTE
l Setting the COM1 properties according to the description in Figure 4-8 and setting them by clicking
Restore Defaults have the same effect. The default settings of the console interface will be used.
l When you log in to the ATN 905 by using the console interface, ensure that the COM1 properties on
the HyperTerminal are consistent with the interface attribute settings on the ATN 905. Otherwise, the
login will fail. This means that if default settings are not used for the interface attributes on the ATN
905, the COM1 properties on the HyperTerminal must be changed to be consistent with the interface
attribute settings on the ATN 905.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
69
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-8 Setting communication parameters
----End
Commissioning Result
After the preceding configurations are complete, press Enter. An initial password is required
for the first login. Set an authentication password. The system automatically saves the set
password.
An initial password is required for the first login via the console.
Set a password and keep it safe! Otherwise you will not be able to login via the
console.
Please configure the login password (6-16)
Enter Password:
Confirm Password:
If the login fails, click Disconnect and then Call. If the login still fails, repeat Step 1 to check
whether the parameters or physical connections are correct. If they are correct, log in to the ATN
905 again.
4.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
70
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
4.3.1 Configuring NE Information
If multiple devices on a network need to be managed, set equipment names to identify each
device.
Data Planning
An NE name consists of the site name, device model, and device number. Each NE is named in
the format of AA-BB-CC. The following provides the meaning of the letters.
l
AA: device model, for example, ATN 910 or ATN 905
BB: site name, for example, SmallCellSiteA
CC: device number, starting from 001
For example, ATN905-SmallCellSiteA-001 refers to an ATN 905 numbered 001 at site
SmallCellSiteA.
Parameter
Value
Description
sysname
ATN905SmallCellSiteA-001
Indicates the NE name.
NOTE
All the NEs involved in this document are named as shown in the following figure.
Figure 4-9 NE names
SmallCellSiteB1
SmallCellSiteA1
Macro Cell
Micro/Pico
ATN905SmallCellSiteB-002
Micro/Pico
Micro/Pico
ATN905SmallCellSiteA-001
IPRAN
ATN910MacroCellSite-003
RNC
Micro/Pico
SmallCellSiteA2
SmallCellSiteB2
Configuration Process
l
Configure the name of the NE as ATN905-SmallCellSiteA-001.
sysname ATN905-SmallCellSiteA-001
Configure the name of the NE as ATN905-SmallCellSiteB-002.
sysname ATN905-SmallCellSiteB-002
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
71
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Configure the name of the NE as ATN910-MacroCellSite-003.
sysname ATN910-MacroCellSite-003
4.3.2 Configuring the VTY User Interface
To log in to an ATN device remotely, you can configure the virtual type terminal (VTY) user
interface to ensure equipment security.
Data Planning
To log in to an ATN device in telnet or Secure Shell (SSH) mode, you can configure the VTY
user interface to ensure equipment security. The following parameters are involved: the
maximum number of VTY user interfaces, user authentication mode, user privilege, and VTY
attributes.
l
By setting the maximum number of VTY user interfaces, you can limit the number of users
who can log in to the ATN device concurrently.
By setting the user authentication mode, you can enhance the equipment security. The user
authentication mode can be set to AAA authentication or password authentication.
1.
The AAA authentication mode is based on users, ensuring high security. To log in to
the ATN device, you need to enter the user name and password.
2.
The password authentication mode is based on VTY channels, requiring simple
configuration while ensuring high security. You only need to be create a login
password.
By setting the user privilege, you can differentiate the access rights of different users on
the ATN device to enhance the management security. User privileges are divided into 16
levels, which are numbered 0 to 15. A larger value indicates a higher user privilege.
You can configure the VTY attributes of a VTY user interface, such as the timeout interval
of communication failure for login users. Each VTY attribute on the VTY user interface
has a default value on the ATN device. You can re-configure the terminal attributes as
required.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
user-interface
maximum-vty
15
Sets the maximum number of
users that are allowed to log
in to the NE to 15.
NOTE
When the value of this
parameter is set to 0, no user
(even the NMS user) can log in
to the ATN device through the
VTY user interface.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
72
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Description
user-interface
vty 0 14
Indicates that the maximum
number of VTY user
interfaces is the total number
of users that have logged in to
the NE through Telnet or
STelnet.
authentication-mode
aaa
Sets the authentication mode
to AAA authentication for
users that attempt to log in to
the NE.
protocol inbound
ssh
Specifies the login protocol
supported by the VTY user
interface to SSH.
user privilege
level 3
Specifies the command level
to level 3.
idle-timeout
50
Sets the timeout interval of
communication failure for
login users.
Configuration Process
Perform the following configurations on all ATN devices:
1.
Set the maximum number of VTY user interfaces.
user-interface maximum-vty 15 //Set the maximum number of VTY user interfaces
that are allowed to log in to the NE at the same time.
2.
Configure VTY attributes.
user-interface vty 0 14 //Perform configurations for VTY 0 to VTY 14.
protocol inbound ssh
authentication-mode aaa
user privilege level 3
idle-timeout 5 0
4.3.3 Configuring AAA Users
If the user authentication mode is set to AAA authentication on an ATN device, you need to
configure user names and passwords on the ATN device to manage and authenticate users.
Data Planning
If the user authentication mode is set to AAA authentication in an ATN device, a user needs to
keep the login user name and password properly, and uses them to log in to the ATN device.
The levels of commands that can be used by users logging in to an ATN device concurrently are
determined by the privileges of these users in the AAA configuration.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
73
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
aaa
Enters the AAA view to
create a user, set a user level,
or configure an
authentication scheme, an
authorization scheme, an
accounting scheme, or a
domain, so that the NE
authenticates users.
local-user XXX
password cipher XXX
USER01
Adds a local user USER01.
local-user level
Sets the user level for the
local user. The system
manages commands by
command level. A user can
use only the commands
whose levels are lower than
or equal to the user level.
local-user xxx
service-type xxx
USER01
Sets the access type of local
users to SSH.
Hello@*#123
ssh
Configuration Process
Perform the following configurations on all ATN devices:
aaa
local-user USER01 password cipher Hello@*#123 //Add a local uer (USER01) and set
the password.
local-user USER01 level 3 //Set the user level of the local user.
local-user USER01 service-type ssh //Set the access type for the user.
NOTE
Requirements on user names and passwords for ATN products are as follows:
l A local user name contains 1 to 253 characters.
l A password must contain eight characters at least.
l A password must contain digits, upper-case and lower-case letters, and special characters, excluding
question marks (?) and spaces.
l The password cannot be the same as the user name or the user name in reverse order.
4.3.4 Configuring the SNMP
Simple Network Management Protocol (SNMP) needs to be configured so that devices can be
managed by the network management system (NMS). This topic describes how to configure the
SNMP.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
74
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Data Planning
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The
following recommended values and precautions in this example are only for reference.
Table 4-2 SNMP parameters
Parameter
Value
Description
snmp-agent
The SNMP agent function is
enabled. By default, the
SNMP agent function is
disabled.
snmp-agent sys-info
version
v2c
This parameter indicates the
SNMP version, which is set
to V2C.
snmp-agent mib-view
included iso-view
iso
The SNMP MIB view
contains the iso subtree.
snmp-agent
community read
cipher
Huawei123!
This parameter indicates a
read community name. The
NMS can gain access to a
device only when the
community names set on the
NMS are the same as those
set on the device.
snmp-agent
community write
cipher
Huawei@123
snmp-agent trap
enable
This parameter indicates a
command used to enable all
traps on a device.
snmp-agent trap
source
NNI
This parameter indicates a
command used to configure
the NNI interface as the
source interface that sends
trap messages.
snmp-agent targethost trap
address udp-domain
20.20.20.20
This parameter indicates a
command that allows the
SNMP agent to send SNMP
trap messages to the Huawei
NMS with 20.20.20.20.
mib-view iso-view
mib-view iso-view
params securityname
Huawei@123 v2c privatenetmanager ext-vb
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
This parameter indicates a
write community name. The
NMS can gain access to a
device only when the
community names set on the
NMS are the same as those
set on the device.
75
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Description
snmp-agent trap
enable feature-name
lldp
This parameter indicates a
command used to enable the
Link Layer Discovery
Protocol (LLDP) trap
function.
ftp client-source i
NNI
This parameter indicates a
command used to configure
the NNI interface as the
source interface of the FTP
client.
Configuration Process
Configure the SNMP as follows:
#
snmp-agent
snmp-agent sys-info version all//Configure the system to use SNMP of all versions.
snmp-agent mib-view included iso-view iso//The SNMP MIB view contains the iso
subtree.
snmp-agent community read cipher Huawei123! mib-view iso-view
snmp-agent community write cipher Huawei@123 mib-view iso-view//The write attribute
includes the read-write permission. When the read community name is consistent with
the write community name, the command line of the read attribute will be
overwritten by the command line of the write attribute.
snmp-agent trap enable
snmp-agent target-host trap address udp-domain 20.20.20.20 vpn-instance
__dcn_vpn__ params securityname Huawei@123 v2c private-netmanager ext-vb//When the
management plane traverses a DCN private network channel, SNMP trap messages can be
sent to the IP address 20.20.20.20 of the U2000. In this scenario, the community
name Huawei@123 is used. If the U2000 is used, you are advised to set parameters
private-netmanager and ext-vb.
snmp-agent trap source LoopBack1024//Specify a source interface that sends trap
packets.
snmp-agent trap enable feature-name lldp
4.4 Configuring the Management Plane
This topic describes the configuration roadmap for the management plane.
4.4.1 Configuring the Management Plane
This topic describes the configuration roadmap for the management plane.
Configuration Roadmap
Traditional management and service packets are closely coupled, making equipment
management more and more complex and costly. Therefore, it is more and more important to
separate the management and service planes. A user operates and manages devices using the
management plane and deploys services using other planes, such as the service plane. That is,
the logical channels of the management plane and other planes are separated. When the
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
76
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
management plane becomes abnormal, other planes can still be used; when other planes become
abnormal, devices can still be managed.
The ATN-supported private network DCN, an exclusive logical channel independent from the
control and service planes, is used to transmit management packets between NEs. Currently, an
independent service VPN (the VPN instance is named __dcn_vpn__) is occupied. This VPN is
only used to transit management packets and cannot be occupied by user services. The DCN is
independent from the control plane, which indicates that the logical channel can be automatically
established without extra service control signaling and routes. Therefore, management packets
can be transmitted. The DCN is independent from the service plane, which indicates that the
logical channel is unrelated to services. That is, the logical channel is available no matter whether
services are available. Therefore, after the ATN equipment is powered on, DCN automatically
becomes available and management packets can be transmitted.
The configuration roadmap is as follows:
l
Establish a management plane between the ATN 905 and the CSG based on private network
DCN channels.
NOTE
After DCN is enabled on the ATN equipment, the following configuration is generated by default:
#
interface LoopBack1023
description DCN loopback interface
ip binding vpn-instance __dcn_vpn__
ip address 100.4.12.12 255.255.255.255
#
ospf 65534 vpn-instance __dcn_vpn__
description DCN ospf create by default
opaque-capability enable
hostname
vpn-instance-capability simple
area 0.0.0.0
network 0.0.0.0 255.255.255.255
#
dcn
ne-ip 100.4.12.12 255.255.255.255
Data Planning
When being initialized, each NE on a DCN automatically generates an NE IP address that maps
the default NE ID, diffuses the NE ID and NE IP address through the Open Shortest Path First
(OSPF) protocol, and automatically generates a core routing table that indicates the mapping
between the NE IP and NE IP address. In this manner, NEs can communicate with each other.
That is, management channels can be interconnected without any user operations. However, on
actual networks, some users can re-plan the NE ID and NE IP address as required instead of
using the default ones.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
77
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Remarks
NEID
It is set before the device is
delivered and can be planned
and changed as required.
By default, the NE ID and NE
IP address are associated.
After the NE ID is changed,
the NE IP address will also
change; after the NE IP
address is changed, the NE
ID will not change.
After the NE IP address is
changed, the default
association between the NE
ID and NE IP address no
longer exists. If the NE ID is
changed later, the NE IP
address will not change
accordingly.
It is set before the device is
delivered and can be planned
and changed as required.
NEIP
All NE IP addresses are in the
128.0.0.0/8 network
segment.
Configuration Process
Re-plan the NE ID and NE IP address.
set neid 9a0005//Set the NE ID in the user view.
dcn
ne-ip 128.9.160.5 255.255.255.0//Set the NE IP address in the DCN view.
4.5 Deploying VRF Lite Services
This topic describes how to deploy VRF Lite services.
4.5.1 Configuration Roadmap
This topic describes the configuration roadmap for VPN routing and forwarding (VRF) Lite.
Usually multiple users share a device. When a user wants to keep the internal network topology
and address allocation plan from other users, network addresses and routing information of
different users need to be separated to ensure security. Logically, each PE can be divided into
multiple virtual routers, that is, multiple VRF instances. Each VRF instance corresponds to a
VPN and has its own routing table, forwarding table, and corresponding interfaces. In this
manner, a PE shared by multiple VPNs is simulated as multiple exclusive PEs and the routing
information exchanged between the PE and CE is related to a specific VPN. In this manner,
VPN routes are separated.
Although VRF instances are usually used with Multiprotocol Label Switching (MPLS), VRF
instances can be used alone. VRF Lite is a typical example. VRF Lite indicates that VRF
instances are supported on the CE. The following provides an example:
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
78
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Three departments of an enterprise branch are required to be isolated from each other and each
department is connected to the PE through a CE. That is, the enterprise branch requires 3 egress
routers and 3 links leading to the PE, and the PE needs to provide 3 interfaces for the enterprise
branch. In this case, port and link resources are wasted and costs increase. To resolve this
problem, VRF Lite is introduced. That is, VRF instances are configured on the CE. The following
figure shows the networking mode. The enterprise branch needs only 1 CE to connect to the PE,
VRF instances are configured on the CE, and the CE interfaces for the 3 departments are bound
to VRF instances. In addition, the CE connects to the PE through only 1 physical link and link
subinterfaces are bound to VRF instances. In this manner, corresponding VRF instances are
logically connected on the CE and PE, so the PE and CE can run a routing protocol in each VRF
instance to exchange VPN routes.
Figure 4-10 Networking diagram for L3VPN deployment
VRF1
VRF2
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
VRF2
VRF1
RNC
Main interface
Dot1q sub-interface
VRF1 service flow
VRF2 service flow
The preceding figure shows how to configure VRF instances. The configuration roadmap is as
follows:
l
Use different VPNs to carry data flows of different users and bind AC interfaces on the
ATN 905 to VRF instances.
Configure dotlq subinterfaces for the interfaces connecting the ATN 905 devices and the
CSG and bind these subinterfaces to VRF instances.
4.5.2 Data Planning
This topic describes data planning required for service deployment.
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The following
recommended values in this example are only for reference.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
79
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-11 Data planning for service deployment
GE0/2/1.2 172.21.1.9/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.9/30 dot1q 3 VRF2
10.182.1.4/32(VRF2)
10.224.1.4/32(VRF2)
10.182.1.1/32(VRF1)
10.224.1.1/32(VRF1)
GE0/2/0.2 172.21.1.21/30 dot1q 2 VRF1
GE0/2/0.3 192.168.1.21/30 dot1q 3 VRF2
Macro Cell
192.168.1.18
172.21.1.6
172.21.1.5
GE0/2/2
192.168.1.17
GE0/2/2
GE0/2/1
GE0/2/0
GE0/2/1
192.168.1.1
GE0/2/3
192.168.1.2
IPRAN
GE0/2/0
GE0/2/3
172.21.1.13
RNC/SGW
172.21.1.14
GE0/2/1.2 172.21.1.10/30 dot1q 2 VRF1
GE0/2/1.3 192.168.1.10/30 dot1q 3 VRF2
10.182.1.2/32(VRF2)
10.224.1.2/32(VRF2)
GE0/2/0.2 172.21.1.22/30 dot1q 2 VRF1
GE0/2/0.3 192.168.1.22/30 dot1q 3 VRF2
10.182.1.3/32(VRF1)
10.224.1.3/32(VRF1)
Table 4-3 Network segment planning
Issue 03 (2013-11-22)
Network Segment
Remarks
10.182.1.0/24
IP address of a small-cell wireless base
station for voice services
10.224.1.0/24
IP address of a small-cell wireless base
station for data services
172.21.1.0/24(VRF1)
IP address of the access link for all small-cell
base stations connected to one marco base
station.
192.168.1.0/24(VRF2)
IP address of the access link for all small-cell
base stations connected to one marco base
station.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
80
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Table 4-4 Interface planning
NE Name
NE
Name
Interface
IP Address
VPN
Remarks
SmallCellSi
teA
SmallC
ellSiteA
1
loopback0
10.182.1.1/32
VRF1
IP address of
NE
SmallCellSite
A1 for voice
services
loopback1
10.224.1.1/32
VRF1
IP address of
NE
SmallCellSite
A1 for data
services
loopback0
10.182.1.2/32
VRF2
IP address of
NE
SmallCellSite
A2 for voice
services
loopback1
10.224.1.2/32
VRF2
IP address of
NE
SmallCellSite
A2 for data
services
loopback0
128.4.11.11/32
Router ID of
ATN905SmallCellSite
A-001
GigabitEth
ernet
0/2/1.2
172.21.1.9/30
VRF1
NNI on a
backhaul
device
192.168.1.9/30
VRF2
NNI on a
backhaul
device
GigabitEth
ernet 0/2/2
172.21.1.5/30
VRF1
To NE
SmallCellSite
A1
GigabitEth
ernet 0/2/3
192.168.1.1/30
VRF2
To NE
SmallCellSite
A2
SmallC
ellSiteA
2
ATN90
5SmallC
ellSiteA
-001
vlan-type
dot1q 2
GigabitEth
ernet
0/2/1.3
vlan-type
dot1q 3
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
81
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
NE Name
NE
Name
Interface
IP Address
VPN
Remarks
SmallCellSi
teB
SmallC
ellSiteB
1
loopback0
10.182.1.4/32
VRF2
IP address of
NE
SmallCellSite
B1 for voice
services
loopback1
10.224.1.4/32
VRF2
IP address of
NE
SmallCellSite
B1 for data
services
loopback0
10.182.1.3/32
VRF1
IP address of
NE
SmallCellSite
B2 for voice
services
loopback1
10.224.1.3/32
VRF1
IP address of
NE
SmallCellSite
B2 for data
services
loopback0
128.4.12.12/32
Router ID of
ATN905SmallCellSite
B-002
GigabitEth
ernet
0/2/0.2
172.21.1.21/30
VRF1
To Next905
192.168.1.21/3
0
VRF2
To Next905
172.21.1.10/30
VRF1
NNI on a
backhaul
device
SmallC
ellSiteB
2
ATN90
5SmallC
ellSiteB
-002
vlan-type
dot1q 2
GigabitEth
ernet
0/2/0.3
vlan-type
dot1q 3
GigabitEth
ernet
0/2/1.2
vlan-type
dot1q 2
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
82
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
NE
Name
4 Solution 2: Native IP VRF Dynamic Route Access
Interface
IP Address
VPN
Remarks
GigabitEth
ernet
0/2/1.3
192.168.1.10/3
0
VRF2
NNI on a
backhaul
device
GigabitEth
ernet 0/2/2
192.168.1.17/3
0
VRF2
To NE
SmallCellSite
B1
GigabitEth
ernet 0/2/3
172.21.1.13/30
VRF1
To NE
SmallCellSite
B2
loopback0
128.4.13.13/32
Router ID
GE0/2/0.2
172.21.1.22/30
VRF1
To Next905
192.168.1.22/3
0
VRF2
To Next905
vlan-type
dot1q 3
MacroCellS
ite
ATN91
0MacroC
ellSite-0
03
vlan-type
dot1q 2
GE0/2/0.3
vlan-type
dot1q 3
Table 4-5 VRF data planning
NE
VPN
Instance
Name
RD
Remarks
ATN905SmallCellSiteA-001
VRF1
100:1
VRF2
100:2
Isolates base station data, and
adds each AC port of ATN 905 to
the specific VRF.
ATN905SmallCellSiteB-002
VRF1
100:1
VRF2
100:2
ATN910MacroCellSite-003
VRF1
200:1
VRF2
200:2
4.5.3 Configuring VRF Lite Services
This topic describes how to configure VRF Lite to carry services.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
83
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Configuring ATN905-SmallCellSiteA-001
1.
Create virtual private network (VPN) instances.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 100:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 100:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/1.2
description NNI
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.9 30
interface GigabitEthernet0/2/1.3
description NNI
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.9 30
interface GigabitEthernet0/2/2
description To SmallCellSiteA1
ip binding vpn-instance VRF1
ip address 172.21.1.5 30
interface GigabitEthernet0/2/3
description To SmallCellSiteA2
ip binding vpn-instance VRF2
ip address 192.168.1.1 30
Configuring ATN905-SmallCellSiteB-002
1.
Create VPN instances.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 100:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 100:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/0.2
description To Next905
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.21 30
interface GigabitEthernet0/2/0.3
description To Next905
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.21 30
interface GigabitEthernet0/2/1.2
description To SmallCellSite
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.10 30
interface GigabitEthernet0/2/1.3
description To SmallCellSite
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.10 30
interface GigabitEthernet0/2/2
description To SmallCellSiteB1
ip binding vpn-instance VRF2
ip address 192.168.1.17 30
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
84
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
interface GigabitEthernet0/2/3
description To SmallCellSiteB2
ip binding vpn-instance VRF1
ip address 172.21.1.13 30
Configuring ATN910-MacroCellSite-003
1.
Create VPN instances.
ip vpn-instance VRF1
ipv4-family
route-distinguisher 100:1
ip vpn-instance VRF2
ipv4-family
route-distinguisher 100:2
2.
Configure subinterfaces and bind them to the VRF instance.
interface GigabitEthernet0/2/1.2
description NNI
vlan-type dot1q 2
ip binding vpn-instance VRF1
ip address 172.21.1.22 30
interface GigabitEthernet0/2/1.3
description NNI
vlan-type dot1q 3
ip binding vpn-instance VRF2
ip address 192.168.1.22 30
4.6 Deploying the IGP
The Interior Gateway Protocol (IGP) can be deployed using either of the intermediate system
to intermediate system (IS-IS) or the Open Shortest Path First (OSPF) protocol.
4.6.1 Configuring the IS-IS
This topic describes how to configure different IS-IS processes on the access ring and
aggregation ring to isolate routes. This is to relieve routing burden of cell site gateways (CSGs).
Configuration Roadmap
This topic describes the configuration roadmap for the multi-process IS-IS.
As an interior gateway protocol (IGP), the IS-IS protocol runs within an autonomous system
(AS). Also as a link status protocol, the IS-IS protocol calculates routes by running the shortest
path first (SPF) algorithm. To support large-scale networks, the IS-IS protocol uses a 2-level
structure in the route domain and enables the division of 1 domain into multiple areas. Generally
speaking, the level-1 router is deployed within an area, the level-2 router among areas, and the
level-1-2 router between the level-1 router and level-2 router. In the OSPF, routes between
different areas are advertised through the backbone area and the SPF algorithm is used only
within the same area. In the IS-IS, however, the SPF algorithm is used for both level-1 and
level-2 routes to generate shortest path trees (SPTs).
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
85
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-12 IS-IS network diagram
GE0/2/1.2 isis 1001 VRF1
GE0/2/1.3 isis 1002 VRF2
10.182.1.4 32(VRF2)
10.224.1.4 32(VRF2)
10.182.1.1 32(VRF1)
10.224.1.132(VRF1)
GE0/2/0.2 isis 1001 VRF1
GE0/2/0.3 isis 1002 VRF2
Macro Cell
GE0/2/2
GE0/2/1
GE0/2/1
GE0/2/2
GE0/2/3
GE0/2/0
GE0/2/0
GE0/2/3
GE0/2/1.2 isis 1001 VRF1
GE0/2/1.3 isis 1002 VRF2
10.182.1.2 32(VRF2)
10.224.1.2 32(VRF2)
IPRAN
RNC/SGW
GE0/2/0.2 isis 1001 VRF1
GE0/2/0.3 isis 1002 VRF2
10.182.1.3 32(VRF1)
10.224.1.3 32(VRF1)
The configuration roadmap is as follows:
1.
Configure an IS-IS process number for each virtual private network (VPN).
2.
Enable IS-IS on interconnected interfaces between NEs.
3.
Configure a static route between the ATN 905 and its directly-connected small-cell base
station.
4.
Import static routes and direct routes to the IS-IS configured on the ATN 905.
Data Planning
This topic describes the data planning for IS-IS configuration.
Table 4-6 IS-IS parameters
Parameter
Value
Remarks
isis
l Service process number
for VRF1: 1001
The IS-IS process is enabled.
l Service process number
for VRF2: 1002
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
86
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Remarks
network-entity
ISIS 1001
This parameter indicates a
network entity title (NET).
l ATN905SmallCellSiteA-001:
49.0020.0010.0100.1001
.00
l ATN905SmallCellSiteB-002:
49.0020.0010.0100.1002
.00
l ATN910MacroCellSite-003:
49.0020.0010.0100.1003
.00
ISIS 1002
l ATN905SmallCellSiteA-001:
49.0020.0010.0100.1001
.00
NOTICE
You are advised to convert
loopback interface addresses
into NETs to ensure that each
NET is unique on a network. If
network NETs are not unique,
route flapping easily occurs.
Therefore, the NETs must be
properly planned. When
creating a level-2 neighbor, ISIS does not check whether the
area addresses of devices in the
level-2 area are the same. If a
level-1 neighbor needs to be
created, the area addresses of
devices in the level-1 area must
be the same; otherwise, the
level-1 neighbor cannot be
created.
l ATN905SmallCellSiteB-002:
49.0020.0010.0100.1002
.00
l ATN910MacroCellSite-003:
49.0020.0010.0100.1003
.00
Issue 03 (2013-11-22)
is-level
Level-2
This parameter indicates the
NE level.
cost-style
Wide
This parameter specifies the
cost style. Routes with the
specified cost style (in this
example, it is wide) are
received or advertised.
is-name
This parameter name is the
same as the NE name. For
example, set the value to
CSG1 for the NE.
This parameter specifies the
dynamic host name for the
IS-IS process.
timer lspgeneration
1 50 50
This parameter specifies the
delay for generating a label
switched path (LSP). Set the
maximum delay to 1s, the
initial delay to 50 ms, and the
incremental delay to 50 ms.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
87
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Remarks
flash-flood
level-2
The LSP fast flooding
function is enabled to speed
up the convergence of an ISIS network.
Configuring Basic IS-IS Functions
This topic describes how to configure basic IS-IS functions.
Configuring ATN905-SmallCellSiteA-001
l
Configure service-layer IS-IS functions for VRF1 and VRF2.
isis 1001 vpn-instance VRF1
is-level level-2 //Configure an NE as a Level-2 NE.
cost-style wide //Set the cost type of the received and advertised IS-IS
routes to wide.
timer lsp-generation 1 50 50 level-2 //Specify the delay for generating
LSPs.
flash-flood level-2 //Enable LSP fast flooding to speed up IS-IS network
convergence.
network-entity 49.0020.0010.0100.1001.00 //Configure a NET.
is-name ATN905-SmallCellSiteA-001 //Specify the dynamic host name for the ISIS process.
import-route static cost 15 //Import static routes.
import-route direct cost 15 //Import direct routes.
interface GigabitEthernet0/2/1.2 //Enable IS-IS for the interface.
isis enable 1001
isis 1002 vpn-instance VRF2
is-level level-2
cost-style wide
timer lsp-generation 1 50 50 level-2
flash-flood level-2
network-entity 49.0020.0010.0100.1001.00
is-name ATN905-SmallCellSite1-001
import-route static cost 15
import-route direct cost 15
interface GigabitEthernet0/2/1.3
isis enable 1002
Configure static routes from the ATN 905 to its directly-connected small-cell base stations.
ip route-static vpn-instance VRF1 10.182.1.1 32 172.21.1.6 //10.182.1.1 is the
logical address of the small-cell base station and 172.21.1.6 is the IP address
of the interface connecting the small-cell base station to the network.
ip route-static vpn-instance VRF1 10.224.1.1 32 172.21.1.6
ip route-static vpn-instance VRF2 10.182.1.2 32 192.168.1.2
ip route-static vpn-instance VRF2 10.224.1.2 32 192.168.1.2
Configuring ATN905-SmallCellSiteB-002
l
Configure service-layer IS-IS functions for VRF1 and VRF2.
isis 1001 vpn-instance VRF1
is-level level-2
cost-style wide
timer lsp-generation 1 50 50 level-2
flash-flood level-2
network-entity 49.0020.0010.0100.1002.00
is-name ATN905-SmallCellSiteA-001
import-route static cost 15
import-route direct cost 15
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
88
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
interface GigabitEthernet0/2/0.2
isis enable 1001
interface GigabitEthernet0/2/1.2
isis enable 1001
isis 1002 vpn-instance VRF2
is-level level-2
cost-style wide
timer lsp-generation 1 50 50 level-2
flash-flood level-2
network-entity 49.0020.0010.0100.1002.00
is-name ATN905-SmallCellSite1-001
import-route static cost 15
import-route direct cost 15
interface GigabitEthernet0/2/0.3
isis enable 1002
interface GigabitEthernet0/2/1.3
isis enable 1002
If the small-cell base station uses a logical address, a static route leading to the logical
address of the small-cell base station must be configured.
ip
ip
ip
ip
route-static
route-static
route-static
route-static
vpn-instance
vpn-instance
vpn-instance
vpn-instance
VRF1
VRF1
VRF2
VRF2
10.182.1.1
10.224.1.1
10.182.1.2
10.224.1.2
32
32
32
32
192.168.1.14
192.168.1.14
192.168.1.18
192.168.1.18
Configuring ATN910-MacroCellSite-003
l
Configure service-layer IS-IS functions.
isis 1001 vpn-instance VRF1
is-level level-2
cost-style wide
timer lsp-generation 1 50 50 level-2
flash-flood level-2
network-entity 49.0020.0010.0100.1003.00
is-name ATN910-MacroCellSite-003
default-route-advertise always //Advertise the default route to a common ISIS area.
interface GigabitEthernet0/2/0.2
isis enable 1001
isis 1002 vpn-instance VRF2
is-level level-2
cost-style wide
timer lsp-generation 1 50 50 level-2
flash-flood level-2
network-entity 49.0020.0010.0100.1003.0
is-name ATN910-MacroCellSite-003
default-route-advertise always //Advertise the default route to a common ISIS area.
interface GigabitEthernet0/2/0.3
isis enable 1002
Import VPN routes to a macro base station.
bgp 100
ipv4-family vpn-instance VRF1
import-route isis 1001 //Import IS-IS routes to the Border Gateway Protocol
(BGP).
ipv4-family vpn-instance VRF2
import-route isis 1002
Verifying IS-IS Route Configurations
This topic describes how to verify IS-IS route configurations after the routes are successfully
configured.
#After IS-IS routes are successfully configured, you can view route details.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
89
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Run the display ip routing-table vpn-instance command to view the brief information about
the IPv4 routing table.
Run the display ip routing-table vpn-instance verbose command to view the detailed
information about the IPv4 routing table.
#You can run the Ping command to verify the connectivity.
Run the ping command on the access device at a macro base station to verify the connectivity.
The destination address is the IP address of the interface on the NE ATN905SmallCellSiteA-001 for connecting the NE and a small-cell base station.
[HUAWEI]ping -v -vpn-instance VRF1 172.21.1.5
PING 172.21.1.5: 56 data bytes, press CTRL_C to
break
Reply from 172.21.1.5: bytes=56 Sequence=1 ttl=251
ms
Reply from 172.21.1.5: bytes=56 Sequence=2 ttl=251
ms
Reply from 172.21.1.5: bytes=56 Sequence=3 ttl=251
ms
Reply from 172.21.1.5: bytes=56 Sequence=4 ttl=251
ms
Reply from 172.21.1.5: bytes=56 Sequence=5 ttl=251
ms
time=2
time=1
time=1
time=1
time=1
--- 172.21.1.5 ping statistics
--5 packet(s)
transmitted
5 packet(s)
received
0.00% packet
loss
round-trip min/avg/max = 1/1/2 ms
4.6.2 Deploying the OSPF
Configuration Roadmap
This topic describes the configuration roadmap for the Open Shortest Path First (OSPF) protocol.
As an interior gateway protocol (IGP), the OSPF protocol runs within an autonomous system
(AS). The OSPF partitions an AS into 1 or multiple logical areas and advertises routes through
link state advertisement (LSA). In the OSPF, the backbone area (represented by area 0) must be
defined. The backbone area is formed by consecutive NEs, and common areas are connected to
the backbone area to communicate with each other.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
90
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Figure 4-13 OSPF network diagram
GE0/2/1.2 OSFP 1001 VRF1
GE0/2/1.3 OSPF 1002 VRF2
10.182.1.4 32(VRF2)
10.224.1.4 32(VRF2)
10.182.1.1 32(VRF1)
10.224.1.132(VRF1)
GE0/2/0.2 OSPF 1001 VRF1
GE0/2/0.3 OSPF 1002 VRF2
Macro Cell
GE0/2/2
GE0/2/2
GE0/2/1
GE0/2/1
GE0/2/3
IPRAN
GE0/2/0
GE0/2/0
GE0/2/3
RNC/SGW
GE0/2/1.2 OSPF 1001 VRF1
GE0/2/1.3 OSPF 1002 VRF2
10.182.1.2 32(VRF2)
10.224.1.2 32(VRF2)
GE0/2/0.2 OSPF 1001 VRF1
GE0/2/0.3 OSPF 1002 VRF2
10.182.1.3 32(VRF1)
10.224.1.3 32(VRF1)
The configuration roadmap is as follows:
l
Configure an OSPF process for each virtual private network (VPN).
Enable OSPF on interconnected interfaces between NEs.
Configure a static route between the ATN 905 and its directly-connected small-cell base
station.
Import static routes and direct routes to the OSPF configured on the ATN 905.
Data Planning
This topic describes the data planning for Open Shortest Path First (OSPF) deployment.
Table 4-7 OSPF parameters
Parameter
Value
Remarks
ospf
l Service process number
for VRF1: 1001
The OSPF process is enabled.
l Service process number
for VRF2: 1002
area
OSPF area 1 is created.
spf-scheduleinterval
Maximum interval: 200 ms
This parameter specifies the
SPF timer.
Initial interval: 50 ms
Incremental interval: 50 ms
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
91
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Parameter
Value
Remarks
lsa-originateinterval
Maximum interval: 100 ms
This parameter specifies the
intelligent timer for updating
link-state advertisements
(LSAs).
Initial interval: 50 ms
Incremental interval: 50 ms
lsa-arrivalinterval
Maximum interval: 500 ms
Initial interval: 50 ms
Incremental interval: 1000
ms
This parameter specifies the
intelligent timer for receiving
LSAs.
Configuring Basic OSPF Functions
This topic describes how to configure basic Open Shortest Path First (OSPF) functions.
For ATN905-SmallCellSiteA-001
l
Configure service-layer OSPF functions (VRF1 and VRF2).
ospf 1001 router-id 128.4.11.11 vpn-instance VRF1//Create OSPF process
1001.
spf-schedule-interval intelligent-timer 200 50 50//Set the maximum interval
for OSPF route calculation to 200 ms, initial interval to 50 ms, and
incremental interval to 50 ms.
lsa-originate-interval intelligent-timer 500 50 100//Set the maximum interval
for updating OSPF link-state advertisements (LSAs) to 500 ms, initial interval
to 50 ms, and incremental interval to 100 ms.
lsa-arrival-interval intelligent-timer 100 50 50//Set the maximum interval
for receiving OSPF LSAs to 100 ms, initial interval to 50 ms, and incremental
interval to 50 ms.
import-route direct cost 15 //Import direct routes.
import-route static cost 15 //Import static routes.
area 0.0.0.0//Configure the OSPF area.
interface GigabitEthernet0/2/1.2
ospf enable 1001 area 0.0.0.0//Enable the OSPF for the interface.
ospf 1002 router-id 128.4.11.11 vpn-instance VRF2
spf-schedule-interval intelligent-timer 200 50 50
lsa-originate-interval intelligent-timer 500 50 100
lsa-arrival-interval intelligent-timer 100 50 50
import-route direct cost 15
import-route static cost 15
area 0.0.0.0
interface GigabitEthernet0/2/1.3
ospf enable 1002 area 0.0.0.0
For ATN905-SmallCellSiteB-002
l
Configure service-layer OSPF functions for VRF1 and VRF2.
ospf 1001 router-id 128.4.12.12 vpn-instance VRF1
spf-schedule-interval intelligent-timer 200 50 50
lsa-originate-interval intelligent-timer 500 50 100
lsa-arrival-interval intelligent-timer 100 50 50
import-route direct cost 15
import-route static cost 15
area 0.0.0.0
interface GigabitEthernet0/2/0.2
ospf enable 1001 area 0.0.0.0
interface GigabitEthernet0/2/1.2
ospf enable 1001 area 0.0.0.0
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
92
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
ospf 1002 router-id 128.4.12.12 vpn-instance VRF2
spf-schedule-interval intelligent-timer 200 50 50
lsa-originate-interval intelligent-timer 500 50 100
lsa-arrival-interval intelligent-timer 100 50 50
import-route direct cost 15
import-route static cost 15
area 0.0.0.0
interface GigabitEthernet0/2/0.3
ospf enable 1002 area 0.0.0.0
interface GigabitEthernet0/2/1.3
ospf enable 1002 area 0.0.0.0
For ATN910-MacroCellSite-003
l
Configure service-layer OSPF functions for VRF1 and VRF2.
ospf 1001 router-id 128.4.13.13 vpn-instance VRF1
spf-schedule-interval intelligent-timer 200 50 50
lsa-originate-interval intelligent-timer 500 50 100
lsa-arrival-interval intelligent-timer 100 50 50
default-route-advertise //Advertise the default route to a common OSPF area.
area 0.0.0.0
interface GigabitEthernet0/2/0.2
ospf enable 1001 area 0.0.0.0
ospf 1002 router-id 128.4.13.13 vpn-instance VRF2
spf-schedule-interval intelligent-timer 200 50 50
lsa-originate-interval intelligent-timer 500 50 100
lsa-arrival-interval intelligent-timer 100 50 50
default-route-advertise //Advertise the default route to a common OSPF area.
area 0.0.0.0
interface GigabitEthernet0/2/0.3
ospf enable 1002 area 0.0.0.0
Import VPN routes.
bgp 100
ipv4-family vpn-instance VRF1
import-route ospf 1001//Import OSPF routes to the Border Gateway Protocol
(BGP).
ipv4-family vpn-instance VRF2
import-route ospf 1002
Verifying OSPF Route Configurations
This topic describes how to verify Open Shortest Path First (OSPF) route configurations after
the routes are successfully configured.
#After OSPF routes are successfully configured, you can view route details.
l
Run the display ip routing-table vpn-instance command to view the brief information about
the IPv4 routing table.
Run the display ip routing-table vpn-instance verbose command to view the detailed
information about the IPv4 routing table.
#You can run the Ping command to verify the connectivity.
Run the ping command on the access device at a macro base station to verify the connectivity.
The destination address ATN905-SmallCellSiteA-001 is the IP address of the interface at the
small-cell base station to which the macro base station is connected.
[HUAWEI]ping -v -vpn-instance VRF1 172.21.1.5
PING 172.21.1.5: 56 data bytes, press CTRL_C to
break
Reply from 172.21.1.5: bytes=56 Sequence=1 ttl=251 time=2
ms
Reply from 172.21.1.5: bytes=56 Sequence=2 ttl=251 time=1
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
93
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
ms
Reply from 172.21.1.5: bytes=56 Sequence=3 ttl=251 time=1
ms
Reply from 172.21.1.5: bytes=56 Sequence=4 ttl=251 time=1
ms
Reply from 172.21.1.5: bytes=56 Sequence=5 ttl=251 time=1
ms
--- 172.21.1.5 ping statistics
--5 packet(s)
transmitted
5 packet(s)
received
0.00% packet
loss
round-trip min/avg/max = 1/1/2 ms
4.7 Deploying QoS
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
4.7.1 Configuring QoS
You can configure simple traffic classification to classify data packets into multiple priorities
or service classes, and therefore to provide differentiated services.
Configuration Roadmap
Traditional IP networks in best-effort mode are mainly used to carry data services, and the service
quality seems insignificant. However, with fast development of IP-oriented Internet services and
emerging of various new services (such as VoIP and VPN services), IP networks have changed
from pure data networks to bearer networks with commercial values. Therefore, IP networks
must ensure the quality of each type of service that they carry. Against this backdrop, quality of
service (QoS) is developed.
The ATN 905 functions as a small-cell base station bearer device or enterprise private line
Ethernet demarcation device (EDD). When configured with simple traffic classification, the
ATN 905 can manage the traffic. Priority mapping based on simple traffic classification indicates
that the priority of the packets on a network is mapped into the packets of another network so
that the packets of the first network can be transmitted on the second network based on the
original or user-defined packet priority. That is, on the ingress, the packets obtain the priority
and color for scheduling on the ATN equipment based on the values of the DSCP and 802.1p
fields. After being scheduled on the ATN equipment, the outgoing packets obtain the values of
the priority fields (such as DSCP and 802.1p) for encapsulation based on the above-mentioned
priority and color. In this manner, during traffic management, packets of different services join
different queues, ensuring differentiated scheduling.
To configure simple traffic classification, do as follows:
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
94
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Bind the default DiffServ domain to service interfaces (including main interfaces and
subinterfaces) of the ATN 905 to configure simple traffic classification.
Data Planning
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
trust upstream
default
Bind the DiffServ domain to
an interface.
Application Process
l
For ATN905-SmallCellSiteA-001
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN905-SmallCellSiteB-002
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN910-MacroCellSite-003
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
4.8 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
4.8.1 Configuration Roadmap
Synchronization includes frequency synchronization and phase synchronization. In this solution,
you are advised to configure synchronous Ethernet and IEEE 1588v2 on the ATN 905 to achieve
frequency synchronization and phase synchronization respectively.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
95
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
To ensure that most services run normally on a current communication network, devices on the
entire network should keep the frequency or phase difference within a permitted range. That is,
synchronization, either frequency synchronization or phase synchronization, must be ensured
on the network. Frequency synchronization (also known as clock synchronization) indicates that
signals retain certain relationships with respect to the phase. That is, the phase difference between
signals is constant. Phase synchronization (also known as time synchronization) indicates that
signals have the same frequency and phase. That is, there is no phase difference between signals.
For example, if two watches always indicate the same time, they are in phase synchronization;
if the two watches always have a constant time difference (such as 6 hours), they are in frequency
synchronization. In the IP RAN scenario, the ATN equipment needs to support frequency or
phase synchronization to meet the requirements of base stations.
Mainstream PSN-based synchronization technologies in the industry include IEEE 1588v2 and
synchronous Ethernet. In this solution, you are advised to configure synchronous Ethernet and
IEEE 1588v2 on the ATN 905 to achieve frequency synchronization and phase synchronization
respectively.
Figure 4-14 Networking diagram for clock deployment
Micro/Pico
Micro/Pico
BITS
GE0/2/2
GE0/2/3
pri 20
GE0/2/1
GE0/2/2
GE0/2/1
pri 20
GE0/2/0 GE0/2/0
ASG
pri 10
RSG
GE0/2/3
Clock Tracking Path
pri n
Priority of a reference clock source at a port
The preceding figure shows how to configure a clock. The configuration roadmap is as follows:
l
Enable synchronous Ethernet and IEEE 1588v2 for the ATN 905, so that the ATN 905 can
track the upstream clock information and time information, and send them to base stations.
4.8.2 Data Planning
This topic describes data planning for clock deployment.
l
For synchronous Ethernet, configure clock signal priorities in the local priority list, and
enable synchronization status message (SSM) control.
NOTE
For synchronous Ethernet clock synchronization, a clock source is selected based on the following
descending order of priority: SSM clock quality, local priority setting, and clock source type.
l The SSM clock quality levels are in the following descending order: primary reference clock (PRC),
SSUA, SSUB, SDH equipment clock (SEC), and DNU. A source for which no quality level is defined,
and a clock source with quality level being DNU, are not be selected during source selection.
l The local priority is configured as follows: The value range is 1 to 255, and a smaller value indicates
a higher priority.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
96
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
For IEEE 1588v2, use the best master clock (BMC) algorithm.
NOTE
When the BMC algorithm is used by a 1588v2-enabled device for master clock selection, priority1 of each
candidate time source is compared first, then the clock class, clock accuracy, and priority2. If priority1 of
candidate time sources is the same, the clock class is compared, and so on. The time source with the highest
priority is selected as the master clock.
Table 4-8 Data planning for synchronous Ethernet time synchronization
NE Name
Parameter
Value
Remarks
ATN905SmallCellSiteA-001
Local priority
list
20
Clock output
port
GE0/2/2
Connects to a base station.
ATN905SmallCellSiteB-002
ATN910MacroCellSite-003
GE0/2/3
Table 4-9 Data planning for IEEE 1588v2 time synchronization
NE Name
Parameter
Value
Remarks
ATN905-SmallCellSiteA-001
Port delay
measurement
mechanism
delay
The mechanism is
recommended to be
set consistently
networkwide.
NE type
BC
The networkwide BC
mode is
recommended.
Ring network
asymmetry automeasurement
enable
Automatically adjusts
the length difference
between transmit and
receive fibers when
ring network
protection switching
occurs for restoration.
Clock output port
GE0/2/2
Connects to a base
station.
ATN905-SmallCellSiteB-002
ATN910-MacroCellSite-003
GE0/2/3
4.8.3 Configuring Synchronous Ethernet to Achieve Frequency
Synchronization
To achieve frequency synchronization on a network, use synchronous Ethernet.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
97
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
Configure NE ATN905-SmallCellSiteA-001
clock ethernet-synchronization enable //Enables global synchronous Ethernet in the
system view.
clock ssm-control on //Configures SSM for source selection. By default, SSM is
enabled for an ATN NE.
interface GigabitEthernet0/2/1
clock priority 20//Assigns a clock priority to the interface. This will affect
clock selection in the inbound direction on the local end. A smaller value
indicates a higher priority. Assigning the highest priority to each interface on
the shortest path for clock signal transmission is recommended.
clock synchronization enable//Enables synchronous Ethernet for an interface.
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
Configure NE ATN905-SmallCellSiteB-002
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock priority 20
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
interface GigabitEthernet0/2/3
clock synchronization enable
Configure NE ATN910-MacroCellSite-003
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
4.8.4 Configuring IEEE 1588v2 to Achieve Time Synchronization
After frequency synchronization is achieved on a network using synchronous Ethernet, use IEEE
1588v2 to achieve time synchronization on the network.
Configure NE ATN905-SmallCellSiteA-001
ptp enable //Enables global IEEE 1588v2.
ptp device-type bc //Specifies the BC mode for all devices.
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay //Configures the delay measurement mechanism of a
device as delay which calculates the time difference based on the link delay of the
master and slave clocks.
ptp enable //Enables IEEE 1588v2 for the interface.
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN905-SmallCellSiteB-002
ptp enable
ptp device-type bc
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
98
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
4 Solution 2: Native IP VRF Dynamic Route Access
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN910-MacroCellSite-003
ptp enable
ptp device-type bc
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
99
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Solution 3: Native Ethernet Access
About This Chapter
The native Ethernet access solution is applied to the scenario where Layer 2 access solutions are
used for the upstream network. In the native Ethernet solution, VLANIF interfaces are
configured to transmit management plane packets, and VLAN packets from a small-cell base
station are transparently transmitted between the ATN 905 and the access device at the macro
base station.
5.1 Scenario Introduction
This topic briefly introduces the application scenarios of the ATN 905, covering the overview,
configuration roadmap, and data planning.
5.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
5.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
5.4 Configuring the Management Plane
This topic describes the configuration roadmap for the management plane.
5.5 Deploying the serive
5.6 Deploying QoS
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
5.7 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
100
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
5.1 Scenario Introduction
This topic briefly introduces the application scenarios of the ATN 905, covering the overview,
configuration roadmap, and data planning.
Overview
Solution 3: Native Ethernet access (native Ethernet + public network IGP management
plane + hybrid interface access)
Figure 5-1 Example network of native Ethernet access
VLAN
(10,20)
VLAN
(30,40)
Macro Cell
ATN 905
IPRAN
ATN 905
CSG
VLAN
(30,40)
Issue 03 (2013-11-22)
VLAN
(10,20)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
RNC
Trunk interface
Dot1q sub-interface
Management plane
VLAN(10,20) service flow
VLAN(30,40) service flow
101
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Table 5-1 Solution information
Solution Feature
Applicable
Scenario
Solution
Advantage
Solution
Constraint
l Service
configurations
for small-cell
base stations:
native Ethernet
1. Scenario in which
the carrier
solution on the
macro base
station side
adopts the Layer
2 access solution
1. Users' IP address
planning does not
need to be
concerned.
1. The loopbreaking
protocols need to
be deployed to
prevent Layer 2
broadcast storms.
l Management
plane:
public network
IGP management
plane
l Native Ethernet
access:
hybrid interface
access
2. Ethernet
demarcation
device (EDD)
scenario
2. Users' VLANs
are not isolated
from carriers'
VLANs.
3. Scenario in which
users' VLANs are
not isolated from
carriers' VLANs
Configuration Roadmap
Small-cell base station packets need to be transparently transmitted to the CSG. The
configuration roadmap is as follows:
l
Add each AC port of the ATN 905 into the VLANs to which the small-cell base station
data belongs, and add the NNI interfaces of the ATN 905 into the VLANs to which the AC
ports belong.
Establish a management plane between the ATN 905 and the CSG based on public network
subinterfaces.
Configure L2VPNs for packets with different VLAN tags on each AC port of the CSG.
Deploy simple traffic classification (STC) on the ATN 905.
Deploy Synchronous Ethernet (SyncE) on the ATN 905 to implement frequency
synchronization; deploy IEEE 1588v2 to implement time synchronization.
Data Planning
Item
Planning Guidelines
Basic configuration
parameters:
You are advised to configure the basic configuration parameters
except NE name in the centralized manner based on the entire
network. In this way, these basic configuration parameters are
planned once for all.
l NE name
l User login parameter
l SNMP
l AAA
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
102
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Item
Planning Guidelines
Small-cell base station
data:
1. The VLAN (to which the small-cell base station data belongs)
need to be planned.
l VLAN ID
ATN 905 data:
l Management
subinterfaces and
their IP addresses
1. Management subinterfaces and their IP addresses need to be
planned.
2. A VLAN ID needs to be planned to traverse interfaces
interconnecting the ATN 905 devices.
l Vlan ID for trunk
QoS
STC is deployed on each service interface of the ATN 905.
Clock
SyncE and 1588v2 functions are enabled on the ATN 905 so that
the ATN 905 traces the clock and time of the upstream device
and transmits the clock signals to base stations.
5.2 Logging In to the ATN 905
This chapter describes how to log in to the ATN 905 for later commissioning. Two login methods,
login by using the console interface and SSH, are introduced.
5.2.1 Logging In to the ATN by Using SSH
This section describes how to log in to the ATN 905 by using SSH. SSH is a secure remote login
protocol developed based on the traditional Telnet protocol. Compared with Telnet, SSH is
greatly improved in terms of the authentication mode and data transmission security.
Figure 5-2 shows the networking diagram for logging in to the ATN 905 by using SSH.
Figure 5-2 Networking diagram for logging in to the ATN 905 by using SSH
network
SSH Client
SSH Server
Prerequisite
l
The ATN 905 is running properly.
The ATN 905 has been logged in using the console interface and an IP address for each
interface has been configured on the ATN 905.
A direct or reachable route exists between the SSH client and the ATN 905.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
103
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
NOTE
Perform the following configurations on the ATN 905 that serves as the SSH server. This section describes only
the SSH login by using the PuTTY program.
Procedure
Step 1 As shown in the following figure, set the IP address of the ATN 905 to 192.168.1.1 and the login
protocol to SSH.
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The IP address of the
management network interface Ethernet0/0/0 (the console interface) is 129.0.0.1. If the ATN has accessed
the network when it is powered on for the first time, its IP address 129.0.0.1 will be automatically changed
to the IP address that DHCP obtains during the startup.
Figure 5-3 Login by using the PuTTY program
Step 2 Enter the user name root and the password Changeme_123.
NOTE
After the ATN is powered on for the first time, you can log in to it in STelnet mode. The user name and
password are root and Changeme_123 respectively. After logging in to the ATN, change the default
password in time.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
104
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Figure 5-4 Login using the PuTTY program
----End
5.2.2 Logging In to the ATN by Using the Console Interface
This section describes how to use the HyperTerminal in Windows on the PC to log in to the
ATN 905 after setting up a local configuration environment with the console interface.
Context
Figure 5-5 shows the networking diagram for logging in to the NE80E/40E by using the console
interface.
Figure 5-5 Networking diagram for logging in to the ATN 905 by using the console interface
PC
ATN
Prerequisite
l
The ATN 905 is running properly.
The PC is connected to the ATN 905 through an asynchronous interface.
Installing terminal emulation program on the PC (such as Windows XP HyperTerminal)
NOTE
Perform the following configurations on the HyperTerminal on the PC.
The console port applies the non-standard serial port communication cable sequence. For more information, see
ATN 905Multi-service Access Equipment Installation Guide.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
105
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Procedure
Step 1 Use a serial cable to connect the serial interface on the PC and the console interface on the ATN
905.
For more information about the console interface, see the ATN 905Multi-service Access
EquipmentHardware Description.
Step 2 Start the HyperTerminal on the PC.
Choose Start > Programs > Accessories > Communications to start the HyperTerminal in
Windows.
Step 3 Set up a connection.
As shown in Figure 5-6, enter the name of the new connection in the Name text box, and select
an icon. Then, click OK.
Figure 5-6 Setting up a connection
Step 4 Set a connection port.
In the Connect To dialog box shown in Figure 5-7, select a port from the drop-down list box
of Connect using according to the port actually used on the PC or terminal. Then, click OK.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
106
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Figure 5-7 Setting a connection port
Step 5 Set communication parameters.
When the COM1 Properties dialog box is displayed as shown in Figure 5-8, set the COM1
properties according to the description in Figure 5-8 or by clicking Restore Defaults.
NOTE
l Setting the COM1 properties according to the description in Figure 5-8 and setting them by clicking
Restore Defaults have the same effect. The default settings of the console interface will be used.
l When you log in to the ATN 905 by using the console interface, ensure that the COM1 properties on
the HyperTerminal are consistent with the interface attribute settings on the ATN 905. Otherwise, the
login will fail. This means that if default settings are not used for the interface attributes on the ATN
905, the COM1 properties on the HyperTerminal must be changed to be consistent with the interface
attribute settings on the ATN 905.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
107
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Figure 5-8 Setting communication parameters
----End
Commissioning Result
After the preceding configurations are complete, press Enter. An initial password is required
for the first login. Set an authentication password. The system automatically saves the set
password.
An initial password is required for the first login via the console.
Set a password and keep it safe! Otherwise you will not be able to login via the
console.
Please configure the login password (6-16)
Enter Password:
Confirm Password:
If the login fails, click Disconnect and then Call. If the login still fails, repeat Step 1 to check
whether the parameters or physical connections are correct. If they are correct, log in to the ATN
905 again.
5.3 Configuring Basic Information
Before configuring services, you need to perform basic configurations, including the device
name, user login parameter, authentication, authorization, and accounting (AAA), and Simple
Network Management Protocol (SNMP) configurations, for the devices.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
108
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
5.3.1 Configuring NE Information
If multiple devices on a network need to be managed, set equipment names to identify each
device.
Data Planning
An NE name consists of the site name, device model, and device number. Each NE is named in
the format of AA-BB-CC. The following provides the meaning of the letters.
l
AA: device model, for example, ATN 910 or ATN 905
BB: site name, for example, SmallCellSiteA
CC: device number, starting from 001
For example, ATN905-SmallCellSiteA-001 refers to an ATN 905 numbered 001 at site
SmallCellSiteA.
Parameter
Value
Description
sysname
ATN905SmallCellSiteA-001
Indicates the NE name.
NOTE
All the NEs involved in this document are named as shown in the following figure.
Figure 5-9 NE names
SmallCellSiteB1
SmallCellSiteA1
Macro Cell
Micro/Pico
ATN905SmallCellSiteB-002
Micro/Pico
Micro/Pico
ATN905SmallCellSiteA-001
IPRAN
ATN910MacroCellSite-003
RNC
Micro/Pico
SmallCellSiteA2
SmallCellSiteB2
Configuration Process
l
Configure the name of the NE as ATN905-SmallCellSiteA-001.
sysname ATN905-SmallCellSiteA-001
Configure the name of the NE as ATN905-SmallCellSiteB-002.
sysname ATN905-SmallCellSiteB-002
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
109
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Configure the name of the NE as ATN910-MacroCellSite-003.
sysname ATN910-MacroCellSite-003
5.3.2 Configuring the VTY User Interface
To log in to an ATN device remotely, you can configure the virtual type terminal (VTY) user
interface to ensure equipment security.
Data Planning
To log in to an ATN device in telnet or Secure Shell (SSH) mode, you can configure the VTY
user interface to ensure equipment security. The following parameters are involved: the
maximum number of VTY user interfaces, user authentication mode, user privilege, and VTY
attributes.
l
By setting the maximum number of VTY user interfaces, you can limit the number of users
who can log in to the ATN device concurrently.
By setting the user authentication mode, you can enhance the equipment security. The user
authentication mode can be set to AAA authentication or password authentication.
1.
The AAA authentication mode is based on users, ensuring high security. To log in to
the ATN device, you need to enter the user name and password.
2.
The password authentication mode is based on VTY channels, requiring simple
configuration while ensuring high security. You only need to be create a login
password.
By setting the user privilege, you can differentiate the access rights of different users on
the ATN device to enhance the management security. User privileges are divided into 16
levels, which are numbered 0 to 15. A larger value indicates a higher user privilege.
You can configure the VTY attributes of a VTY user interface, such as the timeout interval
of communication failure for login users. Each VTY attribute on the VTY user interface
has a default value on the ATN device. You can re-configure the terminal attributes as
required.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
user-interface
maximum-vty
15
Sets the maximum number of
users that are allowed to log
in to the NE to 15.
NOTE
When the value of this
parameter is set to 0, no user
(even the NMS user) can log in
to the ATN device through the
VTY user interface.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
110
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Parameter
Value
Description
user-interface
vty 0 14
Indicates that the maximum
number of VTY user
interfaces is the total number
of users that have logged in to
the NE through Telnet or
STelnet.
authentication-mode
aaa
Sets the authentication mode
to AAA authentication for
users that attempt to log in to
the NE.
protocol inbound
ssh
Specifies the login protocol
supported by the VTY user
interface to SSH.
user privilege
level 3
Specifies the command level
to level 3.
idle-timeout
50
Sets the timeout interval of
communication failure for
login users.
Configuration Process
Perform the following configurations on all ATN devices:
1.
Set the maximum number of VTY user interfaces.
user-interface maximum-vty 15 //Set the maximum number of VTY user interfaces
that are allowed to log in to the NE at the same time.
2.
Configure VTY attributes.
user-interface vty 0 14 //Perform configurations for VTY 0 to VTY 14.
protocol inbound ssh
authentication-mode aaa
user privilege level 3
idle-timeout 5 0
5.3.3 Configuring AAA Users
If the user authentication mode is set to AAA authentication on an ATN device, you need to
configure user names and passwords on the ATN device to manage and authenticate users.
Data Planning
If the user authentication mode is set to AAA authentication in an ATN device, a user needs to
keep the login user name and password properly, and uses them to log in to the ATN device.
The levels of commands that can be used by users logging in to an ATN device concurrently are
determined by the privileges of these users in the AAA configuration.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
111
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Parameter
Value
Description
aaa
Enters the AAA view to
create a user, set a user level,
or configure an
authentication scheme, an
authorization scheme, an
accounting scheme, or a
domain, so that the NE
authenticates users.
local-user XXX
password cipher XXX
USER01
Adds a local user USER01.
local-user level
Sets the user level for the
local user. The system
manages commands by
command level. A user can
use only the commands
whose levels are lower than
or equal to the user level.
local-user xxx
service-type xxx
USER01
Sets the access type of local
users to SSH.
Hello@*#123
ssh
Configuration Process
Perform the following configurations on all ATN devices:
aaa
local-user USER01 password cipher Hello@*#123 //Add a local uer (USER01) and set
the password.
local-user USER01 level 3 //Set the user level of the local user.
local-user USER01 service-type ssh //Set the access type for the user.
NOTE
Requirements on user names and passwords for ATN products are as follows:
l A local user name contains 1 to 253 characters.
l A password must contain eight characters at least.
l A password must contain digits, upper-case and lower-case letters, and special characters, excluding
question marks (?) and spaces.
l The password cannot be the same as the user name or the user name in reverse order.
5.3.4 Configuring the SNMP
After the Simple Network Management Protocol (SNMP) is configured, the NMS can monitor
and manage NEs.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
112
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Data Planning
The SNMP is a standard network management protocol widely used on TCP/IP networks. The
NMS can manage NEs using the SNMP. Specifically, the SNMP defines several device
management operations that can be performed by the NMS and alarms that can be automatically
sent to the NMS when the ATN equipment is faulty. The NMS uses the management information
base (MIB) to identify and manage devices. The SNMP versions include SNMPv1, SNMPv2c,
and SNMPv3, which are all supported by the ATN 905.
The Link Layer Discovery Protocol (LLDP) is a Layer 2 discovery protocol defined in 802.1ab.
When the ATN and its neighbors are all enabled with LLDP, the ATN notifies the neighbors of
its status and obtains the status of the neighbors through LLDP packets. The NMS then can get
information about Layer 2 connection of the ATN. In this manner, the NMS can analyze the
network topology.
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values in this example are only for reference.
Table 5-2 SNMP parameters
Issue 03 (2013-11-22)
Parameter
Value
Description
snmp-agent
Enables the SNMP agent
function. By default, the
SNMP agent function is
disabled.
snmp-agent sys-info
version
all
Configures the system to
adopt all the SNMP versions,
namely, SNMPv1,
SNMPv2c, and SNMPv3.
snmp-agent mib-view
included iso-view
iso
Includes the iso subtree in the
SNMP MIB view.
snmp-agent
community read
cipher
Huawei123!
Sets a read community name.
The NMS can access a device
only when the community
name set on the NMS is the
same as that set on the device.
snmp-agent
community write
cipher
Huawei@123
snmp-agent trap
enable
mib-view iso-view
mib-view iso-view
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Sets a write community
name. The NMS can access a
device only when the
community name set on the
NMS is the same as that set
on the device.
Enables all traps on a device.
113
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Parameter
Value
Description
snmp-agent trap
source
LoopBack0
Configures the LoopBack0
interface as the source
interface that sends trap
messages.
snmp-agent targethost trap
address udp-domain
20.20.20.20
Allows the SNMP agent to
send SNMP trap messages to
the Huawei NMS at
20.20.20.20.
params securityname
Huawei@123 v2c privatenetmanager ext-vb
snmp-agent trap
enable feature-name
lldp
Enables the LLDP trap
function.
snmp-agent extend
error-code
enable
Enables the extended error
code function.
lldp enable
Enables the LLDP function.
Application Process
Perform the following configurations on all ATN devices:
snmp-agent
snmp-agent sys-info version all //Enable SNMP of all versions for the system.
snmp-agent mib-view included iso-view iso //Include the iso subtree SNMP MIB
view.
snmp-agent community read cipher Huawei123! mib-view iso-view
snmp-agent community write cipher Huawei@123 mib-view iso-view //Set the read and
write permissions for the write attributes. When the read entity name and write
entity name are the same, the write attribute command will override the read
attribute command.
snmp-agent trap enable
snmp-agent target-host trap address udp-domain 20.20.20.20 params securityname
Huawei@123 v2c private-netmanager ext-vb //When the management plane is deployed
on public network routes, SNMP trap messages can be sent to the U2000 at management
IP address 20.20.20.20 using entity name Huawei@123. If an NMS provided by Huawei
is used, configure private-netmanager and ext-vb.
snmp-agent trap source LoopBack0 //Set the source interface for trap messages.
snmp-agent trap enable feature-name lldp
snmp-agent extend error-code enable
lldp enable
5.4 Configuring the Management Plane
This topic describes the configuration roadmap for the management plane.
5.4.1 Configuration Roadmap
This topic describes the configuration roadmap for the management plane.
Traditional management and service packets are closely coupled, making equipment
management more and more complex and costly. Therefore, it is more and more important to
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
114
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
separate the management and service planes. A user operates and manages devices using the
management plane and deploys services using other planes, such as the service plane. That is,
the logical channels of the management plane and other planes are separated. When the
management plane becomes abnormal, other planes can still be used; when other planes become
abnormal, devices can still be managed.
The configuration roadmap is as follows:
l
Establish a management plane between the ATN 905 and the CSG based on public network
Interior Gateway Protocol (IGP) routes.
5.4.2 Data Planning
This topic describes data planning for the management plane.
Data Planning
NOTE
Set these parameters based on the actual network conditions, such as network size and topology. The
following recommended values and precautions in this example are for reference only.
Figure 5-10 Management plane configuration diagram
GE0/2/0.1 dot1q 1 192.168.1.21/30
Macro Cell
GE0/2/1.1 dot1q 1
192.168.1.9/30
GE0/2/1.1 dot1q 1
192.168.1.10/30
Loopback0
128.4.11.11/32
IPRAN
GE0/2/0
GE0/2/0
Loopback0
128.4.12.12/32
Loopback0
128.4.13.13/32
RNC/SGW
GE0/2/0.1 dot1q 1 192.168.1.22/30
Table 5-3 Interface planning table
NE Name
Interface
IP Address
OSPF
Process
ID
VPN
ATN905SmallCellSiteA-001
Loopback0
128.4.11.11 32
1001
Loopback10
10.182.1.1 32
GigabitEthernet
0/2/1.1
192.168.1.9 30
vlan-type dot1q 1
ATN905SmallCellSiteB-002
Issue 03 (2013-11-22)
Loopback0
128.4.12.12 32
Loopback10
10.182.1.2 32
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
115
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
5 Solution 3: Native Ethernet Access
Interface
IP Address
OSPF
Process
ID
GigabitEthernet
0/2/0.1
192.168.1.21 30
NOTE
The
OSPF
process
ID must
be the
same as
the
manage
ment
OSPF
process
ID on
the
macro
base
station
side.
vlan-type dot1q 1
GigabitEthernet
0/2/1.1
192.168.1.10 30
vlan-type dot1q 1
ATN910MacroCellSite-003
Loopback0
128.4.13.13 32
Loopback10
10.182.1.3 32
GigabitEthernet0/2
/0.1
192.168.1.22 30
vlan-type dot1q 1
VPN
5.4.3 Configuring the Management Plane
This topic describes how to configure the management plane.
Configuring ATN905-SmallCellSiteA-001
interface GigabitEthernet0/2/1.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.9 30
interface Loopback0 //Set the router ID.
ip address 128.4.11.11 32
interface Loopback10 //Set the management IP address.
ip address 10.182.1.1 32
ospf 1001 router-id 128.4.11.11 //Configure an IGP route between management IP
addresses.
area
0.0.0.1
network 10.182.1.1
0.0.0.0
network 192.168.1.0 0.0.0.3
Configuring ATN905-SmallCellSiteB-002
interface GigabitEthernet0/2/0.1
description ToNext905
vlan-type dot1q 1
ip address 192.168.1.10 30
interface GigabitEthernet0/2/1.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.21 30
interface Loopback0
ip address 128.4.12.12 32
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
116
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
interface Loopback10
ip address 10.182.1.2 32
ospf 1001 router-id
128.4.12.12
area
0.0.0.1
network 10.182.1.2
0.0.0.0
network 192.168.1.0 0.0.0.3
Configuring ATN910-MacroCellSite-003
interface GigabitEthernet0/2/0.1
description NNI
vlan-type dot1q 1
ip address 192.168.1.22 30
interface Loopback0
ip address 128.4.13.13 32
interface Loopback10
ip address 10.182.1.3 32
ospf 1001 router-id
128.4.13.13
area
0.0.0.1
network 10.182.1.3
0.0.0.0
network 192.168.1.0 0.0.0.3
5.5 Deploying the serive
5.5.1 Configuration Roadmap
This topic describes the configuration roadmap for Ethernet services.
In the native Ethernet scenario, the ATN 905 needs to transparently transmit small-cell base
station packets to the cell site gateway (CSG). Trunk interfaces can be added into multiple
VLANs to interconnect network devices.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
117
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Figure 5-11 Ethernet services configuration roadmap
Port trunk allow-pass 10 20 30 40
Port trunk allow-pass 10 20 30 40
Micro Cell
VLAN:30,40
VLAN:10,20
GE0/2/2
GE0/2/2
GE0/2/1
GE0/2/1
GE0/2/0
IPRAN
GE0/2/0
GE0/2/3
GE0/2/3
RNC/SGW
VLAN:10,20
VLAN:30,40
The L3VPN configuration roadmap is as follows:
l
Configure the AC interface and NNI-side interface on the ATN 905 as trunk interfaces and
allow packets with the VLAN of the small-cell base station to pass through.
5.5.2 Data Planning
This topic describes the data planning for service configuration.
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The
following recommended values in this example are only for reference.
Table 5-4 Data planning
NE Name
Interface
VLAN
Remarks
ATN905SmallCellSiteA-00
1
GigabitEthernet
0/2/1
port trunk allow-pass
vlan 10 20 30 40
To Next905
GigabitEthernet
0/2/2
port trunk allow-pass
vlan 10 20
To SmallCellSiteA1
GigabitEthernet
0/2/3
port trunk allow-pass
vlan 30 40
To SmallCellSiteA2
GigabitEthernet
0/2/0
port trunk allow-pass
vlan 10 20 30 40
To MacroCellSite
GigabitEthernet
0/2/1
port trunk allow-pass
vlan 10 20 30 40
To Next905
GigabitEthernet
0/2/2
port trunk allow-pass
vlan 30 40
To SmallCellSiteB1
ATN905SmallCellSiteB-02
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
118
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
NE Name
ATN910MacroCellSite-003
5 Solution 3: Native Ethernet Access
Interface
VLAN
Remarks
GigabitEthernet
0/2/3
port trunk allow-pass
vlan 10 20
To SmallCellSiteB2
GigabitEthernet
0/2/0.1
vlan-type dot1q 10
To Next905
GigabitEthernet
0/2/0.2
vlan-type dot1q 20
To Next905
GigabitEthernet
0/2/0.3
vlan-type dot1q 30
To Next905
GigabitEthernet
0/2/0.4
vlan-type dot1q 40
To Next905
5.5.3 Configuring Ethernet Services
This topic describes the configuration roadmap for Ethernet services.
Configuring ATN905-SmallCellSiteA-001
interface GigabitEthernet0/2/1
portswitch
port link-type trunk //Specify the interface as a trunk interface.
port trunk allow-pass vlan 10 20 30 40 //Allow packets with a VLAN ID ranging from
VLAN 10 to VLAN 20 to pass through.
interface GigabitEthernet0/2/2
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20
interface GigabitEthernet0/2/3
portswitch
port link-type trunk
port trunk allow-pass vlan 30 40
Digital Subscriber Line (DSL) is a technology that provides digital connections over the copper
wire or a local telephone network. xDSL refers to various DSL technologies. It is a family of
bandwidth-efficient modulation techniques developed to achieve extremely high data transfer
rates over twisted-pair cables. The ATN 905 supports VDSL2, an xDSL technology. VDSL2 is
an extension to VDSL1. In this scenario, the upstream interface on ATN905-ATN905SmallCellSiteB-002 can be a VDSL2 or Ethernet interface.
l
If the upstream interface is a VDSL2 interface, perform the following steps:
Configuring ATN905-ATN905-SmallCellSiteB-002
interface xdsl 0/2/0
quit
interface virtual-ethernet 0/2/0
quit
interface dsl-group 0/2/0
add xdsl 0/2/0
dsl-group enable
bind virtual ethernet 0/2/0
quit
interface virtual-ethernet 0/2/0
portswitch
port trunk allow-pass vlan 10 20 30 40
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
119
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
interface GigabitEthernet0/2/2
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20 30 40
interface GigabitEthernet0/2/3
portswitch
port link-type trunk
port trunk allow-pass vlan 30 40
interface GigabitEthernet0/2/4
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20
NOTE
In this scenario, the ATN 905 uses a VDSL2 interface to connect to a DSLAM. For detailed DSLAM
configuration, see corresponding documents of the access network.
If the upstream interface is an Ethernet interface, perform the following steps:
Configuring ATN905-ATN905-SmallCellSiteB-002
interface GigabitEthernet0/2/0
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20 30 40
interface GigabitEthernet0/2/1
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20 30 40
interface GigabitEthernet0/2/2
portswitch
port link-type trunk
port trunk allow-pass vlan 30 40
interface GigabitEthernet0/2/3
portswitch
port link-type trunk
port trunk allow-pass vlan 10 20
Configuring ATN910-MacroCellSite-003
interface GigabitEthernet0/2/0.1
vlan-type dot1q 10 //Configure a VLAN for the dot1q VLAN tag termination subinterface.
mpls l2vc 11.0.0.31 510 control-word raw
mpls l2vc 11.0.0.32 511 control-word raw secondary
mpls l2vpn redundancy master
mpls l2vpn reroute delay 500
mpls l2vpn stream-dual-receiving
mpls l2vpn arp-dual-sending
interface GigabitEthernet0/2/0.2
vlan-type dot1q 20
mpls l2vc 11.0.0.33 512 control-word raw
mpls l2vc 11.0.0.34 513 control-word raw secondary
mpls l2vpn redundancy master
mpls l2vpn reroute delay 500
mpls l2vpn stream-dual-receiving
mpls l2vpn arp-dual-sending
interface GigabitEthernet0/2/0.3
vlan-type dot1q 30
mpls l2vc 11.0.0.35 514 control-word raw
mpls l2vc 11.0.0.36 515 control-word raw secondary
mpls l2vpn redundancy master
mpls l2vpn reroute delay 500
mpls l2vpn stream-dual-receiving
mpls l2vpn arp-dual-sending
interface GigabitEthernet0/2/0.4
vlan-type dot1q 40
mpls l2vc 11.0.0.37 516 control-word raw
mpls l2vc 11.0.0.38 517 control-word raw secondary
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
120
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
mpls
mpls
mpls
mpls
l2vpn
l2vpn
l2vpn
l2vpn
5 Solution 3: Native Ethernet Access
redundancy master
reroute delay 500
stream-dual-receiving
arp-dual-sending
5.6 Deploying QoS
You can deploy quality of service (QoS) on a carrier network to provide differentiated QoS
assurance as required.
5.6.1 Configuring QoS
You can configure simple traffic classification to classify data packets into multiple priorities
or service classes, and therefore to provide differentiated services.
Configuration Roadmap
Traditional IP networks in best-effort mode are mainly used to carry data services, and the service
quality seems insignificant. However, with fast development of IP-oriented Internet services and
emerging of various new services (such as VoIP and VPN services), IP networks have changed
from pure data networks to bearer networks with commercial values. Therefore, IP networks
must ensure the quality of each type of service that they carry. Against this backdrop, quality of
service (QoS) is developed.
The ATN 905 functions as a small-cell base station bearer device or enterprise private line
Ethernet demarcation device (EDD). When configured with simple traffic classification, the
ATN 905 can manage the traffic. Priority mapping based on simple traffic classification indicates
that the priority of the packets on a network is mapped into the packets of another network so
that the packets of the first network can be transmitted on the second network based on the
original or user-defined packet priority. That is, on the ingress, the packets obtain the priority
and color for scheduling on the ATN equipment based on the values of the DSCP and 802.1p
fields. After being scheduled on the ATN equipment, the outgoing packets obtain the values of
the priority fields (such as DSCP and 802.1p) for encapsulation based on the above-mentioned
priority and color. In this manner, during traffic management, packets of different services join
different queues, ensuring differentiated scheduling.
To configure simple traffic classification, do as follows:
l
Bind the default DiffServ domain to service interfaces (including main interfaces and
subinterfaces) of the ATN 905 to configure simple traffic classification.
Data Planning
NOTE
Set these parameters based on the actual network conditions such as network scale and topology. The
following recommended values in this example are only for reference.
Issue 03 (2013-11-22)
Parameter
Value
Description
trust upstream
default
Bind the DiffServ domain to
an interface.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
121
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Application Process
l
For ATN905-SmallCellSiteA-001
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN905-SmallCellSiteB-002
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
interface GE0/2/1.2
trust upstream default
interface GE0/2/1.3
trust upstream default
interface GE0/2/2
trust upstream default
interface GE0/2/3
trust upstream default
For ATN910-MacroCellSite-003
interface GE0/2/0.2
trust upstream default
interface GE0/2/0.3
trust upstream default
5.7 Deploying the Clock
You are advised to use a clock synchronization solution based on actual clock synchronization
requirements.
5.7.1 Configuration Roadmap
Synchronization includes frequency synchronization and phase synchronization. In this solution,
you are advised to configure synchronous Ethernet and IEEE 1588v2 on the ATN 905 to achieve
frequency synchronization and phase synchronization respectively.
To ensure that most services run normally on a current communication network, devices on the
entire network should keep the frequency or phase difference within a permitted range. That is,
synchronization, either frequency synchronization or phase synchronization, must be ensured
on the network. Frequency synchronization (also known as clock synchronization) indicates that
signals retain certain relationships with respect to the phase. That is, the phase difference between
signals is constant. Phase synchronization (also known as time synchronization) indicates that
signals have the same frequency and phase. That is, there is no phase difference between signals.
For example, if two watches always indicate the same time, they are in phase synchronization;
if the two watches always have a constant time difference (such as 6 hours), they are in frequency
synchronization. In the IP RAN scenario, the ATN equipment needs to support frequency or
phase synchronization to meet the requirements of base stations.
Mainstream PSN-based synchronization technologies in the industry include IEEE 1588v2 and
synchronous Ethernet. In this solution, you are advised to configure synchronous Ethernet and
IEEE 1588v2 on the ATN 905 to achieve frequency synchronization and phase synchronization
respectively.
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
122
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Figure 5-12 Networking diagram for clock deployment
Micro/Pico
Micro/Pico
BITS
GE0/2/2
pri 20
GE0/2/1
GE0/2/3
GE0/2/2
GE0/2/1
pri 20
GE0/2/0 GE0/2/0
ASG
pri 10
RSG
GE0/2/3
Clock Tracking Path
pri n
Priority of a reference clock source at a port
The preceding figure shows how to configure a clock. The configuration roadmap is as follows:
l
Enable synchronous Ethernet and IEEE 1588v2 for the ATN 905, so that the ATN 905 can
track the upstream clock information and time information, and send them to base stations.
5.7.2 Data Planning
This topic describes data planning for clock deployment.
l
For synchronous Ethernet, configure clock signal priorities in the local priority list, and
enable synchronization status message (SSM) control.
NOTE
For synchronous Ethernet clock synchronization, a clock source is selected based on the following
descending order of priority: SSM clock quality, local priority setting, and clock source type.
l The SSM clock quality levels are in the following descending order: primary reference clock (PRC),
SSUA, SSUB, SDH equipment clock (SEC), and DNU. A source for which no quality level is defined,
and a clock source with quality level being DNU, are not be selected during source selection.
l The local priority is configured as follows: The value range is 1 to 255, and a smaller value indicates
a higher priority.
For IEEE 1588v2, use the best master clock (BMC) algorithm.
NOTE
When the BMC algorithm is used by a 1588v2-enabled device for master clock selection, priority1 of each
candidate time source is compared first, then the clock class, clock accuracy, and priority2. If priority1 of
candidate time sources is the same, the clock class is compared, and so on. The time source with the highest
priority is selected as the master clock.
Table 5-5 Data planning for synchronous Ethernet time synchronization
NE Name
Parameter
Value
Remarks
ATN905SmallCellSiteA-001
Local priority
list
20
ATN905SmallCellSiteB-002
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
123
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
NE Name
Parameter
Value
Remarks
ATN910MacroCellSite-003
Clock output
port
GE0/2/2
Connects to a base station.
GE0/2/3
Table 5-6 Data planning for IEEE 1588v2 time synchronization
NE Name
Parameter
Value
Remarks
ATN905-SmallCellSiteA-001
Port delay
measurement
mechanism
delay
The mechanism is
recommended to be
set consistently
networkwide.
NE type
BC
The networkwide BC
mode is
recommended.
Ring network
asymmetry automeasurement
enable
Automatically adjusts
the length difference
between transmit and
receive fibers when
ring network
protection switching
occurs for restoration.
Clock output port
GE0/2/2
Connects to a base
station.
ATN905-SmallCellSiteB-002
ATN910-MacroCellSite-003
GE0/2/3
5.7.3 Configuring Synchronous Ethernet to Achieve Frequency
Synchronization
To achieve frequency synchronization on a network, use synchronous Ethernet.
Configure NE ATN905-SmallCellSiteA-001
clock ethernet-synchronization enable //Enables global synchronous Ethernet in the
system view.
clock ssm-control on //Configures SSM for source selection. By default, SSM is
enabled for an ATN NE.
interface GigabitEthernet0/2/1
clock priority 20//Assigns a clock priority to the interface. This will affect
clock selection in the inbound direction on the local end. A smaller value
indicates a higher priority. Assigning the highest priority to each interface on
the shortest path for clock signal transmission is recommended.
clock synchronization enable//Enables synchronous Ethernet for an interface.
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
124
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
Configure NE ATN905-SmallCellSiteB-002
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock priority 20
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
interface GigabitEthernet0/2/2
clock synchronization enable
interface GigabitEthernet0/2/3
clock synchronization enable
Configure NE ATN910-MacroCellSite-003
clock ethernet-synchronization enable
clock ssm-control on
interface GigabitEthernet0/2/0
clock synchronization enable
interface GigabitEthernet0/2/1
clock synchronization enable
5.7.4 Configuring IEEE 1588v2 to Achieve Time Synchronization
After frequency synchronization is achieved on a network using synchronous Ethernet, use IEEE
1588v2 to achieve time synchronization on the network.
Configure NE ATN905-SmallCellSiteA-001
ptp enable //Enables global IEEE 1588v2.
ptp device-type bc //Specifies the BC mode for all devices.
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay //Configures the delay measurement mechanism of a
device as delay which calculates the time difference based on the link delay of the
master and slave clocks.
ptp enable //Enables IEEE 1588v2 for the interface.
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN905-SmallCellSiteB-002
ptp enable
ptp device-type bc
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/2
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/3
ptp delay-mechanism delay
ptp enable
Configure NE ATN910-MacroCellSite-003
ptp enable
ptp device-type bc
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
125
ATN 905 Multi-Service Access Equipment
Configuration Guide (CLI)
5 Solution 3: Native Ethernet Access
interface GigabitEthernet0/2/0
ptp delay-mechanism delay
ptp enable
interface GigabitEthernet0/2/1
ptp delay-mechanism delay
ptp enable
Issue 03 (2013-11-22)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
126
Anda mungkin juga menyukai
- Manual Ne40 HuaweiDokumen474 halamanManual Ne40 HuaweibigdrsmithBelum ada peringkat
- ATN 910&910I&910B&950B V200R003C00 Product Description 01 (CLI)Dokumen119 halamanATN 910&910I&910B&950B V200R003C00 Product Description 01 (CLI)Randy DookheranBelum ada peringkat
- RTN 900 V100R008C10 Per-NE L3VPN Configuration Guide 01Dokumen127 halamanRTN 900 V100R008C10 Per-NE L3VPN Configuration Guide 01Paulo DembiBelum ada peringkat
- RTN 950 V100R011C10 Product Description 02 PDFDokumen334 halamanRTN 950 V100R011C10 Product Description 02 PDFCorreat0% (1)
- IP Multimedia Subsystem A Complete Guide - 2020 EditionDari EverandIP Multimedia Subsystem A Complete Guide - 2020 EditionBelum ada peringkat
- 00479814-ME60 Configuration Guide - Security (V100R006C05 - 05)Dokumen241 halaman00479814-ME60 Configuration Guide - Security (V100R006C05 - 05)Faisal NazirBelum ada peringkat
- RTN 950 V100R005C00 Maintenance Guide 03Dokumen949 halamanRTN 950 V100R005C00 Maintenance Guide 03Jim PeenBelum ada peringkat
- ATN 910&910I&910B&950B V200R003C10 Emergency Maintenance 02 (CLI)Dokumen39 halamanATN 910&910I&910B&950B V200R003C10 Emergency Maintenance 02 (CLI)Miky CCisBelum ada peringkat
- Configuration Guide - MPLS (V600R003C00 - 01)Dokumen669 halamanConfiguration Guide - MPLS (V600R003C00 - 01)Анатолий ПетьковBelum ada peringkat
- Imanager U2000 Unified Network Management System - Planning Guide PDFDokumen227 halamanImanager U2000 Unified Network Management System - Planning Guide PDFboewulfBelum ada peringkat
- I Manager HuaweiDokumen289 halamanI Manager HuaweiArief MahdanBelum ada peringkat
- Imanager U2000 V200R014C60 Web LCT User Guide 01 PDFDokumen144 halamanImanager U2000 V200R014C60 Web LCT User Guide 01 PDFGrover David Perez HuancaBelum ada peringkat
- MA5608TDokumen2 halamanMA5608TRodrigovitchBelum ada peringkat
- Configuration Guide - MPLS (V600R003C00 - 02)Dokumen642 halamanConfiguration Guide - MPLS (V600R003C00 - 02)nuriez1906Belum ada peringkat
- Client Software Installation Guide - (V100R002C01 - 06)Dokumen108 halamanClient Software Installation Guide - (V100R002C01 - 06)selnet_hwBelum ada peringkat
- CX600 V600R007C00 Commission Guide 04 PDFDokumen180 halamanCX600 V600R007C00 Commission Guide 04 PDFAmit AgrawalBelum ada peringkat
- MA5600&MA5603 V300R003C05 Configuration Guide 09Dokumen384 halamanMA5600&MA5603 V300R003C05 Configuration Guide 09Jaime ColvatelBelum ada peringkat
- RTN950ADokumen2 halamanRTN950AClaire100% (1)
- OptiX PTN 950 Packet Transport Platform Product BrochureDokumen6 halamanOptiX PTN 950 Packet Transport Platform Product BrochureJaime JaraBelum ada peringkat
- 5OBG001205 MA5680-T GPON Service ConfigurationDokumen32 halaman5OBG001205 MA5680-T GPON Service ConfigurationMohamed GhazalaBelum ada peringkat
- Configuration Guide - IP Services (V600R003C00 - 01)Dokumen386 halamanConfiguration Guide - IP Services (V600R003C00 - 01)Анатолий ПетьковBelum ada peringkat
- Configuration Guide Huawei - QoSDokumen260 halamanConfiguration Guide Huawei - QoSSkynet - BurundiBelum ada peringkat
- SmartAX MA5694 - MA5698Dokumen5 halamanSmartAX MA5694 - MA5698Kawakif Rofii SiregarBelum ada peringkat
- Imaster NCE-IP V100R022C10 Product Description (x86) 03-EDokumen723 halamanImaster NCE-IP V100R022C10 Product Description (x86) 03-Eabournaud100% (1)
- AgilePOL SolutionDokumen23 halamanAgilePOL SolutionFreddy Ramires AguirreBelum ada peringkat
- ATN 910&910I&910B&950B V200R003C10 Hardware Description 01 (CLI)Dokumen349 halamanATN 910&910I&910B&950B V200R003C10 Hardware Description 01 (CLI)Miky CCisBelum ada peringkat
- PTN Configuration GuideDokumen42 halamanPTN Configuration GuideAlex Geovanni NuñezBelum ada peringkat
- MA5600T & MA5603T & MA5608T V800R016C00 Product Description PDFDokumen68 halamanMA5600T & MA5603T & MA5608T V800R016C00 Product Description PDFyura_saskevychBelum ada peringkat
- MPLS VPNL3Dokumen14 halamanMPLS VPNL3Son Vu TruongBelum ada peringkat
- RTN 950 IDU Hardware DescriptionDokumen915 halamanRTN 950 IDU Hardware DescriptionhekriBelum ada peringkat
- 2 Pon Gepon Olt MaunalDokumen71 halaman2 Pon Gepon Olt MaunalLuiz GustavoBelum ada peringkat
- RTN 905 1E&2E V100R006C10 Commissioning Guide 02. (Configure Basic) PDFDokumen180 halamanRTN 905 1E&2E V100R006C10 Commissioning Guide 02. (Configure Basic) PDFROUERN VannakBelum ada peringkat
- Huawei NE40E Router Quick Ordering Guide (2012!10!30)Dokumen41 halamanHuawei NE40E Router Quick Ordering Guide (2012!10!30)sandeepgona100% (1)
- Special Topic - VLAN&QinQ (V1.0)Dokumen90 halamanSpecial Topic - VLAN&QinQ (V1.0)Ajit PatelBelum ada peringkat
- MA5603T Product Description (GPON)Dokumen90 halamanMA5603T Product Description (GPON)Atia Akbar100% (3)
- Etx-2 MN 0 Manual Etx 203ADokumen932 halamanEtx-2 MN 0 Manual Etx 203AKrustytfeBelum ada peringkat
- MA5616 Configuration Guide (V800R308C01 - 04) PDFDokumen553 halamanMA5616 Configuration Guide (V800R308C01 - 04) PDFAlex Matias100% (1)
- RTN 900 V100R005C01 Configuration Guide 04Dokumen2.319 halamanRTN 900 V100R005C01 Configuration Guide 04EugeneBelum ada peringkat
- Huawei RTN 905e BrochureDokumen2 halamanHuawei RTN 905e BrochureWilliam FernandesBelum ada peringkat
- MA5600T&MA5603T&MA5608T Hardware Description 08Dokumen762 halamanMA5600T&MA5603T&MA5608T Hardware Description 08Thunder-Link.com86% (7)
- Huawei OptiX Metro 1000 Commissioning Guide (V300R007)Dokumen143 halamanHuawei OptiX Metro 1000 Commissioning Guide (V300R007)Thunder-Link.comBelum ada peringkat
- OptiX RTN 980L System Commissioning (Web LCT)Dokumen88 halamanOptiX RTN 980L System Commissioning (Web LCT)Jcarlo RodriguezBelum ada peringkat
- FTTH Manual Huawei PDFDokumen84 halamanFTTH Manual Huawei PDFSatish VermaBelum ada peringkat
- NE40E-X1&NE40E-X2 Product Description (V600R003C00 - 02)Dokumen76 halamanNE40E-X1&NE40E-X2 Product Description (V600R003C00 - 02)Amal ElourakBelum ada peringkat
- Backhauling / Fronthauling for Future Wireless SystemsDari EverandBackhauling / Fronthauling for Future Wireless SystemsKazi Mohammed Saidul HuqBelum ada peringkat
- Signaling in Telecommunication NetworksDari EverandSignaling in Telecommunication NetworksPenilaian: 4 dari 5 bintang4/5 (1)
- VoLTE and ViLTE: Voice and Conversational Video Services over the 4G Mobile NetworkDari EverandVoLTE and ViLTE: Voice and Conversational Video Services over the 4G Mobile NetworkBelum ada peringkat
- ATN 910&910I&910B&950B V200R003C10 Configuration Guide 01 (CLI) PDFDokumen4.653 halamanATN 910&910I&910B&950B V200R003C10 Configuration Guide 01 (CLI) PDFgooblin100% (2)
- ATN 910&910I&910B&950B V200R003C10 Configuration Guide 01 (U2000)Dokumen636 halamanATN 910&910I&910B&950B V200R003C10 Configuration Guide 01 (U2000)Christopher Mendes83% (6)
- CloudEngine 12800 V100R001C00 Configuration Guide - Reliability 03Dokumen126 halamanCloudEngine 12800 V100R001C00 Configuration Guide - Reliability 03aarnulfoBelum ada peringkat
- Configuration Guide Basic Configurations (V200R001C01 - 03)Dokumen188 halamanConfiguration Guide Basic Configurations (V200R001C01 - 03)Andrés Marroquín75% (8)
- CloudEngine 6800&5800 V100R001C00 Configuration Guide - Basic Configuration 04 PDFDokumen201 halamanCloudEngine 6800&5800 V100R001C00 Configuration Guide - Basic Configuration 04 PDFMenganoFulanoBelum ada peringkat
- CloudEngine 6800&5800 V100R001C00 Configuration Guide - Interface Management 04 PDFDokumen48 halamanCloudEngine 6800&5800 V100R001C00 Configuration Guide - Interface Management 04 PDFMenganoFulanoBelum ada peringkat
- CloudEngine 6800&5800 V100R001C00 Configuration Guide - Device Management 04 PDFDokumen146 halamanCloudEngine 6800&5800 V100R001C00 Configuration Guide - Device Management 04 PDFMenganoFulanoBelum ada peringkat
- Check List: Site ID: Region: DateDokumen16 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- Check List: Site ID: Region: DateDokumen6 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- Check List: Site ID: Region: DateDokumen16 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- Check List: Site ID: Region: DateDokumen6 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- Check List: Site ID: Region: DateDokumen6 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- Line No: Project Pool Name Item No.: Feedback DateDokumen260 halamanLine No: Project Pool Name Item No.: Feedback DateSalman IqbalBelum ada peringkat
- Check List: Site ID: Region: DateDokumen16 halamanCheck List: Site ID: Region: DateSalman IqbalBelum ada peringkat
- External Alarm SchematicDokumen2 halamanExternal Alarm SchematicSalman IqbalBelum ada peringkat
- ALM-26522 RF Unit RX Channel RTWPRSSI UnbalancedDokumen2 halamanALM-26522 RF Unit RX Channel RTWPRSSI UnbalancedSalman IqbalBelum ada peringkat
- PMR ETL Summary Report (Equipment Included)Dokumen9 halamanPMR ETL Summary Report (Equipment Included)Salman IqbalBelum ada peringkat
- Yar MHMD What Are The Standards of The G'sDokumen2 halamanYar MHMD What Are The Standards of The G'sSalman IqbalBelum ada peringkat
- Site A Site B Migration New BH TechnologyDokumen4 halamanSite A Site B Migration New BH TechnologySalman IqbalBelum ada peringkat
- Access Control Testing AlarmDokumen5 halamanAccess Control Testing AlarmSalman IqbalBelum ada peringkat
- Upeu Ext1 TO Cpmu 65101 65108 65125 65103 Upeu Ext0 TO Cpmu 65104 65105 65109Dokumen4 halamanUpeu Ext1 TO Cpmu 65101 65108 65125 65103 Upeu Ext0 TO Cpmu 65104 65105 65109Salman IqbalBelum ada peringkat
- STC 4G1 Project (EMU) Alarm DescriptionDokumen1 halamanSTC 4G1 Project (EMU) Alarm DescriptionSalman IqbalBelum ada peringkat
- What Are The Standards of The G'sDokumen2 halamanWhat Are The Standards of The G'sSalman IqbalBelum ada peringkat
- PMR InformationDokumen16 halamanPMR InformationSalman IqbalBelum ada peringkat
- Priority of The Sites, As Shown With Detailed in Tab.1: High Priority PMR PriorityDokumen47 halamanPriority of The Sites, As Shown With Detailed in Tab.1: High Priority PMR PrioritySalman IqbalBelum ada peringkat
- MC AflajDokumen1 halamanMC AflajSalman IqbalBelum ada peringkat
- 2.1.4.5 Lab - Configure Extended VLANs, VTP, and DTP (Instructor Version)Dokumen18 halaman2.1.4.5 Lab - Configure Extended VLANs, VTP, and DTP (Instructor Version)c6722504100% (3)
- Datasheet Earth-4220RF Rev12210000Dokumen2 halamanDatasheet Earth-4220RF Rev12210000HeliumByBGC AccountsBelum ada peringkat
- Module 9 CSS G11 2nd SemDokumen36 halamanModule 9 CSS G11 2nd SemElla Mae GadianBelum ada peringkat
- 7.3.7 Lab - View The Switch Mac Address TableDokumen4 halaman7.3.7 Lab - View The Switch Mac Address TableJad Abou ZeidBelum ada peringkat
- TC1765 OmniPCX Office SIP Trunking Noteworthy Addresses en Ed02Dokumen14 halamanTC1765 OmniPCX Office SIP Trunking Noteworthy Addresses en Ed02Aitor SantiagoBelum ada peringkat
- Setting Up WAN Emulation Using WAN-Bridge Live-CD v1.10Dokumen8 halamanSetting Up WAN Emulation Using WAN-Bridge Live-CD v1.10Prabhat MishraBelum ada peringkat
- Datasheet Live Titanium 20 SeriesDokumen2 halamanDatasheet Live Titanium 20 SeriesNomsa MwayengaBelum ada peringkat
- ADH-STM-1 AXE Exchange TerminalDokumen84 halamanADH-STM-1 AXE Exchange TerminalsukanganulhoBelum ada peringkat
- ZXA10 C300V2.0.1P3 Patch Release NotesDokumen36 halamanZXA10 C300V2.0.1P3 Patch Release Notesivanpgnic6337Belum ada peringkat
- OpenStack Networking CookbookDokumen279 halamanOpenStack Networking Cookbooklemos_pabBelum ada peringkat
- Juniper Networks - SRX Getting Started - Configure Chassis Cluster (High Availability) On A SRX240 Device - Knowledge BaseDokumen4 halamanJuniper Networks - SRX Getting Started - Configure Chassis Cluster (High Availability) On A SRX240 Device - Knowledge BaseDeepak RainaBelum ada peringkat
- Huawei CloudEngine 5800&6800&7800&8800 Series IStack Technology White PaperDokumen96 halamanHuawei CloudEngine 5800&6800&7800&8800 Series IStack Technology White PaperJhonatan RyBelum ada peringkat
- TE - SemVI - Cryptography - System SecurityDokumen4 halamanTE - SemVI - Cryptography - System SecuritySURABHI NAIK192074Belum ada peringkat
- Modulation and Frequency Synthesis X Digital Wireless RadioDokumen233 halamanModulation and Frequency Synthesis X Digital Wireless Radiolcnblzr3877Belum ada peringkat
- Access Network DesignDokumen21 halamanAccess Network Designmcclaink06Belum ada peringkat
- SkyEdge II-c 2G 3G ATP - 0217Dokumen13 halamanSkyEdge II-c 2G 3G ATP - 0217Jhon Frayser Guizado GonzalesBelum ada peringkat
- Netprofiler: Profiling Wide-Area Networks Using Peer CooperationDokumen6 halamanNetprofiler: Profiling Wide-Area Networks Using Peer CooperationNghĩa ZerBelum ada peringkat
- ValueFirst AirMail Data Sheet v1.2Dokumen4 halamanValueFirst AirMail Data Sheet v1.2Divya SinghBelum ada peringkat
- SFP Quick Reference Guide (Switch)Dokumen3 halamanSFP Quick Reference Guide (Switch)juanBelum ada peringkat
- Owasp WiresharkDokumen76 halamanOwasp WiresharkAhmad FleifelBelum ada peringkat
- GSM P&O Training Material For Special Subject-Handover Algorithms - ZTEDokumen49 halamanGSM P&O Training Material For Special Subject-Handover Algorithms - ZTElikamele100% (2)
- Failover 2 ISP Load Balancing PCC Tanpa NetwatchDokumen3 halamanFailover 2 ISP Load Balancing PCC Tanpa Netwatchsuyetno100% (1)
- Routing Protocols OSPF and RIPDokumen8 halamanRouting Protocols OSPF and RIPMuhammad JawadBelum ada peringkat
- Lab 1 - BGP PeeringDokumen72 halamanLab 1 - BGP PeeringSnowie OWBelum ada peringkat
- Cambium Networks Data Sheet Cnmatrix EX3000 Series SwitchesDokumen11 halamanCambium Networks Data Sheet Cnmatrix EX3000 Series Switchesrf.waveguideBelum ada peringkat
- Generations of Mobile CommunicationDokumen5 halamanGenerations of Mobile CommunicationAshna KakkarBelum ada peringkat
- Shalom Hills International SchoolDokumen3 halamanShalom Hills International SchoolNiyatiBelum ada peringkat
- Netsh Network Settings From Command Line in Windows 98 To Windows 7Dokumen3 halamanNetsh Network Settings From Command Line in Windows 98 To Windows 7fanepixBelum ada peringkat
- A100K10803 IP Substation Installation ConfigurationDokumen32 halamanA100K10803 IP Substation Installation ConfigurationJoseLuisBelum ada peringkat
- Daikin Wireless LAN Connecting Adapter Installation ManualDokumen2 halamanDaikin Wireless LAN Connecting Adapter Installation ManualMikiBelum ada peringkat