Yasser Auda CCIEv5 IPv6 FHS Quick Guide
Diunggah oleh
Charly GlezHak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Yasser Auda CCIEv5 IPv6 FHS Quick Guide
Diunggah oleh
Charly GlezHak Cipta:
Format Tersedia
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
IPV6 NDP introduction before understanding First Hop Security
Frist we need to fully understand what protocol IPv6 use to get mac address and other information from
neighbors and routers? IPv6 use NDP for that, so what is NDP ?
IPv6 NDP neighbor discovery protocol replaces ARP in IPv6 networks
NDP help in many things lets overview it in the following examples:
Example 1:
1-Host assign to itself Link Local address using FE80::/10 with eui-64
2-Host send NS Neighbor Solicitation ( like arp request) saying : anyone using my link local address?
If no reply so address is unique.
This process called DAD Duplicate Address Detection
Example 2:
1-when Host want to know mac address for ipv6 address will send NS saying: what is mac address for
this ipv6 address?
2-another Host will send NA Neighbor Advertisement (like arp reply) saying: I have this ipv6 address and
this my mac address.
Example 3:
Host can use NDP to detect all routers on the subnet that could be used as Default Gateway.
1-Host sends RS Router Solicitation to FF02::2 saying: any router around to use as default gateway?
2-Router send RA Router Advertisement saying: yes I am and here is my link local address
Also router will send periodically RA to FF02::1
Also if router had global unicast address ex: 2002:1:1:1::1 then he will send to hosts Prefix
2001:1:1:1::/64 and this good for SLAAC
Example 4:
NDP is useful too with SLAAC stateless address auto configuration (Auto configuration = mini DHCP)
When host knew prefix (network address) from router, host will create host address (eui-64) and use
this prefix address to have complete ipv6 address
Remember DHCPv6 is no longer responsible to provide default gateway address, its default gateway
itself responsibility to announce his self as default gateway to hosts
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Notes:
NDP or ND as we used to call it create Neighbor Cache which is equivalent to an ARP cache or
Table in IPv4 (we can display it with show ipv6 neighbors).
Typing no ipv6 unicast routing will disable the router ability to be forward ipv6 unicast packets
& ipv6 routing protocols and also will disable the sending of ICMPv6 RA messages .
As IPv4 ARP we can create static entry to be stored in arp cache ( ipv6 neighbor Cache ) by
typing : Ipv6 neighbor ipv6-address interface-type interface-number hardware-address
The neighbor cache can be cleared by typing : clear ipv6 neighbors
If we type show ipv6 interface we can see many NP parameters
Remember for later configuration to make our router as DHCP relay agent we type:
Int f0/0
Ipv6 dhcp relay dest 2001:5:6:7::2 (where 2001:5:6:7::2 is DHCPv6 server address)
(Dhcp client ------ f0/0 router f0/1--------dhcp server)
We can change many of these parameters under interfaces
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
RA interval is the amount of time in seconds between consecutive RA messages (default is 200 seconds)
We can change using ipv6 nd ra interval command.
RA Lifetime define how long host should consider this router as a valid default Gateway (default is 1800
seconds = 30 minutes). We can change using ipv6 nd ra lifetime command.
Changing M & O flags :
M Flag (managed address configuration flag) tell host that is configured to obtain its configuration
information automatically using SLACC or DHCPv6
0 = use SLACC (default )
1= use DHCPv6
To change to 1 ( use DHCPv6) we type
Ipv6 nd managed-config-flag
O Flag (Other configuration flag) inform host to get additional information such as DNS info from
DHCPv6 server or not
0 = no additional info available from DHCPv6
1= use DHCPv6 server to get additional info
To change to 1 ( use DHCPv6) we type
Ipv6 other-config-flag
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
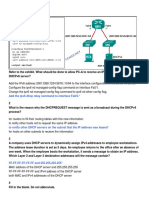
Lets check the following topology to understand more about ipv6 behavior inside our LAN:
R3 act as PC , From R3 point of view R1 OR R2 will be his first Hop to reach external networks
R1 will act as mini DHCP and send ipv6 address to R3
R3
Int f0/1
ipv6 add autoconfig default
Above command will make this interface assigned ipv6 address from same prefix R1 will send using RA
And also R3 will consider R1 default gateway since we add the keyword default
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
You can always use Debug ipv6 nd to see all nd messages
To prevent R2 from sending RA to R3 and maybe act as Default gateway we type :
R2
Int f0/1
Ipv6 nd ra suppress
Before we finish this introduction to NDP lets check the following example about General Prefix
Concept in IPv6 and how its work .
R1 Connected to R2 using f0/0
interface FastEthernet0/0
no ip address
duplex auto
speed auto
ipv6 address 2001:10:1:12::1/64
R2
ipv6 general-prefix MyGlobal 2001:10:1::/48
interface FastEthernet0/0
no ip address
duplex auto
speed auto
ipv6 address MyGlobal ::12:0:0:0:2/64
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Threats regarding all what we learned so far about IPv6 NDP:
-spoof router, receive two RA one from fake router and give wrong default gateway
-spoof DHCP server and send bogus offers
-poison router ND Cache
-overload router ND cache (send packets to entire /64 range)
Tools used to attack your IPv6 Network including your First Hop:
THC IPv6 Attack Toolkit
SI6 Networks IPv6 Toolkit
Evil FOCA
halfscan6, Scan6, CHScanner
Scapy, SendIP, ISIC6, Packit, Spak6
6tunneldos, 4to6ddos, imps6-tools
Credits for knowing these tools goes to Scott Hogg CCIE #5133 author of Cisco Press, 2009. IPv6
Security, By Scott Hogg and Eric Vyncke.
Evil Foca is a tool designed for pen testers and security auditors to perform security testing in IPv4/ IPv6
data networks. The tool is capable to do different attacks such as: MITM on IPv4 networks using ARP
Spoofing and DHCP ACK injection, MITM on IPv6 networks using Neighbor Advertisement Spoofing,
SLAAC Attack, fake DHCPv6, DoS (Denial of Service) on IPv4 networks using ARP Spoofing, DoS (Denial of
Service) on IPv6 networks using SLAAC attack and DNS hijacking.
6
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
So its time to secure our Frist Hop Topology and this is what we call
First Hop Security FHS.
IPv6 First Hop Security ( IPv6 FHS)
IPv6 FHS First Hop Security are also called IPv6 Policies which can be applied to interface or VLAN level.
FHS come with Software policy Database where polices stored .
IPv6 snooping acts as a container policy that enables most of the features available with FHS in IPv6.
Most FHS features are configured in a two-step : firstly you define a policy which describes the behavior
of the feature, secondly you apply this policy to a VLAN or interface.
FHS Features:
IPv6 RA Guard
IPv6 DHCP Guard
IPV6 Snooping (Binding integrity Guard) & Device Tracking
IPv6 Source Guard
IPv6 Destination Guard
IPv6 Prefix Guard
IPv6 PACL
SeND Protocol
IPv6 RA Guard
Used to prevent Router and Prefix Spoofing
The IPv6 RA Guard feature does not offer protection in environments where IPv6 traffic is tunneled.
This feature is supported only in hardware when the ternary content addressable memory (TCAM) is
programmed.
This feature can be configured on a switch port interface in the ingress direction.
This feature supports host mode and router mode.
This feature is supported only in the ingress direction; it is not supported in the egress direction.
This feature is not supported on EtherChannel and EtherChannel port members.
This feature is not supported on trunk ports with merge mode.
This feature is supported on auxiliary VLANs and private VLANs (PVLANs).
Packets dropped by the IPv6 RA Guard feature can be spanned.
If the platform ipv6 acl icmp optimize neighbor-discovery command is configured, the IPv6 RA
Guard feature cannot be configured and an error message will be displayed. This command adds default
global Internet Control Message Protocol (ICMP) entries that will override the RA guard ICMP entries.
IPv6 RA Guard ( RA guard should be deployed on the first hop L2 switch):
RA messages they are the only way to get default gateway info to host in the network (beside static
configuration). DHCPv6 does not carry this information in his messages unlike DHCPv4. , it is wrong if
some host sends RA messages because he is then practically trying to take the role of default gateway
away from router. Configuring RA Guard on all switch ports except port that heads to router we
prevented rouge RA advertisements on that segment.
interface Ethernet0/1
ipv6 nd raguard
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
This configuration will drop any RAs received on this interface thus enforcing the policy that this port
only connects to the end hosts. We will applied to all interfaces connected to hosts.
But what about if we need a configuration that will permit RAs only if they have the M and O bits set,
and enforce that the subsequent DHCP advertised prefix is within the company's range of
2001:db8:cafe::/48 : , we will need to configure RA Guard with Policy style , check the following example
ipv6 nd raguard policy ONLY-DHCPv6-RAs
device-role router
role 'router' allows the RAs through but triggers deep inspection
managed-config-flag on
The RAs that we let through have to have Managed flag set.
other-config-flag on
he Other configuration flag also needs to be set.
match ra prefix-list IPv6-SPACE
Only allow the RAs that advertise the prefixes from our own address space
interface Ethernet0/0
switchport access vlan 100
switchport mode access
ipv6 nd raguard attach-policy ONLY-DHCPv6-RAs
Attach the policy to the port connecting to the router
!
ipv6 prefix-list IPv6-SPACE permit 2001:db8:cafe::/48 ge 64 le 64
Logging dropped packets
It is useful to be able to see which packets are being dropped by FHS. by default packets are dropped
silently. In order to see the packets are being dropped use this command:
ipv6 snooping logging packet drop
For example here is a syslog message indicating that RA Guard has dropped an RA on a particular port:
*Jul 27 17:34:54.953: %SISF-4-PAK_DROP: Message dropped A=FE80::A8BB:CCFF:FE00:6900 G=V=100 I=Et2/0 P=NDP::RA Reason=Message unauthorized on port
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
RA Guard scenario:
All SW1 Interfaces assigned to VLAN 911
SW1
ipv6 access-list R1linklocal
permit ipv6 host FE80::1 any
ipv6 prefix-list R1slaacprefix permit 2001::/64
Create policy for R1 , I will name it R1policy:
ipv6 nd raguard policy R1policy
device-role router
match ipv6 access-list R1linklocal
match ra prefix-list R1slaacprefix
exit
create policy for hosts , I will name it Hostspolicy::
ipv6 nd ragurad policy Hostspolicy
device-role host
exit
apply to interface or vlan (interface applying override vlan applying if both exists):
vlan configuration 911
ipv6 nd ragurad attach-policy Hostspolicy
int g1/1
ipv6 nd raguard attach-policy R1policy
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
DHCPv6 Guard
Lets Remember that DHCPv6 not assign default gateway address as DHCP in IPv4 , since default
routes learned through SLAAC from RA messages. So DHCPv6 Guard Used to Prevent DHCPv6 Server
Spoofing . The DHCPv6 guard feature is not supported on Ether channel ports
Is similar to RA Guard but it blocks DHCPv6 reply messages coming from DHCPv6 servers and relays that
are on wrong ports (which means that they are rouge). it works like an Access list that block UDP port
546 on all port on the switch except port on which the DHCP server is connected. Or VLAN interface for
the subnet if there is DHCP relay configured.
Why UDP Port 546 ?
DHCP uses UDP ports 546 and 547 to initiate communication between the IPv6 client and server. If
either of these ports is in use by another application, or the ports are otherwise reserved, DHCP will not
function.
Port 546 (DHCP Client port for IPv6)
If port 546 is in use by another process, DHCP server cannot perform rogue DHCP server detection in
IPv6.
Port 547 (DHCP server port for IPv6)
If port 547 is in use by another process, DHCP server cannot communicate with DHCPv6 clients.
Configuring DHCPv6 Guard
1) Create & Assign Policy for Hosts , I will name it dhcp-client:
For the Host facing ports you dont need to do this, but if you want to explicitly configure this, thats
how you do it.
SW1(config)#ipv6 dhcp guard policy dhcp-client
SW1(config-dhcp-guard)#device-role client
SW1(config)#Interface range fa0/2-3
SW1(config-if)# switchport mode access
SW1(config-if)# ipv6 dhcp guard attach-policy dhcp-client
2) Create & assign policy for DHCP server facing port , I will name it dhcp-server:
For the server facing ports, you need create DHCPv6 Guard policy.
SW1(config)#ipv6 dhcp guard policy dhcp-server
SW1(config-dhcp-guard)#device-role server
SW1(config-dhcp-guard)#match server access-list ACL1
SW1(config-dhcp-guard)#match reply prefix-list PREF1
Notice You can also provide some extra functionality over access lists; you could block server messages
for particular addresses using an access list and you could also block some advertisements from the
DHCPv6 server blocking certain prefixes using a prefix list as shown below:
SW1(config)#ipv6 access-list ACL1
SW1(config-ipv6-acl)#permit ipv6 host FE80::1 any
10
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
SW1(config)#ipv6 prefix-list PREF1 seq 5 permit 2001::/64 le 128
SW1(config)# Interface fa0/1
SW1(config-if)#switchport mode access
SW1(config-if)# ipv6 dhcp guard attach-policy dhcp-server
DHCP Guard scenario:
By turning on IPv6 Snooping, you automatically drop the switch into Guard Mode which will turn on
DHCPv6 Guard as well as RA Guard; so none of the redirect advertisements or any DHCPv6 server
messages will get through. (You will understand this point once we explain ipv6 snooping feature)
each devive must have one of two modes :
1) Client: Sets the role of the device to client.
2) Server: Sets the role of the device to server.
Since the default mode of the switch is to guard, by default all ports configured with dhcpv6 guard will
be in client mode. Thus all ports will be dropping any dhcpv6 server messages by default.
SW1
SW1(config)#ipv6 dhcp guard policy dhcp-server
SW1(config-dhcp-guard)#device-role server
SW1(config)#int g1/1
SW1(config-if)#sw
SW1(config-if)#sw mo access
SW1(config-if)#ipv6 dhcp guard attach-policy dhcp-server
SW1(config)#ipv6 dhcp guard policy dhcp-client
SW1(config-dhcp-guard)#device-role client
11
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
SW1(config)#int range g1/2 - 3
SW1(config-if)#sw
SW1(config-if)#sw mo acc
SW1(config-if)#ipv6 dhcp guard attach-policy dhcp-client
Additional security can be achieved by assigning an access list to only permit dhcpv6 server messages
from a specific source address and Assigning a prefix-list to allow address allocation only from a known
prefix
SW1(config)#ipv6 access-list MYACL
SW1(config-ipv6-acl)#permit ipv6 host FE80::1 any
SW1(config)#ipv6 prefix-list MYPREFIX seq 5 permit 2001::/64 le 128
SW1(config)#ipv6 dhcp guard policy dhcp-server
SW1(config-dhcp-guard)#match server access-list MYACL
SW1(config-dhcp-guard)#match reply prefix-list MYPREFIX
SW1(config-dhcp-guard)#exit
IPv6 Snooping
IPv6 snooping, "binding integrity guard" is actually a "bundled" feature that combines:
RA guard / DHCP guard
IPv6 address gleaning
IPv6 ND inspection
Device Tracking
Since IPv6 snooping included the guard functions, if you enable IPv6 snooping, you do not need
to explicitly configure RA guard / DHCP guard on the same port.
The below configuration shows a default configuration for IPv6 snooping.
ipv6 snooping policy HOST
!
interface GigabitEthernet1/0/2
switchport access vlan 201
switchport mode access
ipv6 snooping attach-policy HOST
!
To verify the snooping policy you can use the show ipv6 snooping policy [policy name]
command as shown below.
FirstHopSwitch#show ipv6 snooping policy HOST
Policy HOST configuration:
security-level guard <- RA and DHCP messages are dropped
device-role node
<- Only end points are expected on this port
protocol ndp
<- Gleaning addresses from ND process
protocol dhcp
<- Gleaning addresses from DHCP
Policy host is applied on the following targets:
Target
Type Policy
Feature
Target range
Gi1/0/2
PORT HOST
Snooping
vlan all
12
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Note that when IPv6 snooping is configured the default security is set to "guard". This setting
can cause problems when the snooping policy is attached to a port that has a DHCPv6 server
connected to it. This policy setting will drop the DHCPv6 messages. To allow the DHCPv6
messages through, the port must be configured as a trusted port or a specific DHCPv6 guard
policy must be configured.
IPv6 Snooping is doing the same thing as in IPv4 , uses binding table known as ND table and tries to (
remember )bind all IPv6 addresses on the segment to particular MAC address. It does that by monitoring
DHCPv6, ND and other regular data flows. After a while ND table is having all the bindings (MAC-IPv6)
and when an intruder sends rouge NA message his MAC address does not correspond to right MAC
address from that receiver IPv6 address and he will be prevented from sending.
These categories of traffic carry information that the binding table snoops for:
ND traffic
DHCP traffic
Data traffic
NDP Address Gleaning
The NDP address gleaning feature is enabled by default when you configure the ipv6 snooping policy
global configuration command.
IPv6 DHCP Address Gleaning
The IPv6 DHCP address gleaning feature provides the ability to extract addresses from DHCP messages
and populate the binding table. The switch extracts address binding information from all messages types
of DHCPv6 exchanges (using User Datagram Protocol (UDP), ports 546 and 547)
IPv6 Data Address Gleaning
The IPv6 data address gleaning feature provides the ability to extract addresses from redirected data
traffic, to discover neighbors and to populate binding tables.
The IPv6 device tracking
feature provides IPv6 host liveness tracking so that a neighbor table can be updated when an IPv6 host
disappears. The feature tracks the liveness of the neighbors connected through the L2 switch on regular
basis in order to revoke network access privileges as they become inactive.
13
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
How to Configure IPv6 Snooping
Configuring IPv6 ND Inspection
Configures an IPv6 snooping policy and enters IPv6 snooping configuration mode.
Device(config)# ipv6 snooping policy yasserpolicy
Attaches the IPv6 snooping policy to a target.
Device(config-ipv6-snooping)# ipv6 snooping attach-policy yasserpolicy
Configuring IPv6 ND Inspection Globally
Defines the ND inspection policy name and enters ND inspection policy configuration mode.
Device(config)# ipv6 nd inspection policy yasserpolicy
Drops messages with no options, invalid options, or an invalid signature.
Device(config-nd-inspection)# drop-unsecure
Specifies the minimum security level parameter value when cryptographically generated address (CGA)
options are used.
Device(config-nd-inspection)# sec-level minimum 2
Specifies the role of the device attached to the port.
device-role {host | monitor | router}
Device(config-nd-inspection)# device-role monitor
Overrides the default tracking policy on a port. tracking {enable [reachable-lifetime {value | infinite}] |
disable [stale-lifetime {value | infinite}]}
Device(config-nd-inspection)# tracking disable stale-lifetime infinite
Configures a port to become a trusted port. trusted-port
Device(config-nd-inspection)# trusted-port
Applying IPv6 ND Inspection on an Interface
ipv6 nd inspection [attach-policy [policy policy-name] | vlan {add | except | none | remove | all} vlan
[vlan1, vlan2, vlan3...]]
Device(config)# interface fastethernet 0/0
Device(config-if)# ipv6 nd inspection
14
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Configuring IPv6 Device Tracking in Two Steps :
1-configure IPv6 Binding Table contents
Adds a static entry to the binding table database.
ipv6 neighbor binding vlan vlan-id {interface type number |ipv6-addr ess | mac-address} [tracking
[disable | enable |retry-interval value] | reachable-lifetime value]
Device(config)# ipv6 neighbor binding vlan 100 interface Ethernet 0/0 reachable-lifetime 100
Specifies the maximum number of entries that are allowed to be inserted in the binding table
cache.
ipv6 neighbor binding max-entries entries [vlan-limit number| interface-limit number | mac-limit
number]
Device(config)# ipv6 neighbor binding max-entries 100
Enables the logging of binding table main events. ipv6 neighbor binding logging
Device(config)# ipv6 neighbor binding logging
2-configure IPv6 Device Tracking
Track entries in the binding table
Device(config)#ipv6 neighbor tracking
Show ipv6 device Tracking
Configuring the IPv6 First-Hop Security Binding Table Recovery Mechanism
adds a static entry to the binding table database
Device(config)#ipv6 neighbor binding vlan 100 2001:db8::1 interface ethernet 3/0
create an entry in ipv6 prefix list
Device(config)#ipv6 prefix-list abc permit 2001:db8::/64 ge 128
enter ipv6 snooping mode
Device(config)#ipv6 snooping policy xyz
specify that destination address should be recovered from DHCP
Device(config-ipv6-snooping)#destination-glean recovery dhcp
(if looging without recovery required use destination-glean log-only)
optionally specifies that address shoudl be gleaned with dhcp and associates teh protocol with specific
ipv6 prefix list.
Device(config-ipv6-snooping)# protocol dhcp prefix-list abc
Device(config-ipv6-snooping)#exit
optionally enter destination gurad configuration mode
Device(config)# ipv6 destination-gurad policy xyz
15
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
sets the enforcement level of teh policy where alyways enforced or when system stressed only
Device(config-destguard)# enforcement stressed
Device(config-destguard)#exit
enter dhcp gurad mode
Device(config)# ipv6 dhcp guard policy server_side
sets teh role of teh device attached to the server
Device(config-dhcp-guard)# device-role server
Device(config-dhcp-guard)#exit
enter vlan configuration mode
Device(config)#vlan configuration 100
attach ipv6 snooping policy to vlan
Device(config-vlan-config)#ipv6 snooping attach-policy xyz
atatch teh destination guard policy
Device(config-vlan-config)#ipv6 destination-guard attach-policy xyz
Configuring Address Gleaning and Associating Recovery Protocols with Prefix Lists
Device(config)#ipv6 snooping policy 200
specifies that address should be gleaned with DHCP & associates a recovery protocol with the prefix list
Device(config-ipv6-snooping)#protocol dhcp prefix-list myprefix
Configuring IPv6 Prefix Glean
Device(config)#ipv6 snooping polciy yasserpolicy
Device(config-ipv6-snooping)#prefix-glean
16
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
IPv6 Source Guard
uses ND table to drop traffic from rogue sources or IPv6 addresses that are not in the binding
table.
Configuring IPv6 Source Guard
Defines an IPv6 source-guard policy name and enters switch integrated security features source-guard
policy configuration mode.
Device(config)# ipv6 source-guard policy my_sourceguard_policy
Allows hardware bridging for all data traffic sourced by a link-local address.
Device(config-sisf-sourceguard)# permit link-local
Denies data traffic from auto-configured global addresses.
Device(config-sisf-sourceguard)# deny global-autoconf
Allows hardware bridging for all data traffic on the target where the policy is applied.
Device(config-sisf-sourceguard)# trusted
Device(config)# int g1/3
Device(config-if)# ipv6 source-guard attach-policy my_source_guard_policy
17
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
IPv6 Prefix Guard
Will use information from DHCPv6 and RA messages to fill the table with valid prefixes that are
in use and it will block all other prefixes. IPv6 Prefix Guard feature works within the IPv6
Source Guard feature, enabling the device to deny traffic originated from no topologically
correct addresses. IPv6 prefix guard is often used when IPv6 prefixes are delegated to devices
(for example, home gateways) using DHCP prefix delegation. The feature discovers ranges of
addresses assigned to the link and blocks any traffic sourced with an address outside this range.
Configuring IPv6 Prefix Guard
Defines an IPv6 source-guard policy name and enters source-guard policy configuration mode.
ipv6 source-guard policy snooping-policy
Device(config)# ipv6 source-guard policy Mypolicy
Disables the validate address feature and enables the IPv6 prefix guard feature to be configured.
Device(config-source-guard)# no validate address
Enables IPv6 source guard to perform the IPv6 prefix-guard operation.
Device(config-source-guard)# validate prefix
IPv6 Destination Guard If a packet comes on the router destined for directly connected subnet
but for address that is not in the ND table that packet will be dropped to prevent ND exhaustion
type of attacks. To explain this, ND exhaustion is made by sending packets to all addresses in
the subnet. Subnets in IPv6 are bigger that IPv4 and /64 subnet will have
18446744073709551614 possible addresses. If you send packets to all those addresses you will
exhaust the memory of ND cache which will basically disable ND process and all the traffic will
become broadcast.
We need to be carefull will this as if our network device reboots it will possibly prevent devices
to communicate before they are registered in the ND table and they need to communicate to be
registered in the ND table. maybe let dramatic solution to this problem is with Cisco
implemented ND resolution rate limiter.
Configuring IPv6 Destination Guard
Defines the destination guard policy name and enters destination-guard configuration mode.
Device(config)# ipv6 destination-guard policy pol1
Sets the enforcement level for the target address.
Device(config-destguard)# enforcement always
Device(config-destguard)# exit
Enters VLAN configuration mode.
Device(config)# vlan configuration 911
Attaches a destination guard policy to a VLAN.
Device(config-vlan-config)# ipv6 destination-guard attach-policy pol1
18
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
ND resolution rate limiter is limiting number of ND resolution per second per router and cache
size limiter limits the size of cache per device interface so that there cannot get to the point
where all the memory is consumed and device breaks into reboot. ND resolution rate is 100
resolutions per second per router and cache size is limited to 250 IPv6 address per interface. You
can change those values using this interface level commands:
L3SW(config-if)#ipv6 nd cache interface-limit 4
SW(config-if)#ipv6 nd resolution data limit 50
IPv6 PACL
Configuring PACL Mode and Applying IPv6 PACL on an Interface
Once you have configured the IPv6 access list you want to use, you must configure the PACL
mode on the specified IPv6 L2 interface.
IPv6 Port-Based Access List Support
The IPv6 PACL feature provides the ability to provide access control (permit or deny) on L2
switch ports for IPv6 traffic. IPv6 PACLs are similar to IPv4 PACLs, which provide access
control on L2 switch ports for IPV4 traffic. They are supported only in ingress direction and in
hardware.
PACL can filter ingress traffic on L2 interfaces based on L3 and L4 header information or nonIP L2 information.
Device(config)# ipv6 access-list list1
Device(config-ipv6-acl)# exit
Device(config)# interface fastethernet 0/0
Device(config-if)# access-group mode prefer port
Device(config-if)# ipv6 traffic-filter list1 in
19
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Secure ND Protocol (SeND)
To understand SeND you will need to have good knowledge about PKI public key infrastructure and how
certificates obtained .you can read these topics in CompTIA Security+ or CCNA Security books. Also if
you have worked before with Microsoft AD CS Active Directory Certificate Service Role you will have the
required knowledge to understand SeND.
Before continue reading you need to know the meaning of Public Key , Private Key , Hashing Algorithms
, Certificate , Certificate Authority , Digital Signature ,PKI , CRL certificate revocation list.....etc
What is SeND?
SeND protocol counters ND threats. It defines a set of new ND options, and two new ND messages
(Certification Path Solicitation [CPS] and Certification Path Answer [CPA]). It also defines a new auto
configuration mechanism to be used in conjunction with the new ND options to establish address
ownership.
SEND works by having a pair of public and private keys per IPv6 node in a network and by
extending ND with more options. With SEND, nodes cannot choose their own interface
identifier (the lower 64 bits of their IPv6 address); the interface identifier is cryptographically generated
based on the current IPv6 network prefix and the public key and we call it CGA address .
Different components used to compute a CGA. It is based on the following CGA parameters:
A modifier, which is a random number
The public key of the host
The collision count, which is used to prevent a brute-force attack
The subnet prefix, which is the prefix of the desired address, typically received through router
advertisement
All above CGA components will be hashed with SHA-1 and take the least 64 bit in order to create the
interface identifier ( ipv6 host address)
At a minimum, link-local addresses on a SeND interface should be CGAs. Additionally, global addresses
can be CGAs.
So SeND mechanisms in used are:
1-Cryptographically Generated Addresses
Cryptographically generated addresses (CGAs) are IPv6 addresses generated from the cryptographic
hash of a public key .
The node generating a CGA address must first obtain RSA key pair (SeND uses an RSA public/private key
pair). The node then computes the interface identifier part (which is the rightmost 64 bits) and appends
the result to the prefix to form the CGA address.
2-Authorization Delegation Discovery
Authorization delegation discovery is used to certify the authority of routers by using a trust anchor. A
trust anchor is a third party that the host trusts and to which the router has a certification path.
Notice , In most operating systems, the trust anchor is a collection of X.509 certificates of certification
authorities that come preinstalled with the operating system, or is built into an application (such as web
browser).
20
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
SeND Deployment Models
Host-to-Host Deployment Without a Trust Anchor
Neighbor Solicitation Flow
Host-Router Deployment Model
Router Advertisement and Certificate Path Flows
Single CA Model
Host-to-Host Deployment Without a Trust Anchor
Deployment for SeND between hosts is straightforward. The hosts can generate a pair of RSA keys
locally, autoconfigure their CGA addresses, and use them to validate their sender authority, rather than
using a trust anchor to establish sender authority
Neighbor Solicitation Flow
In a neighbor solicitation scenario, hosts and routers in host mode exchange neighbor solicitations and
neighbor advertisements. These neighbor solicitations and neighbor advertisements are secured with
CGA addresses and CGA options, and have nonce, time stamp, and RSA neighbor discovery options
Host-Router Deployment Model
In many cases, hosts will not have access to the infrastructure that will enable them to obtain and
announce their certificates. In these situations, hosts will secure their relationship using CGA, and secure
their relationship with routers using a trusted anchor. When using RAs, SeND mandates that routers are
authenticated through a trust anchor.
Router Advertisement and Certificate Path Flows
the certificate exchange performed using certification path solicitation CPS/CPA SeND messages.
Single CA Model
The deployment model can be simplified in an environment where both hosts and routers trust a single
CA such as the Cisco certification server (CS).
SeND Fields added to NDP
Using CGA is not enough to ensure that the CGA is used by the right node. SEND extends the NDP by
adding further fields to the exchange:
CGA parameters:Sent so that the partners can execute the same algorithm and check whether they
compute the same CGA.
Nonce:A random number used once in all NS messages, the solicited node must include the same
nonce in its reply (this prevents replay attacks).
Signature:The CGA parameters and the nonce are also signed by using the private key of the node
Notice that Having a CGA does not mean that the node has the privilege to be on that network. CGA is
simply a way to ensure the binding of a MAC to an IPv6 address and should facilitate the deployment of
SEND.
SeND & Securing RA Messages
RA messages can be secured by using a similar mechanism where all RA messages are signed by the
routers. Because the hosts need to trust the routers, the routers must have an X.509 certificate
associated with their key pair. This certificate and the signature are transmitted in all RA messages. The
certificate Subject field must include the prefixes that the router might announce. Because certificates
21
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
are issued by a trusted certification authority (CA), the IPv6 nodes can trust the information in the
certificate. The certificates are exchanged by using two new messages that could be repeated if there is
a long certificate chain when using subordinate CA:
Certification Path Solicitation (CPS):Used by a host to get the router certificate if the latter is not in its
cache
Certification Path Advertisement (CPA):The router reply that contains the complete certificate
Note: To prevent replay attacks with SeND, routers include a signed timestamp in their RA messages
SeND configuration Steps
SeND is available in host mode , To implement SeND, configure the host with the following parameters:
An RSA key pair used to generate CGA addresses on the interface.
A SeND modifier that is computed using the RSA key pair.
A key on the SeND interface.
CGAs on the SeND interface.
A Public Key Infrastructure (PKI) trustpoint, with minimum content; for example, the URL of the
certificate server. A trust anchor certificate must be provisioned on the host.
SeND is also available in router mode. You can use the ipv6 unicast-routing command to configure a
node to a router. To implement SeND, configure routers with the same elements as that of the host. The
routers will need to retrieve certificates of their own from a certificate server.
The following operations need to be completed before SeND is configured on the host or router:
Hosts are configured with one or more trust anchors.
Hosts are configured with an RSA key pair or configured with the capability to locally generate it. Note
that for hosts not establishing their own authority via a trust anchor, these keys are not certified by any
CA.
Routers are configured with RSA keys and corresponding certificate chains, or the capability to obtain
these certificate chains that match the host trust anchor at some level of the chain.
Configuring CGA address
To configure a CGA address on interface Ethernet 0/0. This example first generates a RSA key pair
named SEND, Computes the SEND modifier, and finally assigns a CGA link-local and global unicast CGA
to the interface Ethernet 0/0.
crypto key generate rsa label SEND modulus 1024
ipv6 cga generate modifier rsakeypair SEND
interface Ethernet0/0
ipv6 cga rsakeypair SEND
ipv6 address FE80::/64 cga
ipv6 address 2001:db8::/64 cga
For more about Configuring SeND for IPv6 including:
Configuring Certificate Servers to Enable SeND
Configuring a Host to Enable SeND
Configuring a Router to Enable SeND
Implementing IPv6 SeND
22
CCIEv5 IPv6 FHS Quick Guide
By CCSI: Yasser Auda
Configuring SeND Parameters
Read the following link:
http://www.cisco.com/c/en/us/td/docs/ios/ipv6/configuration/guide/12_4t/ipv6_12_4t_book/ip6first_hop_security.html#wp1114080
Resources I used to collect info for this guide :
IPV6 FHS
http://www.cisco.com/c/en/us/products/collateral/ios-nx-os-software/enterprise-ipv6solution/whitepaper_c11-602135.html
http://blog.ipspace.net/2013/07/first-hop-ipv6-security-features-in.html
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipv6/configuration/15-2s/ipv6-15-2s-book/ip6-firsthop-security.html
http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipv6_fhsec/configuration/15-s/ip6f-15-s-book.pdf
http://www.cisco.com/web/about/security/intelligence/ipv6_first_hop.html
Videos from INE:
http://www.youtube.com/watch?v=Zv-stl5kRnI
http://www.youtube.com/watch?v=UtsHZmb1CYc
http://www.youtube.com/watch?v=goHublIvV-8
IPv6 Security
https://supportforums.cisco.com/video/12192486/ipv6-security-video-live-webcast
https://supportforums.cisco.com/document/12188991/ipv6-security-slides-live-webcast
http://www.hackerhalted.com/2013/us/wp-content/uploads/2013/10/HH-Atlanta-2013-IPv6-SecurityScott-Hogg.pdf
Videos from Cisco Get Your Build On YT Channel.
http://www.youtube.com/watch?v=hf5QGxRtG4o
http://www.youtube.com/watch?v=YbDg33vV-0E
http://www.youtube.com/watch?v=QDyqV7u4HSY
http://www.youtube.com/watch?v=-vOY0xXLoj0
http://www.youtube.com/watch?v=EjqimySPv7U
Cisco IPv6 Guides per Feature & IOS Version.
http://docwiki.cisco.com/wiki/Cisco_IOS_IPv6_Feature_Mapping#IPv6_Features
Info about DHCPv6
https://supportforums.cisco.com/blog/153426/implementing-dhcpv6-introduction
https://supportforums.cisco.com/document/116221/part-1-implementing-dhcpv6-stateful-dhcpv6
https://supportforums.cisco.com/document/116236/part-2-implementing-dhcpv6-stateless-dhcpv6
Good Luck
CCSI: Yasser Auda
https://www.facebook.com/YasserRamzyAuda
https://learningnetwork.cisco.com/people/yasser.r.a?view=documents
https://www.youtube.com/user/yasserramzyauda
23
Anda mungkin juga menyukai
- Lab 12 Configuring Stateless and Stateful DHCPv6Dokumen11 halamanLab 12 Configuring Stateless and Stateful DHCPv6Alwan SahmiBelum ada peringkat
- IPv6 NAT-PT Versus NAT64 With Cisco Rout PDFDokumen40 halamanIPv6 NAT-PT Versus NAT64 With Cisco Rout PDFValerio BitontiBelum ada peringkat
- IPv6 SLAAC and DHCPv6Dokumen51 halamanIPv6 SLAAC and DHCPv6Pedro Mantilla Silva100% (1)
- Load Balanced QuanggaDokumen4 halamanLoad Balanced QuanggaAchmad MuzaqiBelum ada peringkat
- CCNA 2 Ch10 ExamDokumen10 halamanCCNA 2 Ch10 ExamBryant Villarin BaldivicioBelum ada peringkat
- TP 2 - DHCPv6Dokumen4 halamanTP 2 - DHCPv6PFEBelum ada peringkat
- Mikrotik Ipv6Dokumen6 halamanMikrotik Ipv6AfrilexxBelum ada peringkat
- IPv6: Compare Cisco NAT-PT Vs NAT64. With Configuration Examples and DNS64.Dokumen40 halamanIPv6: Compare Cisco NAT-PT Vs NAT64. With Configuration Examples and DNS64.Gianrico Fichera100% (2)
- Ipv6 Astaro2005Dokumen19 halamanIpv6 Astaro2005ajaykumar988Belum ada peringkat
- CCIE SP Notes For LabDokumen252 halamanCCIE SP Notes For LabAsif DarveshBelum ada peringkat
- Dynamic Host Configuration Protocol v6: Slaac and Dhcpv6Dokumen21 halamanDynamic Host Configuration Protocol v6: Slaac and Dhcpv6Hasan MilonBelum ada peringkat
- All About Ipv6 Address Space: Document Owner: Manju DevarajDokumen10 halamanAll About Ipv6 Address Space: Document Owner: Manju DevarajManju DevarajBelum ada peringkat
- 10: Icmpv6 Neighbor Discovery: Rick Graziani Cabrillo College Rick - Graziani@Cabrillo - EduDokumen32 halaman10: Icmpv6 Neighbor Discovery: Rick Graziani Cabrillo College Rick - Graziani@Cabrillo - EduAlberto ArellanoBelum ada peringkat
- OSPF Exercise: Campus Network Design WorkshopDokumen9 halamanOSPF Exercise: Campus Network Design WorkshopAlbert OmondiBelum ada peringkat
- DCCN DHCPDokumen19 halamanDCCN DHCPYehualashet BelaynehBelum ada peringkat
- 10.2.3.5 Lab - Configuring Stateless and Stateful DHCPv6Dokumen22 halaman10.2.3.5 Lab - Configuring Stateless and Stateful DHCPv6macmBelum ada peringkat
- 11a Adv Router Config OspfDokumen8 halaman11a Adv Router Config Ospfcatalin ionBelum ada peringkat
- Latest Dump Compiled by Genius PDFDokumen127 halamanLatest Dump Compiled by Genius PDFMateus Gerboni100% (1)
- Lecture 3Dokumen25 halamanLecture 3Hạnh Hoàng ĐìnhBelum ada peringkat
- NEW Cisco CCNA 200-125 Exam Dumps Latest Version 2019 For Free PDFDokumen244 halamanNEW Cisco CCNA 200-125 Exam Dumps Latest Version 2019 For Free PDFJorge Enrique Cortez BastidasBelum ada peringkat
- CCNA 2 Chapter 10 PDFDokumen8 halamanCCNA 2 Chapter 10 PDFMarc Jason YuBelum ada peringkat
- Ospf Lab: Router Types Used in The LabDokumen5 halamanOspf Lab: Router Types Used in The LabmahadvikaBelum ada peringkat
- BÀI TẬP 07 - CÁC GIAO THỨC ĐỊNH TUYẾNDokumen4 halamanBÀI TẬP 07 - CÁC GIAO THỨC ĐỊNH TUYẾNHoàng AnhBelum ada peringkat
- 3 Ipv6 RoutingDokumen27 halaman3 Ipv6 Routingcatalin ionBelum ada peringkat
- 1-Module 01 Basic & InterfaceDokumen35 halaman1-Module 01 Basic & InterfacevajragantaBelum ada peringkat
- CCNA 2 Chapter 10 v5.0 Exam Answers 2015 100Dokumen9 halamanCCNA 2 Chapter 10 v5.0 Exam Answers 2015 100ovidiu0702Belum ada peringkat
- Lab - IPV6Dokumen14 halamanLab - IPV6Ridmi JayasekaraBelum ada peringkat
- SRWE Module 8Dokumen37 halamanSRWE Module 8Juan José RomeroBelum ada peringkat
- Snooping de DHCPDokumen41 halamanSnooping de DHCPionrivas3355Belum ada peringkat
- 25-8-2018 CCNA 200 125 551Q CCNAv6 PDFDokumen250 halaman25-8-2018 CCNA 200 125 551Q CCNAv6 PDFiliutzaBelum ada peringkat
- VH Thc-Ipv6 AttackDokumen58 halamanVH Thc-Ipv6 AttackJudith Cardenas MerchanBelum ada peringkat
- CCNA Practice Final PDFDokumen21 halamanCCNA Practice Final PDFBachi BachiBelum ada peringkat
- How To Configure DHCP in Cisco Packet TracerDokumen12 halamanHow To Configure DHCP in Cisco Packet TracerLuis FfBelum ada peringkat
- Revision Notes CCNA 3 EasyDokumen40 halamanRevision Notes CCNA 3 EasyNur Dinah YeeBelum ada peringkat
- CNE Tutorial 10 - IPv6 Configuration and Static RoutingDokumen18 halamanCNE Tutorial 10 - IPv6 Configuration and Static RoutingLiên VũBelum ada peringkat
- Assign IPv6 On Some OSDokumen17 halamanAssign IPv6 On Some OSNguyễn Tiến HoàiBelum ada peringkat
- Verifying NAT Operation and Basic NAT TroubleshootingDokumen10 halamanVerifying NAT Operation and Basic NAT TroubleshootingcsystemsBelum ada peringkat
- Clase 21-Mod2Dokumen27 halamanClase 21-Mod2Alex Osores RiveraBelum ada peringkat
- Verificacion de NatDokumen10 halamanVerificacion de NatJuanan PalmerBelum ada peringkat
- An IPV6 Presentation On Fundamentals .Have A LookDokumen16 halamanAn IPV6 Presentation On Fundamentals .Have A Looksrikanth reddyBelum ada peringkat
- Hot Standby Router Protocol Features and Functionality: Document ID: 9234Dokumen14 halamanHot Standby Router Protocol Features and Functionality: Document ID: 9234Balaji RamanujamBelum ada peringkat
- IPv6 RoutingDokumen45 halamanIPv6 RoutingNguyễn Tiến HoàiBelum ada peringkat
- Unit - V: Application DevelopmentDokumen42 halamanUnit - V: Application DevelopmentKarthi KeyanBelum ada peringkat
- Troubleshooting IPv6 ConnectivityDokumen2 halamanTroubleshooting IPv6 ConnectivityDarryl BrownBelum ada peringkat
- CCNADokumen7 halamanCCNAdivi handokoBelum ada peringkat
- 7.2.5.3 Lab - Identifying IPv6 AddressesDokumen7 halaman7.2.5.3 Lab - Identifying IPv6 Addressesرافد البركي100% (7)
- Routing Protocol and Routed Protocol: Lab #5 IP Routing IDokumen8 halamanRouting Protocol and Routed Protocol: Lab #5 IP Routing IMahfuzur RahmanBelum ada peringkat
- IPv 6Dokumen29 halamanIPv 6meriem hasBelum ada peringkat
- CCNPv7 ROUTE Lab3-3 OSPFv3-Address-Families InstructorDokumen26 halamanCCNPv7 ROUTE Lab3-3 OSPFv3-Address-Families InstructorHuanChiHuaBelum ada peringkat
- Module 01a - IPv6 OSPF and iBGPDokumen14 halamanModule 01a - IPv6 OSPF and iBGPbongBelum ada peringkat
- Module 01b - IPv6 ISIS and iBGPDokumen13 halamanModule 01b - IPv6 ISIS and iBGPbongBelum ada peringkat
- 359 v16-266simV3350-CCNA 200 125Dokumen126 halaman359 v16-266simV3350-CCNA 200 125bRioR bRioRBelum ada peringkat
- 10.2.4.4 Lab - Troubleshooting DHCPv6Dokumen6 halaman10.2.4.4 Lab - Troubleshooting DHCPv6Karla ArroyoBelum ada peringkat
- Lab 4 - Router As A DHCP ServerDokumen7 halamanLab 4 - Router As A DHCP ServerMiticuta SurubBelum ada peringkat
- AutoconfigurationDokumen9 halamanAutoconfigurationvadapav2901Belum ada peringkat
- 7 SLAAC RickGrazianiDokumen36 halaman7 SLAAC RickGrazianimtcssnspBelum ada peringkat
- First Hop Redundancy Protocol: Network Redundancy ProtocolDari EverandFirst Hop Redundancy Protocol: Network Redundancy ProtocolBelum ada peringkat
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkDari EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkBelum ada peringkat
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityDari EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityBelum ada peringkat
- Cisco Video and Telepresence Architecture Design Guide: March 30, 2012Dokumen110 halamanCisco Video and Telepresence Architecture Design Guide: March 30, 2012Ravi KumarBelum ada peringkat
- ITIL Continual Service Improvement PDFDokumen262 halamanITIL Continual Service Improvement PDFgreeneyedprincess100% (3)
- Cisco Unified Communications With CME, CUE, SRST: Deployment Scenarios, Management and SecurityDokumen59 halamanCisco Unified Communications With CME, CUE, SRST: Deployment Scenarios, Management and Securitymky212Belum ada peringkat
- Cisco CRST Communications Manager de Mexico S de RL de CVDokumen104 halamanCisco CRST Communications Manager de Mexico S de RL de CVCharly GlezBelum ada peringkat
- Designing & Deploying UC NetworksDokumen105 halamanDesigning & Deploying UC NetworksCharly GlezBelum ada peringkat
- Cisco Unified Intelligence Center Solution Reference Network Design (SRND), Release 9.0Dokumen40 halamanCisco Unified Intelligence Center Solution Reference Network Design (SRND), Release 9.0Charly GlezBelum ada peringkat
- Deploying IPv6 in Unified Communications Networks With Cisco Unified Communications Manager PDFDokumen144 halamanDeploying IPv6 in Unified Communications Networks With Cisco Unified Communications Manager PDFCharly GlezBelum ada peringkat
- CVD CampusWiredLANDesignGuide AUG13Dokumen97 halamanCVD CampusWiredLANDesignGuide AUG13paultjiheBelum ada peringkat
- Solution Reference Network Design For Cisco Unified CCX and Cisco Unified IP IVR, Release 8.5Dokumen142 halamanSolution Reference Network Design For Cisco Unified CCX and Cisco Unified IP IVR, Release 8.5Charly GlezBelum ada peringkat
- Cisco IOS XR Introduction Ver 1Dokumen105 halamanCisco IOS XR Introduction Ver 1GRANMAZINGERBelum ada peringkat
- VLSM Subnetting ChartDokumen1 halamanVLSM Subnetting ChartPatricia GalianoBelum ada peringkat
- VcpdemoDokumen68 halamanVcpdemoFlaviaDobrescuBelum ada peringkat
- VMware Testking 2V0-621D v2015-11-26 by Vera 183qDokumen97 halamanVMware Testking 2V0-621D v2015-11-26 by Vera 183qCharly GlezBelum ada peringkat
- Itbraindumps: Latest It Braindumps Study GuideDokumen5 halamanItbraindumps: Latest It Braindumps Study GuideCharly GlezBelum ada peringkat
- Sony hcd-gpx33 gpx55 gpx77 gpx88 Ver.1.0Dokumen82 halamanSony hcd-gpx33 gpx55 gpx77 gpx88 Ver.1.0ZxdIaminxXzlovewithzxXzyouzxBelum ada peringkat
- CCNA Prep - IP Subnetting From NetworkersDokumen40 halamanCCNA Prep - IP Subnetting From NetworkersRenato Siqueira100% (7)
- Lead2Pass 400-101 827 QuestionsDokumen328 halamanLead2Pass 400-101 827 QuestionsSheryar Saqib100% (1)
- (DELL) Networking-n2000-Series Deployment Guide9 En-UsDokumen1.460 halaman(DELL) Networking-n2000-Series Deployment Guide9 En-UsRaphael LambertiBelum ada peringkat
- BSC Dell - Switch - N2000 - N3000 - N4000Dokumen3 halamanBSC Dell - Switch - N2000 - N3000 - N4000Charly GlezBelum ada peringkat
- Yasser Auda Cciev5 Mpls Guide (LDP, VRF Lite, Mpls VPN)Dokumen65 halamanYasser Auda Cciev5 Mpls Guide (LDP, VRF Lite, Mpls VPN)Muhammad Ali100% (2)
- Soluciones de Tecnologías de Lif Ió Soluciones de Tecnologías de Lif IóDokumen2 halamanSoluciones de Tecnologías de Lif Ió Soluciones de Tecnologías de Lif IóCharly GlezBelum ada peringkat
- Soluciones de Tecnologías de Lif Ió Soluciones de Tecnologías de Lif IóDokumen2 halamanSoluciones de Tecnologías de Lif Ió Soluciones de Tecnologías de Lif IóCharly GlezBelum ada peringkat
- Network Virtualization With Dell Infrastructure and VMware NSX V2Dokumen33 halamanNetwork Virtualization With Dell Infrastructure and VMware NSX V2Charly GlezBelum ada peringkat
- Yasser Auda Cciev5 Mpls Guide (LDP, VRF Lite, Mpls VPN)Dokumen65 halamanYasser Auda Cciev5 Mpls Guide (LDP, VRF Lite, Mpls VPN)Muhammad Ali100% (2)
- SW1Dokumen4 halamanSW1Charly GlezBelum ada peringkat
- 350 080Dokumen307 halaman350 080Charly GlezBelum ada peringkat
- Ccie 360 ConnectionsDokumen1 halamanCcie 360 ConnectionsCharly GlezBelum ada peringkat
- SW3Dokumen4 halamanSW3Charly GlezBelum ada peringkat
- IRFDokumen32 halamanIRFCharly GlezBelum ada peringkat
- InterLink BrochureDokumen8 halamanInterLink BrochurePetyo GeorgievBelum ada peringkat
- Prof PracDokumen6 halamanProf Prackatherines9Belum ada peringkat
- BOSS Air and Dirt Separation BrochureDokumen8 halamanBOSS Air and Dirt Separation BrochureWayde WillinsBelum ada peringkat
- BENZZDokumen26 halamanBENZZManimegalai PrasannaBelum ada peringkat
- Apna Aashiyana For WebDokumen32 halamanApna Aashiyana For Websoftdev11Belum ada peringkat
- Niit MCQDokumen10 halamanNiit MCQArun SomanBelum ada peringkat
- Unit-2 Operating SystemDokumen74 halamanUnit-2 Operating SystemSaroj VarshneyBelum ada peringkat
- Product DetailsDokumen215 halamanProduct DetailsEric MagnayeBelum ada peringkat
- CTS Komponent® - DATASHEETDokumen2 halamanCTS Komponent® - DATASHEETJoseph AsfourBelum ada peringkat
- RA 9266 Architecture LawDokumen14 halamanRA 9266 Architecture LawPatricia Caña100% (2)
- Hadoop SessionDokumen65 halamanHadoop SessionSuresh ChowdaryBelum ada peringkat
- Teks DeskripsiDokumen1 halamanTeks DeskripsitimpolmasBelum ada peringkat
- Eaae Guide Schools of Architecture in EuropeDokumen168 halamanEaae Guide Schools of Architecture in EuropeMarian CiucaBelum ada peringkat
- Azobe Class1 Against Marine BorerDokumen3 halamanAzobe Class1 Against Marine BorerEgemen AkbulutBelum ada peringkat
- VLAN Routing: Huawei Technologies Co., LTDDokumen14 halamanVLAN Routing: Huawei Technologies Co., LTDmangla\Belum ada peringkat
- Glasgow University Estates Conservation Strategy Jan 2012Dokumen551 halamanGlasgow University Estates Conservation Strategy Jan 2012gamoviBelum ada peringkat
- First Steps To Use FireDAC - RAD StudioDokumen3 halamanFirst Steps To Use FireDAC - RAD StudioJuli Adi PrastyoBelum ada peringkat
- Ancon Acoustic Wall TiesDokumen4 halamanAncon Acoustic Wall TiesAyman_Elmasry_9107Belum ada peringkat
- Sans 2001-cc2Dokumen21 halamanSans 2001-cc2Mustufa F Kanjeta100% (4)
- Fashion Hub Site SelectionDokumen8 halamanFashion Hub Site SelectionAnonymous wTVJ4cIY0% (1)
- Home Work-9Dokumen3 halamanHome Work-9zahed83Belum ada peringkat
- Theory of Structures Assignment FinalDokumen21 halamanTheory of Structures Assignment FinalManasAroraBelum ada peringkat
- Monolithic GlassDokumen12 halamanMonolithic Glassxkunk9813Belum ada peringkat
- Breakdown of The $7.2 Million Improvement Plan For Monroe County ParksDokumen2 halamanBreakdown of The $7.2 Million Improvement Plan For Monroe County ParksNews 8 WROCBelum ada peringkat
- Tube Fitting Installation SeminarDokumen74 halamanTube Fitting Installation SeminarEscarabBelum ada peringkat
- HLBB Auction Fair Listing 28th Nov'17 (Johor)Dokumen3 halamanHLBB Auction Fair Listing 28th Nov'17 (Johor)Jumrang MendengBelum ada peringkat
- Slab: Plate20... 21 - Panel No. 20: 1.1. ReinforcementDokumen12 halamanSlab: Plate20... 21 - Panel No. 20: 1.1. ReinforcementkkklllyyyBelum ada peringkat
- Pan-Os Cli Command PDFDokumen48 halamanPan-Os Cli Command PDFAckld2008100% (1)
- 4 2 2Dokumen403 halaman4 2 2joBelum ada peringkat
- AutomationDokumen28 halamanAutomationlaxman100% (1)