Selecting The Right Cybercrime-Prevention Solution
Diunggah oleh
Krešimir PuklavecJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Selecting The Right Cybercrime-Prevention Solution
Diunggah oleh
Krešimir PuklavecHak Cipta:
Format Tersedia
IBMSoftware
Thought Leadership White Paper
Selecting the right
cybercrime-prevention solution
Key considerations and best practices for achieving effective, sustainable cybercrime prevention
Contents
1 Introduction
2 Key requirements for effective, sustainable cybercrime prevention
3 Near real-time threat intelligence and visibility
3 Adaptive protection against evolving threats
3 Layered security
4 Early malware detection
5 Limited impact to end users
5 Cost-effective deployment, management and
operations
6 Reliable cybercrime-prevention partner
7 Conclusion
7 For more information
7 About IBM Security solutions
Introduction
Financial institutions, commercial enterprises and government
organizations are all prime targets for cybercrime. Malicious
software, or malware, is the primary attack tool used by
cybercriminals to execute account takeover attacks, steal
credentials and personal information, and initiate fraudulent
transactions. The attack tactics, or crime logic, are constantly
becoming more sophisticated so they can continue to exploit
human and system weaknesses. Fraud-, risk- and IT-security
professionals are looking to establish an effective defense against
these attacks.
IBM Security Trusteer solutions have been helping to protect
users against cybercrime since 2006. Based on our accumulated
experience with hundreds of customers, thousands of fraud cases
and millions of protected endpoints, we have identified the key
principles and best practices for selecting cybercrime-prevention
solutions.
This white paper discusses key considerations and best practices
to help organizations achieve effective and sustainable
cybercrime prevention.
Selecting the right cybercrime-prevention solution
Key requirements for effective,
sustainable cybercrime prevention
When looking at deploying a cybercrime-prevention solution,
organizations must consider multiple requirements. Beyond the
core requirement of providing effective fraud prevention, the
solution must address deployment costs, management
complexity, impact to customers and regulatory compliance.
This white paper will examine some of these requirements
and will compare and contrast various approaches to addressing
them.
Near real-time threat intelligence and visibilityMalware
can bypass virtually all security controls. An effective
cybercrime-prevention solution must be able to assess changes
in the threat landscape. This is essential to maintaining an
effective defense that can protect customers over time.
Rapid protection against evolving threatsBecause all
types of security controls are eventually attacked by malware,
these controls must be able to adapt and stop new attack
vectors. This is a particular concern with hardware-based
solutions, or solutions that rely on statistical approaches to
detect fraud. Often, it is extremely costly and complex for
these types of solutions to respond to new attacks that attempt
to bypass them.
Layered securityUsing multiple layers of security on
endpoints and web applications makes it possible to achieve
powerful and flexible protection. Endpoint security provides
prevention, intelligence and remediation capabilities, and
web-based malware detection provides instant coverage and
lower deployment impact.
Early malware detectionMalware is the root cause of most
fraud. Preventing malware from infecting endpoints and
attacking browsers or web applications can help prevent fraud
from occurring. This requires complete protection of users
online activities, beyond online banking. Early prevention can
also reduce the number of false positives and negatives handled
by fraud and support teams that often result in higher
operational costs and staffing requirements.
Limited impact to end usersTo help ensure that users
adopt fraud-prevention measures, the impact on their
day-to-day workflows must be significantly reduced without
compromising protection. Solutions such as virtual browsers
and hardware tokens sacrifice usability for perceived better
security.
Cost-effective deployment, management and
operationsFraud-prevention solutions should deploy
quickly and require limited intervention from fraud, risk and
support organizations.
Reliable cybercrime-prevention partnerUltimately,
fighting cybercrime is a team effort. Any technology partner
you choose must augment your staff with the expertise and
capabilities to help you sustain an effective defense against
cybercriminals.
IBMSoftware
Near real-time threat intelligence and
visibility
Bottom line: If a financial institution cannot conduct its own
threat research, it should partner with an organization that has
the processes, people and expertise to gather and analyze threat
intelligence and perform continuous risk assessment. Threat
intelligence must be converted into specific actions in a timely
manner to help ensure security controls remain effective.
As noted in the current Federal Financial Institutions
Examination Council (FFIEC) guidance,1 the effectiveness of
security measures used by financial institutions has eroded since
the FFIEC issued its previous guidance in 2005. This realization
has prompted the FFIEC to require financial institutions to
conduct continuous risk assessments and adapt their security
controls to address changes in the threat landscape.
Adaptive protection against evolving
threats
Risk assessment represents a considerable challenge to many
organizations. Fraud and security teams must gather threat
intelligence from various sources, understand the threats that
target their region, industry and specific institution, and
determine if their controls are adequately addressing these
threats. Performing threat analysis requires technology and
expertise that are not available to many financial institutions.
The mirror requirement of threat intelligence is adaptive
protection. Once a new threat or a new attack vector is identified
through the risk-assessment process, a countermeasure must be
rapidly developed and deployed across all protected applications
and users. Financial institutions should assume that even their
latest and greatest security controls will eventually be attacked by
malware, and they must be able to respond immediately when
this happens.
Some cybercrime-prevention solutions attempt to isolate the
user from malware as they access sensitive web applications by
using virtualization technologies contained in hardware devices
or available as software downloads. However, no security control
can eliminate the need to perform risk assessment. Plus, lack of
threat intelligence delays the response to malware attacks until
fraud incidents start to mount. This can be detrimental to a
financial institutions bottom line, brand and customer
retention rate.
Bottom line: Adaptive protection entails a timely, automated
and scalable process to update security controls against emerging
threats. The update process should be transparent to end users
and require limited involvement from the financial institutions
IT and fraud teams.
Layered security
Layered security is a fundamental best practice in cybercrime
prevention. Endpoint controls form the first layer that secures
end user devices against malware infection and attacks on client
applications such as the web browser. Web-based controls create
a second layer that detects high-risk users, devices and sessions.
Combined, these two layers provide a formidable barrier to
cybercrime using different techniques during different parts
of the transaction lifecycle to help prevent and detect
fraudulent activity.
Selecting the right cybercrime-prevention solution
Bottom line: Financial institutions should consider the
solutions overall cybercrime-prevention architecture. Through
phased deployment of multiple protection layers that are
centrally controlled and managed, it is possible to optimize
security without increasing complexity and costs.
Early malware detection
Since the root cause of most fraud losses is malware, preventing
malware from infecting customer machines and tampering with
transactions is critical to helping prevent fraud.
Preventing malware infection requires protection of the users
overall online activity. Users can become infected when visiting
any website, and phishing attacks can happen outside the context
of an online banking session. It is therefore essential to secure all
online activities on the end user machine beyond the specific
online banking site.
Certain approaches to fraud prevention focus on identifying
fraudulent transactions. Fraud detection occurs when a
fraudulent transaction is submitted but before funds are
withdrawn from the account. Due to the statistical nature of
these approaches, a false positive or false negative is likely to
occur. With false positives, the fraud team must review many
legitimate transactions, which is a costly and resource-intensive
process. With false negatives, a direct cost of fraud loss is
virtually guaranteed and subsequent indirect costs, such as brand
damage and customer turnover, soon follow. Cybercriminals also
take many steps to help ensure that fraudulent transactions fly
under the radar by exhibiting as many characteristics of
normal, customer-generated transactions as possible.
Other approaches focus on isolating the online banking session
from malware. History has shown that once a host is infected
with malware, it is possible to attack any security control that
executes on the infected machine. Virtualization-based browser
solutions are no exception, and these, too, are susceptible to
memory injections into their processes executing on the
underlying host.
Conversely, strong endpoint security controls can help prevent
an initial infection, which is the first step in the attack lifecycle.
If malware already resides on the machine, it can be stopped
from attacking the browser and other key services, a vital
component of setting up the attack. A clientless malwaredetection layer can directly identify infected, high-risk users
before an actual fraud attempt occurs, and feed risk data into risk
engines. An adjusted transaction risk score can be used to restrict
access to functions such as adding a payee or transferring money.
In both cases, endpoint-centric security controls can help
directly detect and protect against malware on the endpoint
not just its side effects.
Bottom line: Effectively containing fraud losses favors stopping
malware from ever generating a fraudulent transaction. Look for
a solution that uses malware prevention and detection layers as
cornerstones of security control, as this can help significantly
reduce the number of suspicious transactions that fraud teams
have to deal withand the likelihood of fraud losses.
IBMSoftware
Limited impact to end users
Cybercrime prevention is a balancing act of security,
transparency, usability and interoperability. Server-side solutions
offer transparency but also reduce fraud-prevention capabilities,
as they often lack visibility into endpoint malware, the root cause
of most fraud. Some endpoint solutions require end users to
change the way they access web applications to reduce exposure.
The impact of these solutions on end user acceptance and
adoption of fraud prevention solutions can be substantial.
Other approaches require distribution of hardware devices or
complex software to end users. These deployments incur
shipping, tracking and provisioning costs, cumbersome and
complex update processes, and logistics overhead when devices
have to be replaced if lost or malfunctioning.
Consider the following characteristics of a cybercrimeprevention solution that is simple to deploy and operate:
Typically, end users prefer to continue using their devices and
commercial browsers of choice, as well as to be able to print and
use third-party applications. Furthermore, financial institutions
should aim to provide protection in the background with
limited user interaction.
Bottom line: To encourage end users to adopt fraud-prevention
solutions, financial institutions should choose an option that
limits the impact to their users day-to-day workflows. If users
well-being is ignored in the name of better security, users might
hesitate to employ the proposed security controlswhich can
seriously compromise security efforts.
Cost-effective deployment, management
and operations
While fraud-prevention products should be simple to deploy and
operate, actual implementation costs and complexity levels vary
dramatically among different products.
During initial deployment, some solutions require substantial
effort to establish and sustain a statistical baseline for normal
user activity. Once the baseline is established, fraud teams must
pursue a large number of possible fraud cases that are based
on deviations from the profile, many of which are false positives.
Ultimately, when fraud losses occur or fraudulent transactions
are detected, financial institutions face very limited options
for remediation, as removing malware is a complex and
daunting task.
No changes in user workflow and environmentUsers
prefer not to use awkward devices that can be stolen or
forgotten, or to change the way they use online banking. The
solution should support their browser of choice (Microsoft
Internet Explorer, Mozilla Firefox, Google Chrome and Apple
Safari), their PC platform (Microsoft Windows and Mac) and
third-party applications that support business processes.
No false positivesAccurate fraud detection is a core
requirement of cybercrime prevention. Financial institutions
should not expect a plethora of alerts and warnings to be
investigated. The more visibility the solution has to the threat
landscape, the more accurate it will be in detecting malwaredriven fraud.
Scalable to all channels (retail and business)Financial
institutions need to protect all channels with hundreds to
millions of users. Patching together multiple technologies that
claim security without scalability creates redundancies and
management overhead.
Remediation and malware removalEnd users and financial
institution support teams face the task of restoring endpoints
to a clean state following a malware-driven fraud attempt.
Often, end users have no choice but to reformat their
computer hard drives or restore the operating system to its
factory settings. Both approaches are highly disruptive. A
cybercrime-prevention solution should go beyond detection
and prevention to offer an automated way of removing
malware without the need for complex and disruptive
procedures.
Selecting the right cybercrime-prevention solution
No hardware or software to install at the financial
institutionIT organizations are increasingly adopting
Software-as-a-Service (SaaS) solutions that can reduce the
burden of deploying and maintaining enterprise software
applications. In the case of cybercrime-prevention software,
SaaS allows the solution provider to leverage threat
intelligence across multiple customers and to rapidly update its
protection capabilities, creating a strong network effect.
Bottom line: Cybercrime-prevention solutions should allow for
quick deployments and significantly reduce the rollout and support requirements from financial institutions and end users.
Malware removal and remediation capabilities should enable
infected users to quickly restore their systems to a clean state, so
their productivity is not affected.
Reliable cybercrime-prevention partner
Cybercrime prevention is a process. A financial institutions
trusted cybercrime-prevention partner must be able to
continuously monitor the threat landscape, gather intelligence
and adapt its security controls against emerging threats. The key
ingredient of this process, intelligence, is derived from the
vendors marketplace presence. Simply put, technology is not
enough. The vendor must have the global customer footprint
and operational track record to demonstrate that it can effectively detect changes in the threat landscape, analyze them and
sustain the effectiveness of its security controls over time.
Bottom line: A reliable cybercrime-prevention partner has a
broad global presence, an established customer footprint and a
demonstrated ability to deliver sustainable fraud prevention over
long periods of time.
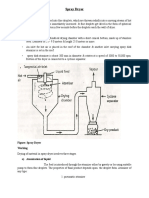
Effective and accurate
Fast time to value
Focus on the root cause
Prevent first, detect next, early
Light integration
Unified platform: any scale
Fraudprevention
architecture
Seamless experience
Transparent to customers
Significantly reduce busy work to staff
Figure 1: Four principles of successful fraud-prevention architecture
Adaptive controls
Near real-time intelligence
Dynamic software vs.
static hardware
IBMSoftware
Conclusion
About IBM Security solutions
When selecting a cybercrime-prevention solution, it is
imperative to realize that, over time, no static security control
can remain effective at stopping malware-driven online banking
fraud. Sustainable cybercrime prevention can be achieved only
by coupling layered adaptive security and near real-time threat
intelligence delivered by a reliable cybercrime-prevention
solution partner. Furthermore, financial institutions must
consider the ability of solutions to leverage security controls
quickly and cost efficiently, without being hindered by poor
usability, limited platform support, long deployment processes
or late detection of fraudulent transactions.
IBM Security offers one of the most advanced and integrated
portfolios of enterprise security products and services.
The portfolio, supported by world-renowned IBM X-Force
research and development, provides security intelligence to
help organizations holistically protect their people,
infrastructures, data and applications, offering solutions for
identity and access management, database security, application
development, risk management, endpoint management, network
security and more. These solutions enable organizations to
effectively manage risk and implement integrated security for
mobile, cloud, social media and other enterprise business
architectures. IBM operates one of the worlds broadest security
research, development and delivery organizations, monitors 15
billion security events per day in more than 130 countries, and
holds more than 3,000 security patents. Additionally, IBM
Global Financing can help you acquire the software capabilities
that your business needs in the most cost-effective and strategic
way possible. Well partner with credit-qualified clients to
customize a financing solution to suit your business and
development goals, enable effective cash management, and
improve your total cost of ownership. Fund your critical IT
investment and propel your business forward with IBMGlobal
Financing. For more information, visit:
Why IBM?
IBM Security solutions are trusted by organizations worldwide
for fraud prevention and identity and access management.
The proven technologies enable organizations to protect their
customers, employees and business-critical resources from the
latest security threats. As new threats emerge, IBM can help
organizations build on their core security infrastructure with
a full portfolio of products, services and business partner
solutions. IBM empowers organizations to reduce their
security vulnerabilities and focus on the success of their
strategic initiatives.
For more information
To learn more about IBM Security Trusteer cybercrimeprevention solutions, please contact your IBM representative or
IBM Business Partner, or visit: ibm.com/security
ibm.com/financing
Copyright IBM Corporation 2014
IBM Corporation
Software Group
Route 100
Somers, NY 10589
Produced in the United States of America
August 2014
IBM, the IBM logo, ibm.com, and X-Force are trademarks of International
Business Machines Corp., registered in many jurisdictions worldwide. Other
product and service names might be trademarks of IBM or other companies.
A current list of IBM trademarks is available on the web at Copyright and
trademark information at ibm.com/legal/copytrade.shtml
Microsoft, Windows, Windows NT, and the Windows logo are trademarks of
Microsoft Corporation in the United States, other countries, or both.
This document is current as of the initial date of publication and may be
changed by IBM at any time. Not all offerings are available in every country
in which IBM operates.
THE INFORMATION IN THIS DOCUMENT IS PROVIDED
AS IS WITHOUT ANY WARRANTY, EXPRESS OR
IMPLIED, INCLUDING WITHOUT ANY WARRANTIES
OF MERCHANTABILITY, FITNESS FOR A PARTICULAR
PURPOSE AND ANY WARRANTY OR CONDITION OF
NON-INFRINGEMENT. IBM products are warranted according to the
terms and conditions of the agreements under which they are provided.
The client is responsible for ensuring compliance with laws and regulations
applicable to it. IBM does not provide legal advice or represent or warrant
that its services or products will ensure that the client is in compliance with
any law or regulation.
Statements regarding IBMs future direction and intent are subject to change
or withdrawal without notice, and represent goals and objectives only.
Statement of Good Security Practices: IT system security involves protecting
systems and information through prevention, detection and response to
improper access from within and outside your enterprise. Improper access
can result in information being altered, destroyed or misappropriated or can
result in damage to or misuse of your systems, including to attack others.
No IT system or product should be considered completely secure and no
single product or security measure can be completely effective in preventing
improper access. IBM systems and products are designed to be part of a
comprehensive security approach, which will necessarily involve additional
operational procedures, and may require other systems, products or services
to be most effective. IBM does not warrant that systems and products are
immune from the malicious or illegal conduct of any party.
Trusteer was acquired by IBMin August of 2013.
1
Federal Financial Institutions Examination Council (FFIEC),
Supplement to Authentication in an Internet Banking Environment,
June 2011. http://www.fdic.gov/news/news/press/2011/pr11111a.pdf
Please Recycle
WGW03042-USEN-01
Anda mungkin juga menyukai
- Four Steps To Protect Your Enterprise From Data LeakageDokumen15 halamanFour Steps To Protect Your Enterprise From Data LeakageKrešimir PuklavecBelum ada peringkat
- Always On SSL White Paper CH PDFDokumen16 halamanAlways On SSL White Paper CH PDFKrešimir PuklavecBelum ada peringkat
- ED BAKER - Blues Riffs For Piano PDFDokumen28 halamanED BAKER - Blues Riffs For Piano PDFBelu Iglesias Barcia100% (3)
- Piano Concerto No. 1 in BB Major, Op. 23-1Dokumen49 halamanPiano Concerto No. 1 in BB Major, Op. 23-1barnaldomortBelum ada peringkat
- 4-43821 030 WP PhishingTactics 0214Dokumen9 halaman4-43821 030 WP PhishingTactics 0214SagarBelum ada peringkat
- Lončarić Biljana - Possibilities of Marketing Evaluation of The Tourist Region of Slavonija and Baranja PDFDokumen32 halamanLončarić Biljana - Possibilities of Marketing Evaluation of The Tourist Region of Slavonija and Baranja PDFKrešimir Puklavec100% (1)
- Barrios, Augustin. El Sueño de La Muñeca, Minueto en Do, Minueto en La, Gavota Al Estilo Antiguo, MabelitaDokumen10 halamanBarrios, Augustin. El Sueño de La Muñeca, Minueto en Do, Minueto en La, Gavota Al Estilo Antiguo, Mabelitasupertzar_st3645Belum ada peringkat
- Ivanović Zoran - TOURISM AND HOSPITALITY MANAGEMENT PDFDokumen150 halamanIvanović Zoran - TOURISM AND HOSPITALITY MANAGEMENT PDFKrešimir PuklavecBelum ada peringkat
- White Paper Firesheep Eng 3Dokumen10 halamanWhite Paper Firesheep Eng 3Krešimir PuklavecBelum ada peringkat
- Strategy Monitoring Security in Cloud EnvironmentsDokumen14 halamanStrategy Monitoring Security in Cloud EnvironmentsKrešimir PuklavecBelum ada peringkat
- Symantec Whitepaper Mobile Shopping PDFDokumen10 halamanSymantec Whitepaper Mobile Shopping PDFKrešimir PuklavecBelum ada peringkat
- DC - DR ABCs Testing FinalDokumen11 halamanDC - DR ABCs Testing FinalneelBelum ada peringkat
- ABCs of Disaster Recovery Testing - HB - FinalDokumen8 halamanABCs of Disaster Recovery Testing - HB - FinalKrešimir PuklavecBelum ada peringkat
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (587)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (73)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (265)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (119)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- PA2 Value and PD2 ValueDokumen4 halamanPA2 Value and PD2 Valueguddu1680Belum ada peringkat
- Financial Services : An OverviewDokumen15 halamanFinancial Services : An OverviewAnirudh JainBelum ada peringkat
- How To Calibrate OscilloscopeDokumen2 halamanHow To Calibrate OscilloscopeninoBelum ada peringkat
- Sight Reduction Tables For Marine Navigation: B, R - D, D. SDokumen12 halamanSight Reduction Tables For Marine Navigation: B, R - D, D. SGeani MihaiBelum ada peringkat
- Sample of Accident Notification & Investigation ProcedureDokumen2 halamanSample of Accident Notification & Investigation Procedurerajendhar100% (1)
- Matrices Class 12 Maths Important Questions Chapter 3 - Learn CBSEDokumen41 halamanMatrices Class 12 Maths Important Questions Chapter 3 - Learn CBSEkhateeb ul islam qadriBelum ada peringkat
- Horizontal Machining Centers: No.40 Spindle TaperDokumen8 halamanHorizontal Machining Centers: No.40 Spindle TaperMax Litvin100% (1)
- Direction: Read The Questions Carefully. Write The Letters of The Correct AnswerDokumen3 halamanDirection: Read The Questions Carefully. Write The Letters of The Correct AnswerRomyross JavierBelum ada peringkat
- Leks Concise Guide To Trademark Law in IndonesiaDokumen16 halamanLeks Concise Guide To Trademark Law in IndonesiaRahmadhini RialiBelum ada peringkat
- Primary 2 (Grade 2) - GEP Practice: Contest Problems With Full SolutionsDokumen24 halamanPrimary 2 (Grade 2) - GEP Practice: Contest Problems With Full Solutionswenxinyu1002100% (1)
- Fictional Narrative: The Case of Alan and His FamilyDokumen4 halamanFictional Narrative: The Case of Alan and His Familydominique babisBelum ada peringkat
- Theory Is An Explanation Given To Explain Certain RealitiesDokumen7 halamanTheory Is An Explanation Given To Explain Certain Realitiestaizya cBelum ada peringkat
- Barry Wylant: Design Thinking and The Experience of InnovationDokumen13 halamanBarry Wylant: Design Thinking and The Experience of InnovationVanesa JuarezBelum ada peringkat
- How To Install Windows XP From Pen Drive Step by Step GuideDokumen3 halamanHow To Install Windows XP From Pen Drive Step by Step GuideJithendra Kumar MBelum ada peringkat
- b2 Open Cloze - Western AustraliaDokumen3 halamanb2 Open Cloze - Western Australiaartur solsonaBelum ada peringkat
- Economics and The Theory of Games - Vega-Redondo PDFDokumen526 halamanEconomics and The Theory of Games - Vega-Redondo PDFJaime Andrés67% (3)
- Symasym BBDokumen37 halamanSymasym BBChandraRizkyBelum ada peringkat
- Stmma-Fd: Zhejiang Castchem New Material Co.,Ltd&Castchem (Hangzhou), IncDokumen2 halamanStmma-Fd: Zhejiang Castchem New Material Co.,Ltd&Castchem (Hangzhou), IncYash RaoBelum ada peringkat
- Rock Type Identification Flow Chart: Sedimentary SedimentaryDokumen8 halamanRock Type Identification Flow Chart: Sedimentary Sedimentarymeletiou stamatiosBelum ada peringkat
- TOS 22402 Winter 19th I SCHEME Paper Model Answer PaperDokumen25 halamanTOS 22402 Winter 19th I SCHEME Paper Model Answer Paperirshadmirza753Belum ada peringkat
- Modesto Mabunga Vs PP (GR 142039)Dokumen3 halamanModesto Mabunga Vs PP (GR 142039)Ericha Joy GonadanBelum ada peringkat
- Dryers in Word FileDokumen5 halamanDryers in Word FileHaroon RahimBelum ada peringkat
- HUMAN RIGHTS, RATIONALITY, AND SENTIMENTALITYDokumen13 halamanHUMAN RIGHTS, RATIONALITY, AND SENTIMENTALITYJohn HunterBelum ada peringkat
- Beyond VaR OfficialDokumen76 halamanBeyond VaR OfficialmaleckicoaBelum ada peringkat
- Security Testing MatDokumen9 halamanSecurity Testing MatLias JassiBelum ada peringkat
- Manual de Instruções Iveco Eurocargo Euro 6Dokumen226 halamanManual de Instruções Iveco Eurocargo Euro 6rsp filmes100% (1)
- Practical Finite Element Simulations With SOLIDWORKS 2022Dokumen465 halamanPractical Finite Element Simulations With SOLIDWORKS 2022knbgamageBelum ada peringkat
- Acc418 2020 2Dokumen3 halamanAcc418 2020 2faithBelum ada peringkat
- Horizontal Vertical MarketDokumen4 halamanHorizontal Vertical MarketVikasBelum ada peringkat
- Detailed Lesson Plan in MAPEH III I. ObjectivesDokumen19 halamanDetailed Lesson Plan in MAPEH III I. ObjectivesJenna FriasBelum ada peringkat