Secure Image Transmission With Secret Fragment Visible Mosaic Images
Diunggah oleh
Editor IJRITCCHak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Secure Image Transmission With Secret Fragment Visible Mosaic Images
Diunggah oleh
Editor IJRITCCHak Cipta:
Format Tersedia
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3595 - 3598
_______________________________________________________________________________________________
Secure Image Transmission with Secret Fragment Visible Mosaic Images
Miss. Nayan A. Ardak1, Prof. Nitin A. Shelke2,
1
M.E. final year CSE, GHRCEM,
Amravati, India
nayan.ardak@gmail.com
2
Dept. of comp. science and Engg. Asst. Professor of GHRCEM,
Amravati, India
Abstract: Mosaic means picture or decorative design made by setting small colour pieces, also mosaic is a composite
picture made of overlapping images, photos etc. Reshuffle of the fragments of a one image in another image form a new image called mosaic
image. To create a mosaic image, secret image is first divided into rectangular shaped fragments, called tile images, which are fitted into a target
image called secret fragment visible mosaic image of same size. The mosaic image looks similar to preselected target image, is yield by dividing
input image into fragments and transforming their colour into another colour. Greedy heuristic algorithm is proposed to find a related tile image
of the secret image to fit into each block in the target image. The information related to the recovery of image is embedding inside target block
with the help of lossless substitution scheme. The proposed method, designed for dealing with mosaic images which are useful for hiding secret
images. To enhance the security of embed data proposed system also work.
Keywords- Colour transformation, image encryption, mosaic image, secures image transmission.
________________________________________________*****___________________________________________________
1. INTRODUCTION
Today images usually contain private or confidential
information so that they should be protected from leakages
during transmissions. Recently, many methods have been
proposed for securing image transmission such as image
encryption and data hiding. Image encryption is a technique
that uses to encrypt image into noise form, using high
redundancy and strong spatial correlation. The encrypted image
is a meaningless file and before encryption additional
information is not provided. Data hiding is alternative for
image encryption that hide secret image into a cover image so
that no one can realize the existence of the secret data. Large
number of data is not hide into a single is the main issue of data
hiding. Specifically, if one wants to hide a secret image into a
cover image with the same size, the secret image must be
highly compressed in advance. A new technique for secret
image transmission is proposed with the help of secret image
and target image.
Select three images secret image, target image, and
mosaic image. After selecting the target image, the given secret
image is first divided into number of rectangular fragments
called tile images, which then are fit into similar blocks in the
target image, called target blocks, according to a comparison of
colour transformation. Next, the color characteristic of each tile
image is transformed into the other colour, resulting in a
mosaic image which looks like the target image. Appropriate
schemes are also proposed to conduct nearly lossless recovery
of the original secret image from the resulting mosaic image
[1].
2.1 Mosaic Image Creation
In this module after creating the mosaic image, upload the
mosaic image on web page for secure transmission with the key
then receiver get this mosaic image and key. Key on receiver
side is in encrypted form by using private key receiver decrypt
this key, download the mosaic image and recover the secret
image with the help of decrypted key.
Figure 2.1 Mosaic Image creation
2. PROPOSED METHOD
In the mosaic image creation firstly select the one secret image
and target image both having same size, secrete image is
divided into number of fragments called the tiles of images.
Then target image it again divided into same number of tiles as
that of secrete image then apply the colour transformation on it
the fit that tiles of secret image into target block and form a
mosaic image.
Figure 2.2 Transmission of image
3595
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3595 - 3598
_______________________________________________________________________________________________
Above figure 2.2 shows transmission of mosaic image,
for recovery of secret image sender uploads mosaic image and
key on web. In receiver side key is in encrypted format using
MD 5, receiver decrypt the key with the help private key. MD 5
is used for hash key generation.
2.2 Recovery of Image
In the recovery of secret image module firstly take mosaic
image then extract embedded information from it and recover
the information and secret image. The module includes two
stages:
Extracting the embedded information for secret image
recovery from the mosaic image.
Recovering the secret image using the extracted
information.
Recover one by one in a raster-scan order the tile images Ti, i =
1 through n, of the desired secret image S by the following
steps:
1) Rotate in the reverse direction the block indexed by ji,
namely Bji, in F through the optimal angle and fit the
resulting block content into Ti to form an initial tile
image Ti
2) Use the extracted means and related standard deviation
quotients to recover the original pixel values in Ti.
3) Use the extracted means, standard deviation quotients, and
to compute the two parameters cS and cL.
4) Scan Ti to find out pixels with values 255 or 0 which
indicate that overflows or underflows respectively have
occurred there.
schemes are also proposed to conduct nearly lossless recovery
of the original secret image.
The Root Mean Square Error (RMSE) (also called the
root mean square deviation, RMSD) is a used to measure the
error between recover image and original image. These
calculated difference is also called residuals, and the RMSE
serves to aggregate them into a single measure of predictive
power. The RMSE of a model prediction with respect to the
estimated variable Xmodel is defined as the square root of the
mean squared error:
2
RMSE =
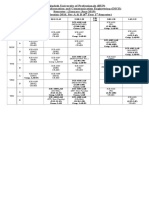
Table 3.1 Time for embedding and recovery of secret image
Time to fit the
Time to
tiles of secret
recover the
image into
secret image
target image
from mosaic
(ms)
image (ms)
Koala
191.25
56.02
Desert
201.84
102.02
Lighthouse
243.23
142.26
Jellyfish
205.23
126.09
Flower
186.25
146.23
Input Images
300
Figure 2.3 Recovery of secret image
250
3. PERFORMANCE ANALYSIS
The given secret image is first divided into rectangular
fragments called tile images, which then are fit into similar
blocks in the target image, called target blocks, according to a
similarity criterion based on color variations. Next, the color
characteristic of each tile image is transformed to be that of the
corresponding target block in the target image, resulting in a
mosaic image which looks like the target image. Relevant
Time to fit the tiles of
secret image
Time to recover the
secret image
200
Time (MS)
5) Add respectively the values cS or cL to the corresponding
residual values of the found pixels.
6) Take the results as the final pixel values, resulting in a final
tile image Ti.
In recovery of secret image first select the mosaic
image from its saved location then enter the decrypted key and
click on get original button to get the recovered image with
smallest rmse value than original one in the second phase, the
embedded information is extracted to recover nearly losslessly
the secret image from the generated mosaic image.
150
100
50
0
Input Images
Figure 3.1 Time for embedding and recovery of secret
image
Above 3.1 shows time for embedding tile and time for recovery
of the secret image from the mosaic images using sample
images. Both calculated time are in MS.
3596
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3595 - 3598
_______________________________________________________________________________________________
2.5
Table 3.2 Time for colour transformation
Time for colour
Input Images
transformation(millisecond)
Desert
1903.2
Lighthouse
1196.8
Flowers
2028.01
Jellyfish
1887.6
Image (1)
1998.06
Koala
1965.6
Image (2)
1526.23
Penguins
1823.03
RMSE
1.5
RMSE Value of
Existing System
for Recovery
RMSE Value of
Proposed System
for recovery
0.5
Image Image Image Image Image
(1)
(2)
(3)
(4)
(5)
Input Images
Figure 3.3 RMSE value of recovery of secret image
In the above table and figure 3.3 calculate the RMSE value for
recovery of secret image for taking the value of existing system
and the proposed system, from the five different images of
same size.
2500
Time (MS)
2000
Table 3.4 RMSE value of mosaic image
1500
1000
Time of color
transformation
500
Penguins
Koala
Image (2)
Image (1)
Jellyfish
Flower
Desert
Lighthouse
Input Images
Figure 3.2 Time for colour transformation
Name of
image
Image(3)
Lighthouse
Images(4)
Koala
Penguins
77
55
63
87
Rocks
68
43
59
76
Hydrangeas
63
68
63
73
Images(6)
65
57
69
71
Above 3.2 shows time for embedding and time recovery of
secrete image for above sample images, dark colour column for
time of fit the tiles of secret image light colour column is for
time of recovery of secret image.
Input images
RMSE value of
RMSE value of
existing system
proposed
for recovery [9]
system for
80
RMSE
Table 3.3 RMSE value of recovery of secret image
100
60
40
20
RMSE value of Mosaic Image
Image(3)
Lighthouse
Images(4)
Koala
recovery
Image (1)
0.94
0.936
Image (2)
0.98
Figure 3.4 RMSE value of mosaic image
Image (3)
1.2
0.995
Image (4)
1.5
1.1
Following table is for calculating the RMSE value of the
mosaic image for one secret image with number of target
images show in table 7.4 and figure 7.6
Image (5)
2.1
1.8
4. Conclusions
In this proposed work tile image fitting information for secret
image recovery is embedded into randomly selected tile images
in the resulting mosaic image controlled by a secret key. An
additional security enhancement measure was also use, with the
help of key additional security is provided to the system. This
3597
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3595 - 3598
_______________________________________________________________________________________________
proposed system is better than existing system because
additional security is provide in proposed system and freely
choose the secret image and target image.
REFERENCES
[1] J. Kim and F. Pellacini, Jigsaw image mosaics,
Proc. of 2002 Int'l Conf. on Computer Graphics &
Interactive Techniques (SIGGRAPH 02), San
Antonio, USA, July 2002, pp. 657-664.
[2] Y. Dobashi, T. Haga, H. Johan and T. Nishita, A
method for creating mosaic image using voronoi
diagrams, Proc. of 2002 European Association for
Computer Graphics (Eurographics 02), Saarbrucken,
Germany, Sept. 2002, pp. 341-348.
[3] J. Tian, Reversible data embedding using a
difference expansion, IEEE Trans. Circuits Syst.
Video Technol., Vol. 13, No. 8, Aug. 2003, pp. 890
896.
[4] Ming-Shing Su, Wen-Liang Hwang, and Kuo-Young
Cheng Analysis on Multi resolution Mosaic Images
IEEE transactions on image processing, Vol. 13, No.
7, July 2004, pp. 952-959.
[5] Lukac and Plataniotis digital image indexing using
secret sharing schemes: a unified framework for
single-sensor
consumer
electronics
IEEE
transactions on consumer electronics, Vol. 51, No. 3,
August 2005, pp. 908-917.
[6] S. Battiato, G. Di Blasi, G.M. Farinella and G. Gallo,
Digital mosaic framework: an overview, Euro
graphics Computer Graphic Forum, Vol. 26, No. 4,
Dec. 2007, pp. 794-812.
[7] I. J. Lai and W. H. Tsai, Secret-fragment-visible
mosaic image A new computer art and its application
to information hiding, IEEE Trans. Inf. Forens.
Secure, Vol. 6, No. 3, Sep. 2011, pp. 936945.
[8] LI Jing Remote Viewing Image Mosaic based on
Fuzzy Cellular Automata Corner Detection in
Substation International Journal of Security and Its
Applications Vol.7, No.6 (2013), pp.55-66.
[9] Hae-Yeoun Lee Generation of Photo-Mosaic Images
through Block Matching and Color Adjustment
International Journal of Computer, Information,
Systems and Control Engineering Vol.: 8 No:3, 2014,
pp. 426-430.
[10] Ya-lin lee and Tsai IEEE transactions on circuits and
systems for video technology, Vol. 24, No. 4, April
2014, pp. 695-704.
AUTHOR BIOGRAPH
Miss Nayan A. Ardak has completed her
B.E. in computer science and engineering from Sant
Gadge Baba University Amravati. She is currently
pursuing the M.E. degree at GHRCEM College
Amravat.
Prof. N. A. Shelke has completed
his M.Tech in Computer Science and
Engineering
from
Government
College of Engineering Amravati.
He is currently working as an
Assistant Professor in GHRCEM
Amravati. His area of research
includes Image Processing, Artificial
Neural Network, Pattern Recognition
and Genetic Algorithm.
3598
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
Anda mungkin juga menyukai
- Ib Psychology - Perfect Saq Examination Answers PDFDokumen2 halamanIb Psychology - Perfect Saq Examination Answers PDFzeelaf siraj0% (2)
- Howo ModelDokumen54 halamanHowo ModelTry SumantryBelum ada peringkat
- Teachers Guide Lower Secondary Science PDFDokumen141 halamanTeachers Guide Lower Secondary Science PDFNuzhat IbrahimBelum ada peringkat
- Zgouras Catherine Team Together 1 Teachers BookDokumen257 halamanZgouras Catherine Team Together 1 Teachers Booknata86% (7)
- Secure Image Transmission Via Mosaic Images Using Genetic AlgorithmDokumen6 halamanSecure Image Transmission Via Mosaic Images Using Genetic AlgorithmIJIRSTBelum ada peringkat
- 1Dokumen26 halaman1ahmedBelum ada peringkat
- Crypting Image in A Communication MediaDokumen4 halamanCrypting Image in A Communication MediaseventhsensegroupBelum ada peringkat
- 12 - Chapter 3types of Visual Cryptography Schemes PDFDokumen28 halaman12 - Chapter 3types of Visual Cryptography Schemes PDFAymen HamadaBelum ada peringkat
- Li Tsai Isvc 2011Dokumen10 halamanLi Tsai Isvc 2011ArunSiddesh KBBelum ada peringkat
- Bit Slicng Based Visual Cryptography On Gray Scale ImageDokumen4 halamanBit Slicng Based Visual Cryptography On Gray Scale ImageEditor IJRITCCBelum ada peringkat
- YalinDokumen9 halamanYalinCristian VascoBelum ada peringkat
- Chapter 1Dokumen5 halamanChapter 1pius1985Belum ada peringkat
- Secured Lossless Share WatermarkingDokumen4 halamanSecured Lossless Share WatermarkingEditor IJRITCCBelum ada peringkat
- Study of Image Fusion Using Discrete Wavelet and Multiwavelet Transform With MATLAB SimulinkDokumen3 halamanStudy of Image Fusion Using Discrete Wavelet and Multiwavelet Transform With MATLAB SimulinkEditor IJRITCCBelum ada peringkat
- BTC With K Means Classifier Using Color Image ClusteringDokumen7 halamanBTC With K Means Classifier Using Color Image ClusteringJournal of Computer ApplicationsBelum ada peringkat
- Securing Visual Cryptographic Shares Using Public Key EncryptionDokumen6 halamanSecuring Visual Cryptographic Shares Using Public Key EncryptionRamesh MohapatraBelum ada peringkat
- Ijaiem 2013 09 16 019 PDFDokumen5 halamanIjaiem 2013 09 16 019 PDFInternational Journal of Application or Innovation in Engineering & ManagementBelum ada peringkat
- Visual Cryptographic Algorithm With Shared Data: Gazal Sahai T.S.LambaDokumen5 halamanVisual Cryptographic Algorithm With Shared Data: Gazal Sahai T.S.LambaHari RamBelum ada peringkat
- Development of Visual Cryptography Technique For Authentication Using Facial ImagesDokumen8 halamanDevelopment of Visual Cryptography Technique For Authentication Using Facial ImagesEditor IJRITCCBelum ada peringkat
- Final Report - MLDokumen12 halamanFinal Report - MLBollam Pragnya 518Belum ada peringkat
- JTD3E - Group8 - Major Assigment Practicum ReportDokumen10 halamanJTD3E - Group8 - Major Assigment Practicum ReportMikhail RachmanBelum ada peringkat
- Study of Different Approaches of Thresholding Methods For Segmentation in Digital Image ProcessingDokumen4 halamanStudy of Different Approaches of Thresholding Methods For Segmentation in Digital Image ProcessingEditor IJRITCC100% (1)
- Extending The Visual Cryptography Algorithm Without Removing Cover ImagesDokumen4 halamanExtending The Visual Cryptography Algorithm Without Removing Cover ImagesseventhsensegroupBelum ada peringkat
- Linear ReportDokumen4 halamanLinear ReportMahmoud Ahmed 202201238Belum ada peringkat
- IISDokumen10 halamanIISPetko PetkovskiBelum ada peringkat
- 2021 Dip 1Dokumen37 halaman2021 Dip 1Abdul KadirBelum ada peringkat
- Design and Implementation of Visual Cryptography System For Transmission of Secure DataDokumen4 halamanDesign and Implementation of Visual Cryptography System For Transmission of Secure DataEditor IJRITCCBelum ada peringkat
- DIP Lab FileDokumen13 halamanDIP Lab FileAniket Kumar 10Belum ada peringkat
- Image RestorationDokumen12 halamanImage RestorationHarikesh MauryaBelum ada peringkat
- 29 Denslin Brabin Region Based CDokumen5 halaman29 Denslin Brabin Region Based CVinay VamsiBelum ada peringkat
- Image Hiding Technique Based On Secret Fragment Visible Mosaic ImageDokumen6 halamanImage Hiding Technique Based On Secret Fragment Visible Mosaic ImageISAR-PublicationsBelum ada peringkat
- Data Hiding and Retrieval Using Visual CryptographyDokumen9 halamanData Hiding and Retrieval Using Visual CryptographyIJIRAEBelum ada peringkat
- A Combined Model of Bayesian Network and Spatial Markov Kernel For Multiclass Image Segmentation and CategorizationDokumen4 halamanA Combined Model of Bayesian Network and Spatial Markov Kernel For Multiclass Image Segmentation and CategorizationIJMERBelum ada peringkat
- Image Encryption Using The Image Steganography Concept and PLIP ModelDokumen5 halamanImage Encryption Using The Image Steganography Concept and PLIP ModelHaritha MuthuBelum ada peringkat
- Group1 - Minor - ProjectDokumen31 halamanGroup1 - Minor - ProjectsibohegitBelum ada peringkat
- Visual Secret Sharing Using Cryptography: K.K.W.I.E.E.R, Nashik, Maharashtra IndiaDokumen3 halamanVisual Secret Sharing Using Cryptography: K.K.W.I.E.E.R, Nashik, Maharashtra IndiaInnovative Research PublicationsBelum ada peringkat
- Image Steganography Using Modified Least Significant BitDokumen5 halamanImage Steganography Using Modified Least Significant Bitادريس عطيه النيانBelum ada peringkat
- Bitwise Operations On Images in Computer VisionDokumen4 halamanBitwise Operations On Images in Computer VisionArushi SrivastavaBelum ada peringkat
- Object Detection Using Deep Learning Algorithm CNNDokumen9 halamanObject Detection Using Deep Learning Algorithm CNNIJRASETPublicationsBelum ada peringkat
- Final Doc Cbir (Content Based Image Retrieval) in Matlab Using Gabor WaveletDokumen69 halamanFinal Doc Cbir (Content Based Image Retrieval) in Matlab Using Gabor WaveletSatyam Yadav100% (1)
- Image Inpainting For Gap Filling and Text Abstraction by Using Optical Character RecognitionDokumen5 halamanImage Inpainting For Gap Filling and Text Abstraction by Using Optical Character RecognitionEditor IJRITCCBelum ada peringkat
- Information Technology BY A.Anil (006-09-5001) R.Gaurav Singh (006-08-5012)Dokumen23 halamanInformation Technology BY A.Anil (006-09-5001) R.Gaurav Singh (006-08-5012)navatha25Belum ada peringkat
- Copy-Move Forgery Detection Using DCTDokumen5 halamanCopy-Move Forgery Detection Using DCTijeteeditorBelum ada peringkat
- DV1614: Basic Edge Detection Using PythonDokumen5 halamanDV1614: Basic Edge Detection Using PythonvikkinikkiBelum ada peringkat
- Secured Data Hiding by Using Extended VisualDokumen5 halamanSecured Data Hiding by Using Extended VisualInternational Journal of Research in Engineering and TechnologyBelum ada peringkat
- Currency Recognition On Mobile Phones Proposed System ModulesDokumen26 halamanCurrency Recognition On Mobile Phones Proposed System Moduleshab_dsBelum ada peringkat
- Ip 42 612 620 PDFDokumen9 halamanIp 42 612 620 PDFlambanaveenBelum ada peringkat
- VC of IRIS Images For ATM Banking: S. Koteswari P. John Paul S. IndraniDokumen5 halamanVC of IRIS Images For ATM Banking: S. Koteswari P. John Paul S. IndraniSaiaditya AdityaBelum ada peringkat
- Image Segmentation: Universidad Central "Marta Abreu" de Las Villas Departamento de Automática y Sistemas ComputacionalesDokumen25 halamanImage Segmentation: Universidad Central "Marta Abreu" de Las Villas Departamento de Automática y Sistemas ComputacionalesJose Antonio Rizo DarkinsBelum ada peringkat
- Ijcsn 2012 1 6 20Dokumen6 halamanIjcsn 2012 1 6 20ijcsnBelum ada peringkat
- Breast CancerDokumen40 halamanBreast CancerVamsi ReddyBelum ada peringkat
- Image Processing NotesDokumen2 halamanImage Processing NotesEdu CostaBelum ada peringkat
- 2D Chaos Based Color Image Encryption Using Pseudorandom Key GenerationDokumen6 halaman2D Chaos Based Color Image Encryption Using Pseudorandom Key GenerationInternational Journal of Application or Innovation in Engineering & ManagementBelum ada peringkat
- Simulink Model Based Image SegmentationDokumen4 halamanSimulink Model Based Image Segmentationeditor_ijarcsseBelum ada peringkat
- DIP Mini ProjectDokumen12 halamanDIP Mini ProjectSHIVANSH KASHYAP (RA2011003010988)Belum ada peringkat
- 2 1502352051 - 10-08-2017 PDFDokumen4 halaman2 1502352051 - 10-08-2017 PDFEditor IJRITCCBelum ada peringkat
- FPGA Implementation of Efficient and High Speed Template Matching ModuleDokumen5 halamanFPGA Implementation of Efficient and High Speed Template Matching ModuleseventhsensegroupBelum ada peringkat
- Image Mining Method and Frameworks: Shaikh Nikhat FatmaDokumen11 halamanImage Mining Method and Frameworks: Shaikh Nikhat FatmaInternational Journal of computational Engineering research (IJCER)Belum ada peringkat
- An Overview of Image Steganography Techniques: WWW - Ijecs.inDokumen5 halamanAn Overview of Image Steganography Techniques: WWW - Ijecs.inManan AgarwalBelum ada peringkat
- Image Stagnographyproject SynopsisDokumen13 halamanImage Stagnographyproject SynopsisRamanjit SinghBelum ada peringkat
- A Survey On Indian Coins Identification and Detection Using Blob Analysis Image ProcessingDokumen4 halamanA Survey On Indian Coins Identification and Detection Using Blob Analysis Image ProcessingEditor IJRITCCBelum ada peringkat
- NeurIPS 2020 Swapping Autoencoder For Deep Image Manipulation PaperDokumen14 halamanNeurIPS 2020 Swapping Autoencoder For Deep Image Manipulation PaperhhhBelum ada peringkat
- Channel Estimation Techniques Over MIMO-OFDM SystemDokumen4 halamanChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCBelum ada peringkat
- Importance of Similarity Measures in Effective Web Information RetrievalDokumen5 halamanImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCBelum ada peringkat
- A Review of 2D &3D Image Steganography TechniquesDokumen5 halamanA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCBelum ada peringkat
- Prediction of Crop Yield Using LS-SVMDokumen3 halamanPrediction of Crop Yield Using LS-SVMEditor IJRITCCBelum ada peringkat
- A Study of Focused Web Crawling TechniquesDokumen4 halamanA Study of Focused Web Crawling TechniquesEditor IJRITCCBelum ada peringkat
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDokumen5 halamanDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCBelum ada peringkat
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDokumen3 halamanPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaBelum ada peringkat
- 44 1530697679 - 04-07-2018 PDFDokumen3 halaman44 1530697679 - 04-07-2018 PDFrahul sharmaBelum ada peringkat
- 45 1530697786 - 04-07-2018 PDFDokumen5 halaman45 1530697786 - 04-07-2018 PDFrahul sharmaBelum ada peringkat
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDokumen5 halamanHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaBelum ada peringkat
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDokumen3 halamanSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaBelum ada peringkat
- Itimer: Count On Your TimeDokumen4 halamanItimer: Count On Your Timerahul sharmaBelum ada peringkat
- 41 1530347319 - 30-06-2018 PDFDokumen9 halaman41 1530347319 - 30-06-2018 PDFrahul sharmaBelum ada peringkat
- 49 1530872658 - 06-07-2018 PDFDokumen6 halaman49 1530872658 - 06-07-2018 PDFrahul sharmaBelum ada peringkat
- Paper On Design and Analysis of Wheel Set Assembly & Disassembly Hydraulic Press MachineDokumen4 halamanPaper On Design and Analysis of Wheel Set Assembly & Disassembly Hydraulic Press MachineEditor IJRITCCBelum ada peringkat
- 1988 Mazda 323 Workshop Manual V1.0 (Turbo Only)Dokumen880 halaman1988 Mazda 323 Workshop Manual V1.0 (Turbo Only)Mike Marquez100% (2)
- Tekla SoakwayDokumen2 halamanTekla SoakwayBalaji Naik100% (1)
- Class Routine Final 13.12.18Dokumen7 halamanClass Routine Final 13.12.18RakibBelum ada peringkat
- T54125ADokumen64 halamanT54125ARaúl FroddenBelum ada peringkat
- Visual Metaphor Process BookDokumen18 halamanVisual Metaphor Process Bookmatt8859Belum ada peringkat
- Drilling Jigs Italiana FerramentaDokumen34 halamanDrilling Jigs Italiana FerramentaOliver Augusto Fuentes LópezBelum ada peringkat
- Application Letter For Promotion T2 T3Dokumen24 halamanApplication Letter For Promotion T2 T3FGacadSabadoBelum ada peringkat
- Pascal Die Casting Machine SystemDokumen20 halamanPascal Die Casting Machine Systemenascimento32Belum ada peringkat
- Sop GC6890 MS5973Dokumen11 halamanSop GC6890 MS5973Felipe AndrinoBelum ada peringkat
- Combinational Logic-Part-2 PDFDokumen25 halamanCombinational Logic-Part-2 PDFSAKSHI PALIWALBelum ada peringkat
- Research Project Presentation of Jobairul Karim ArmanDokumen17 halamanResearch Project Presentation of Jobairul Karim ArmanJobairul Karim ArmanBelum ada peringkat
- "Large Quote Goes Here.": Title or Heading HereDokumen2 halaman"Large Quote Goes Here.": Title or Heading HereHesti RianaBelum ada peringkat
- Davis A. Acclimating Pacific White Shrimp, Litopenaeus Vannamei, To Inland, Low-Salinity WatersDokumen8 halamanDavis A. Acclimating Pacific White Shrimp, Litopenaeus Vannamei, To Inland, Low-Salinity WatersAngeloBelum ada peringkat
- Sensor de Temperatura e Umidade CarelDokumen1 halamanSensor de Temperatura e Umidade CarelMayconLimaBelum ada peringkat
- 8051 Programs Using Kit: Exp No: Date: Arithmetic Operations Using 8051Dokumen16 halaman8051 Programs Using Kit: Exp No: Date: Arithmetic Operations Using 8051Gajalakshmi AshokBelum ada peringkat
- Unit 1 - Plant & Eqpt. Safety Apprisal & Control Techq.Dokumen147 halamanUnit 1 - Plant & Eqpt. Safety Apprisal & Control Techq.Madhan MBelum ada peringkat
- I. Objectives Ii. Content Iii. Learning ResourcesDokumen13 halamanI. Objectives Ii. Content Iii. Learning ResourcesZenia CapalacBelum ada peringkat
- Optimizing Stata For Analysis of Large Data SetsDokumen29 halamanOptimizing Stata For Analysis of Large Data SetsTrần Anh TùngBelum ada peringkat
- EXPERIMENT 1 - Bendo Marjorie P.Dokumen5 halamanEXPERIMENT 1 - Bendo Marjorie P.Bendo Marjorie P.100% (1)
- 22 Thành NG Quen Thu C Trên Ielts - FirefighterDokumen2 halaman22 Thành NG Quen Thu C Trên Ielts - FirefighterNinh NguyễnBelum ada peringkat
- Measures of Indicator 1Dokumen2 halamanMeasures of Indicator 1ROMMEL BALAN CELSOBelum ada peringkat
- Ateneo de Naga University: Professional Training For Teacher 4.0Dokumen10 halamanAteneo de Naga University: Professional Training For Teacher 4.0Rosemarie BrionesBelum ada peringkat
- ISO-50001-JK-WhiteDokumen24 halamanISO-50001-JK-WhiteAgustinusDwiSusantoBelum ada peringkat
- World Trends in Municipal Solid Waste ManagementDokumen11 halamanWorld Trends in Municipal Solid Waste ManagementNeima EndrisBelum ada peringkat
- SQL - Day 2: Structured Query LanguageDokumen10 halamanSQL - Day 2: Structured Query LanguageNight KingBelum ada peringkat
- CS3501 Compiler Design Lab ManualDokumen43 halamanCS3501 Compiler Design Lab ManualMANIMEKALAIBelum ada peringkat