LR SANS Top 20 Whitepaper
Diunggah oleh
pgupta101Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
LR SANS Top 20 Whitepaper
Diunggah oleh
pgupta101Hak Cipta:
Format Tersedia
WHITEPAPER
SANS Top 20 Critical Controls for Cyber Defense
SANS Top 20
Critical Controls for
Effective Cyber Defense
JANUARY 2014
WWW.LOGRHYTHM.COM
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
SANS Top 20 Critical Controls for Effective Cyber Defense
Summary
In a rapidly evolving threat landscape, organizations must
protect their entire IT environment against both external
and internal attacks. Threats and risks arrive from many
angles, requiring security professionals to use a wide variety
of methods to defend against attacks. As a result, many
organizations are now adopting the 20 Critical Security
Controls developed by the SANS Institute. These controls help
organizations prioritize the most effective methods and policies
for safeguarding their assets, information and infrastructure.
This paper outlines how LogRhythms Security Intelligence
Platform maps directly to each of the 20 Critical Security
Controls. The LogRhythm Platform has been specifically
designed to provide real-time, continuous monitoring at the log
layer. LogRhythm collects, normalizes and analyzes all available
log and machine data in real time. All data is immediately
forwarded to the AI Engine, LogRhythms patented Machine
Analytics technology, for advanced behavioral and statistical
analysis to deliver true visibility into all activity observed within
the environment.
organizations maintain a secure
network. Alerts can be sent
to groups or individuals, and
can also be suppressed for a
configurable period of time while
investigations are carried out.
Reports for manual review can
be generated either on-demand or scheduled for delivery. For
additional ease of deployment and streamlined administration,
multiple list management templates are provided that enable
organizations to simplify the process of aligning specific
components to individual organizational requirements.
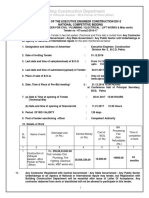
The SANS Critical Controls are listed in the table below, with an
outline of how LogRhythm can support the implementation of
each control.
This document has been created based on version 4.1 of the
Critical Controls.
By combining machine data with both external and internal
context such as geographic location and user logins,
LogRhythm is able to establish normal behavioral patterns,
thus enabling real-time detection of abnormal behavior.
And LogRhythm goes beyond monitoring and detection by
providing automated, intelligent remediation capabilities via
SmartResponseTM . This combination of capabilities delivers
greater accuracy in threat detection and automates key
components of the response process, accelerating remediation
times. LogRhythm empowers organizations to manage
risk more effectively while also reducing the Total Cost of
Ownership for their Security Intelligence program.
Protecting Critical Information
LogRhythm provides a broad range of out-of-the-box advanced
alerts, investigations, and reports that map directly to various
components of the SANS Critical Controls in an effort to help
WWW.LOGRHYTHM.COM
PAGE 1
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
SANS Top 20 Critical Controls for Cyber Security
Critical Control
1
Inventory of Authorized and
Unauthorized Devices
Description
The processes and tools used to track/control/
prevent/correct network access by devices
(computers, network components, printers,
anything with IP addresses) based on an asset
inventory of which devices are allowed to
connect to the network.
LogRhythm Supporting Capability
LogRhythm can import from asset databases, and
correlate actual devices present on the network against
lists of approved devices. LogRhythm can also collect
logs from DHCP servers to help detect unknown or
unauthorized systems.
LogRhythm supports the Control 1 Metric by identifying
new unauthorized devices being connected to the
network in near real time (for example via DHCP logs).
LogRhythm offers the ability through SmartResponseTM
to automatically isolate the system from the network (for
example by disabling the appropriate switch port) once an
approval process has been completed.
Inventory of Authorized and
Unauthorized Software
The processes and tools organizations use to
track/control/prevent/correct installation and
execution of software on computers based on an
asset inventory of approved software.
LogRhythm monitors for the installation or execution
of unauthorized software. LogRhythm can also create
and maintain dynamic lists of approved software based
on behavioral monitoring that may be operated in the
environment.
LogRhythm supports the Control 2 Metric by identifying
attempts to install unauthorized software (for example
via Windows application logs), by identifying attempts to
execute unauthorized software (by monitoring process
startups).
LogRhythm offers the ability through SmartResponseTM
to automatically terminate execution of unauthorized
software, or otherwise quarantine the affected system
once an approval process has been completed.
Secure Configurations for
Hardware and Software on
Mobile Devices, Laptops,
Workstations, and Servers
The processes and tools organizations use
to track/control/prevent/correct security
weaknesses in the configurations of the hardware
and software of mobile devices, laptops,
workstations, and servers based on a formal
configuration management and change control
process.
LogRhythm monitors the use of privileged or generic
accounts, the startup of services, the use of ports, and
the application of patches. LogRhythm can also detect
changes to key files through its File Integrity Monitor.
LogRhythm supports the Control 3 Metric by identifying
changes to key files, services, ports, configuration files, or
software installed on the system.
LogRhythm has the ability through SmartResponseTM
to automatically respond to file or service changes, or
otherwise quarantine the affected system.
Continuous Vulnerability
Assessment and Remediation
The processes and tools used to detect/
prevent/correct security vulnerabilities in the
configurations of devices that are listed and
approved in the asset inventory database.
LogRhythm collects logs from vulnerability scanners. It is
able to correlate event logs with data from vulnerability
scans. LogRhythm can monitor the use of the account
that was used to perform the vulnerability scan.
LogRhythm supports the Control 4 Metric by collecting
logs and data from vulnerability scans. This enables
LogRhythm to correlate both the data from the scan and
the logs about the scan, providing the basis to report
on progress of the vulnerability scan, and of any devices
where the scan did not take place. LogRhythm can also
collect logs relating to patch installation, and can trigger
an alert based on successful completion.
WWW.LOGRHYTHM.COM
PAGE 2
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
Critical Control
5
Malware Defenses
Description
The processes and tools used to detect/prevent/
correct installation and execution of malicious
software on all devices.
LogRhythm Supporting Capability
LogRhythm collects logs from malware detection tools
and correlate those logs with other data collected
in real time to eliminate false positives and detect
blended threats. LogRhythm can also collect logs from
email and web-content filtering tools. Via its advanced
Agent, LogRhythm can detect and report data copied
to removable storage devices. LogRhythm is tightly
integrated with industry-leading security vendors
including FireEye, Sourcefire, Fortinet and Palo Alto
among many others.
LogRhythm supports the Control 5 Metric by continually
collecting and monitoring logs from a wide variety of
malware detection tools, in addition to its own agent
technology.
LogRhythm has the ability through SmartResponseTM to
automatically terminate the execution of unauthorized
software and quarantine any affected systems.
Application Software Security
The processes and tools organizations use to
detect/prevent/correct security weaknesses in
the development and acquisition of software
applications.
LogRhythm collects logs from web application firewalls,
and from vulnerability scanners. LogRhythm also
offers a built-in Web Application Defense Module via its
knowledge base.
LogRhythm supports the Control 6 Metric through the
LogRhythm Web Application Defense Module which
is designed to leverage web log data with a focus on
detection, identification, and prevention of security
related issues. By design, this module can be used in
combination with Intrusion Detection Systems and
Web Application Firewalls or on its own. Because
of LogRhythms ability to correlate across various
applications and device logs at once, it is especially well
positioned to create meaningful, relevant alerts around
suspicious web log data. The Web Application Defense
Module provides out-of-the-box alerts for detecting
Suspicious URL Characters and malicious user agent
strings, in addition to automatically populating an
attacking IPs list. This list enables reporting to be done
on source IPs that are attacking web applications.
LogRhythm collects logs from WAFs and IDS/IPS systems,
in addition to vulnerability scanners. All security event
logs are correlated in real time.
LogRhythm has the ability through SmartResponseTM to
automatically push a new configuration to a firewall (for
example via the Palo Alto API), or otherwise quarantine
the affected system.
Wireless Device Control
The processes and tools used to track/control/
prevent/correct the security use of wireless
local area networks (LANS), access points, and
wireless client systems.
LogRhythm collects logs from a variety of wireless
devices and management systems. In conjunction with
logs collected from DHCP servers, wireless clients may be
detected connecting to the organizations network.
LogRhythm supports the Control 7 Metric by collecting
logs from wireless devices, wireless management
systems, and DHCP. Real time correlation of these logs
enables the identification of unauthorized wireless
devices or configurations.
LogRhythm has the ability through SmartResponseTM to
automatically isolate the system from the network (for
example by disabling the appropriate switch port).
WWW.LOGRHYTHM.COM
PAGE 3
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
Critical Control
Description
LogRhythm Supporting Capability
Data Recovery Capability
The processes and tools used to properly back up
critical information with a proven methodology
for timely recovery of it.
LogRhythm collects logs from Windows and other backup
systems. Through the AI Engine, LogRhythm can detect
backups that did not successfully complete, or backups
that did not start.
There is no Metric for Control 8.
Security Skills Assessment
and Appropriate Training to
Fill Gaps
The process and tools to make sure an
organization understands the technical skill gaps
within its workforce, including an integrated
plan to fill the gaps through policy, training, and
awareness.
SANS Control 9 is policy based and focuses on skills and
training. LogRhythm is able to monitor user compliance
with policy and send alerts in real time where credentials
are used in an abnormal manner. Since all user activity is
logged and collected, correlation and reporting are
effective methods for monitoring adherence to policy.
There is no Metric for Control 9.
10
Secure Configurations for
Network Devices such as
Firewalls, Routers, and
Switches
The processes and tools used to track/control/
prevent/correct security weaknesses in the
configurations in network devices such as
firewalls, routers, and switches based on formal
configuration management and change control
processes.
LogRhythm collects logs from any network device that
generates syslog or SNMP.
LogRhythm supports the Control 10 Metric by collecting
logs from network devices and correlating changes
against a change control system to identify and alert on
any unauthorized changes.
LogRhythm has the ability through SmartResponseTM
to automatically shut down any services performing
unauthorized changes.
11
Limitation and Control of
Network Ports, Protocols, and
Services
The processes and tools used to track/control/
prevent/correct use of ports, protocols, and
services on networked devices.
By collecting logs from port scanners, LogRhythm is able
to detect open ports on the network. LogRhythm can also
collect logs on protocols in use and services starting up
on individual devices.
LogRhythm supports the Control 11 Metric by collecting
logs from across the environment and baselining the
behavior patterns observed over a period of time.
Using this baseline, deviations from normal or expected
behavior can be detected and alerts generated.
LogRhythms AI Engine and list management capabilities
can alert on the use of non-authorized ports in the
environment in real time.
12
Controlled Use of
Administrative Privileges
The processes and tools used to track/control/
prevent/correct the use, assignment, and
configuration of administrative privileges on
computers, networks, and applications.
LogRhythm collects logs from almost any device and can
monitor the use of default, generic, service and other
privileged accounts.
LogRhythm supports the Control 11 Metric by collecting
logs on administrative activity from across the
infrastructure. LogRhythm offers an out-of-the-box
Privileged User Monitoring Module, which simplifies the
task of tracking and monitoring accounts with elevated
privileges and automates a number of tasks that are
generally done manually. By design, this module can be
used in combination with multiple operating systems
(various Linux distributions, Windows, Solaris, etc.)
in addition to MS Exchange server 2007 and 2010.
LogRhythms unique ability to simultaneously correlate
data across multiple applications and devices strengthens
privileged user monitoring and exposes suspicious
activity performed by administrative accounts.
WWW.LOGRHYTHM.COM
PAGE 4
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
Critical Control
13
14
Boundary Defense
Maintenance, Monitoring, and
Analysis of Audit Logs
Description
LogRhythm Supporting Capability
The processes and tools used to detect/prevent/
correct the flow of information transferring
networks of different trust levels with a focus on
security-damaging data.
LogRhythm collects logs from a wide variety of boundary
defense devices for correlation or compliance purposes.
The processes and tools used to detect/prevent/
correct the use of systems and information
based on audit logs of events that are considered
significant or could impact the security of an
organization.
LogRhythm provides a comprehensive platform for the
maintenance, monitoring and analysis of audit logs.
LogRhythm supports the Control 12 Metric by collecting
logs from boundary defense devices in addition to
NetFlow data. LogRhythm can build trends of data flows
based on observed behavior and alert on deviations from
normal behavior. By understanding the internal network
infrastructure, internal and external context can be added
to alerts, helping identify unexpected traffic flows such as
a website in the DMZ communicating directly with a SQL
database, rather than communicating via the application
layer. LogRhythm also offers out-of-the-box support for
third party threat lists and custom IP address blacklists
and can alert in real- time when connections are made to
any blacklisted IP address or host.
LogRhythm supports the Control 14 Metric by collecting
all events from across the network. LogRhythm offers
silent log source detection in order to validate that
devices are still generating logs, and has comprehensive
time normalization abilities to ensure that the SIEM
engine sees the logs in the actual order they occurred.
LogRhythm performs extensive processing of every
log that is collected, assigning a common event and
establishing a risk based priority for each log.
LogRhythms patented real-time analytics technology, the
AI Engine, can baseline behavior of users, hosts and data
from across the network. Once a baseline is established,
abnormal behavior can be detected and alarmed on.
15
Controlled Access Based on
the Need to Know
The processes and tools used to track/control/
prevent/correct secure access to information
according to the formal determination of which
persons, computers, and applications have a
need and right to access information based on an
approved classification.
LogRhythm collects audit logs from across the network.
Fully integrated File Integrity Monitoring capabilities
monitor for and alert on a variety of malicious behaviors,
including improper user access of confidential files to
botnet related breaches and transmittal of sensitive data.
LogRhythm supports the Control 15 Metric by collecting
logs of all attempts by users to access files on local
systems or network accessible file shares without the
appropriate privileges. LogRhythms File Integrity
Monitor can also be used to establish a baseline of
normal behavior against a file or fileset, and can alert on
deviations from that behavioral baseline.
WWW.LOGRHYTHM.COM
PAGE 5
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
16
Critical Control
Description
Account Monitoring and
Control
The processes and tools used to track/control/
prevent/correct the use of system and application
accounts.
LogRhythm Supporting Capability
LogRhythm collects audit logs from across the network
for both local and network accounts.
LogRhythm supports the Control 16 Metric by collecting
logs of all user activity and correlating this with lists of
privileged, generic, and service accounts, and also with
lists of accounts for users that are terminated. Using
a SmartResponseTM plug-in, lists can be automatically
maintained when changes take place in the environment.
LogRhythm can alert when the use of terminated
accounts are observed, and offers extensive reporting
capabilities in this area.
LogRhythm can also establish baselines of normal
account behavior. For example, LogRhythm can track
which servers a user normally connects to, and alert on
deviation from that norm.
17
Data Loss Prevention
The processes and tools used to track/control/
prevent/correct data transmission and storage,
based on the datas content and associated
classification.
LogRhythm collects logs from both endpoints and
network perimeter devices in order to assist in the
detection of data loss incidents. LogRhythm also provides
basic Data Loss Detection functionality in its advanced
agent technology.
LogRhythm supports the Control 17 Metric by collecting
logs from endpoints, authentication systems, boundary
defense devices, proxies and email servers amongst
others. LogRhythm is able to detect abnormal activity
(e.g. upload of large number of files to Internet based
file sharing facilities) in real time and take immediate
action via a SmartResponseTM plug-in that can block user
access, or terminate the process that is exfiltrating the
data.
LogRhythms patented real-time analytics technology,
the AI Engine, is able to establish baselines of behavior.
For example, AI Engine can observe how users work with
a certain set of documents, and alert on deviations from
that behavior.
18
Incident Response and
Management
The process and tools to make sure an
organization has a properly tested plan with
appropriate trained resources for dealing with
any adverse events or threats of adverse events.
SANS Control 18 is policy based and focuses on having a
clear Incident Response policy.
LogRhythm has an integrated incident management
capability providing real-time updates on an incidents
status (i.e., working, closed, etc.). Status and commentary
can be attached to each alert and progress reports can be
generated on demand.
There is no Metric for Control 18.
19
Secure Network Engineering
The process and tools used to build, update,
and validate a network infrastructure that can
properly withstand attacks from advanced
threats.
SANS Control 19 is focused on the design of the network.
By bringing understanding of the internal network design
into LogRhythm, this information can be used to identify
unexpected traffic flows such as sensitive systems being
accessed directly from the Internet.
There is no Metric for Control 19.
WWW.LOGRHYTHM.COM
PAGE 6
WHITEPAPER - SANS TOP 20 CRITICAL CONTROLS FOR CYBER DEFENSE
Critical Control
20
Penetration Tests and Red
Team Exercises
Description
LogRhythm Supporting Capability
The process and tools used to simulate attacks
against a network to validate the overall security
of an organization.
LogRhythm collects logs from across the environment.
It is a valuable monitoring tool during any penetration
test, or red team exercise. LogRhythm enables the
accounts used in the penetration test to be automatically
monitored for legitimate use. LogRhythm also enables the
detection of unusual behavior and may be used to detect
the attempts to exploit the enterprise systems during
penetration testing.
There is no Metric for Control 20.
INFO@LOGRHYTHM.COM
PAGE 7
2014 LogRhythm Inc. | Whitepaper - SANS Top 20 Critical Controls for Cyber Defense
Anda mungkin juga menyukai
- Implementation Guide 2330: Standard 2330 - Documenting InformationDokumen4 halamanImplementation Guide 2330: Standard 2330 - Documenting Informationpgupta101Belum ada peringkat
- Find People, Jobs, Companies, and More Search For:: Skip To Main ContentDokumen9 halamanFind People, Jobs, Companies, and More Search For:: Skip To Main Contentpgupta101Belum ada peringkat
- Why Do You Want This Senior It Auditor Job?: Negotiate and Be Assertive at The Same TimeDokumen10 halamanWhy Do You Want This Senior It Auditor Job?: Negotiate and Be Assertive at The Same Timepgupta101Belum ada peringkat
- HindiDokumen1 halamanHindipgupta101Belum ada peringkat
- Cisa 1 10% The Is Audit Process 82 Q OnlyDokumen16 halamanCisa 1 10% The Is Audit Process 82 Q Onlypgupta101Belum ada peringkat
- Network Infrastructure Auditing ChecklistDokumen2 halamanNetwork Infrastructure Auditing Checklistolfa0Belum ada peringkat
- IT Audit ChecklistDokumen38 halamanIT Audit Checklistpgupta10167% (3)
- Section 3: Appendix: 1. Audit Checklist: Risk Management ProcessDokumen3 halamanSection 3: Appendix: 1. Audit Checklist: Risk Management Processpgupta101Belum ada peringkat
- Audit of Security Management: Sl. No. Audit Area Test ProceduresDokumen1 halamanAudit of Security Management: Sl. No. Audit Area Test Procedurespgupta101Belum ada peringkat
- Physical and Environmental Audit ChecklistDokumen4 halamanPhysical and Environmental Audit Checklistpgupta101Belum ada peringkat
- DeltaV Cyber SecurityDokumen8 halamanDeltaV Cyber Securitypgupta101Belum ada peringkat
- Microsoft Baseline Security An PDFDokumen5 halamanMicrosoft Baseline Security An PDFpgupta101Belum ada peringkat
- Oracle DBA Workshop IIDokumen4 halamanOracle DBA Workshop IIpgupta101Belum ada peringkat
- Comptia Security Sy0 401Dokumen24 halamanComptia Security Sy0 401pgupta101Belum ada peringkat
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- Autodesk Student Account Creation Manual With ActivitesDokumen17 halamanAutodesk Student Account Creation Manual With ActivitesBharath WajBelum ada peringkat
- Sam Ovens Funnel ChecklistDokumen3 halamanSam Ovens Funnel Checklistg100% (1)
- Configuring Yahoo Messenger-: Step 1Dokumen1 halamanConfiguring Yahoo Messenger-: Step 1RaffyLaguesmaBelum ada peringkat
- Mobility Management GSM Technology AircomDokumen12 halamanMobility Management GSM Technology Aircomaudi_r8Belum ada peringkat
- Vega Series Analog/Digital GatewaysDokumen2 halamanVega Series Analog/Digital GatewaysMiguel Andres VanegasBelum ada peringkat
- Secflow-1v DsDokumen8 halamanSecflow-1v DsclaupasinaBelum ada peringkat
- 839-4816 (Office) or (770) 301-8648 (Cell) : Corporate Finance: A Focused Approach, by Michael C. Ehrhardt / Eugene FDokumen1 halaman839-4816 (Office) or (770) 301-8648 (Cell) : Corporate Finance: A Focused Approach, by Michael C. Ehrhardt / Eugene FlilbouyinBelum ada peringkat
- Netwrk Aptitude1Dokumen4 halamanNetwrk Aptitude1Thilina PathiranaBelum ada peringkat
- Cheating Prevention in Visual CryptographtDokumen4 halamanCheating Prevention in Visual CryptographtvaddeseetharamaiahBelum ada peringkat
- Himabindu GeraDokumen6 halamanHimabindu GeraAvishek Datta GuptaBelum ada peringkat
- Building Construction Department: Construction of Vidhayak Awasan - MLA Parisar at Patna (Bihar)Dokumen3 halamanBuilding Construction Department: Construction of Vidhayak Awasan - MLA Parisar at Patna (Bihar)PERVEZ AHMAD KHANBelum ada peringkat
- SEC Railway Bhilai 1418201585123 - NITDokumen2 halamanSEC Railway Bhilai 1418201585123 - NITjjtrivedi8717Belum ada peringkat
- Alu - A7302 Isam Fttu Operator Gpon Nant-E - Ce PDFDokumen433 halamanAlu - A7302 Isam Fttu Operator Gpon Nant-E - Ce PDFszejkdudi100% (1)
- Programme: Teresa National High SchoolDokumen2 halamanProgramme: Teresa National High SchoolRobert Merginio CatapusanBelum ada peringkat
- FCT CMMS-ST ManualDokumen134 halamanFCT CMMS-ST ManualRobin Van de BeekBelum ada peringkat
- The Chelsea Standard Front January 24, 2013Dokumen1 halamanThe Chelsea Standard Front January 24, 2013Kathleen Steffen MurphyBelum ada peringkat
- C Vuser Functions in Loadrunner: Home Project Management Certification Papers Join UsDokumen18 halamanC Vuser Functions in Loadrunner: Home Project Management Certification Papers Join UssanthoshjshBelum ada peringkat
- Hacking With LinuxDokumen102 halamanHacking With LinuxAndres Pedroza100% (1)
- WSTG (Web Application Security Testing) OWASP - Mind MapDokumen1 halamanWSTG (Web Application Security Testing) OWASP - Mind MapMatheus FragaBelum ada peringkat
- UAE Digest March 09Dokumen68 halamanUAE Digest March 09Fa Hian100% (6)
- Spip User Manual Public PDFDokumen124 halamanSpip User Manual Public PDFJoel FBelum ada peringkat
- USA TODAY CEO Forum at The University of WashingtonDokumen6 halamanUSA TODAY CEO Forum at The University of WashingtonUSA TODAY EducationBelum ada peringkat
- Telecom Manager Interview QuestionsDokumen5 halamanTelecom Manager Interview Questionsteenu1100% (1)
- StitchedDokumen1 halamanStitchedScribd Dot ComBelum ada peringkat
- 2016 CPRA Log - Rancho CucamongaDokumen25 halaman2016 CPRA Log - Rancho CucamongaBeau YarbroughBelum ada peringkat
- A Survey On Google Project Loon Google BalloonDokumen3 halamanA Survey On Google Project Loon Google BalloonEditor IJTSRDBelum ada peringkat
- 11 18 0477 00 00ax Punctured NDPDokumen9 halaman11 18 0477 00 00ax Punctured NDPrfidguysBelum ada peringkat
- Blackbook (35 & 48)Dokumen62 halamanBlackbook (35 & 48)Pinky SinghBelum ada peringkat
- K2000 Admin Guide v33Dokumen170 halamanK2000 Admin Guide v33amlesh80100% (1)
- MM Communication CourseDokumen6 halamanMM Communication CourseHosein SoleimaniBelum ada peringkat