Azure Security Infographic
Diunggah oleh
Federating for HealthHak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Azure Security Infographic
Diunggah oleh
Federating for HealthHak Cipta:
Format Tersedia
cloud
Microsoft Azure
security
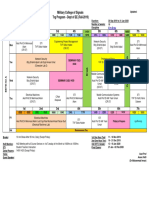
Join forces with Microsoft Azure
Benefit from Microsoft’s unmatched scale and experience running
trusted enterprise cloud services around the globe. Leverage our
deep investments in technology, operational processes, and expertise
to provide a trusted platform for your cloud initiatives. With Microsoft
as your ally, you can take advantage of the cloud more quickly while
reducing security and compliance costs and minimizing risk to your
organization.
IDENTITY AND ACCESS
Azure offers enterprise-level cloud identity governance that enables
you to manage access for your users:
• Sync existing identities and enable single sign-on to Azure, Office
AZURE
CLOUD APPS 365, and a world of other cloud applications
ACTIVE DIRECTORY
• Monitor access patterns to identify and mitigate potential threats
• Help prevent unauthorized access with Azure Multi-Factor
Authentication
• Empower end users with self-service identity management
capabilities
ACTIVE DIRECTORY
CE
N
IA
NETWORK SECURITY
PL
Your Azure virtual machines and data are isolated from undesirable
traffic and users. However, you can access them through encrypted or
M
private connections:
VPN
• Benefit from firewalled and partitioned networks to help protect
CO
against unwanted traffic from the Internet
• Securely connect to your on-premises datacenter or a single
computer using Azure Virtual Network
+
EXPRESSROUTE • Manage your virtual machines with encrypted remote desktop and
Y
Windows PowerShell sessions
AC
VIRTUAL NETWORK
• Keep your traffic off the Internet by using Azure ExpressRoute, a
AZURE ON-PREMISES private fiber link between you and Azure
IV
DATA PROTECTION PR
+
Microsoft makes data protection a priority. Technology safeguards,
such as encryption, and operational processes about data destruction
TY
keep your data yours only:
• Encryption is used to help secure data in transit between
RI
datacenters and you, as well as between and at Microsoft
CU
datacenters
• You can choose to implement additional encryption using a range
of approaches—you control the encryption method and keys
SE
• If you delete data or leave Azure, we follow strict industry standards
ENCRYPTED DATA DATA
that call for overwriting storage resources before reuse, as well as
COMMUNICATIONS ENCRYPTION DESTRUCTION
physically disposing of decommissioned hardware
DATA PRIVACY
Microsoft is committed to safeguarding the privacy of your data, and
you control where your data resides and who can access it:
• Specify the geographic areas where your data is stored—data can
be replicated within a geographic area for redundancy
• Get additional contractual commitments about the transfer of
personal data to address the E.U. Data Protection Directive
• Limit Microsoft access to and use of your data—we strictly control
and permit access only as necessary to provide or troubleshoot
the service
• We never use your customer data for advertising purposes
YOU
UPDATES MONITORING TESTING
THREAT DEFENSE
Protection from known and emerging threats requires constant
vigilance, and an array of defenses is in place:
• Integrated deployment systems manage security updates for
Microsoft software, and you can apply update management
MICROSOFT
processes to your virtual machines
• Continuous monitoring and analysis of traffic reveal anomalies and
threats—forensic tools dissect attacks, and you can implement
logging to aid analysis
• You can conduct penetration testing of applications you run in
Azure—we take care of penetration testing for Azure services
{
COMPLIANCE PROGRAMS AND CERTIFICATIONS
ISO 27001 Cloud compliance is easier with Azure. By providing compliant,
independently verified services, we help you streamline compliance for
SOC 1 the infrastructure and applications you run in Azure. We share detailed
information—including audit reports and compliance packages—to
SOC 2 provide insight into how specific regulatory standards are met.
FedRAMP
UK G-Cloud
PCI DSS
HIPAA
MICROSOFT MICROSOFT
MICROSOFT MICROSOFT
Like it? Get it.
© 2014 Microsoft Corporation. All rights reserved. Created by the Azure poster team Email: Azureposter@microsoft.com
Anda mungkin juga menyukai
- AZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500Dari EverandAZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500Belum ada peringkat
- Cloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingDari EverandCloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingBelum ada peringkat
- Zscaler Internet AccessDokumen8 halamanZscaler Internet Accessmdaashik9102Belum ada peringkat
- Azure Networking Pitch DeckDokumen71 halamanAzure Networking Pitch Decktarunsood2009Belum ada peringkat
- Zscaler Sase OverviewDokumen2 halamanZscaler Sase OverviewDSN.Rachel MadrigalBelum ada peringkat
- Zpa For AzureDokumen7 halamanZpa For AzureVineet Kohli100% (1)
- Virtual Private Network As A Service A Need For Discrete Cloud Architecture PDFDokumen7 halamanVirtual Private Network As A Service A Need For Discrete Cloud Architecture PDFsania nadafBelum ada peringkat
- Skyhigh Security Security Service Edge (SSE)Dokumen8 halamanSkyhigh Security Security Service Edge (SSE)Kundan KumarBelum ada peringkat
- Okta + Zscaler: Deliver Seamless Authentication and Security To Cloud-Based ApplicationsDokumen3 halamanOkta + Zscaler: Deliver Seamless Authentication and Security To Cloud-Based ApplicationsnewscollectingBelum ada peringkat
- Cloud-Delivered Security For The Digital WorkspaceDokumen5 halamanCloud-Delivered Security For The Digital WorkspaceMaliha Ikhlass WardallyBelum ada peringkat
- Zscaler Cloud Protection at A GlanceDokumen2 halamanZscaler Cloud Protection at A GlanceMossasi ChunBelum ada peringkat
- SOLUTION BRIEF - Zscaler Cloud Protection (ZCP)Dokumen2 halamanSOLUTION BRIEF - Zscaler Cloud Protection (ZCP)Prasad KshirsagarBelum ada peringkat
- Network As Code Architecture Cross-BG Presentation-1Dokumen10 halamanNetwork As Code Architecture Cross-BG Presentation-1Upma GandhiBelum ada peringkat
- Cloud Computing IEEE PaperDokumen4 halamanCloud Computing IEEE PaperAsrar Ul HaqBelum ada peringkat
- CloudDokumen20 halamanCloudIkhwan Firdaus NurgumilarBelum ada peringkat
- Netskope Cloud-FirewallDokumen2 halamanNetskope Cloud-Firewallarifien.somaBelum ada peringkat
- Fundamentals of Cloud ComputingDokumen49 halamanFundamentals of Cloud ComputingCornel BentBelum ada peringkat
- Okta Session Handout 1Dokumen24 halamanOkta Session Handout 1scott tangBelum ada peringkat
- Azure Enterprise-Ready NetworkingDokumen42 halamanAzure Enterprise-Ready NetworkingspringleeBelum ada peringkat
- 【HSE】2021 HSE Training - Product Professional - H3C CloudnetDokumen41 halaman【HSE】2021 HSE Training - Product Professional - H3C CloudnetAndre GermaineBelum ada peringkat
- Cloud Networking Portfolio: Universal Cloud Network and EcosystemDokumen6 halamanCloud Networking Portfolio: Universal Cloud Network and EcosystemabenyeungBelum ada peringkat
- NB 06 Networking Aag Cte enDokumen2 halamanNB 06 Networking Aag Cte entest001133557799Belum ada peringkat
- SSE Brief - Cloudflare One 2023 v2Dokumen2 halamanSSE Brief - Cloudflare One 2023 v2Ra SkynthBelum ada peringkat
- Aveva LFM Datasheet 2018Dokumen4 halamanAveva LFM Datasheet 2018kakoso74Belum ada peringkat
- Zscaler Digital Experience Data SheetDokumen8 halamanZscaler Digital Experience Data SheetJames CookeBelum ada peringkat
- Zscaler Internet Access - 2022Dokumen7 halamanZscaler Internet Access - 2022Mossasi ChunBelum ada peringkat
- Microsoft Azure Use Cases For Everyone: EbookDokumen16 halamanMicrosoft Azure Use Cases For Everyone: EbookkumarajaBelum ada peringkat
- NVS Getting Access To On Premises Apps and Resources With Microsoft TunnelDokumen15 halamanNVS Getting Access To On Premises Apps and Resources With Microsoft TunnelSubash AcharyaBelum ada peringkat
- Aviatrix Cloud Network Platform Solution Brief v6Dokumen3 halamanAviatrix Cloud Network Platform Solution Brief v6hari gautamBelum ada peringkat
- f5 Distributed Cloud Mesh DsDokumen6 halamanf5 Distributed Cloud Mesh DsDuDu DevBelum ada peringkat
- Cybersecurity Insurance Qualification MadeDokumen2 halamanCybersecurity Insurance Qualification MadeLEO RCBelum ada peringkat
- Protect Your Organization From RansomwareDokumen1 halamanProtect Your Organization From RansomwareEsk ImouBelum ada peringkat
- AZ 140T00A ENU Powerpoint 04Dokumen18 halamanAZ 140T00A ENU Powerpoint 04marcmanuel.azureBelum ada peringkat
- ACE Prof Mod2a - MCNADokumen9 halamanACE Prof Mod2a - MCNASyed Asad RazaBelum ada peringkat
- Application of Dynamic Token Check Technique in Cloud ComputingDokumen6 halamanApplication of Dynamic Token Check Technique in Cloud ComputingerpublicationBelum ada peringkat
- Zscaler Private Access: Fast, Direct, Secure Private App Access For All Users, Devices, and LocationsDokumen10 halamanZscaler Private Access: Fast, Direct, Secure Private App Access For All Users, Devices, and LocationsMohammed AbdulBelum ada peringkat
- Brkarc 3001Dokumen75 halamanBrkarc 3001Cap StormBelum ada peringkat
- Zscaler Internet AccessDokumen5 halamanZscaler Internet AccessPrasad KshirsagarBelum ada peringkat
- ThousandEyes Product Brief Platform OverviewDokumen2 halamanThousandEyes Product Brief Platform OverviewNguyen Ngoc DuyBelum ada peringkat
- Cloud Computing FundamentalsDokumen30 halamanCloud Computing FundamentalsARJIT KULSHRESTHABelum ada peringkat
- Azure Developers Sheet-DarkDokumen1 halamanAzure Developers Sheet-Darkthiyagu_808Belum ada peringkat
- MSFT Cloud Architecture SecurityDokumen9 halamanMSFT Cloud Architecture SecurityPratik KadamBelum ada peringkat
- EPN Vs VPNDokumen1 halamanEPN Vs VPNZahirah amniBelum ada peringkat
- Transtelco Tech-Sheet AZUREDokumen3 halamanTranstelco Tech-Sheet AZUREMayra MunozBelum ada peringkat
- SWIFT Infosheet Alliance Connect VirtualDokumen1 halamanSWIFT Infosheet Alliance Connect VirtualTomm LeeBelum ada peringkat
- Netskope Security Service Edge (SSE) : Solution BriefDokumen6 halamanNetskope Security Service Edge (SSE) : Solution BriefPacBelum ada peringkat
- InfoVista Ativa Automated Assurance and OperationsDokumen6 halamanInfoVista Ativa Automated Assurance and Operationsedo sadonoBelum ada peringkat
- Use Case ZscalerDokumen48 halamanUse Case ZscalerMossasi ChunBelum ada peringkat
- Cloud Computing Security Issues & Challenges: A Review: Avijit Mondal & Subrata Paul Radha Tamal Goswami Sayan NathDokumen5 halamanCloud Computing Security Issues & Challenges: A Review: Avijit Mondal & Subrata Paul Radha Tamal Goswami Sayan NathMuhammad Atiq ur RehmanBelum ada peringkat
- Cisco Umbrella DNS Security Essentials Data SheetDokumen3 halamanCisco Umbrella DNS Security Essentials Data SheetDmitryBelum ada peringkat
- Product Brief Cloudflare Zero Trust 2022 Q2 PDFDokumen6 halamanProduct Brief Cloudflare Zero Trust 2022 Q2 PDFAgustín GonzálezBelum ada peringkat
- Cloud Computing-1 (1) With Pages RemovedDokumen6 halamanCloud Computing-1 (1) With Pages RemovedManikandan KBelum ada peringkat
- Meraki Whitepaper Guest AccessDokumen12 halamanMeraki Whitepaper Guest AccessJim MillerBelum ada peringkat
- Netskope Security Cloud Platform: Data-Centric. Cloud-Smart. FastDokumen4 halamanNetskope Security Cloud Platform: Data-Centric. Cloud-Smart. FastPacBelum ada peringkat
- Datasheet Nokia Mobile VPNDokumen2 halamanDatasheet Nokia Mobile VPNIndriyanto PkgBelum ada peringkat
- Fortinet EMEA Channel 40mins Webinar FortiSASE Q42022Dokumen27 halamanFortinet EMEA Channel 40mins Webinar FortiSASE Q42022sadique010Belum ada peringkat
- MSFT Cloud Architecture NetworkingDokumen12 halamanMSFT Cloud Architecture NetworkingPedro SantosBelum ada peringkat
- 1 s20 S1389128621002474 Main - 221130 - 191957Dokumen8 halaman1 s20 S1389128621002474 Main - 221130 - 191957Gattem Raghu RamBelum ada peringkat
- Data Profile Cloud LokalDokumen30 halamanData Profile Cloud LokalNCI MediSmartBelum ada peringkat
- DGTL BRKRST 2377Dokumen164 halamanDGTL BRKRST 2377masterlinh2008Belum ada peringkat
- Configuring and Debugging EximDokumen42 halamanConfiguring and Debugging EximGabriel H. MartinezBelum ada peringkat
- CobolDokumen30 halamanCobolCesar RenteriaBelum ada peringkat
- Hightech Product Export Promotion SchemeDokumen5 halamanHightech Product Export Promotion SchemeMalay9099Belum ada peringkat
- SAP Implementation Methodlogies BigBang Vs PhasesDokumen6 halamanSAP Implementation Methodlogies BigBang Vs PhasesLionelkeneth12Belum ada peringkat
- Cospas Sarsat - T.001 - Oct2014Dokumen70 halamanCospas Sarsat - T.001 - Oct2014Amador Garcia IIIBelum ada peringkat
- Chemistry v1.00 For TI-89 Flash Application Senior Programmer: Matt AcostaDokumen5 halamanChemistry v1.00 For TI-89 Flash Application Senior Programmer: Matt Acostahasta abajo garganta profundaBelum ada peringkat
- Digital Marketing Scope and Career OpportunitiesDokumen15 halamanDigital Marketing Scope and Career Opportunitiesarunmittal1985Belum ada peringkat
- UsingDokumen28 halamanUsingCristo_Alanis_8381Belum ada peringkat
- Apollo DevelopmentsDokumen2 halamanApollo DevelopmentscarlosBelum ada peringkat
- Computers in RailwaysDokumen1.014 halamanComputers in Railwaysgokulvarmarajak100% (5)
- Is Your Class Site : Clean?Dokumen32 halamanIs Your Class Site : Clean?yk007Belum ada peringkat
- Data Stage PPT MaterialsDokumen216 halamanData Stage PPT MaterialsAntoni GomezBelum ada peringkat
- Business Communication - Business PresentationsDokumen8 halamanBusiness Communication - Business PresentationsPiyush Mittal100% (1)
- TCP-IP Guide V1-0Dokumen32 halamanTCP-IP Guide V1-0John GreenBelum ada peringkat
- 55101-mt - Design and Analysis of AlgorithmsDokumen2 halaman55101-mt - Design and Analysis of AlgorithmsSRINIVASA RAO GANTABelum ada peringkat
- Itt MCQDokumen48 halamanItt MCQJ Anne JoshuaBelum ada peringkat
- Comparative Study of Gaussian and Box-Car Filter of L-Band SIR-C Data Image Using Pol-SAR For Speckle Noise ReductionDokumen5 halamanComparative Study of Gaussian and Box-Car Filter of L-Band SIR-C Data Image Using Pol-SAR For Speckle Noise ReductionPORNIMA JAGTAPBelum ada peringkat
- Stanford HandoutDokumen221 halamanStanford Handoutsrinip_007100% (1)
- How To Fix Volume Shadow Copy Service ErrorsDokumen4 halamanHow To Fix Volume Shadow Copy Service ErrorsJoshua MazerBelum ada peringkat
- ENG Change Order ProcessDokumen2 halamanENG Change Order Processsoureddy1981Belum ada peringkat
- SSCD Module1Dokumen72 halamanSSCD Module1Chirag UBelum ada peringkat
- Truespace For DarkBASIC ProfessionalDokumen13 halamanTruespace For DarkBASIC ProfessionalclaudefrancisBelum ada peringkat
- Uml Class DiagramsDokumen35 halamanUml Class DiagramsNihal MullaBelum ada peringkat
- BIM Roadmap - Cheng Tai FattDokumen33 halamanBIM Roadmap - Cheng Tai Fattusernaga84Belum ada peringkat
- Programas VHDLDokumen7 halamanProgramas VHDLLuisDuránBelum ada peringkat
- Ug TRG Prog Fall 2019Dokumen17 halamanUg TRG Prog Fall 2019Muhaamad Haseeb KhokharBelum ada peringkat
- AIM For Business Flows Bf.016 Application Setup Document: Oracle Process Manufacturing - Process ExecutionDokumen8 halamanAIM For Business Flows Bf.016 Application Setup Document: Oracle Process Manufacturing - Process ExecutionAbderrazak JouiniBelum ada peringkat
- Old Company Name in Catalogs and Other DocumentsDokumen26 halamanOld Company Name in Catalogs and Other DocumentsSujith KmBelum ada peringkat
- P.E.S. College of Engineering, Mandya - 571 401Dokumen2 halamanP.E.S. College of Engineering, Mandya - 571 401saifBelum ada peringkat