Ijater 05 02
Diunggah oleh
Deiva SigamaniJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Ijater 05 02
Diunggah oleh
Deiva SigamaniHak Cipta:
Format Tersedia
International Journal of Advanced Technology & Engineering Research (IJATER)
SECURITY IN E-BANKING VIA CARD LESS BIOMETRIC
ATMS
S.T. Bhosale
Research Scholar
V.P. Institute of Management Studies and Research, Sangli
Dr. B.S.Sawant
Director
K. B. P. Institute of Management Studies and Research, Satara
Enormous risks to the computer systems that they
Abstract support, such as telecommunications, power distribution,
national defense, law enforcement, financial services,
Banks in India have started introducing biometric automatic government services and emergency service follow the
teller machines (ATMs) as it seems to be an effective way of benefits of this interconnectivity. Security is associated with
preventing card usage and is also a channel to expand a risk, threat and vulnerability. [1] [7]
banks reach to the rural and illiterate masses. Union Bank of
India installed a first such Kisan ATM at Siyagangai branch II. Objective
Tamil Nadu. Dena Bank has launched the Bio-metric ATMs 1. To study scope of biometric authentication techniques in
in Gujarat. Andhra Bank has launched mobile biometric ATMs.
access ATMs, one each for the Twin Cities of Hyderabad and 2. To generate module which helps for simple operation of
Sceunderabad. Corporation Bank has also introduced ATMs with full proof secure authentication via
talking biometric ATMs. These ATMs talks to the farmer networking?
in their local languages. [2] [9] 3. Providing suggestions with advantages and limitations of
Present study deals with new innovative model for proposed model.
biometric ATMs which replaces card system by biometric
technology for operating ATMs. Proposed model provides
high security in authentication which also protects service III. Review of Literature
user from unauthorized access. In this proposed model user
required to authenticate himself with biometric identification
(Thumb/ Fingerprint/Iris etc.), Personal Identity Number International references:
(PIN) and selection of bank branch from displayed list if Customers must be convinced that the technologies provide
necessary. This proposed model is designed for the rural more benefit than the card-and-PIN system, which works well,
farmers, semi-literate peoples. This model reduces said John Hall, spokesman for the American Bankers
complexity with authentication as authentication is always Association. The cards also serve functions beyond the ATMs,
with you with high security. It also saves time, cost, and as debit cards and as advertising for the banks. "Getting that
efforts compared with card based ATMs and also saves wallet space is important," said Bill Spence, a biometric expert
environmental pollution problem of excess number of plastic with Campbell, Calif.-based Recognition Systems Inc.
cards. However, companies that make automated teller machines
have found budding markets for the fingerprint technology in
South America, where citizens already are accustomed to the
Keywords: Biometric ATMs, authentication, PIN, use of fingerprints for general identification, such as ID cards
security, plastic cards. they carry. Diebold Inc. of North Canton, Ohio, has supplied
fingerprint-capable ATMs to a bank in Chile that is using them
in a pilot project. Last year Dayton, Ohio-based NCR Corp.
I. Introduction installed 400 of them in Colombia. BanCafe, Colombia's fifth-
largest bank, bought the ATMs at the end of 2002 for added
Need of Security security for coffee growers and to get them to open accounts.
Computers have taken over virtually all of our major record The growers wouldn't need to carry ATM cards, which can be
keeping functions. Recently, personal computers have made it a lure for thieves. "Biometrics is certainly the most secure
cost-effective to automate many office functions. form of authentication," said Avivah Litan, an analyst with
Organizations have begun to share data across wide area. This Gartner Inc., a Stamford, Conn.-based technology analysis
has prompted efforts to convert principally LAN-based firm. "It's the hardest to imitate and duplicate." [4]
protocols into WAN-friendly protocols. Frequently the
protocol of choice has been TCP/IP, interconnects with each What is Identification Authentication?
other via private networks as well as through public networks Identification is the process by which the identity of a user is
companies using TCP/IP. Computerization has many established, authentication is the process by which a service
advantages with automated systems, however introduces new confirms the claim of a user to use a specific identity by the
risks. use of credentials. Biometrics are vey reliable for
ISSN No: 2250-3536 Volume 2, Issue 4, July 2012 9
International Journal of Advanced Technology & Engineering Research (IJATER)
authentication. The difference is between a system that looks
at a hand geometry and says this is Doctor Hunk
(identification) versus a mans who says I, Doctor Hunk,
present my hand to prove who I am? . And the system
confirms this hand matches Doctor Hunks template
(authentication). Biometric authentication is feasible today. [8]
[11] [12]
What is biometric authentication?
Biometrics is biological authentications, based on some
physical characteristics of the human body. The list of
biometric authentication technologies is still growing. There
are two categories of biometric identifiers include
physiological and behavioral characteristics. Physiological Fig. 1 Working of biometric authentication
characteristics are related to the shape of the body, and include
but are not limited to: fingerprint, face recognition, DNA, palm Source: http://en.wikipedia.org/wiki/File:Biometric_system_diagram.png
print, hand geometry, iris recognition (which has largely
replaced retina), and odor /scent. Behavioral characteristics V. Technical Specification:
are related to the behavior of a person, including but not
limited to: typing rhythm, gait, digital signature and voice.
More traditional means of access control include token-based During every authentication process there is slight variation in
identification systems, such as drivers license or passport, and matching biometric characteristic. This is because the physical
knowledge-based identification systems, such as password or characteristics of the user may change for a number of reasons.
Personal Identification Number (PIN). For instance, suppose the fingerprint of the user is captured
Now there are devices to recognize the following and used for authentication every time. The sample taken
biometrics: fingerprints, hand geometry (shape and size of every authentication may not be the same, because of finger
fingers), retina and iris (part of the eyes), voice, handwriting, can be dirty, can have cuts, other marks or the fingers position
blood vessels in the finger, and face. Authentication with on the reader can be different and so on. Therefore, an exact
biometric has advantages that is it cannot be lost, stolen, match of the sample need not be required. An approximate
forgotten lent or forged and is always available, always at match can be acceptable. Therefore using registration process,
hand, so to speak. If we success in combining this multiple samples of the user biometric data are created. They
authentication along with password/ PIN then it becomes as are combined and their average stored in the user database, so
easy way to use ATMs with full proof authentication. that the different possibilities of the users samples during the
Biometric authentication mechanism is receiving a lot of actual authentication can roughly map to this average sample.
[3]
public attention. A biometric device is perhaps the ultimate
attempt in trying to prove who you are. Conceptual Model for ATM Banking with knowledge
based and biometric security:
CBS
IV. Working of biometric
authentication:
A biometric device works on the basis of some human
characteristics, such as fingerprint, voice or patter of line in the
iris of your eye. These devices include handprint detectors,
voice recognizers and identification patter in the retina.
Authentication with such devices uses unforgivable physical
characteristics to authenticate users. The user database
contains a sample of users biometric characteristics. During
authentication, the user is required to provide another sample
of the users biometric characteristics. This is matched with the
one in the database, and if the two samples are the same, then
the user is considered to be a valid user. Following figure
shows the working of biometric authentication process. [5] [6] [10]
Fig.2 Conceptual ATM model
ISSN No: 2250-3536 Volume 2, Issue 4, July 2012 10
International Journal of Advanced Technology & Engineering Research (IJATER)
3. If users fail more than 4 times to identify himself then
make provision to block that users account for that day
for security purpose.
4. If such blocks more than 4 times (within 3 months) then
block the user account and tell him to regenerate new
authentication in their home bank.
Fig.3 Biometric ATMs IX. Advantages of Card Less ATMS
1. Provides strong authentication.
2. Biometric system replaces card system with physiological
VI. Working: characteristics.
3. Hidden costs of ATM card management like- card
A typical biometrics authentication process involves: Firstly personalization, delivery, management, re-issuance, help-
the creation of the users biometric sample i.e. fingerprint desk, and re-issuance can be avoided.
recognition (Middle finger) etc. and its storage in the user 4. Ideal for Indian rural masses.
database in respective account holders bank. (Bank does this 5. Account holder may nominate for another person which
authorization). During the actual authentication, the user is will have valid identification for same account.
required to provide a sample of the same nature i.e. finger print 6. It is more helpful to senior citizens because it is difficult
etc. with its Personal Identification Number (PIN) and selected to carry and maintain card with him.
bank branch in caf centre (ATMs) then system will generate 7. Complaints regarding card such as - stolen cards,
code called virtual account identification (V-ID). This is regenerating new cards, maintaining and recording of
usually sent across in encrypted form (e.g. using SSL) through cards etc. will be eliminated. Thus it is helpful to bank to
network to the server. On the server side, the users current reduce cost, time and efforts for card process.
sample is decrypted and compared with the one stored in the 8. Flexible account access allows service users to access
database. their accounts as per their convenience.
If the two samples match to the expected degree on 9. Due to biometric authentication no one is able to access
the particular values, the users is considered as authenticate others account.
user and proceed further for transactions, otherwise user is 10. Users having authenticity to change their PIN code for
considered as invalid user and then terminates session. security purpose.
VII. Drawbacks of existing Card based X. Limitations
1. This method is costlier requires more instrument to be
ATMs installed in ATM centers.
1. Persons having Debit/Credit or different cards with PIN 2. Due to biometric only account holder (except nominee)
code is becomes owner of that account, without any other can access account.
identification of actual account holder. 3. Due to multiple authentications it is time consuming at
2. Existing system is on card basis so it requires more time to initial stage and requires fast and efficient technology to
process cards. manage such system.
3. If card is lost /stolen there is high possibility of misuse of 4. If service user is unable to input correct identification
card. within 4 chances then his/her account will be blocked
4. If card is stolen /lost then bank requires more time to and if such block more than 4 in 3 months then his/her
regenerate new card also it is costly. account is blocked and he/she has to re-identify himself
5. After 2/3 years or after repeated transactions card will in their home bank.
unable to operate, hence bank should have to provide new
card to account holder then it is expensive costly and time
consuming.
XI. Suggestions
6. Excess use of plastic cards is harmful for environment. 1. Separate efficient, talent and technical staff should be
7. If an account holder has multiple cards then it is difficult available in bank for supporting that system and for
to handle and use those cards. achieving better service user satisfaction.
2. Banks should have DEMO room for demonstrating new
technologies to service users, bank staff and have video
VIII. Requirement and Working conferencing system for live communication.
Conditions: 3. Bank should promote their service users for operating e-
banking services.
1. ATM centre should have biometric device for biometric
4. Bank may earn revenue by collecting nominal fees for
authentication and PIN pad to accept PIN.
providing training regarding usage of e-banking service
2. Authentication is required per transaction.
to their account holders which will help banks to
generate profit and with better customer relationship.
ISSN No: 2250-3536 Volume 2, Issue 4, July 2012 11
International Journal of Advanced Technology & Engineering Research (IJATER)
5. Banks should always support to their service users [2] Biometric ATMs for rural India, Chirasrota Jena,Weekly
regarding any problems while using e-banking services. Insight for Technology Professionals, 12,
March 2007, www. Expresscomputeronline.com, Access
date 16-Dec-2011
XII. Problems with biometric [3] Handbook of Biometrics. Springer. pp. 122. ISBN 978-0-
1. Biometrics techniques are relatively new, and some 387-71040-2.
people find their use intrusive. Hand geometry, http://www.springer.com/computer/image+processing/book/97
fingerprint and face recognition (which can be done from 8-1-4419-4375-0, access on 10-Dec-2011, 5.00pm
a camera across the room) are not quite enveloping, but [4] International References:
people have real concerns about peering (hard to watch) http://www.rediff.com/money/2005/oct/11atm.htm, Access on
into a laser beam or strictly a finger into a slot. 16- Dec- 2011, 11.00 am
2. Biometrics recognition devices are costly, although as [5] Jain, A., Hong, L., & Pankanti, S. (2000). "Biometric
the devices become more popular, their cost goes down. Identification", Communications of the ACM, 43(2), p. 91-98.
3. All biometrics readers use sampling and establish a [6] Jain, Anil K.; Ross, Arun (2008). "Introduction to
threshold for when a match is close enough to accept. Biometrics", pp. 45-60
The device has to sample the biometric, measure often [7] Krause Micki, Tipton Harold F., Handbook of Information
hundreds of key point, and compare that set of Security Management (Imprint: Auerbach Publications)
measurements with a template. There is normal (Publisher: CRC Press LLC), ISBN: 0849399475,
variability. http://www.ccert.edu.cn/education/cissp/hism/ewtoc.html, data
4. Although equipments are improving, there are still false access on 13-Dec-2011, 3.50 pm
reading / recognition. [8] Laudon Kenneth, Traver Carol Guercio, E-Commerce
5. The speed at which recognition must be done limits (2005), Second Edition , pp. 237-239, Pearson Education
accuracy. (Singapore), Pvt. Ltd.
[9] ONeil Erin, Back to the future at your local ATM,
XIII. Future ATMs http://banking.about.com/od/securityandsafety/a/biometricatms
Todays ATMs operating on the basis of card system and PIN, .htm, access on 16-Dec-2011 at 11.45 am
where as for better security biometric authentication is [10] Pfleeger Charles P., Pfleeger Shari Lacorence, Shah
growing demand. According to security experts, fingerprints Deven N. (2009), Security in Computing, User
can easily be lifted and replicated. The most secure biometric Authentication, pp. 257-258, IVth Edition, Pearson
technology uses a device designed to perform an iris scan Publication.
based on more than 2,000 unique measurement points. [11] S.C. Bihari, e-Banking, When Convenience Banking can
According to developers, people and pets all over the world Become Inconvenience, pp. 52-55, First Edition, Skylark
will be connected to a system that uses iris scan identification Publication, New Delhi
within the next decades. In future solar power and biometric [12] S.C. Bihari, e-Banking, When Convenience Banking can
with PIN based ATMs will be launched by banks especially in Become Inconvenience, pp. 85-91, First Edition, Skylark
rural areas. [13] Publication, New Delhi
[13] http://www.indianexpress.com/news/district-gets-its-first-
solar-biometric-atm/767886/, access on date 15-Dec-2011,
XIV. Conclusion 1.00 pm
Proposed conceptual model is designed for ATM users for
various transactions like withdrawing cash, balance enquiry
etc. Point of Sales (POS) machines will also use biometric Biographies
authentication. This system requires biometric authentication
(finger print, iris recognition) which is always with user, PIN 1. SATISH BHOSALE. Assistant Professor, MCA
code and selection of bank branch, which then creates virtual Dept. VPIMSR, Sangli. Pursuing Ph.D. from Shivaji
account (V-ID) it helps for identification and authentication of University, Kolhapur. Specialization in E-commerce,
service user. This is card less e-banking technique for ATMs, ERP, Software Engineering. Published and presented
which reduces efforts of handling, operating and various risks research articles in more than 16 National and
associated with cards. The same and simplified procedure will International Journals and various conferences. Satish
be helpful for Internet, Mobile and POS transactions. Due to Bhosale may be reached at stbhosale@yahoo.co.in.
unique method of authentication it reduces cost, time, efforts 2. Dr. B.S. Sawant. Director, KBPIMSR Satara.
of both banks as well as service users. Research guide. He had guided and awarded more
than 4 Ph.D. and 2 M.Phil. Students. He is Editor-in-
XV. References: Chief of ETHOS research journal. Dr. B. S. Sawant
may be reached at drbssawant@rediffmail.com
[1] Kahate Atul (2004), Cryptography and Network Security,
User Authentication Mechanism, pp. 303-
304, III rd Edition, McGraw-Hill Publications.
ISSN No: 2250-3536 Volume 2, Issue 4, July 2012 12
Anda mungkin juga menyukai
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Allotted List Round 2 PDFDokumen370 halamanAllotted List Round 2 PDFDeiva SigamaniBelum ada peringkat
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- Communications Theory by CHITODE PDFDokumen434 halamanCommunications Theory by CHITODE PDFDeiva SigamaniBelum ada peringkat
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5795)
- Industrial Automation On PLC and Scada: Presented by Saravanan.K Eie FinalyearDokumen13 halamanIndustrial Automation On PLC and Scada: Presented by Saravanan.K Eie FinalyearDeiva SigamaniBelum ada peringkat
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- BEEE 2013novdec 2015Dokumen2 halamanBEEE 2013novdec 2015Deiva SigamaniBelum ada peringkat
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- ShilpiDokumen21 halamanShilpiDeiva SigamaniBelum ada peringkat
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (345)
- GSM Based Anti-Theft Transaction SystemDokumen6 halamanGSM Based Anti-Theft Transaction SystemDeiva SigamaniBelum ada peringkat
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Commercial Prospects For Virginia Tech Nanotechnology: Cutting Edge Research Investment in Emerging TechnologiesDokumen31 halamanCommercial Prospects For Virginia Tech Nanotechnology: Cutting Edge Research Investment in Emerging TechnologiesDeiva SigamaniBelum ada peringkat
- Industrial Automation On PLC and Scada: Presented by Saravanan.K Eie FinalyearDokumen13 halamanIndustrial Automation On PLC and Scada: Presented by Saravanan.K Eie FinalyearDeiva SigamaniBelum ada peringkat
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (400)
- Moc 7811Dokumen5 halamanMoc 7811Deiva SigamaniBelum ada peringkat
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- Merchant Guide: Version 2.0 - November 2021Dokumen22 halamanMerchant Guide: Version 2.0 - November 2021wan muhdBelum ada peringkat
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
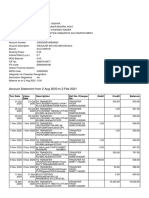
- Account Statement From 2 Aug 2020 To 2 Feb 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDokumen5 halamanAccount Statement From 2 Aug 2020 To 2 Feb 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit Balancefuture doctorBelum ada peringkat
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (74)
- Account Opening Form For Resident Individual (Single/Joint) AccountsDokumen12 halamanAccount Opening Form For Resident Individual (Single/Joint) AccountsSaikumar AvanigaddaBelum ada peringkat
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- Euroset 825 User ManualDokumen70 halamanEuroset 825 User ManualMd AlauddinBelum ada peringkat
- Rti Revoke Dod 17-6-2019Dokumen10 halamanRti Revoke Dod 17-6-2019ChakBelum ada peringkat
- Imagerunner Advance DX c259 - c359 - DatasheetDokumen4 halamanImagerunner Advance DX c259 - c359 - Datasheetvladimir latinovicBelum ada peringkat
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- 4444 17789 1 PBDokumen20 halaman4444 17789 1 PBHossain Moulude TejoBelum ada peringkat
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- BASE24-eps OverviewDokumen36 halamanBASE24-eps OverviewTedh Shin100% (4)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- IGNOU MCA 3rd Semster Object Oriented AnalysisDokumen17 halamanIGNOU MCA 3rd Semster Object Oriented AnalysisAmrutha Santosh KumarBelum ada peringkat
- List of Registered Independent Sales OrganizationsDokumen53 halamanList of Registered Independent Sales Organizationscdill70100% (1)
- Nokia E71x For AT&TDokumen125 halamanNokia E71x For AT&TWireflyBelum ada peringkat
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- SonalMarutiDivate (3y 0m)Dokumen2 halamanSonalMarutiDivate (3y 0m)Rashmi ShahBelum ada peringkat
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1091)
- Page - 1Dokumen60 halamanPage - 1Tahir HussainBelum ada peringkat
- MMX 352G USB Modem User ManualDokumen26 halamanMMX 352G USB Modem User ManualshivaarunachalaBelum ada peringkat
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Basic Pre-Contractual Information: Name and Address of N26 Bank GMBH, Sucursal en EspañaDokumen6 halamanBasic Pre-Contractual Information: Name and Address of N26 Bank GMBH, Sucursal en EspañaJosué BoteroBelum ada peringkat
- HDMF Contributions and Loan PaymentDokumen29 halamanHDMF Contributions and Loan PaymentRocelle IndicoBelum ada peringkat
- Bunna International Bank SDokumen12 halamanBunna International Bank STong89% (9)
- Sony Xperia XA1 Ultra - Schematic Diagarm PDFDokumen130 halamanSony Xperia XA1 Ultra - Schematic Diagarm PDFCami&coz Camí&coz0% (3)
- Ydm7116a Manual 200727 Isl-1865-04Dokumen2 halamanYdm7116a Manual 200727 Isl-1865-04HuanBelum ada peringkat
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Microcontroller ProjectsDokumen15 halamanMicrocontroller ProjectsPreet JAYSWALBelum ada peringkat
- ECL-ACC980 ManualDokumen4 halamanECL-ACC980 ManualAneal LiverpoolBelum ada peringkat
- Huawei Sne Mobile Phone User Guide - (Emui9.0.1 - 01, En-Uk, Normal)Dokumen68 halamanHuawei Sne Mobile Phone User Guide - (Emui9.0.1 - 01, En-Uk, Normal)FarzadBelum ada peringkat
- Top Features & Benefits On Your: NEO Credit Card!Dokumen4 halamanTop Features & Benefits On Your: NEO Credit Card!Raja Ram TyagiBelum ada peringkat
- Text Banking TcsDokumen6 halamanText Banking Tcsshivam markanBelum ada peringkat
- EMV v4.3 Book 1 ICC To Terminal Interface 2012060705394541Dokumen189 halamanEMV v4.3 Book 1 ICC To Terminal Interface 2012060705394541Sunil ShenavaBelum ada peringkat
- Answers & Audioscripts: - A Content-Based Listening Course For EFL LearnersDokumen46 halamanAnswers & Audioscripts: - A Content-Based Listening Course For EFL Learners497248871Belum ada peringkat
- Group 5 Assignment 5 Developing A Physical Secuirty ArchitectureDokumen34 halamanGroup 5 Assignment 5 Developing A Physical Secuirty Architectureapi-651266391Belum ada peringkat
- ADVT User Guide 6 0 PDFDokumen163 halamanADVT User Guide 6 0 PDFsaddamibnsyedBelum ada peringkat
- Brother MFD EmbeddedDokumen5 halamanBrother MFD EmbeddedMartijn ReinderinkBelum ada peringkat
- Secure Live ATM Transaction Using Steganography and Image ProcessingDokumen8 halamanSecure Live ATM Transaction Using Steganography and Image ProcessingInternational Journal of Innovative Science and Research TechnologyBelum ada peringkat
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)