Security VSRX Vmware Install Guide PWP
Diunggah oleh
alireza nematyJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Security VSRX Vmware Install Guide PWP
Diunggah oleh
alireza nematyHak Cipta:
Format Tersedia
vSRX Installation Guide for VMware
Release
15.1X49
Modified: 2016-01-07
Copyright 2016, Juniper Networks, Inc.
Juniper Networks, Inc.
1133 Innovation Way
Sunnyvale, California 94089
USA
408-745-2000
www.juniper.net
Copyright 2016, Juniper Networks, Inc. All rights reserved.
Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United
States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other
trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify,
transfer, or otherwise revise this publication without notice.
vSRX Installation Guide for VMware
15.1X49
Copyright 2016, Juniper Networks, Inc.
All rights reserved.
The information in this document is current as of the date on the title page.
YEAR 2000 NOTICE
Juniper Networks hardware and software products are Year 2000 compliant. Junos OS has no known time-related limitations through the
year 2038. However, the NTP application is known to have some difficulty in the year 2036.
END USER LICENSE AGREEMENT
The Juniper Networks product that is the subject of this technical documentation consists of (or is intended for use with) Juniper Networks
software. Use of such software is subject to the terms and conditions of the End User License Agreement (EULA) posted at
http://www.juniper.net/support/eula.html. By downloading, installing or using such software, you agree to the terms and conditions of
that EULA.
ii Copyright 2016, Juniper Networks, Inc.
Table of Contents
About the Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation and Release Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Documentation Feedback . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
Requesting Technical Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xii
Self-Help Online Tools and Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . xii
Opening a Case with JTAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xii
Chapter 1 Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Understanding vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Understanding vSRX with VMware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
System Requirements for vSRX on VMware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Software Environment Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Hardware Recommendations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Best Practices Recommendations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
vSRX Factory Default Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Interface Naming and Mapping . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Chapter 2 Installing vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Installing vSRX with VMware vSphere Web Client . . . . . . . . . . . . . . . . . . . . . . . . . 21
Adding vSRX Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Adding and Mapping SR-IOV Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Adding VMXNET 3 Interfaces 4 through 7 . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
Adding VMXNET 3 Interfaces 8 through 10 . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
Validating the vSRX .ova File for VMware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Chapter 3 vSRX Licensing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
vSRX Feature Licenses Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
License Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
vSRX Evaluation License . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Product Evaluation License . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Advanced Security Features License . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Bandwidth (Throughput) Licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
vSRX License Keys Components . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
License Management Fields Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
Managing Licenses for vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
vSRX Evaluation License Installation Process . . . . . . . . . . . . . . . . . . . . . . . . . 39
Adding a New License Key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Updating vSRX Licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Deleting a License Key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
License Warning Messages . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
vSRX License Model Numbers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Copyright 2016, Juniper Networks, Inc. iii
vSRX Installation Guide for VMware
Chapter 4 Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 55
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
iv Copyright 2016, Juniper Networks, Inc.
List of Figures
Chapter 2 Installing vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Figure 1: Example of vSRX Deployment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Figure 2: vSRX Edit Settings Page . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Chapter 3 vSRX Licensing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Figure 3: J-Web Licenses Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
Figure 4: License Details in the CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Figure 5: J-Web Licenses Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Figure 6: Add License Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Figure 7: License Details Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Figure 8: License Details Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Figure 9: Delete Licenses Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Figure 10: J-Web Dashboard for License Expiry Warning . . . . . . . . . . . . . . . . . . . . 45
Copyright 2016, Juniper Networks, Inc. v
vSRX Installation Guide for VMware
vi Copyright 2016, Juniper Networks, Inc.
List of Tables
About the Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Table 1: Notice Icons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . x
Table 2: Text and Syntax Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . x
Chapter 1 Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Table 3: Specifications for vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Table 4: Hardware Specifications for the Host Machine . . . . . . . . . . . . . . . . . . . . . 16
Table 5: Factory Default Settings for Security Policies . . . . . . . . . . . . . . . . . . . . . . 18
Table 6: Interface Names for a Standalone vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Table 7: Interface Names for a vSRX Cluster Pair . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Chapter 2 Installing vSRX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Table 8: Disk Formats for Virtual Disk Storage . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Chapter 3 vSRX Licensing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Table 9: vSRX Feature Licenses Type . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Table 10: Summary of License Management Fields . . . . . . . . . . . . . . . . . . . . . . . . 37
Table 11: vSRX Bandwidth Licensing Package Types . . . . . . . . . . . . . . . . . . . . . . . 46
Table 12: Standard (STD) vSRX Bandwidth Licenses . . . . . . . . . . . . . . . . . . . . . . 48
Table 13: vSRX AppSecure and IPS (ASCB / ASEC) Bandwidth Licenses . . . . . . . 49
Table 14: vSRX AppSecure and IPS Subscription Licenses . . . . . . . . . . . . . . . . . . 50
Table 15: vSRX Content Security (CS) Bandwidth Licenses . . . . . . . . . . . . . . . . . . 51
Table 16: vSRX Content Security (CS) Subscription Licenses . . . . . . . . . . . . . . . . 52
Table 17: vSRX Sophos Anti-virus (S-AV) Bandwidth Licenses . . . . . . . . . . . . . . . 53
Table 18: vSRX Enhanced Web Filtering Bandwidth Licenses . . . . . . . . . . . . . . . . 54
Copyright 2016, Juniper Networks, Inc. vii
vSRX Installation Guide for VMware
viii Copyright 2016, Juniper Networks, Inc.
About the Documentation
Documentation and Release Notes on page ix
Documentation Conventions on page ix
Documentation Feedback on page xi
Requesting Technical Support on page xii
Documentation and Release Notes
To obtain the most current version of all Juniper Networks technical documentation,
see the product documentation page on the Juniper Networks website at
http://www.juniper.net/techpubs/.
If the information in the latest release notes differs from the information in the
documentation, follow the product Release Notes.
Juniper Networks Books publishes books by Juniper Networks engineers and subject
matter experts. These books go beyond the technical documentation to explore the
nuances of network architecture, deployment, and administration. The current list can
be viewed at http://www.juniper.net/books.
Documentation Conventions
Table 1 on page x defines notice icons used in this guide.
Copyright 2016, Juniper Networks, Inc. ix
vSRX Installation Guide for VMware
Table 1: Notice Icons
Icon Meaning Description
Informational note Indicates important features or instructions.
Caution Indicates a situation that might result in loss of data or hardware damage.
Warning Alerts you to the risk of personal injury or death.
Laser warning Alerts you to the risk of personal injury from a laser.
Tip Indicates helpful information.
Best practice Alerts you to a recommended use or implementation.
Table 2 on page x defines the text and syntax conventions used in this guide.
Table 2: Text and Syntax Conventions
Convention Description Examples
Bold text like this Represents text that you type. To enter configuration mode, type the
configure command:
user@host> configure
Fixed-width text like this Represents output that appears on the user@host> show chassis alarms
terminal screen.
No alarms currently active
Italic text like this Introduces or emphasizes important A policy term is a named structure
new terms. that defines match conditions and
Identifies guide names. actions.
Junos OS CLI User Guide
Identifies RFC and Internet draft titles.
RFC 1997, BGP Communities Attribute
Italic text like this Represents variables (options for which Configure the machines domain name:
you substitute a value) in commands or
configuration statements. [edit]
root@# set system domain-name
domain-name
x Copyright 2016, Juniper Networks, Inc.
About the Documentation
Table 2: Text and Syntax Conventions (continued)
Convention Description Examples
Text like this Represents names of configuration To configure a stub area, include the
statements, commands, files, and stub statement at the [edit protocols
directories; configuration hierarchy levels; ospf area area-id] hierarchy level.
or labels on routing platform The console port is labeled CONSOLE.
components.
< > (angle brackets) Encloses optional keywords or variables. stub <default-metric metric>;
| (pipe symbol) Indicates a choice between the mutually broadcast | multicast
exclusive keywords or variables on either
side of the symbol. The set of choices is (string1 | string2 | string3)
often enclosed in parentheses for clarity.
# (pound sign) Indicates a comment specified on the rsvp { # Required for dynamic MPLS only
same line as the configuration statement
to which it applies.
[ ] (square brackets) Encloses a variable for which you can community name members [
substitute one or more values. community-ids ]
Indention and braces ( { } ) Identifies a level in the configuration [edit]
hierarchy. routing-options {
static {
route default {
; (semicolon) Identifies a leaf statement at a
nexthop address;
configuration hierarchy level.
retain;
}
}
}
GUI Conventions
Bold text like this Represents graphical user interface (GUI) In the Logical Interfaces box, select
items you click or select. All Interfaces.
To cancel the configuration, click
Cancel.
> (bold right angle bracket) Separates levels in a hierarchy of menu In the configuration editor hierarchy,
selections. select Protocols>Ospf.
Documentation Feedback
We encourage you to provide feedback, comments, and suggestions so that we can
improve the documentation. You can provide feedback by using either of the following
methods:
Online feedback rating systemOn any page at the Juniper Networks Technical
Documentation site at http://www.juniper.net/techpubs/index.html, simply click the
stars to rate the content, and use the pop-up form to provide us with information about
your experience. Alternately, you can use the online feedback form at
http://www.juniper.net/techpubs/feedback/.
Copyright 2016, Juniper Networks, Inc. xi
vSRX Installation Guide for VMware
E-mailSend your comments to techpubs-comments@juniper.net. Include the document
or topic name, URL or page number, and software version (if applicable).
Requesting Technical Support
Technical product support is available through the Juniper Networks Technical Assistance
Center (JTAC). If you are a customer with an active J-Care or Partner Support Service
support contract, or are covered under warranty, and need post-sales technical support,
you can access our tools and resources online or open a case with JTAC.
JTAC policiesFor a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/us/en/local/pdf/resource-guides/7100059-en.pdf.
Product warrantiesFor product warranty information, visit
http://www.juniper.net/support/warranty/.
JTAC hours of operationThe JTAC centers have resources available 24 hours a day,
7 days a week, 365 days a year.
Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online
self-service portal called the Customer Support Center (CSC) that provides you with the
following features:
Find CSC offerings: http://www.juniper.net/customers/support/
Search for known bugs: http://www2.juniper.net/kb/
Find product documentation: http://www.juniper.net/techpubs/
Find solutions and answer questions using our Knowledge Base: http://kb.juniper.net/
Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
Search technical bulletins for relevant hardware and software notifications:
http://kb.juniper.net/InfoCenter/
Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
Open a case online in the CSC Case Management tool: http://www.juniper.net/cm/
To verify service entitlement by product serial number, use our Serial Number Entitlement
(SNE) Tool: https://tools.juniper.net/SerialNumberEntitlementSearch/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
Use the Case Management tool in the CSC at http://www.juniper.net/cm/.
Call 1-888-314-JTAC (1-888-314-5822 toll-free in the USA, Canada, and Mexico).
xii Copyright 2016, Juniper Networks, Inc.
About the Documentation
For international or direct-dial options in countries without toll-free numbers, see
http://www.juniper.net/support/requesting-support.html.
Copyright 2016, Juniper Networks, Inc. xiii
vSRX Installation Guide for VMware
xiv Copyright 2016, Juniper Networks, Inc.
CHAPTER 1
Overview
Understanding vSRX on page 15
Understanding vSRX with VMware on page 15
System Requirements for vSRX on VMware on page 16
vSRX Factory Default Settings on page 17
Interface Naming and Mapping on page 18
Understanding vSRX
vSRX is a virtual security appliance that provides security and networking services at the
perimeter or edge in virtualized private or public cloud environments. vSRX runs as a
virtual machine (VM) on a standard x86 server.
vSRX enables advanced security and routing at the network edge in a multitenant
virtualized environment. vSRX is built on Junos OS and delivers networking and security
features similar to those available on SRX Series Services Gateways for the branch.
Some of the key benefits of vSRX in virtualized private or public cloud multitenant
environments include:
Stateful firewall protection at the tenant edge
Faster deployment of virtual firewalls
Full routing, VPN, and networking capabilities
Centralized and local management
NOTE: vSRX supports SCSI-based or IDE-based disk images.
Understanding vSRX with VMware
VMware vSphere is a virtualization environment for systems supporting the x86
architecture. VMware ESXi is the hypervisor used to create and run virtual machines
(VMs) and virtual appliances on a host machine. The VMware vCenter Server is a service
that manages the resources of multiple ESXi hosts.
Copyright 2016, Juniper Networks, Inc. 15
vSRX Installation Guide for VMware
The VMware vSphere Web Client is used to deploy the vSRX VM.
Related Understanding vSRX on page 15
Documentation
System Requirements for vSRX on VMware
Software Environment Requirements on page 16
Hardware Recommendations on page 16
Best Practices Recommendations on page 17
Software Environment Requirements
Table 3 on page 16 lists the system software requirement specifications for the vSRX
environment.
Table 3: Specifications for vSRX
Component Specification
Hypervisor support VMware ESXi 5.1, 5.5 or 6.0
Memory 4 GB
Disk space 16 GB (IDE or SCSI drives)
vCPUs 2
vNICs Up to 10
Virtual NIC types SR-IOV
VMXNET3
NOTE:
We recommend the Intel X710/XL710 or X520/X540 physical NICs for
SR-IOV support on vSRX.
The Intel DPDK drivers use polling mode for all vNICs, so the NAPI and
interrupt mode features in VMXNET3 are not currently supported.
For SR-IOV limitations, see the Known Behavior section of the vSRX
Release Notes.
Hardware Recommendations
Table 4 on page 16 lists the hardware specifications for the host machine that runs the
vSRX virtual machine (VM).
Table 4: Hardware Specifications for the Host Machine
Component Specification
Host memory size Minimum 4 GB
16 Copyright 2016, Juniper Networks, Inc.
Chapter 1: Overview
Table 4: Hardware Specifications for the Host Machine (continued)
Component Specification
Host processor type x86_64 multicore CPU
NOTE: DPDK requires Intel Virtualization VT-x/VT-d support
in the CPU. See About Intel Virtualization Technology.
Physical NIC Intel X710/XL710 or X520/X540 physical NICs for SR-IOV
support on vSRX
NOTE:
You can check for CPU and other hardware compatibility here:
http://www.vmware.com/resources/compatibility/search.php?deviceCategory=cpu
To determine the Junos OS features supported on vSRX, use the Juniper Networks Feature
Explorer, a Web-based application that helps you to explore and compare Junos OS
feature information to find the right software release and hardware platform for your
network. Find Feature Explorer here:
Feature Explorer: vSRX
Best Practices Recommendations
vSRX deployments can be complex, and there is a great deal of variability in the specifics
of possible deployments. The following recommendations might apply to and improve
performance and function in your particular circumstances:
If the node on which vSRX is running is different from the node to which the Intel PCI
NIC is connected, then packets will have to traverse an additional hop in the QPI link,
and this will reduce overall throughput. Use the extopo command to view information
about relative physical NIC locations. On some servers where this information is not
available, refer to the hardware documentation for the slot-to-NUMA node topology.
Related About Intel Virtualization Technology
Documentation
DPDK Release Notes
vSRX Factory Default Settings
vSRX requires the following basic configuration settings:
Interfaces must be assigned IP addresses.
Interfaces must be bound to zones.
Policies must be configured between zones to permit or deny traffic.
Copyright 2016, Juniper Networks, Inc. 17
vSRX Installation Guide for VMware
NOTE: The management interface, fxp0, requires the following:
VMware uses the VMXNET 3 vNIC and requires promiscuous mode on the
vSwitch.
KVM uses the virtIO vNIC and requires promiscuous mode on the bridge.
Use the ifconfig bridge-name promisc command on the host OS to enable
promiscuous mode on the Linux bridge.
Table 5 on page 18 lists the factory default settings for the vSRX security policies.
Table 5: Factory Default Settings for Security Policies
Source Zone Destination Zone Policy Action
trust untrust permit
trust trust permit
Interface Naming and Mapping
Each network adapter defined for a vSRX is mapped to a specific interface, depending
on whether the vSRX instance is a standalone VM or one of a cluster pair for high
availability. The interface names and mappings in vSRX have changed since the previous
release (called Firefly Perimeter), as shown in the following tables. Note the following
changes:
In standalone mode:
fxp0 is the out-of-band management interface
ge-0/0/0 is the first traffic (revenue) interface
In cluster mode:
fxp0 is the out-of-band management interface
em0 is the cluster control link for both nodes
Any of the traffic interfaces can be specified as the fabric links, such as ge-0/0/0
for fab0 on node 0 and ge-7/0/0 for fab1 on node 1.
Table 6 on page 18 shows the interface names and mappings for a standalone vSRX.
Table 6: Interface Names for a Standalone vSRX
Network
Adapter Interface Name in Junos OS 15.1X49 for vSRX
1 fxp0
2 ge-0/0/0
18 Copyright 2016, Juniper Networks, Inc.
Chapter 1: Overview
Table 6: Interface Names for a Standalone vSRX (continued)
Network
Adapter Interface Name in Junos OS 15.1X49 for vSRX
3 ge-0/0/1
4 ge-0/0/2
5 ge-0/0/3
6 ge-0/0/4
7 ge-0/0/5
8 ge-0/0/6
9 ge-0/0/7
10 ge-0/0/8
Table 7 on page 19 shows the interface names and mappings for a pair of vSRX VMs in
a cluster (node 0 and node 1).
Table 7: Interface Names for a vSRX Cluster Pair
Network
Adapter Interface Name in Junos OS 15.1X49 for vSRX
1 fxp0 (node 0 and 1)
2 em0 (node 0 and 1)
3 ge-0/0/0 (node 0)
ge-7/0/0 (node 1)
4 ge-0/0/1 (node 0)
ge-7/0/1 (node 1)
5 ge-0/0/2 (node 0)
ge-7/0/2 (node 1)
6 ge-0/0/3 (node 0)
ge-7/0/3 (node 1)
7 ge-0/0/4 (node 0)
ge-7/0/4 (node 1)
8 ge-0/0/5 (node 0)
ge-7/0/5 (node 1)
9 ge-0/0/6 (node 0)
ge-7/0/6 (node 1)
Copyright 2016, Juniper Networks, Inc. 19
vSRX Installation Guide for VMware
Table 7: Interface Names for a vSRX Cluster Pair (continued)
Network
Adapter Interface Name in Junos OS 15.1X49 for vSRX
10 ge-0/0/7 (node 0)
ge-7/0/7 (node 1)
20 Copyright 2016, Juniper Networks, Inc.
CHAPTER 2
Installing vSRX
Installing vSRX with VMware vSphere Web Client on page 21
Adding vSRX Interfaces on page 25
Validating the vSRX .ova File for VMware on page 30
Installing vSRX with VMware vSphere Web Client
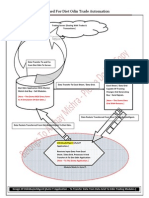
Figure 1 on page 21 shows an example of how vSRX can be deployed to provide security
for applications running on one or more virtual machines. The following procedure
describes how to install vSRX and connect vSRX interfaces to the virtual switches for
the appropriate applications. Only the vSRX virtual switch has a connection to a physical
adapter (the uplink) so that all application traffic flows through the vSRX VM to the
external network.
Figure 1: Example of vSRX Deployment
Copyright 2016, Juniper Networks, Inc. 21
vSRX Installation Guide for VMware
To install vSRX with the VMware vSphere Web Client:
1. Download the vSRX software package for VMware from the Juniper website.
NOTE: Do not change the filename of the downloaded software image
or the installation will fail.
2. Enter the vCenter server hostname or address in your browser
(https://<ipaddress>:9443) to access the vSphere Web Client, and log in to the vCenter
server with your credentials.
3. Select a host or other valid parent for a virtual machine and click Actions > All vCenter
Actions > Deploy OVF Template.
NOTE: The Client Integration Plug-in must be installed before you can
deploy OVF templates (see your VMware documentation).
4. Click Browse to locate the vSRX software package, and then click Next.
5. Click Next in the OVF Template Details window, or click Cancel to select a different
template file.
6. Click Accept in the End User License Agreement window, and then click Next.
7. Change the default vSRX VM name in the Name box and click Next. It is advisable to
keep this name the same as the hostname you intend to give to the VM.
8. In the Datastore window, do not change the default settings for:
Datastore
Available Space
Table 8 on page 22 lists the disk formats available to store the virtual disk. You can
choose one of the three options listed.
NOTE: For detailed information on the disk formats, see Virtual Disk
Provisioning.
Table 8: Disk Formats for Virtual Disk Storage
Disk Format Description
Thick Provision Lazy Zeroed Allocates disk space to the virtual disk without erasing the
previously stored data. The previous data is erased when the VM
is used for the first time.
Thick Provision Eager Erases the previously stored data completely and then allocates
Zeroed the disk space to the virtual disk. Creation of disks in this format is
time consuming.
22 Copyright 2016, Juniper Networks, Inc.
Chapter 2: Installing vSRX
Table 8: Disk Formats for Virtual Disk Storage (continued)
Disk Format Description
Thin Provision Allocates only as much datastore space as the disk needs for its
initial operations. Use this format to save storage space.
9. Select a datastore to store the configuration file and virtual disk files in OVF template,
and then click Next.
10. Select your management network from the list, and then click Next. The management
network is assigned to the first network adapter, which is reserved for the management
interface (fxp0).
11. Click Finish to complete the installation.
12. Open the Edit Settings page of the vSRX VM and select a virtual switch for each
network adapter. Three network adapters are created by default. Network adapter 1
is for the management network (fxp0). To add a fourth adapter, select Network from
New device list at the bottom of the page. To add more adapters, see Adding vSRX
Interfaces on page 25.
In Figure 2 on page 24, network adapter 2 uses the management network for the uplink
to the external network.
Copyright 2016, Juniper Networks, Inc. 23
vSRX Installation Guide for VMware
Figure 2: vSRX Edit Settings Page
13. Enable promiscuous mode for the management virtual switch:
1. Select the host where the vSRX VM is installed, and select Manage > Networking
> Virtual switches.
2. In the list of virtual switches, select vSwitch0 to view the topology diagram for the
management network connected to network adapter 1.
3. Click the Edit icon at the top of the list, select Security, and select Accept next to
Promiscuous mode. Click OK.
Note that vSwitch1 corresponds to network adapter 2, vSwitch2 corresponds to
network adapter 3, and so on.
14. Optionally, enable hardware-assisted virtualization to optimize performance of the
vSRX Routing Engine that runs in a nested VM:
1. Power off the vSRX VM.
2. Right-click on the vSRX VM and select Edit Settings.
24 Copyright 2016, Juniper Networks, Inc.
Chapter 2: Installing vSRX
3. On the Virtual Hardware tab, expand CPU, select Expose hardware-assisted
virtualization to guest OS, and click OK.
On the Manage tab, select Settings > VM Hardware and expand CPU to verify that the
Hardware virtualization option is shown as Enabled.
NOTE: The default vSRX VM login ID is root with no password. By default,
vSRX is assigned a DHCP-based IP address if a DHCP server is available on
the network.
Related Migration, Upgrade, and Downgrade Instructions
Documentation
Adding vSRX Interfaces on page 25
Adding vSRX Interfaces
vSRX for VMware supports up to 10 interfaces. The network adapter for each interface
uses SR-IOV or VMXNET 3 as the adapter type. The first network adapter is for the
management interface (fxp0) and must use VMXNET 3. All additional network adapters
should have the same adapter type. The three network adapters created by default use
VMXNET 3.
The first three network adapters are mapped sequentially to the vSRX interfaces, as
shown in Interface Naming and Mapping on page 18. As you add more network adapters,
the load balancing mechanism will disrupt the mapping sequence.
The following procedures describe how to add more than three network adapters and
maintain sequential mapping to the vSRX interfaces:
Adding and Mapping SR-IOV Interfaces on page 25
Adding VMXNET 3 Interfaces 4 through 7 on page 28
Adding VMXNET 3 Interfaces 8 through 10 on page 28
Adding and Mapping SR-IOV Interfaces
SR-IOV interfaces must be added as PCI devices on VMware. To add an SR-IOV interface
as a PCI Device, you must first select an available Virtual Function (VF) on the device.
Use the following procedure to locate available VFs, add PCI devices, and maintain
sequential mapping:
1. To locate one or more VFs:
a. Use SSH to log in to the ESXi server and enter the following command to view the
VFs for vmnic6 (or another vNIC):
# esxcli network sriovnic vf list -n vmnic6
VF ID Active PCI Address Owner World ID
Copyright 2016, Juniper Networks, Inc. 25
vSRX Installation Guide for VMware
----- ------ ----------- --------------
0 true 005:16.0 982641
1 true 005:16.2 982641
2 true 005:16.4 982641
3 false 005:16.6 -
4 false 005:17.0 -
5 false 005:17.2 -
6 false 005:17.4 -
Choose one or more VF IDs that are not active, such as 3 through 6. Note that a VF
assigned to a VM that is powered off is shown as inactive.
b. Enter the lspci command to view the VF number of the chosen VF IDs. In the
following example, find the entry that ends with [vmnic6], scroll down to the next
entry ending in VF_3, and note the associated VF number 05:10.6. Note that the
next VF_3 entry is for vmnic7.
# lspci
0000:05:00.0 Network controller: Intel Corporation 82599EB 10-Gig ...
[vmnic6]
0000:05:00.1 Network controller: Intel Corporation 82599EB 10-Gig ...
[vmnic7]
0000:05:10.0 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.0_VF_0]
0000:05:10.1 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.1_VF_0]
0000:05:10.2 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.0_VF_1]
0000:05:10.3 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.1_VF_1]
0000:05:10.4 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.0_VF_2]
0000:05:10.5 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.1_VF_2]
0000:05:10.6 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.0_VF_3] ----- VF ID 3 on vmnic6, with VF number
05:10.6.
0000:05:10.7 Network controller: Intel Corporation 82599 Ethernet Controller
Virtual Function [PF_0.5.1_VF_3] ----- VF ID 3 on vmnic7.
2. To add SR-IOV interfaces and maintain sequential mapping:
NOTE: You must use the vSphere Web Client to access the vCenter server,
and DO NOT delete and re-add any network adapters during the following
procedure.
a. Power off the vSRX VM and open the Edit Settings page. By default there are three
network adapters using VMXNET 3. Delete network adapter 2 and 3.
b. Select the VM Options tab, click Advanced in the left frame, and then click Edit
Configuration at the bottom of the page.
c. Change the value of the following items from TRUE to FALSE:
pciBridge5.present
26 Copyright 2016, Juniper Networks, Inc.
Chapter 2: Installing vSRX
pciBridge6.present
pciBridge7.present
Do not change pciBridge0.present or pciBridge4.present.
d. Click OK twice to update the VM settings.
e. Open the Edit Settings page again and add one or more PCI devices on the Virtual
Hardware page, up to a maximum of six PCI devices. For each device, you must
select an entry with an available VF number from Step 1. For example:
05:10.6 | Intel Corporation 82599 Ethernet Controller Virtual Function
f. Click OK and open the Edit Settings page to verify that up to seven network adaptors
are shown on the Virtual Hardware page (one VMXNET 3 network adapter and up
to six SR-IOV interfaces as PCI devices).
To view the SR-IOV interface MAC addresses, select the VM Options tab, click
Advanced in the left frame, and then click Edit Configuration. In the parameters
pciPassthruN.generatedMACAddress, N indicates the PCI device number (0 through
9).
g. Power on the vSRX VM and log in to the VM to verify that VMXNET 3 network
adapter 1 is mapped to fxp0, PCI device 0 is mapped to ge-0/0/0, PCI device 1 is
mapped to ge-0/0/1, and so on.
h. To add up to three more network adapters:
i. Enter the CLI command request system power-off to power off the VM. Do not
use the vSphere Web Client to power off the VM.
ii. Open the Edit Settings page.
iii. Select the VM Options tab, click Advanced in the left frame, and then click Edit
Configuration at the bottom of the page.
iv. Change the value of pciBridge5.present from FALSE to TRUE. If the following
parameters and values are not shown, click Add Row to add each of them.
Parameter Value
pciBridge5.virtualDev pcieRootPort
pciBridge5.functions 8
pciBridge5.pciSlotNumber 22
v. Repeat Step d through g to add up to three more PCI devices (the maximum is
10).
Copyright 2016, Juniper Networks, Inc. 27
vSRX Installation Guide for VMware
NOTE: A vSRX VM with SR-IOV interfaces cannot be cloned. You must deploy
a new vSRX VM and add the SR-IOV interfaces as described here.
Adding VMXNET 3 Interfaces 4 through 7
Use the following procedure to maintain sequential mapping when adding VMXNET 3
network adapters 4 through 7:
NOTE: During this procedure DO NOT delete and re-add any network
adapters.
1. Power off the vSRX VM and open the Edit Settings page.
2. Using the vSphere Web Client, select the VM Options tab, click Advanced in the left
frame, and then click Edit Configuration at the bottom of the page. (Using the vSphere
desktop client, select General under Advanced in the left frame, and click Configuration
Parameters at the bottom of the page.)
3. Change the value of the following items from TRUE to FALSE:
pciBridge5.present
pciBridge6.present
pciBridge7.present
Do not change pciBridge0.present or pciBridge4.present.
4. Click OK twice to update the VM settings.
5. Open the Edit Settings page again and add up to four network adapters (the 4th
through the 7th network adapters) on the Virtual Hardware page. For each network
adapter, select Network from New device list at the bottom of the page, expand New
Network, and select VMXNET 3 as the adapter type.
6. Click OK and open the Edit Settings page to verify that up to seven network adaptors
are shown on the Virtual Hardware page.
7. Power on the vSRX VM and log in to the VM to verify that network adapter 1 is mapped
to fxp0, network adapter 2 is mapped to ge-0/0/0, and so on. Use the show interfaces
terse CLI command to verify that the fxp0 and ge-0/0/n interfaces are up.
Adding VMXNET 3 Interfaces 8 through 10
Use the following procedure to maintain sequential mapping when adding VMXNET 3
network adapters 8 through 10:
NOTE: During this procedure DO NOT delete and re-add any network
adapters.
28 Copyright 2016, Juniper Networks, Inc.
Chapter 2: Installing vSRX
1. Enter the CLI command request system power-off to power off the VM. Do not use
the vSphere Web Client to power off the VM.
2. Open the Edit Settings page.
3. Using the vSphere Web Client, select the VM Options tab, click Advanced in the left
frame, and then click Edit Configuration at the bottom of the page. (Using the vSphere
desktop client, select General under Advanced in the left frame, and click Configuration
Parameters at the bottom of the page.)
4. Change the value of pciBridge5.present from FALSE to TRUE. If the following
parameters and values are not shown, click Add Row to add each of them.
Parameter Value
pciBridge5.virtualDev pcieRootPort
pciBridge5.functions 8
pciBridge5.pciSlotNumber 22
5. Click OK twice to update the VM settings.
6. Open the Edit Settings page again and up to three network adapters (the 8th, 9th,
and 10th network adaptors) on the Virtual Hardware page. For each network adapter,
select Network from New device list at the bottom of the page, expand New Network,
and select VMXNET 3 as the adapter type.
7. Click OK and open the Edit Settings page to verify that up to ten network adaptors
are shown on the Virtual Hardware page.
8. Power on the vSRX VM and log in to the VM to verify that network adapter 1 is mapped
fxp0, network adapter 2 is mapped to ge-0/0/0, and so on. Use the show interfaces
terse CLI command to verify that the fxp0 and ge-0/0/n interfaces are up.
Copyright 2016, Juniper Networks, Inc. 29
vSRX Installation Guide for VMware
Validating the vSRX .ova File for VMware
The vSRX open virtual application (OVA) image is securely signed. You can validate the
OVA image, if necessary, but you can install or upgrade vSRX without validating the OVA
image.
Before you validate the OVA image, ensure that the Linux/UNIX PC or Windows PC on
which you are performing the validation has the following utilities available: tar, openssl,
and ovftool. You can download the VMware Open Virtualization Format (OVF) tool from
https://my.vmware.com/web/vmware/details?
productId=353&downloadGroup=OVFTOOL351.
To validate the OVA image on a Linux machine:
1. Download the vSRX OVA image and the Juniper Networks Root certificate file
(JuniperRootRSACA.pem) from the vSRX software download page.
NOTE: You need to download the Juniper Networks Root certificate file
only once; you can use the same file to validate OVA images for future
releases of vSRX.
2. (Optional) If you downloaded the OVA image and the certificate file to a PC running
Windows, copy the two files to a temporary directory on a PC running Linux or UNIX.
You can also copy the OVA image and the certificate file to a temporary directory
(/var/tmp or /tmp) on a vSRX node.
Ensure that the OVA image file and the Juniper Networks Root certificate file are not
modified during the validation procedure. You can do this by providing write access
to these files only to the user performing the validation procedure. This is especially
important if you use an accessible temporary directory, such as /tmp or /var/tmp,
because such directories can be accessed by several users. Take precautions to ensure
that the files are not modified by other users during the validation procedure.
3. Navigate to the directory containing the OVA image.
4. Unpack the OVA image by running the following command:
tar xf ova-filename
where ova-filename is the filename of the previously downloaded OVA image.
5. Verify that the unpacked OVA image contains a certificate chain file (certchain.pem)
and a signature file (vsrx.cert).
6. Validate the signature in the unpacked OVF file (extension .ovf) by running the following
command:
ovftool ovf-filename
where ovf-filename is the filename of the unpacked OVF file contained within the
previously downloaded OVA image.
30 Copyright 2016, Juniper Networks, Inc.
Chapter 2: Installing vSRX
7. After the unpacked OVF file is validated, validate the signing certificate with the Juniper
Networks Root CA file by running the following command:
openssl verify -CAfile JuniperRootRSACA.pem -untrusted Certificate-Chain-File
Signature-file
where JuniperRootRSACA.pem is the Juniper Networks Root CA file,
Certificate-Chain-File is the filename of the unpacked certificate chain file (extension
.pem) and Signature-file is the filename of the unpacked signature file (extension
.cert).
If the validation is successful, a message indicating that the validation is successful
is displayed. A sample of the validation procedure is as follows:
-bash-4.1$ ls
JuniperRootCA.pem junos-vsrx-12.1X47-D15.4-domestic.ova
-bash-4.1$ mkdir tmp
-bash-4.1$ cd tmp
-bash-4.1$ tar xf ../junos-vsrx-12.1X47-D15.4-domestic.ova
-bash-4.1$ ls
certchain.pem junos-vsrx-12.1X47-D15.4-domestic.cert
junos-vsrx-12.1X47-D15.4-domestic-disk1.vmdk junos-vsrx-12.1X47-D15.4-domestic.mf
junos-vsrx-12.1X47-D15.4-domestic.ovf
-bash-4.1$ /usr/lib/vmware-ovftool/ovftool junos-vsrx-12.1X47-D15.4-domestic.ovf
OVF version: 1.0
VirtualApp: false
Name: vSRX
Version: JUNOS 12.1
Vendor: Juniper Networks Inc.
Product URL:
http://www.juniper.net/us/en/products-services/software/security/vsrxseries/
Vendor URL: http://www.juniper.net/
Download Size: 227.29 MB
Deployment Sizes:
Flat disks: 2.00 GB
Sparse disks: 265.25 MB
Networks:
Name: VM Network
Description: The VM Network network
Virtual Machines:
Name: Juniper Virtual SRX
Operating System: freebsdguest
Virtual Hardware:
Families: vmx-07
Number of CPUs: 2
Cores per socket: 1
Memory: 2.00 GB
Disks:
Index: 0
Instance ID: 5
Capacity: 2.00 GB
Copyright 2016, Juniper Networks, Inc. 31
vSRX Installation Guide for VMware
Disk Types: IDE
NICs:
Adapter Type: E1000
Connection: VM Network
Adapter Type: E1000
Connection: VM Network
Deployment Options:
Id: 2GvRAM
Label: 2G vRAM
Description:
2G Memory
-bash-4.1$ openssl verify -CAfile ../JuniperRootCA.pem -untrusted certchain.pem
junos-vsrx-12.1X47-D15.4-domestic.cert
junos-vsrx-12.1X47-D15.4-domestic.cert: OK
8. (Optional) If the validation is not successful, perform the following tasks:
a. Determine if the contents of the OVA image have been modified. If the contents
have been modified, download the OVA image from the vSRX downloads page.
b. Determine whether the Juniper Networks Root CA file is corrupted or modified. If
it was corrupted or modified, download the certificate file from the vSRX downloads
page.
c. Retry the preceding validation steps using one or both new files.
Related Installing vSRX with VMware vSphere Web Client on page 21
Documentation
32 Copyright 2016, Juniper Networks, Inc.
CHAPTER 3
vSRX Licensing
vSRX Feature Licenses Overview on page 33
Managing Licenses for vSRX on page 39
vSRX License Model Numbers on page 45
vSRX Feature Licenses Overview
Some Junos OS software features require a license to activate the feature.
To enable a licensed feature, you need to purchase, install, manage, and verify a license
key that corresponds to each licensed feature. To conform to software feature licensing
requirements, you must purchase one license per feature per instance. The presence of
the appropriate software unlocking key on your virtual instance allows you to configure
and use the licensed feature.
Licenses are usually ordered when the software application is purchased, and this
information is bound to a customer ID. If you did not order the licenses when you purchased
your software application, contact your account team or Juniper Networks Customer
Care for assistance.
Licenses can be procured from the Juniper Networks License Management System (LMS).
NOTE: The license for advanced security features available on the physical
SRX Series device cannot be used with vSRX deployments.
NOTE: If you are performing a software downgrade with licenses installed,
you will see an error message in the CLI when you try to configure the licensed
features or run the command show system license status.
We recommend deleting existing licenses before performing a software
downgrade.
Copyright 2016, Juniper Networks, Inc. 33
vSRX Installation Guide for VMware
License Types
Juniper Networks provides evaluation licenses for both basic firewall features and
advanced security features for a limited period.
If you want to use vSRX to provide basic firewall features, you can use core (basic)
licenses. However, to use some of the more advanced security features, such as
AppSecure, IDP, and UTM, you might need to purchase advanced features licenses.
vSRX Evaluation License
To speed deployment of licensed features, Junos OS software for vSRX implements an
honor-based licensing structure and provides you with a 60-day product evaluation
license or a 30-day advanced security features license, both of which allow you to use
a licensed feature for the specified period without having to install a license key.
Table 9 on page 34 lists vSRX evaluation license types.
Table 9: vSRX Feature Licenses Type
License Model
License Package Type Period Number
Trial license Product evaluation- Basic 60 days -
(temporary for
evaluation only)
Product evaluation- Advanced 30 days -
features
Product Evaluation License
This is a 60-day evaluation license for vSRX. This product unlocking license is required
for basic functions, such as networking, routing and, basic security features.
vSRX software image includes a 60-day trial license. When you download and install
the vSRX image, you are entitled to use the trial license for 60 days.
Within 30 days of the license expiration date, a license expiration warning appears when
you log in to the vSRX instance. After the product evaluation license expires, you will not
be able to use the product; it will be disabled because as flow configuration options will
not work. Only management interfaces and CLI configurations are preserved.
Advanced Security Features License
The advanced security features license is a 30-day trial license for vSRX that is required
for advanced security features such as UTM, IDP, and AppSecure.
You can download the trial license for advanced security features from one of the
following locations:
Software Download Page
vSRX 60-Day Free Trial License Page
34 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Installation of the trial license is similar to the regular license installation. For details, see
Managing Licenses for vSRX on page 39.
NOTE: The 30-day trial license period begins on the day you enable enhanced
security features after you install the evaluation licenses.
To continue using vSRX features after an optional 30-day period, you must
purchase and install the license; otherwise, the features are disabled.
If the license for advanced security features expires while the evaluation
license (product unlocking license) is still valid, only the advanced security
features that require license are disabled.
NOTE: Direct upgrade is not supported for upgrading from earlier Junos OS
releases for vSRX to Junos OS Release 15.1X49-D15 for vSRX. When you
download and install the vSRX image for Junos OS Release 15.1X49-D15, you
are entitled use the trial license for 60 days.
Bandwidth (Throughput) Licenses
Bandwidth (throughput) licenses allow you to use a single instance of the software for
up to the maximum throughput specified in the license entitlement. Throughput licenses
can be combined on a single instance of the software so that the maximum throughput
for that instance is the aggregate of all the throughput licenses assigned to that instance.
A throughput license cannot be split across multiple instances. Throughput licenses are
identified in the license entitlement in Mbps, or Gbps.
For more information on Bandwidth licenses, see vSRX License Model Numbers on
page 45.
A throughput license can be perpetual or subscription-based.
Perpetual license: A perpetual license allows you to use the licensed software
indefinitely.
Subscription-based license: A subscription-based license is an annual license that
allows you to use the licensed software feature for a limited duration. Subscriptions
might involve periodic downloads of content (such as for IDP threat signature files).
At the end of the license period, you need to renew the license to continue using it.
All license subscriptions are renewable.
Only subscription-based licenses, which are active for a set period, require renewal.
Perpetually licensed features or capacities never expire and therefore never need to
be renewed.
For more information, see vSRX subscriptions.
For details on installing and managing licenses, see Managing Licenses for vSRX on
page 39.
Copyright 2016, Juniper Networks, Inc. 35
vSRX Installation Guide for VMware
vSRX License Keys Components
A license key consists of two parts:
License IDAlphanumeric string that uniquely identifies the license key. When a license
is generated, it is given a license ID.
License dataBlock of binary data that defines and stores all license key objects.
For example, in the following typical license key, the string E413XXXX57 is the license ID,
and the trailing block of data is the license data:
E413XXXX57 aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff aaaaaa
aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff
The license data conveys the customer ID and the software serial number (Juniper
Networks support reference number) to the vSRX instance.
License Management Fields Summary
The Licenses page displays a summary of licensed features that are configured on the
vSRX instance and a list of licenses that are installed on the vSRX instance.
To view the license details, select Maintain>Licenses in the J-Web user interface. The
Licenses window appears as shown in Figure 3 on page 36.
Figure 3: J-Web Licenses Window
36 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
You can also view the details of a license in the CLI using the show system license
command. Figure 4 on page 37 shows details of an evaluation license in the CLI.
Figure 4: License Details in the CLI
The information on the license management page is summarized in Table 10 on page 37.
Table 10: Summary of License Management Fields
Field Name Definition
Feature Summary
Feature Name of the licensed feature:
FeaturesSoftware feature licenses.
All featuresAll-inclusive licenses.
Licenses Used Number of licenses currently being used on the vSRX instance. Usage
is determined by the configuration. If a feature license exists and that
feature is configured, the license is considered used.
Copyright 2016, Juniper Networks, Inc. 37
vSRX Installation Guide for VMware
Table 10: Summary of License Management Fields (continued)
Field Name Definition
Licenses Installed Number of licenses installed on the vSRX instance for the particular
feature.
Licenses Needed Number of licenses required for legal use of the feature. Usage is
determined by the configuration on the vSRX instance: If a feature is
configured and the license for that feature is not installed, a single
license is needed.
Licenses expires on Date the license expires.
Installed Licenses
ID Unique alphanumeric ID of the license.
State ValidThe installed license key is valid.
InvalidThe installed license key is not valid.
Version Numeric version number of the license key.
Group If the license defines a group license, this field displays the group
definition.
If the license requires a group license, this field displays the required
group definition.
NOTE: Because group licenses are currently unsupported, this field
is always blank.
Enabled Features Name of the feature that is enabled with the particular license.
Expiration Date the license expires.
Software serial number The serial number is a unique 14-digit number that Juniper Networks
uses to identify your particular software installation. You can find the
software serial number in the Software Serial Number Certificate
attached to the e-mail that was sent when you ordered your Juniper
Networks software.
Customer ID ID that identifies the registered user.
Related vSRX License Model Numbers on page 45
Documentation
Managing Licenses for vSRX on page 39
38 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Managing Licenses for vSRX
This section includes following topics:
vSRX Evaluation License Installation Process on page 39
Adding a New License Key on page 39
Updating vSRX Licenses on page 42
Deleting a License Key on page 42
License Warning Messages on page 44
vSRX Evaluation License Installation Process
Juniper Networks provides a 60-day evaluation license for vSRX standard security
features. In addition, you can download and install 30-day evaluation license for vSRX
advanced (Layer 7) security features.
Within 30 days of the license expiration date, a license expiration warning appears when
you log in to the device. After license expiry, vSRX no longer functions effectively. Only
management interfaces and the CLI configuration are preserved.
vSRX software image includes a 60-day trail license. When you download and install
the vSRX image, you are entitled use the trial license for 60 days.
If you want to install evaluation license for advanced security features (30-day evaluation
license), you can download the evaluation license from one of the following options:
Software Download Page
vSRX 60-Day Free Trial License Page
Installation of the evaluation license is similar to the regular license installation using the
CLI. See Adding a New License Key on page 39
NOTE: The 30-day evaluation license period begins on the day you enable
enhanced security features after installing evaluation licenses.
To continue using vSRX features after an optional 30-day evaluation period,
you must purchase and install the license. Otherwise, the features are
disabled.
Adding a New License Key
You can add a license key from a file or URL, from a terminal, or from the J-Web user
interface.
Copyright 2016, Juniper Networks, Inc. 39
vSRX Installation Guide for VMware
To install a license using the J-Web interface:
1. Select Maintain>Licenses on the J-Web user interface. The Licenses window is
displayed as shown in Figure 5 on page 40.
Figure 5: J-Web Licenses Window
2. Under Installed Licenses, click Add. The Add License dialog is displayed as shown in
Figure 6 on page 40.
Figure 6: Add License Window
3. Do one of the following, using a blank line to separate multiple license keys:
Enter the full URL to the destination file containing the license key in the License
File URL box.
Paste the license key text, in plain-text format, in the License Key Text box.
4. Click OK to add the license key. The License Details window is displayed as shown in
Figure 7 on page 41.
40 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Figure 7: License Details Window
5. The license key is installed and activated on vSRX.
To install a license from the CLI:
1. From operational mode, add a license key using one of the following steps:
Enter the full URL to the destination file containing the license key.
user@host> request system license add <license-key>
Paste the license key text in plain-text format.
user@host>request system license add terminal
2. When prompted, enter the license key, separating multiple license keys with a blank
line. If the license key you enter is invalid, an error is generated when you press CTRL+D
to exit license entry mode.
[Type ^D at a new line to end input,
enter blank line between each license key]
E413012057 aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff aaaaaa
aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff
E413012057: successfully added
add license complete (no errors)
3. View the details of the license by entering the show system license command.
root@host> show system license
License usage: Licenses Licenses Licenses Expiry
Feature name used installed needed
wf key websense ewf 1 0 1 invalid
Licenses installed: none
Copyright 2016, Juniper Networks, Inc. 41
vSRX Installation Guide for VMware
NOTE: You can save the license key to a file and upload this file to vSRX
file system through FTP or Secure Copy (SCP), and then use the request
system license add file-name command to install the license.
4. The license key is installed and activated on vSRX.
Updating vSRX Licenses
You can update the vSRX licenses using the following two methods:
Automatic license update using the CLI
Manual license update using the CLI
As a prerequisite, you must install at least one valid license key on your vSRX for required
features. License auto-update is performed based on the valid software serial number
and customer ID embedded in the license key.
To enable automatic license updates from the CLI:
1. Contact your account team or Juniper Networks Customer Care to extend the validity
period of existing license keys and obtain the URL for a valid update server.
2. Once you have successfully extended your license key and received the update server
URL, configure the auto-update parameter.
user@host> set system license autoupdate url https://ae1.juniper.net/
3. Configure renew options (if required). The following sample shows configuring before
expiration as 30 days and renew interval as 6 hours.
user@host> set system license renew before-expiration 30
user@host> set system license renew interval 6
The configuration allows vSRX to contact the license server 30 days before the current
license expires and sends an automatic update request every 6 hours.
To manually update the license from the CLI:
1. Update the license keys manually.
user@host> request system license update url <url.of.license.server>
NOTE: The request system license update command will always use the
default Juniper license server https://ae1.juniper.net.
2. Check the status of the license by entering the show system license command.
This command sends a license update request to the license server immediately.
Deleting a License Key
You can delete a license key using the CLI or the J-Web user interface.
42 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
To delete a license using the J-Web interface:
1. Select Maintain>Licenses .
2. Select the check box of the license or licenses you want to delete, as shown in
Figure 8 on page 43.
Figure 8: License Details Window
3. Click Delete.
4. Click OK to confirm your deletion, as shown in Figure 9 on page 43
Figure 9: Delete Licenses Window
The license key you deleted will be removed.
To delete a license key using the CLI:
1. From operational mode, for each license, enter the following command and specify
the license ID. You can delete only one license at a time.
user@host> request system license delete <license-key-identifier>
Or you can use the following command to delete all installed licenses at a time.
Copyright 2016, Juniper Networks, Inc. 43
vSRX Installation Guide for VMware
user@host> request system license delete all
2. Type yes when you are prompted to confirm the deletion.
Delete license JUNOS606279 ? [yes,no] (no)
The license key you deleted will be removed.
License Warning Messages
You must purchase a new license or renew your existing subscription-based license to
have a seamless transition from the old license to the new one.
The following conditions occur when a license expires on vSRX:
Evaluation license for the core expires: Packet forwarding on vSRX is disabled. However,
you can manage vSRX through the fxp0 management interface, and the CLI
configuration is preserved.
Subscription-based licenses for advanced security features expire but
subscription-based licenses for core services are active: A 30-day grace period begins,
allowing the user to continue using advanced security features. After the grace period,
advanced security features are disabled. Basic features are always available for using.
After subscription-based licenses for core services are expired, a warning message is
displayed to notify the user, but basic features will be preserved.
Subscription-based license for core features expires but subscription-based license
for advanced security features is active: A warning message is displayed to notify the
user. However, you can continue to use all features on vSRX. Advanced security features
are disabled when the subscription-based license for advanced security features
expires, but basic features are still preserved.
To use features that require a license, you must install and configure a license key. After
the license expires, warning messages are displayed in the system log and on the J-Web
dashboard.
When a license expires, the System Alarms section of the J-Web dashboard displays a
message stating that the license has expires as shown in Figure 10 on page 45.
44 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Figure 10: J-Web Dashboard for License Expiry Warning
When license expires, the following message is displayed when you login:
Virtual Appliance License is invalid
Related vSRX Feature Licenses Overview on page 33
Documentation
vSRX License Model Numbers on page 45
vSRX License Model Numbers
The licenses used by all Juniper Networks devices are based on SKUs, which represent
lists of features. Each license includes a list of features that the license enables along
with information about those features.
For information about purchasing software licenses, contact your Juniper Networks sales
representative at http://www.juniper.net/in/en/contact-us/.
vSRX licenses are based on application packages and processing capacity.
Bandwidth (throughput) licenses allow you to use a single instance of the software for
up to the maximum throughput specified in the license entitlement. Throughput licenses
can be combined on a single instance of the software so that the maximum throughput
for that instance is the aggregate of all the throughput licenses assigned to that instance.
A throughput license cannot be split across multiple instances. Throughput licenses are
identified in the license entitlement in Mbps, or Gbps.
Copyright 2016, Juniper Networks, Inc. 45
vSRX Installation Guide for VMware
vSRX provides bandwidth in the following capacities (throughput per instance): 10 Mbps,
100 Mbps, 1 Gbps, 2 Gbps, and 4 Gbps. Each of these bandwidth tiers are offered with
four different packages along with bandwidth based ala-carte advanced Layer 7 security
services SKUs.
Table 11 on page 46 describes the features available with the various license packages.
Table 11: vSRX Bandwidth Licensing Package Types
License
Type Description Duration
STD Includes the following features: Both perpetual and subscription
license options are available.
Core security firewall, ALG, screens,
user firewall
IPSec VPN (site-to-site VPN)
See Table 12 on page 48 for STD
NAT bandwidth SKUs available for vSRX.
CoS
Multicast services IP Multicast (PIM,
IGMP)
Routing services BGP, OSPF, DHCP,
J-Flow, IPv4, and IPv6
High availability
Foundation Static routing,
management (J-Web, CLI, and
NetConf), on-box logging, diagnostics
Software platform KVM, Openstack,
ESXi 6.0, Contrail
ASCB / Includes all STD features and the Subscription licenses only.
ASEC following additional AppSecure features:
AppID
See Table 13 on page 49 for
AppFW
bandwidth SKUs available for vSRX
AppQoS with AppSecure and IPS features.
AppTrack
CS Includes all STD and ASEC features with Subscription licenses only.
the addition of UTM capabilities:
Antispam
See Table 15 on page 51 for CS
Antivirus
bandwidth SKUs available for vSRX.
Content filtering
Web filtering
46 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Table 11: vSRX Bandwidth Licensing Package Types (continued)
License
Type Description Duration
Advanced Ala-carte Layer 7 security services licenses Subscription licenses only.
Security including:
Services See Table 14 on page 50 for
(Ala carte: Sophos antivirus AppSecure and IPS SKUs available
ASEC, S-AV, Websense enhanced Web filtering for vSRX.
W-EWF)
AppSecure See Table 17 on page 53 for Sophos
IPS antivirus bandwidth SKUs available
for vSRX.
Table 18 on page 54 lists the Web
filtering subscription licenses
available for vSRX.
NOTE: License stacking is allowed. So, for example, to license 20 Mbps of
throughput for the standard (STD) feature set perpetually, use two
VSRX-10M-STD licenses.
Table 12 on page 48 lists the standard bandwidth licenses available for vSRX.
Copyright 2016, Juniper Networks, Inc. 47
vSRX Installation Guide for VMware
Table 12: Standard (STD) vSRX Bandwidth Licenses
STD Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-STD
standard package (1 year, 3 years, and
perpetual) VSRX-10M-STD-1
VSRX-10M-STD-1-R
VSRX-10M-STD-3
VSRX-10M-STD-3-R
VSRX-100M-STD
VSRX-100M-STD-1
VSRX-100M-STD-1-R
VSRX-100M-STD-3
VSRX-100M-STD-3-R
VSRX-1G-STD
VSRX-1G-STD-1
VSRX-1G-STD-1-R
VSRX-1G-STD-3
VSRX-1G-STD-3-R
VSRX-2G-STD
VSRX-2G-STD-1
VSRX-2G-STD-1-R
VSRX-2G-STD-3
VSRX-2G-STD-3-R
VSRX-4G-STD
VSRX-4G-STD-1
VSRX-4G-STD-1-R
VSRX-4G-STD-3
VSRX-4G-STD-3-R
48 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Table 13 on page 49 lists the bandwidth licenses available for vSRX with AppSecure and
IPS features.
Table 13: vSRX AppSecure and IPS (ASCB / ASEC) Bandwidth Licenses
ASCB / ASEC Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-ASECB-1
AppSecure package includes all features
in the STD package with IPS and VSRX-10M-ASECB-1-R
AppSecure (1 year and 3 years
subscription) VSRX-10M-ASECB-3
VSRX-10M-ASECB-3-R
VSRX-100M-ASCB-1
VSRX-100M-ASCB-1-R
VSRX-100M-ASCB-3
VSRX-100M-ASCB-3-R
VSRX-1G-ASECB-1
VSRX-1G-ASECB-1-R
VSRX-1G-ASECB-3
VSRX-1G-ASECB-3-R
VSRX-2G-ASECB-1
VSRX-2G-ASECB-1-R
VSRX-2G-ASECB-3
VSRX-2G-ASECB-3-R
VSRX-4G-ASECB-1
VSRX-4G-ASECB-1-R
VSRX-4G-ASECB-3
VSRX-4G-ASECB-3-R
Table 14 on page 50 lists the subscription licenses available for vSRX with AppSecure
and IPS features.
Copyright 2016, Juniper Networks, Inc. 49
vSRX Installation Guide for VMware
Table 14: vSRX AppSecure and IPS Subscription Licenses
ASEC Licenses Model Number
10M/100M/1G/2G/4G VSRX-10M-ASEC-1
subscriptionvSRX AppSecure package
includes IPS and AppSecure (1 year and VSRX-10M-ASEC-1-R
3 years subscription)
VSRX-10M-ASEC-3
VSRX-10M-ASEC-3-R
VSRX-100M-ASEC-1
VSRX-100M-ASEC-1-R
VSRX-100M-ASEC-3
VSRX-100M-ASEC-3-R
VSRX-1G-ASEC-1
VSRX-1G-ASEC-1-R
VSRX-1G-ASEC-3
VSRX-1G-ASEC-3-R
VSRX-2G-ASEC-1
VSRX-2G-ASEC-1-R
VSRX-2G-ASEC-3
VSRX-2G-ASEC-3-R
VSRX-4G-ASEC-1
VSRX-4G-ASEC-1-R
VSRX-4G-ASEC-3
VSRX-4G-ASEC-3-R
Table 15 on page 51 lists the Content Security(CS) bandwidth licenses available for vSRX.
50 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Table 15: vSRX Content Security (CS) Bandwidth Licenses
CS Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-CS-B-1
CS package includes all features in STD,
IPS, and Appsecure, enhanced Web VSRX-10M-CS-B-1-R
filtering, Sophos antivirus, antispam,
contentfiltering, (1 year and 3 years). VSRX-10M-CS-B-3
VSRX-10M-CS-B-3-R
VSRX-100M-CS-B-1
VSRX-100M-CS-B-1-R
VSRX-100M-CS-B-3
VSRX-100M-CS-B-3-R
VSRX-1G-CS-B-1
VSRX-1G-CS-B-1-R
VSRX-1G-CS-B-3
VSRX-1G-CS-B-3-R
VSRX-2G-CS-B-1
VSRX-2G-CS-B-1-R
VSRX-2G-CS-B-3
VSRX-2G-CS-B-3-R
VSRX-4G-CS-B-1
VSRX-4G-CS-B-1-R
VSRX-4G-CS-B-3
VSRX-4G-CS-B-3-R
Table 16 on page 52 lists the CS subscription licenses available for vSRX.
Copyright 2016, Juniper Networks, Inc. 51
vSRX Installation Guide for VMware
Table 16: vSRX Content Security (CS) Subscription Licenses
CS Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-CS-1
CS package includes enhanced Web
filtering, Sophos antivirus, antispam, VSRX-10M-CS-1-R
Appsecure and IPS (1 year and 3 years)
VSRX-10M-CS-3
VSRX-10M-CS-3-R
VSRX-100M-CS-1
VSRX-100M-CS-1-R
VSRX-100M-CS-3
VSRX-100M-CS-3-R
VSRX-1G-CS-1
VSRX-1G-CS-1-R
VSRX-1G-CS-3
VSRX-1G-CS-3-R
VSRX-2G-CS-1
VSRX-2G-CS-1-R
VSRX-2G-CS-3
VSRX-2G-CS-3-R
VSRX-4G-CS-1
VSRX-4G-CS-1-R
VSRX-4G-CS-3
VSRX-4G-CS-3-R
Table 17 on page 53 lists the Sophos antivirus (S-AV) bandwidth licenses available for
vSRX.
52 Copyright 2016, Juniper Networks, Inc.
Chapter 3: vSRX Licensing
Table 17: vSRX Sophos Anti-virus (S-AV) Bandwidth Licenses
S-AV Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-S-AV-1
S-AV license (1 year and 3 years).
VSRX-10M-S-AV-1-R
VSRX-10M-S-AV-3
VSRX-10M-S-AV-3-R
VSRX-100M-S-AV-1
VSRX-100M-S-AV-1-R
VSRX-100M-S-AV-3
VSRX-100M-S-AV-3-R
VSRX-1G-S-AV-1
VSRX-1G-S-AV-1-R
VSRX-1G-S-AV-3
VSRX-1G-S-AV-3-R
VSRX-2G-S-AV-1
VSRX-2G-S-AV-1-R
VSRX-2G-S-AV-3
VSRX-2G-S-AV-3-R
VSRX-4G-S-AV-1
VSRX-4G-S-AV-1-R
VSRX-4G-S-AV-3
VSRX-4G-S-AV-3-R
Table 18 on page 54 lists the enhanced Web filtering (E-EWF) subscription licenses
available for vSRX.
Copyright 2016, Juniper Networks, Inc. 53
vSRX Installation Guide for VMware
Table 18: vSRX Enhanced Web Filtering Bandwidth Licenses
W-EWF Licenses Model Number
10M/100M/1G/2G/4G throughputvSRX VSRX-10M-W-EWF-1
W-EWF license (1 year and 3 years).
VSRX-10M-W-EWF-1-R
VSRX-10M-W-EWF-3
VSRX-10M-W-EWF-3-R
VSRX-100M-WEWF-1
VSRX-100M-WEWF-1-R
VSRX-100M-WEWF-3
VSRX-100M-WEWF-3-R
VSRX-1G-W-EWF-1
VSRX-1G-W-EWF-1-R
VSRX-1G-W-EWF-3
VSRX-1G-W-EWF-3-R
VSRX-2G-W-EWF-1
VSRX-2G-W-EWF-1-R
VSRX-2G-W-EWF-3
VSRX-2G-W-EWF-3-R
VSRX-4G-W-EWF-1
VSRX-4G-W-EWF-1-R
VSRX-4G-W-EWF-3
VSRX-4G-W-EWF-3-R
Related vSRX Feature Licenses Overview on page 33
Documentation
Managing Licenses for vSRX on page 39
54 Copyright 2016, Juniper Networks, Inc.
CHAPTER 4
Index
Index on page 57
Copyright 2016, Juniper Networks, Inc. 55
vSRX Installation Guide for VMware
56 Copyright 2016, Juniper Networks, Inc.
M
manuals
comments on....................................................................xi
P
Index parentheses, in syntax descriptions..................................xi
R
RAM
Symbols
maximum...........................................................................16
#, comments in configuration statements.....................xi
( ), in syntax descriptions.......................................................xi
S
.ova
Specifications
validating..........................................................................30
vSRX....................................................................................16
< >, in syntax descriptions.....................................................xi
support, technical See technical support
[ ], in configuration statements...........................................xi
syntax conventions...................................................................x
{ }, in configuration statements..........................................xi
| (pipe), in syntax descriptions............................................xi
T
technical support
B contacting JTAC...............................................................xii
braces, in configuration statements..................................xi
brackets
V
angle, in syntax descriptions........................................xi
vCPUs
square, in configuration statements.........................xi
maximum...........................................................................16
vNICs
C maximum...........................................................................16
comments, in configuration statements.........................xi
vSRX
conventions
hardware requirements................................................16
text and syntax...................................................................x
RAM......................................................................................16
curly braces, in configuration statements.......................xi
specifications...................................................................16
customer support....................................................................xii
understanding..................................................................15
contacting JTAC...............................................................xii
validating image.............................................................30
vCPUs..................................................................................16
D
vNICs....................................................................................16
disk formats...............................................................................22
documentation
comments on....................................................................xi
F
factory default settings..........................................................17
font conventions........................................................................x
H
host OS........................................................................................16
L
licenses
displaying (J-Web).........................................................37
Copyright 2016, Juniper Networks, Inc. 57
vSRX Installation Guide for VMware
58 Copyright 2016, Juniper Networks, Inc.
Anda mungkin juga menyukai
- MSSQL Server Sys Admin GuideDokumen256 halamanMSSQL Server Sys Admin Guideapi-3761813Belum ada peringkat
- VMware Admin GuideDokumen368 halamanVMware Admin GuideDenya_bit100% (1)
- Asg TmonDokumen276 halamanAsg Tmonaya gandaBelum ada peringkat
- ResumeDokumen3 halamanResumeRafi ShaikBelum ada peringkat
- SAE ProjectDokumen200 halamanSAE ProjectKhai Huynh100% (3)
- Microsoft Virtualization: Master Microsoft Server, Desktop, Application, and Presentation VirtualizationDari EverandMicrosoft Virtualization: Master Microsoft Server, Desktop, Application, and Presentation VirtualizationPenilaian: 4 dari 5 bintang4/5 (2)
- Microsoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferenceDari EverandMicrosoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferencePenilaian: 4.5 dari 5 bintang4.5/5 (3)
- HP Opencall Ss7 Platform Operations Guide: For Release 3.2 On Hp-Ux Pa-RiscDokumen430 halamanHP Opencall Ss7 Platform Operations Guide: For Release 3.2 On Hp-Ux Pa-Riscopenid_AgrpmDdZBelum ada peringkat
- V14.2 Vmware Installation GuideDokumen62 halamanV14.2 Vmware Installation Guideimanuel antonius sohirinBelum ada peringkat
- Subject: Appointment Letter For The Post of Business Development ExecutiveDokumen3 halamanSubject: Appointment Letter For The Post of Business Development ExecutiveMeet ShahBelum ada peringkat
- AccessugDokumen136 halamanAccessugrajitkarmakarBelum ada peringkat
- Integrating Siebel Web Services Aug2006Dokumen146 halamanIntegrating Siebel Web Services Aug2006api-3732129100% (1)
- Security VSRX Vmware Guide PWPDokumen82 halamanSecurity VSRX Vmware Guide PWPDede RizkiBelum ada peringkat
- Getting StartedDokumen56 halamanGetting Startediqbal apriansyahBelum ada peringkat
- Getting Started With VMXDokumen56 halamanGetting Started With VMXRio ArdianBelum ada peringkat
- Sanpoint Control Quickstart Installation and Configuration GuideDokumen176 halamanSanpoint Control Quickstart Installation and Configuration GuideMonu SaneBelum ada peringkat
- Check Point Security Gateway R70 Installation and Configuration Guide For Crossbeam X-Series PlatformsDokumen62 halamanCheck Point Security Gateway R70 Installation and Configuration Guide For Crossbeam X-Series PlatformsDinesh PalBelum ada peringkat
- Getting Started VMXKVMDokumen96 halamanGetting Started VMXKVMmudassaruetBelum ada peringkat
- Getting Started Guide For Branch SRX SeriesDokumen158 halamanGetting Started Guide For Branch SRX Seriessatya28Belum ada peringkat
- NS VPXGettingStarted GuideDokumen141 halamanNS VPXGettingStarted Guidechandru831000Belum ada peringkat
- DellDokumen80 halamanDellspada1975Belum ada peringkat
- Veritas Netbackup - Adminguide - AdvancedclientDokumen268 halamanVeritas Netbackup - Adminguide - AdvancedclientNarupon100% (4)
- Book Software SRX Series Volume 1 PDFDokumen2.394 halamanBook Software SRX Series Volume 1 PDFSatyapriya PanigrahiBelum ada peringkat
- Kofax Vrs - 4.5 - User's - GuideDokumen126 halamanKofax Vrs - 4.5 - User's - GuideDrago LovricBelum ada peringkat
- Kofax Installation GuideDokumen258 halamanKofax Installation GuideCharles ObodoBelum ada peringkat
- Licensing End User GuideDokumen162 halamanLicensing End User Guidewu wuBelum ada peringkat
- Docu81533 - NetWorker 9.1 Licensing GuideDokumen86 halamanDocu81533 - NetWorker 9.1 Licensing GuideZuhaib ShafiBelum ada peringkat
- NetWorker Installation Guide Version 8.2Dokumen148 halamanNetWorker Installation Guide Version 8.2eduardo arturo zaldivarBelum ada peringkat
- NetbackupDokumen268 halamanNetbackupBrijith VBBelum ada peringkat
- Sky Atp Admin Guide PDFDokumen126 halamanSky Atp Admin Guide PDFschadrac1Belum ada peringkat
- TRA InstallationDokumen44 halamanTRA Installationsreeg2005690Belum ada peringkat
- VERITAS NetBackup 5.1 Advanced Client System Administrators Guide For UNIX and WindowsDokumen287 halamanVERITAS NetBackup 5.1 Advanced Client System Administrators Guide For UNIX and WindowsgabjonesBelum ada peringkat
- LacpDokumen360 halamanLacptorBelum ada peringkat
- Xir2 Bip Install Unix enDokumen284 halamanXir2 Bip Install Unix enkishore9257Belum ada peringkat
- Juniper SRX Security Chassis ClusterDokumen426 halamanJuniper SRX Security Chassis ClusterNOC AlbideyNetBelum ada peringkat
- Hpsu 83000 InstallDokumen252 halamanHpsu 83000 Installcool_sasank9191Belum ada peringkat
- Vxworks: Command-Line Tools User'S GuideDokumen94 halamanVxworks: Command-Line Tools User'S GuidecesarBelum ada peringkat
- Suite Talk Web Services Platform GuideDokumen341 halamanSuite Talk Web Services Platform GuideSohailBelum ada peringkat
- Quick Start Guide: Esx Server 3.0 and Virtualcenter 2.0Dokumen78 halamanQuick Start Guide: Esx Server 3.0 and Virtualcenter 2.0Sinem KocBelum ada peringkat
- 6-5 WebSphere MQ Adapter Install and Users GuideDokumen218 halaman6-5 WebSphere MQ Adapter Install and Users GuideAnubha AgarwalBelum ada peringkat
- BusinessObjects Enterprise™ XI Release 2Dokumen312 halamanBusinessObjects Enterprise™ XI Release 2Hayfa Ben SlimaBelum ada peringkat
- 4.5 MS SQLDokumen224 halaman4.5 MS SQLysfgdkglBelum ada peringkat
- Security Application IdentificationDokumen342 halamanSecurity Application IdentificationrazielBelum ada peringkat
- WSP Install GuideDokumen176 halamanWSP Install GuideStefano EsmBelum ada peringkat
- Junos® OS Getting Started Guide For Routing DevicesDokumen398 halamanJunos® OS Getting Started Guide For Routing DevicesPriscilla Felicia HarmanusBelum ada peringkat
- VSX5000-InstlGuide N450000590r001Dokumen230 halamanVSX5000-InstlGuide N450000590r001Georgi VodenitcharovBelum ada peringkat
- Ug962 v7 Vc709 XT Connectivity TRD UgDokumen98 halamanUg962 v7 Vc709 XT Connectivity TRD Ugteo2005Belum ada peringkat
- PowerVC V1.3.2Dokumen308 halamanPowerVC V1.3.2ecorradiBelum ada peringkat
- BlueSocket VWLAN Admin GuideDokumen227 halamanBlueSocket VWLAN Admin GuidedragelecBelum ada peringkat
- RV AdministrationDokumen320 halamanRV AdministrationhwangjaesunBelum ada peringkat
- Bcefp NutshellDokumen120 halamanBcefp NutshellVSBelum ada peringkat
- JCE-Developer - Guide-4 6 0Dokumen108 halamanJCE-Developer - Guide-4 6 0thefunkystuff0% (1)
- NexentaStor 4 Installation GuideDokumen47 halamanNexentaStor 4 Installation GuiderokkhanBelum ada peringkat
- Dell Marvell Fibre Channel Adapter 26xx User GuideDokumen160 halamanDell Marvell Fibre Channel Adapter 26xx User GuideecorradiBelum ada peringkat
- Tib RV AdministrationDokumen457 halamanTib RV AdministrationtesterBelum ada peringkat
- IBM Proventia IPS and Check Point VPN-1 VSX NGX R65Dokumen64 halamanIBM Proventia IPS and Check Point VPN-1 VSX NGX R65tpressleyBelum ada peringkat
- DSLS 1 PDFDokumen153 halamanDSLS 1 PDFBruno CarboniBelum ada peringkat
- DSLS PDFDokumen153 halamanDSLS PDFBruno CarboniBelum ada peringkat
- DSLSDokumen153 halamanDSLSjcdh_99Belum ada peringkat
- Suite Talk Web Services Platform GuideDokumen193 halamanSuite Talk Web Services Platform Guidetranhieu5959Belum ada peringkat
- XRC UserDokumen236 halamanXRC Userwenyuchen96Belum ada peringkat
- Tib Be InstallationDokumen83 halamanTib Be InstallationBushra KanwalBelum ada peringkat
- Ns Vcs MXDokumen92 halamanNs Vcs MXSalman SaluBelum ada peringkat
- Palo Alto Networks: VM-Series Deployment GuideDokumen210 halamanPalo Alto Networks: VM-Series Deployment GuideNguyen Ho LongBelum ada peringkat
- Stacks and QueuesDokumen21 halamanStacks and QueuesDhivya NBelum ada peringkat
- SMA 2373 CAT II Marking SchemeDokumen3 halamanSMA 2373 CAT II Marking SchemeRotich VincentBelum ada peringkat
- Microsoft Dynamics Ax 2012 Retail PerformanceDokumen67 halamanMicrosoft Dynamics Ax 2012 Retail PerformanceDao Van HangBelum ada peringkat
- DsfssafaDokumen4 halamanDsfssafaGasBelum ada peringkat
- Data Structure Practical - MCA Idol Shree Ram CollegeDokumen65 halamanData Structure Practical - MCA Idol Shree Ram CollegeUnknownBelum ada peringkat
- BLDC Motor ControlDokumen8 halamanBLDC Motor ControlSithija AlwisBelum ada peringkat
- WSGI Werkzeug and The Challenges of Building A Python Web FrameworkDokumen22 halamanWSGI Werkzeug and The Challenges of Building A Python Web FrameworkIgor Guerrero FonsecaBelum ada peringkat
- 11.3 Eigenvalues and Eigenvectors of A Tridiagonal MatrixDokumen7 halaman11.3 Eigenvalues and Eigenvectors of A Tridiagonal MatrixVinay GuptaBelum ada peringkat
- An Approximate Analysis Procedure For Piled Raft FoundationsDokumen21 halamanAn Approximate Analysis Procedure For Piled Raft FoundationsNicky198100% (1)
- CS 253 Binary Search Trees ChapterDokumen28 halamanCS 253 Binary Search Trees ChapterMuhammed Abdel HamidBelum ada peringkat
- Designing Combinational Logic Circuits: Part2 Alternative Logic Forms: Ratio Logic Pass-Transistor Dynamic LogicDokumen52 halamanDesigning Combinational Logic Circuits: Part2 Alternative Logic Forms: Ratio Logic Pass-Transistor Dynamic LogicPrasanna VenkatesanBelum ada peringkat
- Platform1 Server and N-MINI 2 Configuration Guide V1.01Dokumen47 halamanPlatform1 Server and N-MINI 2 Configuration Guide V1.01sirengeniusBelum ada peringkat
- ResultsDokumen5 halamanResultsCHEATINGBASTARDBelum ada peringkat
- Using Final windows in Smartforms to display total page counts by ship-to-partyDokumen6 halamanUsing Final windows in Smartforms to display total page counts by ship-to-partypanirbanonline3426Belum ada peringkat
- Linear regression method to find slope and interceptDokumen3 halamanLinear regression method to find slope and interceptAMIRA EZZATIE BINTI MOHD HATTA -Belum ada peringkat
- Purchasing Doc Release With Multiple CurrenciesDokumen8 halamanPurchasing Doc Release With Multiple CurrenciesBalanathan VirupasanBelum ada peringkat
- Viewshed Calculation AlgoDokumen8 halamanViewshed Calculation AlgoYasirBelum ada peringkat
- NetWorker Module For Microsoft Applications 2.3 Application GuideDokumen278 halamanNetWorker Module For Microsoft Applications 2.3 Application GuidevinoopnvBelum ada peringkat
- Documentation - Diet Odin Demo ApplicationDokumen4 halamanDocumentation - Diet Odin Demo Applicationashucool23Belum ada peringkat
- MC InterfacingDokumen24 halamanMC InterfacingSuhas HattiBelum ada peringkat
- PDFDokumen19 halamanPDFपोटैटो शर्मा0% (1)
- Idm CrackDokumen34 halamanIdm CracktilalmansoorBelum ada peringkat
- A Review On Plant Recognition and Classification Techniques Using Leaf ImagesDokumen6 halamanA Review On Plant Recognition and Classification Techniques Using Leaf ImagesseventhsensegroupBelum ada peringkat
- Project Report: Optical Character Recognition Using Artificial Neural NetworkDokumen9 halamanProject Report: Optical Character Recognition Using Artificial Neural NetworkRichard JamesBelum ada peringkat
- Fundamentals of Programming: Course OutlineDokumen32 halamanFundamentals of Programming: Course OutlineAngelina Febriany SimarmataBelum ada peringkat
- Assignment 4 - ArraysDokumen3 halamanAssignment 4 - ArraysSarthak SBelum ada peringkat