(IJCST-V4I5P43) :sharmila Chopade, Mohini Mohite, Bhagyashri Narwade, Mahadevi Barche
Diunggah oleh
EighthSenseGroupJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
(IJCST-V4I5P43) :sharmila Chopade, Mohini Mohite, Bhagyashri Narwade, Mahadevi Barche
Diunggah oleh
EighthSenseGroupHak Cipta:
Format Tersedia
International Journal of Computer Science Trends and Technology (IJCST) Volume 4 Issue 5, Sep - Oct 2016
RESEARCH ARTICLE
OPEN ACCESS
Increasing the Quality of Security of Mobile Ad-Hoc Networks
Sharmila Chopade, Mohini Mohite, Bhagyashri Narwade, Mahadevi Barche
Computer Department
Pune University, DYPIET Ambi
India
ABSTRACT
Security enhancement have become popular as a key communication technology in military tactical environments such as
establishment of communication networks used to co-ordinate military deployment among the soldiers, vehicles and operational
command centers. Military environments has many risks needed to be considered seriously due to the clear features of
MANETs, including open wireless link, lack of centralized infrastructure of security protection. Security Trust Management
Scheme and Trust Identity Acknowledgment (TIA) are the two solutions for the risk. Direct observation and indirect
observation are two components of trust management scheme. The trust value is calculated using Bayesian inference in direct
observation and the trusts value is calculated using the Dempster -Shafer Theory (DST) in indirect observation. The throughput
and Packet Delivery Ratio (PDR) of observed node is improved and security is maintained and enhanced.
Keywords:- MANET-Mobile Ad Hoc Network, Security Trust Management (STM), Trust Identity Acknowledgement (TIA),
Dempster-Shafer Theory (DST), Security Enhancement (SE).
I.
INTRODUCTION
MANET is the collection of nodes that connect with each
other with the help of wireless link. Nodes are moved from
one place to another place in topology. Node is co-operating
with each other and route the packets. Trust on the node and
managing nodes are the major issues in MANET because of
having the less resource and process complexity. MANET is a
challenging research factor because of security. The two
complementary classes of approaches of MANETs, one is
prevention-based approach and second is detection based
approach. A centralized key management infrastructure is one
of the issue of the Prevention based approach, which may not
be realistic in MANETs such as distributed networks.
Prevention based approaches can prevent misbehavior.
Detection based approaches can identify malicious activities
based on trust. Some excellent work has been done on
detection based approaches in MANETs. Detection based
approaches do not support direct and indirect observation at
the same time to evaluate the trust of an observed node.
Indirect observation is used to access the reliability of nodes.
Data packets and control packets are do not differentiate by
trust methods. Detection of packet drop uses TWOACK, SACK, AACK acknowledgement schemes to overcome the
defects. TWOACK method is used to detect misbehaving link
by acknowledging data packets transmitted over each nodes
along with the path from source to destination. MANETs
control packets usually are more important than data packets.
MANET interprets trust, that a node performs as expected.
MANET proposes a trust management scheme to increase the
ISSN: 2347-8578
quality of the security of MANETs with the help of
interpretation.
II. MOTIVATION
MANET propose, security management schemes that
enhances the security of MANET. The Bayesian inferences
DST protocol used to calculate the trust value of observed
node in the MANETS. The malicious activity, missing
packets or modifying packets can be detected through the trust
value. Trust value can be calculated by the trust direct and
indirect value.
III. LITERATURE SURVEY
A. Securing mobile ad hoc networks with certificate less
public keys (CPK) [3]: As the future research, intend to
determine the efficiency of the proposed schemes through
simulations and practical implementations.
B. Survey of Secure Mobile Ad Hoc Routing Protocols [1]:
Several routing protocols have been used in Mobile Ad hoc
Networks (MANETs) such as military, government &
commercial applications. These protocols focus on security
issues and differentiate in terms of routing methodologies.
AODV, DSR, OLSR and TORA protocols are most widely
used for analysis and evaluation.
www.ijcstjournal.org
Page 220
International Journal of Computer Science Trends and Technology (IJCST) Volume 4 Issue 5, Sep - Oct 2016
C. Mitigating routing misbehavior in mobile ad hoc networks
(MRM)[2]: Mitigation would like to evaluate the watchdog
and considering latency in addition to throughput.
D. Structural Results for Combined Continuous User
Authentication and Intrusion Detection in High Security
Mobile Ad-Hoc Networks (CCAID) [6]: Malicious activities
can be identified. Intrusion detection systems (IDSs) and user
authentication these two approaches jointly consider for
effective security design. Continuous user authentication is an
important prevention-based approach to protect high security
mobile ad-hoc networks (MANETs). Intrusion detection
systems (IDSs) are also important in MANETs to effectively
identify malicious activities.
E. hierarchical identity based key management scheme in
tactical mobile ad hoc networks (HTM) [5]: As the future
research, directions to develop trust management model with
desirable attributes such as adaptation to environmental
dynamics, scalability, reliability, and reconfigurability
F. Securing resource-constrained wireless Ad-hoc networks
(SRC)[4]: The protocols Should be further optimized and
expanded in the future. However, nothing stands in the way of
using mesh networks.
G. A mean field game theoretic approach for security
enhancements in mobile ad hoc networks Wireless
Communication (GTA) [7]: GTA are going to extend trust
aware with energy aware AODV protocol. While knowledge
forwarding, the nodes can amendment the trail supported
energy state of each nodes. Thus GTA able to improve the
QOS with improved security. Finally QOS able to improve
prolong network.
Fig. 1 Example of mobile ad hoc network
To explain the basic procedure of trust evaluation in scenario,
an example network is shown in Fig. 1. In this example, node
1 is an observer node, and node 3 is an observed node. Node 1
transmits data through node 3 to node 5. When node 3
receives data messages and forwards to node 5, node 1 can
overhear it. Then, node 1 can evaluate the trust value of node
3 based on data messages. The same idea is applied to control
message situation. Means, node 1 can obtain information from
nodes 2 and 4, which have interactions with node 3 to evaluate
the trust value of node 3. This information obtained from
third-party nodes is called indirection observation
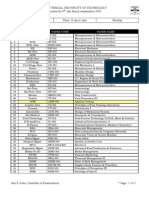
Table 1: Literature Survey
Sr
no
1.
Yea
r
1999
Approache
s
Survey of
Secure
Mobile Ad
Hoc
Routing
Protocols
Mitigation
Routing
Misbehavio
r
Advantages
Limitations
Dynamic
topologies,
bandwidth,
variable
capacity
links.
Increase
throughput,
done without
a priori trust.
Few
works
have been done
on availability
but integrity is
not taken in
consideration.
Mitigation
would like to
evaluate
the
watchdog and
considering
latency
in
addition
to
throughput.
2.
2000
3.
2006
Certificate
Public
Keys
Detecting
and removing
the malicious
nodes
in
network.
4.
2009
Securing
Resource
Constraine
d
5.
2010
Tactical
The protocols
should
be
further
optimized
and expanded
in the future.
The dynamic
CPK intend to
evaluate
and
justify
the
efficiency
of
the
proposed
schemes.
Computational
complexity
of the pairing
operations
IV. SYSTEM DESIGN
ISSN: 2347-8578
www.ijcstjournal.org
Develop
Page 221
trust
International Journal of Computer Science Trends and Technology (IJCST) Volume 4 Issue 5, Sep - Oct 2016
6.
7.
2011
2014
Mobile
node
selection
process
is
formulated.
Combined
Continuous
User
Authenticat
ion
and
Intrusion
Detection
Effectively
identify
malicious
activity.
Game
Theory
Approach
Improve QOS
which able to
improve
prolong
network.
management
model
with
desirable
attributes such
as adaptation.
Mobility and
wireless
channels, for
making
the
scheduling
decisions
in
MANET
are
not considered.
Performance
with
limited
energy.
.
V. CONCLUSION
The security of mobile ad hoc networks enhanced by using
Trust Management Scheme that includes direct and indirect
observations. The use of uncertain reasoning will provide
finest value for the trust variable. Bayesian inference with
direct observation and Dempster Shafer Theory with indirect
observation are used to calculate the trust value. Trust
assurance using fuzzy logic is another better method. Trust
assurance registers each node needed for data transmission
and sends the data.
ACKNOWLEDGEMENT
The authors which making their resources available would
like to thank the publishers, researchers and teachers for their
guidance. We also thank authority of the college for providing
the required infrastructure support. Finally, we would like to
extend heartfelt gratitude to friends and family members.
[2] S. Marti, T. Giuli, K. Lai, and M. Maker, Mitigating
routing misbehavior in mobile ad hoc networks, in
Proc. ACM MobiCom, Aug. 2000, pp. 255265.
[3] Y. Zhang, W. Liu, W. Lou, and Y. Fang, Securing
mobile ad hoc networks with certificateless public
keys, IEEE Trans. Dependable Secure Comput., vol. 3,
no. 4, pp. 386399, Oct.Dec. 2006.
[4] Y. Fang, X. Zhu, and Y. Zhang, Securing resourceconstrained wireless ad hoc networks, IEEE Wireless
Comm., vol. 16, no. 2, pp. 2430, Apr. 2009.
[5] F. R. Yu, H. Tang, P. Mason, and F. Wang, A
hierarchical identity based key management scheme in
tactical mobile ad hoc networks, IEEE Trans. Netw.
Serv. Manag., vol. 7, no. 4, pp. 258267, Dec. 2010.
[6] S. Bu, F. R. Yu, P. Liu, P. Manson, and H. Tang,
Distributed combined authentication and intrusion
detection with data fusion in high-security mobile ad
hoc networks, IEEE Trans. Veh. Technol., vol. 60, no.
3, pp. 10251036, Mar. 2011.
[7] Q. Guan, F. R. Yu, S. Jiang, and V. Leung, Joint
topology control and authentication design in mobile
ad
hoc
networks
with
cooperative
communications,IEEE Trans. Veh. Tech., vol. 61, no.
6, pp. 26742685, Jul. 2012.
[8] Y. Wang, F. R. Yu, H. Tang, and M. Huang, A mean
field game theoretic approach for security
enhancements in mobile ad hoc networks,IEEE Trans.
Wireless Commun., vol. 13, no. 3, pp. 16161627,Mar.
2014.
REFERENCES
[1] S. Corson and J. Macker , Mobile Ad Hoc Networking
(MANET): Routing protocol performance issues and
evaluation considerations, Jan. 1999, IETF RFC
2501.
ISSN: 2347-8578
www.ijcstjournal.org
Page 222
Anda mungkin juga menyukai
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Is 12894: 1990Dokumen6 halamanIs 12894: 1990mukaslam100% (7)
- (IJCST-V12I1P2) :DR .Elham Hamed HASSAN, Eng - Rahaf Mohamad WANNOUSDokumen11 halaman(IJCST-V12I1P2) :DR .Elham Hamed HASSAN, Eng - Rahaf Mohamad WANNOUSEighthSenseGroupBelum ada peringkat
- (IJCST-V11I6P5) :A.E.E. El-Alfi, M. E. A. Awad, F. A. A. KhalilDokumen9 halaman(IJCST-V11I6P5) :A.E.E. El-Alfi, M. E. A. Awad, F. A. A. KhalilEighthSenseGroupBelum ada peringkat
- (IJCST-V12I1P4) :M. Sharmila, Dr. M. NatarajanDokumen9 halaman(IJCST-V12I1P4) :M. Sharmila, Dr. M. NatarajanEighthSenseGroupBelum ada peringkat
- (IJCST-V12I1P7) :tejinder Kaur, Jimmy SinglaDokumen26 halaman(IJCST-V12I1P7) :tejinder Kaur, Jimmy SinglaEighthSenseGroupBelum ada peringkat
- (IJCST-V11I6P8) :subhadip KumarDokumen7 halaman(IJCST-V11I6P8) :subhadip KumarEighthSenseGroupBelum ada peringkat
- (IJCST-V11I4P12) :N. Kalyani, G. Pradeep Reddy, K. SandhyaDokumen16 halaman(IJCST-V11I4P12) :N. Kalyani, G. Pradeep Reddy, K. SandhyaEighthSenseGroupBelum ada peringkat
- (IJCST-V11I4P15) :M. I. Elalami, A. E. Amin, S. A. ElsaghierDokumen8 halaman(IJCST-V11I4P15) :M. I. Elalami, A. E. Amin, S. A. ElsaghierEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P17) :yash Vishwakarma, Akhilesh A. WaooDokumen8 halaman(IJCST-V11I3P17) :yash Vishwakarma, Akhilesh A. WaooEighthSenseGroupBelum ada peringkat
- (IJCST-V11I5P4) :abhirenjini K A, Candiz Rozario, Kripa Treasa, Juvariya Yoosuf, Vidya HariDokumen7 halaman(IJCST-V11I5P4) :abhirenjini K A, Candiz Rozario, Kripa Treasa, Juvariya Yoosuf, Vidya HariEighthSenseGroupBelum ada peringkat
- (IJCST-V11I4P9) :KiranbenV - Patel, Megha R. Dave, Dr. Harshadkumar P. PatelDokumen18 halaman(IJCST-V11I4P9) :KiranbenV - Patel, Megha R. Dave, Dr. Harshadkumar P. PatelEighthSenseGroupBelum ada peringkat
- (IJCST-V11I4P5) :P Jayachandran, P.M Kavitha, Aravind R, S Hari, PR NithishwaranDokumen4 halaman(IJCST-V11I4P5) :P Jayachandran, P.M Kavitha, Aravind R, S Hari, PR NithishwaranEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P25) :pooja Patil, Swati J. PatelDokumen5 halaman(IJCST-V11I3P25) :pooja Patil, Swati J. PatelEighthSenseGroupBelum ada peringkat
- (IJCST-V11I4P3) :tankou Tsomo Maurice Eddy, Bell Bitjoka Georges, Ngohe Ekam Paul SalomonDokumen9 halaman(IJCST-V11I4P3) :tankou Tsomo Maurice Eddy, Bell Bitjoka Georges, Ngohe Ekam Paul SalomonEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P24) :R.Senthilkumar, Dr. R. SankarasubramanianDokumen7 halaman(IJCST-V11I3P24) :R.Senthilkumar, Dr. R. SankarasubramanianEighthSenseGroupBelum ada peringkat
- (Ijcst-V11i4p1) :fidaa Zayna, Waddah HatemDokumen8 halaman(Ijcst-V11i4p1) :fidaa Zayna, Waddah HatemEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P20) :helmi Mulyadi, Fajar MasyaDokumen8 halaman(IJCST-V11I3P20) :helmi Mulyadi, Fajar MasyaEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P21) :ms. Deepali Bhimrao Chavan, Prof. Suraj Shivaji RedekarDokumen4 halaman(IJCST-V11I3P21) :ms. Deepali Bhimrao Chavan, Prof. Suraj Shivaji RedekarEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P12) :prabhjot Kaur, Rupinder Singh, Rachhpal SinghDokumen6 halaman(IJCST-V11I3P12) :prabhjot Kaur, Rupinder Singh, Rachhpal SinghEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P8) :pooja Patil, Swati J. PatelDokumen5 halaman(IJCST-V11I3P8) :pooja Patil, Swati J. PatelEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P13) : Binele Abana Alphonse, Abou Loume Gautier, Djimeli Dtiabou Berline, Bavoua Kenfack Patrick Dany, Tonye EmmanuelDokumen31 halaman(IJCST-V11I3P13) : Binele Abana Alphonse, Abou Loume Gautier, Djimeli Dtiabou Berline, Bavoua Kenfack Patrick Dany, Tonye EmmanuelEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P2) :K.Vivek, P.Kashi Naga Jyothi, G.Venkatakiran, SK - ShaheedDokumen4 halaman(IJCST-V11I3P2) :K.Vivek, P.Kashi Naga Jyothi, G.Venkatakiran, SK - ShaheedEighthSenseGroupBelum ada peringkat
- (IJCST-V11I2P18) :hanadi Yahya DarwishoDokumen32 halaman(IJCST-V11I2P18) :hanadi Yahya DarwishoEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P7) :nikhil K. Pawanikar, R. SrivaramangaiDokumen15 halaman(IJCST-V11I3P7) :nikhil K. Pawanikar, R. SrivaramangaiEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P11) :Kalaiselvi.P, Vasanth.G, Aravinth.P, Elamugilan.A, Prasanth.SDokumen4 halaman(IJCST-V11I3P11) :Kalaiselvi.P, Vasanth.G, Aravinth.P, Elamugilan.A, Prasanth.SEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P9) :raghu Ram Chowdary VelevelaDokumen6 halaman(IJCST-V11I3P9) :raghu Ram Chowdary VelevelaEighthSenseGroupBelum ada peringkat
- (IJCST-V11I2P19) :nikhil K. Pawanika, R. SrivaramangaiDokumen15 halaman(IJCST-V11I2P19) :nikhil K. Pawanika, R. SrivaramangaiEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P1) :Dr.P.Bhaskar Naidu, P.Mary Harika, J.Pavani, B.Divyadhatri, J.ChandanaDokumen4 halaman(IJCST-V11I3P1) :Dr.P.Bhaskar Naidu, P.Mary Harika, J.Pavani, B.Divyadhatri, J.ChandanaEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P4) :V Ramya, A Sai Deepika, K Rupa, M Leela Krishna, I Satya GirishDokumen4 halaman(IJCST-V11I3P4) :V Ramya, A Sai Deepika, K Rupa, M Leela Krishna, I Satya GirishEighthSenseGroupBelum ada peringkat
- (IJCST-V11I3P5) :P Adhi Lakshmi, M Tharak Ram, CH Sai Teja, M Vamsi Krishna, S Pavan MalyadriDokumen4 halaman(IJCST-V11I3P5) :P Adhi Lakshmi, M Tharak Ram, CH Sai Teja, M Vamsi Krishna, S Pavan MalyadriEighthSenseGroupBelum ada peringkat
- (IJCST-V11I2P17) :raghu Ram Chowdary VelevelaDokumen7 halaman(IJCST-V11I2P17) :raghu Ram Chowdary VelevelaEighthSenseGroupBelum ada peringkat
- Hap Carrier Learning-Part 1Dokumen18 halamanHap Carrier Learning-Part 1alishakibniaBelum ada peringkat
- E1 Install GuideDokumen31 halamanE1 Install GuideRahul JaiswalBelum ada peringkat
- Bor11999 NSW Manual Bk1 Structural Fire AccusticDokumen72 halamanBor11999 NSW Manual Bk1 Structural Fire AccusticEmanuel Ifrim100% (1)
- Cve 2012 6081Dokumen25 halamanCve 2012 6081Miguel LozanoBelum ada peringkat
- Walktrough Amnesia The Machine For PigsDokumen9 halamanWalktrough Amnesia The Machine For PigsErie FailenggoBelum ada peringkat
- Manual de Programacion Os7030 SamsungDokumen495 halamanManual de Programacion Os7030 SamsunghugoBelum ada peringkat
- Cable Armado Nema RV1-2004Dokumen36 halamanCable Armado Nema RV1-2004DELMAR QUIROGA CALDERONBelum ada peringkat
- MS440209PM 48G6+ - 207PM 48G6Dokumen8 halamanMS440209PM 48G6+ - 207PM 48G6victor mauricio colonia rangelBelum ada peringkat
- Indice AashtoDokumen71 halamanIndice AashtoFranklinBelum ada peringkat
- HP 245 G3 ZSO41 LA-A997P r1.0Dokumen46 halamanHP 245 G3 ZSO41 LA-A997P r1.0Mirgen Miranda100% (2)
- MCC Instruction Manual Rev PDFDokumen44 halamanMCC Instruction Manual Rev PDFvidhyaBelum ada peringkat
- 04Dokumen13 halaman04kyjwowBelum ada peringkat
- Houghton PCC Case StudyDokumen2 halamanHoughton PCC Case StudyBreathing BuildingsBelum ada peringkat
- HIT 7050 Tr3271eu00tr 0302 MaintenanceDokumen78 halamanHIT 7050 Tr3271eu00tr 0302 MaintenanceJoseMiguelBlancoAlvarez100% (1)
- Tale of ZesteriaDokumen74 halamanTale of ZesteriaWWW.SCRIBD.L0GIN.PWBelum ada peringkat
- Bangalore PlacesDokumen11 halamanBangalore PlacesRamakrishna KunapareddyBelum ada peringkat
- Boq r0 Reactor Gd1 and Gd2 190418Dokumen52 halamanBoq r0 Reactor Gd1 and Gd2 190418UDayBelum ada peringkat
- Curtain Wall Calculation PDFDokumen134 halamanCurtain Wall Calculation PDFAlaaBadwy100% (1)
- Data Tiering in BW4HANA and SAP BW On HANA Roadmap UpdateDokumen14 halamanData Tiering in BW4HANA and SAP BW On HANA Roadmap UpdateNarendra PeddireddyBelum ada peringkat
- Dremel Catalog 2013Dokumen70 halamanDremel Catalog 2013wdowiuueBelum ada peringkat
- FM Local ChandpurDokumen14 halamanFM Local ChandpurShaiful IslamBelum ada peringkat
- Lovecraft - Fungi From Yuggoth and OthersDokumen44 halamanLovecraft - Fungi From Yuggoth and OthersCelephaïs Press / Unspeakable Press (Leng)100% (4)
- PLC To Rio CommunicationDokumen1 halamanPLC To Rio CommunicationSubrat DasBelum ada peringkat
- Bes 1300-102Dokumen0 halamanBes 1300-102Jose GuerreiroBelum ada peringkat
- Rajib Mall Lecture NotesDokumen87 halamanRajib Mall Lecture NotesAnuj NagpalBelum ada peringkat
- Sowmya ResumeDokumen4 halamanSowmya ResumesowmyaBelum ada peringkat
- WBUT Routine 5 TH Sem 2009Dokumen7 halamanWBUT Routine 5 TH Sem 2009siddhartha rayBelum ada peringkat
- Rates 02032015Dokumen13 halamanRates 02032015qoci5koBelum ada peringkat