Compusoft, 3 (12), 1374-1376 PDF
Diunggah oleh
Ijact EditorDeskripsi Asli:
Judul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Compusoft, 3 (12), 1374-1376 PDF
Diunggah oleh
Ijact EditorHak Cipta:
Format Tersedia
COMPUSOFT, An international journal of advanced computer technology, 3 (12), December-2014 (Volume-III, Issue-XII)
ISSN:2320-0790
Data Wiping and Anti Forensic Techniques
Dr. AJEET SINGH POONIA
Govt. College of Engineering and Technology, Bikaner, India
Abstract: In the era of information technologies every one using the smart phone, laptop, and many other electronic
gadgets. These all have high storage capacity, so people use these devices to store photos, videos, music files,
contacts details, calendar and even personal information also. People when see the new brands or new technologies
in the market they just sell their old phones or electronic gadgets. While selling their gadgets, people behave like
smart person and delete all information containing in it and in the memory card, hard disk etc. and they feel secure
after deleting or formatting the data contained in that devices. Now as we know that deleting the information which
is stored in smart electronic gadgets is not so easy. When we format or delete the information from the media
storage it actually deletes the links of data blocks not the actual data residing in it. So it can be easily recovered your
data by the help of some data recovery tools. When we sell our electronic gadgets to the shopkeeper, he can recover
your personal photos, videos, important information, contact details etc. using the tools available in the market. So
beware while selling your smart phone, laptops and other electronic gadgets those have storage capacity as other
person can miss use it. In this paper we will cover how to efficiently wipe the memory, so that another person cant
recover the required data/information.
Keyword: Data Sanitization Methods; Metadata; Cryptography; Stegnography; Electronic Gadgets:
I.
change or encrypt the information so that data cant
be recovered. In data wiping techniques we overwrite
the existing data by some special character like null
or any random character so we cant recover that
data.
INTRODUCTION
Wiping means erasing the memory content and after
overwriting the memory with some character like null
character and randomized character. After wiping it
become impossible to recover the data existing
previously because it deletes the links to memory
blocks and also replace the memory content with
some new character value. There are various data
wiping and anti forensics techniques available in the
market by which we can avoid these mishappining.
Anti forensics techniques also works in similar way
as data wiping does. By mean of anti forensics
techniques we use some techniques on the storage
devices that data cant recovered. For example meta
data can be erased from the media, so it become
impossible to read that type of file or we can change
first 4 byte of a file that having information about file
type after that we cant identify that which type of
file is this.[1]
Main difference between anti forensics and data
wiping techniques is that in anti forensics technique
we dont delete the data from the storage device we
A.
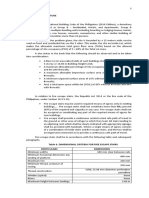
S.No.
1.
2.
1374
Differences between Data Wiping and
Anti Forensics Techniques
There are major following differences
exist between these two
Data Wiping
Anti Forensics
In these techniques
exiting
data
is
overwritten
from
some
special
character
or
randomized
character.
In the data wiping,
more than one pass
can be used, means
The meta data or
file structure is
changed so user is
not able to read the
data.
In these techniques
data
can
be
encrypted so that
COMPUSOFT, An international journal of advanced computer technology, 3 (12), December-2014 (Volume-III, Issue-XII)
we change or alter this data then we cant
read that file. [3]
data
cant
be
recovered without
having
the
encryption key.
It is possible through By tools we can
some tools.
perform encryption
but we have to
manually change the
meta data of the
storage device.
It is very hard to From some tools we
recover data after can recover data
wiping.
even
after
anti
forensics.
Table I Differences between Data
Wiping and Anti Forensics Techniques
many times data can
be overwritten for the
safe deletion.
3.
4.
II.
ANTI FORENSICS TECHNIQUES
A.
Cryptography: Cryptography is the
traditional method of anti forensics. In this
method, data is encrypted using some
encryption methods using a private key. In
future, anyone wants to access the data
needs that private key otherwise data is not
recovered in human readable format. Now
days some tools are available in market by
which we can recover encrypted data also
like Encase higher versions. [3]
B.
Also called data clearing, is a software based
method of overwriting the data that completely
destroys all electronic data residing on the
storage device. Data wiping is method of
overwriting the existing data by null character or
some random character. The following method
can be used for data wiping: [2]
A.
Data Sanitization Method: In data
sanitization method data on hard drive is
overwritten by data destruction program or
file shredder program. If the overwriting is
done through the software then it comes
under the category of data sanitization
method.[4]
B.
File shredder: File shredder is a method
that deletes the files permanently from hard
disk or any storage device. Now it is clear
that what is the data wiping and anti
forensics techniques so it is better that we
should use data wiping techniques for
permanently erasing the data. We will
discuss some tools that are open source and
can be used for data wiping. Our problem is
how to wipe the data while selling the
mobile phones, computer etc. those having
memory them. Here we will discuss both
types of methods for non technical person
and technical person.
Stenography: Stenography also can be used
as anti forensics techniques. In this
technique we can hide our sensitive data
with the image or video file. Because in the
image file some spaces are always available
in that space we can put our message. So
only the receiver knows about the message.
Receiver can easily extract the message
attached to the image file. [3]
C.
Generic Data Hiding: In the storage media
there may be slack areas that are due to
fragmentation of the disk. So we store some
data in those slack areas from that area
forensics tools cant recover data. In
addition to this host protected areas can be
use for hide the data. [3]
D.
Overwriting Metadata: Meta data is the
most important data about data. It helps lot
to read the content of the file. If the Meta
data of a file is altered then it becomes hard
to read that file. Every file structure initial
four bytes uses as the Meta data of a file. If
DATA WIPING TECHNIQUES
III.
IV.
1375
DATA WIPING TOOLS AND
TECHNIQUES
A.
For Non-Technical Person: In era of
internet every one having smart phone and
computer and also switch from one model to
another model after selling the old without
wiping it. So best way to erase or overwrite
your personal information from your mobile
phone memory just store another data like
you can store a movie or music anything.
Now your mobile data or personal
information is overwritten and cant be
recovered. So this method is useful for every
person but not a standard method.
B.
For Technical Background Person: There
are various data wiping software is available
COMPUSOFT, An international journal of advanced computer technology, 3 (12), December-2014 (Volume-III, Issue-XII)
on the internet. We can use open source
software for wiping the storage devices.
VI.
REFERENCES
[1] Defcon paper Anti-forensics Techniques and AntiAnti-Forensics by Michael Perklin.
[2] Counter forensics techniques a brief overview By
1) DBAN (Darik's Boot and Nuke) :It is
free data destruction tool. We can create
a ISO bootable CD or flash drive as
pendrive and then we can boot the
computer directly from the these
bootable CD or Pendrive. It uses
following data sanitization methods
DoD 5220.22-M, RCMP TSSIT OPSII, Gutmann, Random Data, Write Zero.
[5]
2)
CBL Data Shredder: It also can be
used in two forms we can boot it from
the CD or Pendrive for wiping the hard
disk or we can run it as a regular
program for wiping another storage
devices. It uses following data
sanitization methods DoD 5220.22-M,
Gutmann, RMCP DSX, Schneier,
VSITR. We can also select random data
or no of passes for data overwriting. [5]
3)
ErAce: ErAce is very easy to use
because you simply boot from it and
then press one button to wipe all the
data from a drive. Data Sanitization
Methods: DoD 5220.22-M [4]
4)
HDShredder: HDShredder [5] is a
data destruction program that's available
in two forms, both of which work with
one data
wipe method.
Data
Sanitization Methods: Write Zero
[4]
[5]
5) HDDErase: HDDErase [5] is probably
the best Secure Erase based data
destruction software available.Data
Sanitization Methods: Secure Erase
V.
Grant Thornton.
Anti-Forensics A Systems Disruption
Approach.
Data Sanitization Method A List of Software Based
Data Sanitization Methods By Tim Fisher
Data Destruction Software Programs By Tim Fisher
[3] Modern
CONCLUSION
Data wiping techniques are most useful when
we want to permanently erase the data from the
storage devices as compared to Anti Forensic
Techniques. After erasing permanently we can
sell our mobile or computer so that no one can
recover our personal information. So this type of
cyber crime can be controlled if we are little bit
aware about these techniques. Otherwise we
have lots of personal information in our mobile
phone and computer and we delete the entire
information without knowing that it can be
recovered from the recovery software.
1376
Anda mungkin juga menyukai
- Introduction To Mobile Forensics: Data Recovery On Android DevicesDokumen17 halamanIntroduction To Mobile Forensics: Data Recovery On Android DevicesEsteban RamirezBelum ada peringkat
- Data Loss Prevention Technologies: (Manuscript Received April 14, 2009)Dokumen9 halamanData Loss Prevention Technologies: (Manuscript Received April 14, 2009)bbdgei_tnpBelum ada peringkat
- Data Security Technologies: Data Security Is The Means of Ensuring ThatDokumen6 halamanData Security Technologies: Data Security Is The Means of Ensuring ThataadhaBelum ada peringkat
- Secure Data SanitizationDokumen12 halamanSecure Data SanitizationjavaoopBelum ada peringkat
- 10Dokumen29 halaman10vatsb22Belum ada peringkat
- Pros and Cons of Cryptography, Steganography and Perturbation TechniquesDokumen6 halamanPros and Cons of Cryptography, Steganography and Perturbation Techniquesparitosh chandrakapureBelum ada peringkat
- Definition - What Does Data Security Mean?Dokumen4 halamanDefinition - What Does Data Security Mean?Aditia WardaBelum ada peringkat
- Ict Project: by Hareth Hameed of VIII-CDokumen20 halamanIct Project: by Hareth Hameed of VIII-CHameed Ahmed Khas KheliBelum ada peringkat
- Unit 3 NETWORK AND SECURITYDokumen9 halamanUnit 3 NETWORK AND SECURITYdev chauhanBelum ada peringkat
- Data Security: SOFTWARE RESTRICTIONS: The Use of Software Means To Restrict AccessDokumen4 halamanData Security: SOFTWARE RESTRICTIONS: The Use of Software Means To Restrict AccessHolsworth WilsonBelum ada peringkat
- Best Practices For Endpoint Data Loss Prevention: This Report Sponsored byDokumen15 halamanBest Practices For Endpoint Data Loss Prevention: This Report Sponsored byNikitas KladakisBelum ada peringkat
- Information System Assignments 26Dokumen48 halamanInformation System Assignments 26Morgan OkothBelum ada peringkat
- Cyber Security Unit 2 NotesDokumen32 halamanCyber Security Unit 2 NotessakshamBelum ada peringkat
- Dsa 102 Lesson 3Dokumen12 halamanDsa 102 Lesson 3shadowlord468Belum ada peringkat
- Protection of Data Using Various Storage PlatformsDokumen5 halamanProtection of Data Using Various Storage Platformssafdar mehmoodBelum ada peringkat
- 5 1457765073 - 12-03-2016 PDFDokumen6 halaman5 1457765073 - 12-03-2016 PDFEditor IJRITCCBelum ada peringkat
- Privacy Enhancement ComputationDokumen30 halamanPrivacy Enhancement ComputationTheertha SBelum ada peringkat
- Data Security in Cloud StorageDokumen4 halamanData Security in Cloud StorageEditor IJRITCCBelum ada peringkat
- Privacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharDokumen13 halamanPrivacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharrajeshBelum ada peringkat
- Privacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharDokumen13 halamanPrivacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharrajeshBelum ada peringkat
- Privacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharDokumen13 halamanPrivacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharrajeshBelum ada peringkat
- Ans 3: More Documentation Means Easier Usage. More Documentation Means Better Add-On ModulesDokumen3 halamanAns 3: More Documentation Means Easier Usage. More Documentation Means Better Add-On ModulesMohamed AbdulsamadBelum ada peringkat
- ATARC AIDA Guidebook - FINAL KDokumen3 halamanATARC AIDA Guidebook - FINAL KdfgluntBelum ada peringkat
- De-Wipimization: Detection of Data Wiping Traces For Investigating Ntfs File SystemDokumen15 halamanDe-Wipimization: Detection of Data Wiping Traces For Investigating Ntfs File SystemTomas KanevičiusBelum ada peringkat
- Data Security ConsiderationLesson3Dokumen34 halamanData Security ConsiderationLesson3juliafrancel17Belum ada peringkat
- Cyber Security and Privacy: Balancing Convenience and Security in The Era of Big DataDokumen10 halamanCyber Security and Privacy: Balancing Convenience and Security in The Era of Big DataYahya BennaniBelum ada peringkat
- Data Security ConsiderationDokumen14 halamanData Security ConsiderationJames EstreraBelum ada peringkat
- Cybercrimes Solutions Using Digital Forensic ToolsDokumen9 halamanCybercrimes Solutions Using Digital Forensic ToolsSidra ChBelum ada peringkat
- Midterms Module 2 Computer SecurityDokumen30 halamanMidterms Module 2 Computer Securitykerwin OligarioBelum ada peringkat
- RecentDokumen97 halamanRecentSanathBelum ada peringkat
- Singh G. Cisco Certified CyberOps Associate 200-201.guide - .2021Dokumen1.029 halamanSingh G. Cisco Certified CyberOps Associate 200-201.guide - .2021JuanCarlosArias100% (1)
- Discussion NetworkingDokumen4 halamanDiscussion NetworkingNor Fitri Hana JaafarBelum ada peringkat
- Digital Fluency Last Min ReferenceDokumen21 halamanDigital Fluency Last Min Referenceanushatanga7Belum ada peringkat
- CryptographyDokumen77 halamanCryptographyDominic LouiseBelum ada peringkat
- Beginner's Guide for Cybercrime InvestigatorsDari EverandBeginner's Guide for Cybercrime InvestigatorsPenilaian: 5 dari 5 bintang5/5 (1)
- What Is Backup?Dokumen12 halamanWhat Is Backup?jak messiBelum ada peringkat
- Course Instructor: Ngollo T. Kishegena Coursecode: Course Name: System Administration & Security TypeofworkDokumen8 halamanCourse Instructor: Ngollo T. Kishegena Coursecode: Course Name: System Administration & Security Typeofworkmahmoud janBelum ada peringkat
- SteganographyDokumen32 halamanSteganographysathishBelum ada peringkat
- Database Security Research Paper PDFDokumen7 halamanDatabase Security Research Paper PDFyuyglccnd100% (1)
- Data Alteration Detection: A PC To USB Pen Drive PerspectiveDokumen4 halamanData Alteration Detection: A PC To USB Pen Drive PerspectiveInternational Journal of Application or Innovation in Engineering & ManagementBelum ada peringkat
- Data Security: BackupsDokumen5 halamanData Security: BackupsUmesh KanadeBelum ada peringkat
- Cheat SheetDokumen5 halamanCheat Sheetahasanhabib010177Belum ada peringkat
- Three Types of EncryptionDokumen18 halamanThree Types of Encryptionrocky2000097100% (3)
- Ipt NotesDokumen44 halamanIpt NotesEe Yern NgBelum ada peringkat
- DSA102 L3 RemovableMediaDokumen2 halamanDSA102 L3 RemovableMediaLeenBelum ada peringkat
- DatabasesynopsisDokumen15 halamanDatabasesynopsisAJMAL BaigBelum ada peringkat
- 02 - Types of Computer Forensics TechnologyDokumen11 halaman02 - Types of Computer Forensics TechnologyKranthi Kumar Ch80% (5)
- SSRN Id3319251Dokumen5 halamanSSRN Id3319251Hòa Nguyễn Lê MinhBelum ada peringkat
- What Are Data Encryption Solutions?Dokumen4 halamanWhat Are Data Encryption Solutions?Shaban MahekulaBelum ada peringkat
- Using Transparent Encryption To Defeat 12 Common Data BreachesDokumen13 halamanUsing Transparent Encryption To Defeat 12 Common Data BreachesRizqy NurtomoBelum ada peringkat
- Understanding and Selecting Data Masking Solutions: Creating Secure and Useful DataDokumen33 halamanUnderstanding and Selecting Data Masking Solutions: Creating Secure and Useful Dataherind100% (1)
- UNIT4IMDokumen6 halamanUNIT4IMcal,lme MeanwhileBelum ada peringkat
- Short Communication Report: Implementation of A Data and Computer Security ApplicationDokumen3 halamanShort Communication Report: Implementation of A Data and Computer Security Applicationpallavidalal22Belum ada peringkat
- Computer Forensics in Contemporary Times: Issues and ChallengesDokumen13 halamanComputer Forensics in Contemporary Times: Issues and ChallengesKartik SolankiBelum ada peringkat
- Data and Types of DataDokumen8 halamanData and Types of DataRishabh VermaBelum ada peringkat
- Synopsis For Separable Reversible Data Hiding in Encrypted Image Using AESDokumen26 halamanSynopsis For Separable Reversible Data Hiding in Encrypted Image Using AESSanjayBhatia100% (1)
- ComputerDokumen10 halamanComputerkhenoenrileBelum ada peringkat
- The Indian Evidence ActDokumen13 halamanThe Indian Evidence ActnehaBelum ada peringkat
- Unit 1 IT Systems Protecting Data and InformationDokumen9 halamanUnit 1 IT Systems Protecting Data and InformationxfeudalBelum ada peringkat
- Graphical Password Authentication Scheme Using CloudDokumen3 halamanGraphical Password Authentication Scheme Using CloudIjact EditorBelum ada peringkat
- Information Technology in Human Resource Management: A Practical EvaluationDokumen6 halamanInformation Technology in Human Resource Management: A Practical EvaluationIjact EditorBelum ada peringkat
- Role of Information Technology in Supply Chain ManagementDokumen3 halamanRole of Information Technology in Supply Chain ManagementIjact EditorBelum ada peringkat
- Measurement, Analysis and Data Collection in The Programming LabVIEWDokumen5 halamanMeasurement, Analysis and Data Collection in The Programming LabVIEWIjact EditorBelum ada peringkat
- Compusoft, 3 (12), 1369-1373 PDFDokumen5 halamanCompusoft, 3 (12), 1369-1373 PDFIjact EditorBelum ada peringkat
- Compusoft, 3 (11), 1337-1342 PDFDokumen6 halamanCompusoft, 3 (11), 1337-1342 PDFIjact EditorBelum ada peringkat
- Compusoft, 3 (11), 1317-1326 PDFDokumen10 halamanCompusoft, 3 (11), 1317-1326 PDFIjact EditorBelum ada peringkat
- Compusoft, 3 (11), 1276-1281 PDFDokumen6 halamanCompusoft, 3 (11), 1276-1281 PDFIjact EditorBelum ada peringkat
- Compusoft, 3 (11), 1300-1305 PDFDokumen6 halamanCompusoft, 3 (11), 1300-1305 PDFIjact EditorBelum ada peringkat
- Compusoft, 3 (11), 1289-1293 PDFDokumen5 halamanCompusoft, 3 (11), 1289-1293 PDFIjact EditorBelum ada peringkat
- En 10143-1993Dokumen7 halamanEn 10143-1993Eduardo TeixeiraBelum ada peringkat
- Getting Started in Steady StateDokumen24 halamanGetting Started in Steady StateamitBelum ada peringkat
- Teacher Empowerment As An Important Component of Job Satisfaction A Comparative Study of Teachers Perspectives in Al Farwaniya District KuwaitDokumen24 halamanTeacher Empowerment As An Important Component of Job Satisfaction A Comparative Study of Teachers Perspectives in Al Farwaniya District KuwaitAtique RahmanBelum ada peringkat
- Amanuel MekonnenDokumen125 halamanAmanuel Mekonnenabata yohannesBelum ada peringkat
- Catholic Social TeachingsDokumen21 halamanCatholic Social TeachingsMark de GuzmanBelum ada peringkat
- Maya Evaluating InterfacesDokumen6 halamanMaya Evaluating InterfacesChristopher WalkerBelum ada peringkat
- Low Invasion CoringDokumen4 halamanLow Invasion CoringKHALEDFEKAIRBelum ada peringkat
- Renaissance QuestionsDokumen3 halamanRenaissance QuestionsHezel Escora NavalesBelum ada peringkat
- Problems 1Dokumen2 halamanProblems 1Andoy Don M.Belum ada peringkat
- DPL MDDokumen3 halamanDPL MDCoy IngramBelum ada peringkat
- DOPE Personality TestDokumen8 halamanDOPE Personality TestMohammed Hisham100% (1)
- Ens Air To Water Operation ManualDokumen8 halamanEns Air To Water Operation ManualcomborBelum ada peringkat
- Lifestyle Mentor. Sally & SusieDokumen2 halamanLifestyle Mentor. Sally & SusieLIYAN SHENBelum ada peringkat
- Intro To Geometric Design and Vertical AlignmentDokumen25 halamanIntro To Geometric Design and Vertical AlignmentAhsan ArfanBelum ada peringkat
- (Dust of Snow) & 2 (Fire and Ice) - NotesDokumen3 halaman(Dust of Snow) & 2 (Fire and Ice) - NotesdakshBelum ada peringkat
- Strata Ene 2023Dokumen8 halamanStrata Ene 2023gabyBelum ada peringkat
- Remote Sensing: Carbon Stocks, Species Diversity and Their Spatial Relationships in The Yucatán Peninsula, MexicoDokumen18 halamanRemote Sensing: Carbon Stocks, Species Diversity and Their Spatial Relationships in The Yucatán Peninsula, MexicoSara EspinozaBelum ada peringkat
- Sex, Law, and Society in Late Imperial China (Law, Society, and Culture in China) by Matthew SommerDokumen444 halamanSex, Law, and Society in Late Imperial China (Law, Society, and Culture in China) by Matthew SommerFer D. MOBelum ada peringkat
- A Research Paper On DormitoriesDokumen5 halamanA Research Paper On DormitoriesNicholas Ivy EscaloBelum ada peringkat
- Student Material CN Version - 2017.11.10Dokumen25 halamanStudent Material CN Version - 2017.11.10Jagaddeesha BRBelum ada peringkat
- Inspection List For Electrical PortableDokumen25 halamanInspection List For Electrical PortableArif FuadiantoBelum ada peringkat
- Prestressed Concrete ProblemDokumen9 halamanPrestressed Concrete ProblemPrantik Adhar SamantaBelum ada peringkat
- Experiential MarketingDokumen23 halamanExperiential Marketingambesh Srivastava100% (5)
- Engineering Properties (Al O) : 94% Aluminum Oxide Mechanical Units of Measure SI/Metric (Imperial)Dokumen7 halamanEngineering Properties (Al O) : 94% Aluminum Oxide Mechanical Units of Measure SI/Metric (Imperial)Hendy SetiawanBelum ada peringkat
- CV LeTranNguyen enDokumen4 halamanCV LeTranNguyen enLe Tran NguyenBelum ada peringkat
- KIT REQUEST FORM - GradDokumen2 halamanKIT REQUEST FORM - Graddamie aadamsBelum ada peringkat
- Symptoms and DiseasesDokumen8 halamanSymptoms and Diseaseschristy maeBelum ada peringkat
- Executive Shirt CompanyDokumen6 halamanExecutive Shirt CompanyPramod kBelum ada peringkat
- ExerciseDokumen10 halamanExerciseNguyen Mai QuynhBelum ada peringkat
- Addis Ababa University Lecture NoteDokumen65 halamanAddis Ababa University Lecture NoteTADY TUBE OWNER100% (9)