New Text Document
Diunggah oleh
dustboy0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
9 tayangan5 halamansstry
Hak Cipta
© © All Rights Reserved
Format Tersedia
TXT, PDF, TXT atau baca online dari Scribd
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen Inisstry
Hak Cipta:
© All Rights Reserved
Format Tersedia
Unduh sebagai TXT, PDF, TXT atau baca online dari Scribd
0 penilaian0% menganggap dokumen ini bermanfaat (0 suara)
9 tayangan5 halamanNew Text Document
Diunggah oleh
dustboysstry
Hak Cipta:
© All Rights Reserved
Format Tersedia
Unduh sebagai TXT, PDF, TXT atau baca online dari Scribd
Anda di halaman 1dari 5
A New Way to Design and Implementation of Hybrid Crypto System for Security of t
he Information in Public Network
Ravindra Kumar Gupta1, Parvinder Singh2
1Assistant Professor, 2M.Tech Scholar, CSE, SSSIST Sehore (M.P) India
Abstract In this paper, a new hybrid concept is proposed by analyzing the princip
le of the hybrid cryptography based on the combination of symmetric and message
digesting. Moreover, the security and performance of the proposed concept will a
lso estimate. In proposed concept we designed a new symmetric encryption algorit
hm and combine with SHA-1 message digesting function to provide hybrid nature. N
ow the proposed system will try to improve exiting problem. In proposed system s
ymmetric key will use series of logical functions like XOR, Circular Shift (Righ
t, Left), Feastel function [6] and these operations are time efficient operation
as compared to mathematical operation for providing confidentiality and authent
ication. For integrity, proposed system use SHA-1[15] algorithm. Due to this rea
son proposed system is efficient then existing system. The experimental results
based on combination of symmetric and message digesting will approve the effecti
veness of the proposed concept, and the combination of symmetric and message dig
esting will show large variation in key space and provide high-level security. T
he cipher text generated by this method will be approximately double in size as
the plaintext, and will be suitable for practical use in the secure transmission
of confidential information over the Internet. The purpose of hybrid cryptosyst
ems is not to provide perfect or risk-free security. Rather, the purpose of cryp
tography-based security is to protect information resources by making unauthoriz
ed collection of the information or tampering with the information costly than t
he existing potential value that might be gained. Good hybrid cryptography, when
properly implemented and used, makes attempts to violate security cost-prohibit
ive.
Keywords-- Encryption, Decryption, Security, Image, Cryptography.
I. INTRODUCTION
Hybrid cryptography [1, 2, 3, 4] is a technique using multiple ciphers of differ
ent types together, each to its best advantage. A hybrid cryptosystem can be con
structed using any two separate cryptosystems:
? A key has encapsulation scheme which is a public-key or any other type of cryp
tosystem.
? A data has encapsulation scheme which is a symmetric-key cryptosystem.
The hybrid cryptosystem is itself a public-key system, who s public and private ke
ys are the same as in the key encapsulation scheme. In place of public key syste
m we can use digital signature like message digesting function with symmetric ke
y system to make hybrid crypto system. Note that for very long messages the bulk
of the work in encryption/decryption is done by the more efficient symmetric-ke
y scheme, while the inefficient public-key scheme is used only to encrypt/decryp
t a short key value. For example, to encrypt a message addressed to user-1 in a
hybrid technique user-2 does the following [1, 8]:
1. Obtains user-1 public key.
2. Generates a fresh symmetric key
3. Encrypts the message using the symmetric key.
4. Encrypt the symmetric key using user-1 public key. Send both of these encrypt
ions to user-1.
To decrypt this hybrid cipher text, user-1 does the following:
1. User-1 uses her private key to decrypt the symmetric key.
2. User-1 uses this symmetric key to decrypt the message.
But in this paper we have used hash function in place of public key system. As w
e know that hash functions play an important role in digital signature schemes.
A digital signature is a cryptographic technique that produces the electronic eq
uivalent of a manual signature. This means that a digital signature can prohibit
the forging of a message by anybody else but the sender. Moreover the receiver
is given guarantee of the message's authenticity, in the sense that he can subse
quently prove to a third party that the message is authentic even if its origina
tor revokes it. The concept of a digital signature was suggested in 1976 by W. D
iffie and M. Hellman: [15] the sender transforms the information with a secret k
ey, and the receiver can verify the signature by applying the corresponding publ
ic key [7, 9]. Reason behind choosing this model is the security and efficiency.
Most interesting thing in this technique is the combination of two different te
chniques.
International Journal of Emerging Technology and Advanced Engineering
Website: www.ijetae.com (ISSN 2250-2459, ISO 9001:2008 Certified Journal, Volume
3, Issue 8, August 2013)
109
Basically this technique is a method of encryption that combines two or more cry
ptography technique and usually includes a combination of symmetric and message
digesting function to take benefit of the strengths of each type of technique. S
ymmetric encryption has the performance advantage and therefore is the common so
lution for encrypting and decrypting performance-sensitive data, such as an onli
ne data stream. However, symmetric encryption has a downside, i.e. cryptographic
key needs to be known to both the sender and receiver of encrypted data, and th
e exchanging of the key over an insecure channel may cause security risks. On th
e other hand, message digesting provides better security in that the message dig
esting provides digital signature and support to integrity principal. Proposed r
esearch is the designing and implementation of a new Hybrid concept. Proposed te
chnique is a method of encryption that combines two or more cryptography techniq
ue and usually includes a combination of symmetric and message digesting techniq
ue to take benefit of the strengths of each type of cryptography. Basically ther
e are four security principles Confidentiality , Integrity , Authentication , and Non-Rep
diation . In which Symmetric Technique fulfill the concept of Confidentiality, it
also provide the performance advantage and therefore is the common solution for
encrypting and decrypting performance-sensitive data [12, 13, 14]. On the other
hand, message digests technique is fulfilling the authentication as well as inte
grity security principle concept to provide better security in the cryptography.
II. PROPOSED WORK
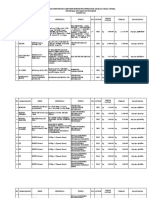
The block diagram of proposed hybrid crypto system is shown in figure 1, plain t
ext encrypted by proposed symmetric encryption algorithm to produce cipher text,
then message digesting function is also apply on plain text by using SHA-160 to
produce message digest of plain text. Now again applying proposed encryption te
chnique on produced message digest text so it will also convert in cipher text.
Now combine both Cipher Values (C1 and C2) into one and send to the receiver. At
receiver end, separate both cipher (C1 and C2) values and apply proposed decryp
tion algorithm one by one on each cipher value. From first cipher value plain te
xt will get and from second cipher value C2 message digest will get. Then apply
message digesting function SHA-1 on plain text which is produced during decrypti
on to produced message digest. Now finally comparing both message digests values
with each other for changes in message digest.
If both message digests are same then plain text securely received otherwise ori
ginal plain text is tempered by the hacker so drop the whole information.
Figure 1:- Block diagram of Proposed Hybrid crypto system
Proposed Architecture: Figure 2 is showing general architecture of the proposed
concept. In this figure user send a request to explorer to send text information
. Server executes this request and response to user in the form of display mail
page of the site. For example, user wants to send personal information in a file
through this mail in public network. First of all user will select confidential
information from file at user end and then send to other end but these confiden
tial information will not go directly to other end it will pass through the desi
gned system. This system uses security features like cryptography, with the help
of cryptography it will encrypt confidential information into cipher text and t
his cipher text will transmit to other end via public network. Basically the pro
posed concept using hybrid technique of cryptography where it s using proposed sym
metric algorithm as a symmetric technique and SHA-1 as message digesting techniq
ue where all the confidential information encrypt via proposed symmetric algorit
hm and authenticity of the information will be checked via SHA-1. After that it
will send cipher data and encrypted key to the other end.
International Journal of Emerging Technology and Advanced Engineering
Website: www.ijetae.com (ISSN 2250-2459, ISO 9001:2008 Certified Journal, Volume
3, Issue 8, August 2013)
110
Figure 2: General Architecture of Proposed Encryption Concept
Figure 3 is showing the receiving end procedure. At receiving end receiver recei
ves cipher message C1 and C2, then receiver decrypt to C1 from proposed decrypti
on algorithm then plain message will again convert into message digest from prop
osed symmetric key. Here proposed model is trying to improve existing problem. I
n this research, proposed symmetric key are using series of logical function lik
e XOR, Circular Shift (Right, Left), feastial function, and these operations are
time efficient operations as compared to mathematical operation.
Figure 3: GenerA New Way to Design and Implementation of Hybrid Crypto System fo
r Security of the Information in Public Network
Ravindra Kumar Gupta1, Parvinder Singh2
1Assistant Professor, 2M.Tech Scholar, CSE, SSSIST Sehore (M.P) India
Abstract In this paper, a new hybrid concept is proposed by analyzing the princip
le of the hybrid cryptography based on the combination of symmetric and message
digesting. Moreover, the security and performance of the proposed concept will a
lso estimate. In proposed concept we designed a new symmetric encryption algorit
hm and combine with SHA-1 message digesting function to provide hybrid nature. N
ow the proposed system will try to improve exiting problem. In proposed system s
ymmetric key will use series of logical functions like XOR, Circular Shift (Righ
t, Left), Feastel function [6] and these operations are time efficient operation
as compared to mathematical operation for providing confidentiality and authent
ication. For integrity, proposed system use SHA-1[15] algorithm. Due to this rea
son proposed system is efficient then existing system. The experimental results
based on combination of symmetric and message digesting will approve the effecti
veness of the proposed concept, and the combination of symmetric and message dig
esting will show large variation in key space and provide high-level security. T
he cipher text generated by this method will be approximately double in size as
the plaintext, and will be suitable for practical use in the secure transmission
of confidential information over the Internet. The purpose of hybrid cryptosyst
ems is not to provide perfect or risk-free security. Rather, the purpose of cryp
tography-based security is to protect information resources by making unauthoriz
ed collection of the information or tampering with the information costly than t
he existing potential value that might be gained. Good hybrid cryptography, when
properly implemented and used, makes attempts to violate security cost-prohibit
ive.
Keywords-- Encryption, Decryption, Security, Image, Cryptography.
I. INTRODUCTION
Hybrid cryptography [1, 2, 3, 4] is a technique using multiple ciphers of differ
ent types together, each to its best advantage. A hybrid cryptosystem can be con
structed using any two separate cryptosystems:
? A key has encapsulation scheme which is a public-key or any other type of cryp
tosystem.
? A data has encapsulation scheme which is a symmetric-key cryptosystem.
The hybrid cryptosystem is itself a public-key system, who s public and private ke
ys are the same as in the key encapsulation scheme. In place of public key syste
m we can use digital signature like message digesting function with symmetric ke
y system to make hybrid crypto system. Note that for very long messages the bulk
of the work in encryption/decryption is done by the more efficient symmetric-ke
y scheme, while the inefficient public-key scheme is used only to encrypt/decryp
t a short key value. For example, to encrypt a message addressed to user-1 in a
hybrid technique user-2 does the following [1, 8]:
1. Obtains user-1 public key.
2. Generates a fresh symmetric key
3. Encrypts the message using the symmetric key.
4. Encrypt the symmetric key using user-1 public key. Send both of these encrypt
ions to user-1.
To decrypt this hybrid cipher text, user-1 does the following:
1. User-1 uses her private key to decrypt the symmetric key.
2. User-1 uses this symmetric key to decrypt the message.
But in this paper we have used hash function in place of public key system. As w
e know that hash functions play an important role in digital signature schemes.
A digital signature is a cryptographic technique that produces the electronic eq
uivalent of a manual signature. This means that a digital signature can prohibit
the forging of a message by anybody else but the sender. Moreover the receiver
is given guarantee of the message's authenticity, in the sense that he can subse
quently prove to a third party that the message is authentic even if its origina
tor revokes it. The concept of a digital signature was suggested in 1976 by W. D
iffie and M. Hellman: [15] the sender transforms the information with a secret k
ey, and the receiver can verify the signature by applying the corresponding publ
ic key [7, 9]. Reason behind choosing this model is the security and efficiency.
Most interesting thing in this technique is the combination of two different te
chniques.
International Journal of Emerging Technology and Advanced Engineering
Website: www.ijetae.com (ISSN 2250-2459, ISO 9001:2008 Certified Journal, Volume
3, Issue 8, August 2013)
109
Basically this technique is a method of encryption that combines two or more cry
ptography technique and usually includes a combination of symmetric and message
digesting function to take benefit of the strengths of each type of technique. S
ymmetric encryption has the performance advantage and therefore is the common so
lution for encrypting and decrypting performance-sensitive data, such as an onli
ne data stream. However, symmetric encryption has a downside, i.e. cryptographic
key needs to be known to both the sender and receiver of encrypted data, and th
e exchanging of the key over an insecure channel may cause security risks. On th
e other hand, message digesting provides better security in that the message dig
esting provides digital signature and support to integrity principal. Proposed r
esearch is the designing and implementation of a new Hybrid concept. Proposed te
chnique is a method of encryption that combines two or more cryptography techniq
ue and usually includes a combination of symmetric and message digesting techniq
ue to take benefit of the strengths of each type of cryptography. Basically ther
e are four security principles Confidentiality , Integrity , Authentication , and Non-Rep
diation . In which Symmetric Technique fulfill the concept of Confidentiality, it
also provide the performance advantage and therefore is the common solution for
encrypting and decrypting performance-sensitive data [12, 13, 14]. On the other
hand, message digests technique is fulfilling the authentication as well as inte
grity security principle concept to provide better security in the cryptography.
II. PROPOSED WORK
The block diagram of proposed hybrid crypto system is shown in figure 1, plain t
ext encrypted by proposed symmetric encryption algorithm to produce cipher text,
then message digesting function is also apply on plain text by using SHA-160 to
produce message digest of plain text. Now again applying proposed encryption te
chnique on produced message digest text so it will also convert in cipher text.
Now combine both Cipher Values (C1 and C2) into one and send to the receiver. At
receiver end, separate both cipher (C1 and C2) values and apply proposed decryp
tion algorithm one by one on each cipher value. From first cipher value plain te
xt will get and from second cipher value C2 message digest will get. Then apply
message digesting function SHA-1 on plain text which is produced during decrypti
on to produced message digest. Now finally comparing both message digests values
with each other for changes in message digest.
If both message digests are same then plain text securely received otherwise ori
ginal plain text is tempered by the hacker so drop the whole information.
Figure 1:- Block diagram of Proposed Hybrid crypto system
Proposed Architecture: Figure 2 is showing general architecture of the proposed
concept. In this figure user send a request to explorer to send text information
. Server executes this request and response to user in the form of display mail
page of the site. For example, user wants to send personal information in a file
through this mail in public network. First of all user will select confidential
information from file at user end and then send to other end but these confiden
tial information will not go directly to other end it will pass through the desi
gned system. This system uses security features like cryptography, with the help
of cryptography it will encrypt confidential information into cipher text and t
his cipher text will transmit to other end via public network. Basically the pro
posed concept using hybrid technique of cryptography where it s using proposed sym
metric algorithm as a symmetric technique and SHA-1 as message digesting techniq
ue where all the confidential information encrypt via proposed symmetric algorit
hm and authenticity of the information will be checked via SHA-1. After that it
will send cipher data and encrypted key to the other end.
International Journal of Emerging Technology and Advanced Engineering
Website: www.ijetae.com (ISSN 2250-2459, ISO 9001:2008 Certified Journal, Volume
3, Issue 8, August 2013)
110
Figure 2: General Architecture of Proposed Encryption Concept
Figure 3 is showing the receiving end procedure. At receiving end receiver recei
ves cipher message C1 and C2, then receiver decrypt to C1 from proposed decrypti
on algorithm then plain message will again convert into message digest from prop
osed symmetric key. Here proposed model is trying to improve existing problem. I
n this research, proposed symmetric key are using series of logical function lik
e XOR, Circular Shift (Right, Left), feastial function, and these operations are
time efficient operations as compared to mathematical operation.
Figure 3: Gener
Anda mungkin juga menyukai
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- IPS PressVest Premium PDFDokumen62 halamanIPS PressVest Premium PDFLucian Catalin CalinBelum ada peringkat
- Uh 60 ManualDokumen241 halamanUh 60 ManualAnonymous ddjwf1dqpBelum ada peringkat
- Astm D 1196 PDFDokumen3 halamanAstm D 1196 PDFSetyawan Chill Gates0% (1)
- P66 M10 CAT B Forms and Docs 04 10Dokumen68 halamanP66 M10 CAT B Forms and Docs 04 10VinayBelum ada peringkat
- Em FlexicokingDokumen8 halamanEm FlexicokingHenry Saenz0% (1)
- Sample Design v3Dokumen129 halamanSample Design v3dustboyBelum ada peringkat
- SSR 5Dokumen3 halamanSSR 5dustboyBelum ada peringkat
- KRACK (Key Reinstallation) Attack 1. Explanation of WPA/WPA2Dokumen8 halamanKRACK (Key Reinstallation) Attack 1. Explanation of WPA/WPA2dustboyBelum ada peringkat
- Wifi Packet FormatDokumen31 halamanWifi Packet FormatdustboyBelum ada peringkat
- ClaimDokumen9 halamanClaimdustboyBelum ada peringkat
- New Text DocumentDokumen10 halamanNew Text DocumentdustboyBelum ada peringkat
- New Text DocumentDokumen19 halamanNew Text DocumentdustboyBelum ada peringkat
- New Text DocumentDokumen11 halamanNew Text DocumentdustboyBelum ada peringkat
- MSC ACFN2 RD4 ClassDokumen25 halamanMSC ACFN2 RD4 Classmengistu jiloBelum ada peringkat
- Anviz T5 RFID ManualDokumen52 halamanAnviz T5 RFID ManualLuis Felipe Olaya SandovalBelum ada peringkat
- XU-CSG Cabinet Minutes of Meeting - April 4Dokumen5 halamanXU-CSG Cabinet Minutes of Meeting - April 4Harold John LaborteBelum ada peringkat
- Assessing The Marks and Spencers Retail ChainDokumen10 halamanAssessing The Marks and Spencers Retail ChainHND Assignment Help100% (1)
- DLI Watchman®: Vibration Screening Tool BenefitsDokumen2 halamanDLI Watchman®: Vibration Screening Tool Benefitssinner86Belum ada peringkat
- ProjectDokumen33 halamanProjectPiyush PatelBelum ada peringkat
- Ice 3101: Modern Control THEORY (3 1 0 4) : State Space AnalysisDokumen15 halamanIce 3101: Modern Control THEORY (3 1 0 4) : State Space AnalysisBipin KrishnaBelum ada peringkat
- Revised Corporation Code - Non Stock Close and Special CorporationsDokumen19 halamanRevised Corporation Code - Non Stock Close and Special CorporationsVenziel PedrosaBelum ada peringkat
- Gmail - ICICI BANK I PROCESS HIRING FOR BACKEND - OPERATION PDFDokumen2 halamanGmail - ICICI BANK I PROCESS HIRING FOR BACKEND - OPERATION PDFDeepankar ChoudhuryBelum ada peringkat
- Physico-Chemical Properties of Nutmeg (Myristica Fragrans Houtt) of North Sulawesi NutmegDokumen9 halamanPhysico-Chemical Properties of Nutmeg (Myristica Fragrans Houtt) of North Sulawesi NutmegZyuha AiniiBelum ada peringkat
- Jurnal Vol. IV No.1 JANUARI 2013 - SupanjiDokumen11 halamanJurnal Vol. IV No.1 JANUARI 2013 - SupanjiIchsan SetiadiBelum ada peringkat
- Rab Sikda Optima 2016Dokumen20 halamanRab Sikda Optima 2016Julius Chatry UniwalyBelum ada peringkat
- Junos ErrorsDokumen2 halamanJunos ErrorsrashidsharafatBelum ada peringkat
- Inspection Report For Apartment Building at 1080 93rd St. in Bay Harbor IslandsDokumen13 halamanInspection Report For Apartment Building at 1080 93rd St. in Bay Harbor IslandsAmanda RojasBelum ada peringkat
- Afzal ResumeDokumen4 halamanAfzal ResumeASHIQ HUSSAINBelum ada peringkat
- Controlled DemolitionDokumen3 halamanControlled DemolitionJim FrancoBelum ada peringkat
- Forces L2 Measuring Forces WSDokumen4 halamanForces L2 Measuring Forces WSAarav KapoorBelum ada peringkat
- Dash 3000/4000 Patient Monitor: Service ManualDokumen292 halamanDash 3000/4000 Patient Monitor: Service ManualYair CarreraBelum ada peringkat
- Key Performance Indicators - KPIsDokumen6 halamanKey Performance Indicators - KPIsRamesh Kumar ManickamBelum ada peringkat
- Maharashtra State Board 9th STD History and Political Science Textbook EngDokumen106 halamanMaharashtra State Board 9th STD History and Political Science Textbook EngSomesh Kamad100% (2)
- ATS2017 ProspectusDokumen13 halamanATS2017 ProspectusGiri WakshanBelum ada peringkat
- Using Visual Rating To Diagnose DementiaDokumen10 halamanUsing Visual Rating To Diagnose DementiaImágenes Rosendo GarcíaBelum ada peringkat
- USDA List of Active Licensees and RegistrantsDokumen972 halamanUSDA List of Active Licensees and Registrantswamu885Belum ada peringkat
- Epistemology and OntologyDokumen6 halamanEpistemology and OntologyPriyankaBelum ada peringkat
- 1st Problem Solving Assignment - Barrels of Apples - M383 Sp22.docx-2Dokumen4 halaman1st Problem Solving Assignment - Barrels of Apples - M383 Sp22.docx-2Kor16Belum ada peringkat