An 993
Diunggah oleh
GlennDeskripsi Asli:
Judul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
An 993
Diunggah oleh
GlennHak Cipta:
Format Tersedia
AN993
Interfacing Microwire Serial EEPROMs to PIC16 Devices
This application note provides assistance and source
Author: Chris Parris
code to ease the design process of interfacing a
Microchip Technology Inc.
Microchip PIC16F54 PICmicro® microcontroller to a
Microchip Microwire serial EEPROM, without the use of
a hardware serial port.
INTRODUCTION
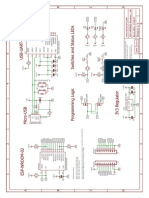
Figure 1 depicts the hardware schematic for the inter-
There are many different microcontrollers on the face between Microchip’s Microwire devices and the
market today that are being used in embedded control Microchip PIC16F54 microcontroller. The schematic
applications. Many of these embedded control systems shows the necessary connections to interface the
need nonvolatile memory. Because of their small foot- microcontroller and the serial EEPROM (the firmware
print, byte level flexibility, low I/O pin requirement, low was written assuming these connections).
power consumption and low cost, serial EEPROMs are
a popular choice for nonvolatile storage.
Microchip Technology has addressed these needs by
offering a full line of serial EEPROMs covering industry
standard serial communication protocols for two-wire
(I2C™), three-wire (Microwire), and SPI™ communica-
tion. Serial EEPROM devices are available in a variety
of densities, operational voltage ranges, and packaging
options.
FIGURE 1: CIRCUIT FOR PIC16F54 AND 93 SERIES (MICROWIRE) DEVICE
PDIP (300 MIL) RA2 1 18 RA1
RA3 2 17 RA0
T0CKI 3 16 OSC1/CLKIN
PIC16F54
MCLR/VPP 4 15 OSC2/CLKOUT
VSS 5 14 VDD
RB0 6 13 RB7/PGD
RB1 7 12 RB6/PGC
RB2 8 11 RB5
RB3 9 10 RB4
Vcc
CS(1) 1 8 Vcc 10K
93XXXXX
CLK 2 7 PE(2)
10K
DI 3 6 ORG(3)
DO 4 5 Vss
Note 1: CS should always have a pull-down resistor to protect against data corruption during power-up or power-down of the
microcontroller.
2: PE pin available only on 93XX76X and 93XX86X devices. Pull-up resistor suggested ~10K ohm.
3: ORG pin available only on 93XXXXC devices.
© 2005 Microchip Technology Inc. DS00993A-page 1
AN993
FIRMWARE DESCRIPTION
The purpose of the program is to show individual
features of the Microwire protocol and give code
samples of the Start bit, opcodes and addressing
schemes so that the basic building blocks of a program
can be shown. The firmware performs five basic
operations:
• Erase/Write Enable command
• Write command for one word of data
• Ready/Busy polling
• Read command for one word of data
• Erase/Write Disable command
The code was tested using the 93LC66B serial
EEPROM. This device features 256 x 16 (4 Kbit) of
memory and 16-bit organization. A 10 MHz crystal
oscillator is used to clock the PIC16F54. If a faster
clock is used, the code must be modified to ensure all
timing specs are met. The waveforms provided are
shown from CS active to CS disable so an entire
instruction can be seen. To ease the interpretation of
the serial data, the data sheet waveforms are provided
below the oscilloscope screen shots. All values
represented in this application note are decimal values
unless otherwise noted.
Device Setup
Although this application note focuses on the 93LC66B
device, the firmware supports all 93XXXX devices. This
is done by setting the following two constants at the
beginning of the source code:
• NUMBITS
• ORGVAL
The NUMBITS constant is used in the output subrou-
tines to determine how many bits are required to be
output. More specifically, it is used by the EWEN and
EWDS commands to calculate the number of dummy
bits required. It is also used by the Read and Write
subroutines to skip over the unused bits in the address
word. This constant must equal the required number of
clock cycles for an EWEN command (11 for the
93XX66B).
Note: On devices of the same density, the
required number of clock cycles differs
between 8-bit and 16-bit organizations.
Therefore, if the organization is changed,
NUMBITS must also be updated appropri-
ately.
The ORGVAL constant specifies the data organization.
This value must be set to either 8 or 16, depending
upon which device organization is being used. The
93XXXXA devices use 8-bit organization, whereas the
93XXXXB devices use 16-bit organization. Further-
more, the 93XXXXC devices allow a selectable word
size (either 8 or 16-bit) through the use of the ORG pin.
DS00993A-page 2 © 2005 Microchip Technology Inc.
AN993
WRITE ENABLE
Figure 2 shows an example of the Erase/Write Enable
(EWEN) command. Chip Select is brought high
(active), and the Start bit and four-bit opcode (‘0011’)
are sent out first, with the required number of dummy
bits (6 for the 93XX66B) following. The EWEN com-
mand must be given before a write is attempted. The
device will be enabled for writes until an Erase/Write
Disable command is given or the device is powered
down.
FIGURE 2: ERASE/WRITE ENABLE (EWEN)
TCSL
CS
CLK
1 0 0 1 1 x ••• x
DI
© 2005 Microchip Technology Inc. DS00993A-page 3
AN993
WRITE COMMAND (START BIT, Once the internal write cycle has begun, the Ready/
Busy signal can be polled on the DO pin to check when
OPCODE, ADDRESS AND DATA)
the write finishes. A 6 ms delay needs to be added if the
Figure 3 shows an example of the Write command. The Ready/Busy status is not being polled. This code uses
device is selected and the Start bit, opcode and the Ready/Busy polling.
word address are sent out. Next, the data is clocked out
to the device. When the Chip Select is toggled, the
internal write cycle is initiated.
FIGURE 3: WRITE COMMAND, ADDRESS AND DATA
TCSL
CS
CLK
DI 1 0 1 An ••• A0 Dx ••• D0
TSV TCZ
High-Z
DO Busy Ready
High-Z
TWC
DS00993A-page 4 © 2005 Microchip Technology Inc.
AN993
READY/BUSY POLLING
After a valid Write command is given, the DO line of the Note that the 93AAXX and 93LCXX devices have a
93XXXX can be monitored to check if the internal write maximum program cycle time (TWC) of 6 ms, but in this
cycle has been successfully initiated and, if so, to example, the write cycle only lasted 3.2 ms. This
determine when the write cycle is complete. The oscil- illustrates that the write cycle typically is much shorter
loscope plot below shows that the device is selected than the specified maximum. Therefore, it can be highly
and the DO line is low for approximately 3.2 ms before beneficial to take advantage of the Ready/Busy polling
the device brings the DO line high, indicating that the feature, so as to increase efficiency when writing
write cycle is complete. multiple words of data to the device.
FIGURE 4: READY/BUSY POLLING
© 2005 Microchip Technology Inc. DS00993A-page 5
AN993
READ COMMAND (START BIT,
OPCODE, ADDRESS AND DATA)
Figure 5 shows an example of the Read command.
The device is selected and the Start bit, opcode and the
word address are sent out. At this point, the device gets
ready to transmit data. The microcontroller must gener-
ate the clock signals, and read DO on each falling clock
edge. In this example, the data being read is 0x55AA.
FIGURE 5: READ COMMAND
CS
CLK
DI 1 1 0 An ••• A0
DO High-Z
0 Dx ••• D0 Dx ••• D0 Dx ••• D0
DS00993A-page 6 © 2005 Microchip Technology Inc.
AN993
ERASE/WRITE DISABLE COMMAND
Once the internal write cycle is complete, the Write The EWDS command should always be sent to the
Disable (EWDS) command should be given (see device after completing a write or prior to powering
Figure 6). This command consists of a Start bit and the down the device/system.
four-bit opcode (‘0000’), followed by the appropriate
number of dummy bits (6 for the 93XX66B).
FIGURE 6: ERASE/WRITE DISABLE COMMAND
TCSL
CS
CLK
DI 1 0 0 0 0 x ••• x
© 2005 Microchip Technology Inc. DS00993A-page 7
AN993
CONCLUSION
These are some of the basic features of Microwire
communications on one of Microchip’s PIC16 devices
without the use of a hardware serial port. The code is
highly portable and can be used on many PICmicro®
microcontrollers with very minor modifications. Using
the code provided, designers can begin to build their
own Microwire libraries to be as simple or as complex
as needed.
The code was tested on Microchip’s PICDEM™ 2 Plus
Demonstration Board with the connections shown in
Figure 1.
DS00993A-page 8 © 2005 Microchip Technology Inc.
Note the following details of the code protection feature on Microchip devices:
• Microchip products meet the specification contained in their particular Microchip Data Sheet.
• Microchip believes that its family of products is one of the most secure families of its kind on the market today, when used in the
intended manner and under normal conditions.
• There are dishonest and possibly illegal methods used to breach the code protection feature. All of these methods, to our
knowledge, require using the Microchip products in a manner outside the operating specifications contained in Microchip’s Data
Sheets. Most likely, the person doing so is engaged in theft of intellectual property.
• Microchip is willing to work with the customer who is concerned about the integrity of their code.
• Neither Microchip nor any other semiconductor manufacturer can guarantee the security of their code. Code protection does not
mean that we are guaranteeing the product as “unbreakable.”
Code protection is constantly evolving. We at Microchip are committed to continuously improving the code protection features of our
products. Attempts to break Microchip’s code protection feature may be a violation of the Digital Millennium Copyright Act. If such acts
allow unauthorized access to your software or other copyrighted work, you may have a right to sue for relief under that Act.
Information contained in this publication regarding device Trademarks
applications and the like is provided only for your convenience The Microchip name and logo, the Microchip logo, Accuron,
and may be superseded by updates. It is your responsibility to
dsPIC, KEELOQ, microID, MPLAB, PIC, PICmicro, PICSTART,
ensure that your application meets with your specifications.
PRO MATE, PowerSmart, rfPIC, and SmartShunt are
MICROCHIP MAKES NO REPRESENTATIONS OR WAR- registered trademarks of Microchip Technology Incorporated
RANTIES OF ANY KIND WHETHER EXPRESS OR IMPLIED,
in the U.S.A. and other countries.
WRITTEN OR ORAL, STATUTORY OR OTHERWISE,
RELATED TO THE INFORMATION, INCLUDING BUT NOT AmpLab, FilterLab, Migratable Memory, MXDEV, MXLAB,
LIMITED TO ITS CONDITION, QUALITY, PERFORMANCE, PICMASTER, SEEVAL, SmartSensor and The Embedded
MERCHANTABILITY OR FITNESS FOR PURPOSE. Control Solutions Company are registered trademarks of
Microchip disclaims all liability arising from this information and Microchip Technology Incorporated in the U.S.A.
its use. Use of Microchip’s products as critical components in Analog-for-the-Digital Age, Application Maestro, dsPICDEM,
life support systems is not authorized except with express dsPICDEM.net, dsPICworks, ECAN, ECONOMONITOR,
written approval by Microchip. No licenses are conveyed, FanSense, FlexROM, fuzzyLAB, In-Circuit Serial
implicitly or otherwise, under any Microchip intellectual property Programming, ICSP, ICEPIC, Linear Active Thermistor,
rights. MPASM, MPLIB, MPLINK, MPSIM, PICkit, PICDEM,
PICDEM.net, PICLAB, PICtail, PowerCal, PowerInfo,
PowerMate, PowerTool, rfLAB, rfPICDEM, Select Mode,
Smart Serial, SmartTel, Total Endurance and WiperLock are
trademarks of Microchip Technology Incorporated in the
U.S.A. and other countries.
SQTP is a service mark of Microchip Technology Incorporated
in the U.S.A.
All other trademarks mentioned herein are property of their
respective companies.
© 2005, Microchip Technology Incorporated, Printed in the
U.S.A., All Rights Reserved.
Printed on recycled paper.
Microchip received ISO/TS-16949:2002 quality system certification for
its worldwide headquarters, design and wafer fabrication facilities in
Chandler and Tempe, Arizona and Mountain View, California in
October 2003. The Company’s quality system processes and
procedures are for its PICmicro® 8-bit MCUs, KEELOQ® code hopping
devices, Serial EEPROMs, microperipherals, nonvolatile memory and
analog products. In addition, Microchip’s quality system for the design
and manufacture of development systems is ISO 9001:2000 certified.
© 2005 Microchip Technology Inc. DS00993A-page 9
WORLDWIDE SALES AND SERVICE
AMERICAS ASIA/PACIFIC ASIA/PACIFIC EUROPE
Corporate Office Australia - Sydney India - Bangalore Austria - Weis
2355 West Chandler Blvd. Tel: 61-2-9868-6733 Tel: 91-80-2229-0061 Tel: 43-7242-2244-399
Chandler, AZ 85224-6199 Fax: 61-2-9868-6755 Fax: 91-80-2229-0062 Fax: 43-7242-2244-393
Tel: 480-792-7200 China - Beijing India - New Delhi Denmark - Ballerup
Fax: 480-792-7277 Tel: 86-10-8528-2100 Tel: 45-4450-2828
Tel: 91-11-5160-8631
Technical Support: Fax: 86-10-8528-2104 Fax: 45-4485-2829
Fax: 91-11-5160-8632
http://support.microchip.com
China - Chengdu Japan - Kanagawa France - Massy
Web Address:
Tel: 86-28-8676-6200 Tel: 81-45-471- 6166 Tel: 33-1-69-53-63-20
www.microchip.com
Fax: 86-28-8676-6599 Fax: 81-45-471-6122 Fax: 33-1-69-30-90-79
Atlanta
Alpharetta, GA China - Fuzhou Korea - Seoul Germany - Ismaning
Tel: 86-591-8750-3506 Tel: 82-2-554-7200 Tel: 49-89-627-144-0
Tel: 770-640-0034
Fax: 86-591-8750-3521 Fax: 82-2-558-5932 or Fax: 49-89-627-144-44
Fax: 770-640-0307
China - Hong Kong SAR 82-2-558-5934 Italy - Milan
Boston
Tel: 852-2401-1200 Tel: 39-0331-742611
Westborough, MA Malaysia - Penang
Fax: 852-2401-3431 Tel:011-604-646-8870 Fax: 39-0331-466781
Tel: 774-760-0087
Fax: 774-760-0088 China - Shanghai Fax:011-604-646-5086 Netherlands - Drunen
Tel: 86-21-5407-5533 Tel: 31-416-690399
Chicago Philippines - Manila
Itasca, IL Fax: 86-21-5407-5066 Tel: 011-632-634-9065 Fax: 31-416-690340
Tel: 630-285-0071 China - Shenyang Fax: 011-632-634-9069 England - Berkshire
Fax: 630-285-0075 Tel: 86-24-2334-2829 Tel: 44-118-921-5869
Fax: 86-24-2334-2393 Singapore
Fax: 44-118-921-5820
Dallas Tel: 65-6334-8870
Addison, TX China - Shenzhen Fax: 65-6334-8850
Tel: 972-818-7423 Tel: 86-755-8203-2660
Taiwan - Kaohsiung
Fax: 972-818-2924 Fax: 86-755-8203-1760
Tel: 886-7-536-4818
Detroit China - Shunde Fax: 886-7-536-4803
Farmington Hills, MI Tel: 86-757-2839-5507 Taiwan - Taipei
Tel: 248-538-2250 Fax: 86-757-2839-5571 Tel: 886-2-2500-6610
Fax: 248-538-2260 China - Qingdao Fax: 886-2-2508-0102
Kokomo Tel: 86-532-502-7355 Taiwan - Hsinchu
Kokomo, IN Fax: 86-532-502-7205 Tel: 886-3-572-9526
Tel: 765-864-8360 Fax: 886-3-572-6459
Fax: 765-864-8387
Los Angeles
Mission Viejo, CA
Tel: 949-462-9523
Fax: 949-462-9608
San Jose
Mountain View, CA
Tel: 650-215-1444
Fax: 650-961-0286
Toronto
Mississauga, Ontario,
Canada
Tel: 905-673-0699
Fax: 905-673-6509
04/20/05
DS00993A-page 10 © 2005 Microchip Technology Inc.
Anda mungkin juga menyukai
- An1183 PDFDokumen16 halamanAn1183 PDFAdnen GuedriaBelum ada peringkat
- Interfacing Spi™ Serial Eeproms To Microchip Picmicro MicrocontrollersDokumen10 halamanInterfacing Spi™ Serial Eeproms To Microchip Picmicro MicrocontrollersEssel Jojo FlintBelum ada peringkat
- EEPROMSDokumen18 halamanEEPROMSalejandrodmsosaBelum ada peringkat
- PIC16C84 MicrochipDokumen110 halamanPIC16C84 MicrochipSalvador Herrera GrisBelum ada peringkat
- Pic 16 C 505Dokumen85 halamanPic 16 C 505Joel LopezBelum ada peringkat
- Interfacing The 8051 With 2-Wire Serial EepromsDokumen12 halamanInterfacing The 8051 With 2-Wire Serial EepromsNusret YılmazBelum ada peringkat
- PIC12C509ADokumen113 halamanPIC12C509AsandrorrrBelum ada peringkat
- Ocosii On DspicDokumen32 halamanOcosii On DspicptkienBelum ada peringkat
- Permanent Switch Board ContentDokumen56 halamanPermanent Switch Board ContentCrispBelum ada peringkat
- Microchip 18F877 DatasheetDokumen218 halamanMicrochip 18F877 DatasheetberetyBelum ada peringkat
- Dspic33F/Pic24H Flash Programming SpecificationDokumen84 halamanDspic33F/Pic24H Flash Programming SpecificationSobhi MahBelum ada peringkat
- 30430D PDFDokumen128 halaman30430D PDFAnonymous 1z5A6Lc4Belum ada peringkat
- PIC16F627Dokumen6 halamanPIC16F627kelyBelum ada peringkat
- So Do Chan ICDokumen305 halamanSo Do Chan ICManh NguyenvanBelum ada peringkat
- Transmission Line Multiple Fault Detection and Indication To Electricity BoardDokumen74 halamanTransmission Line Multiple Fault Detection and Indication To Electricity BoardCrisp100% (1)
- PIC16C63A/65B/73B/74B: 8-Bit CMOS Microcontrollers With A/D ConverterDokumen185 halamanPIC16C63A/65B/73B/74B: 8-Bit CMOS Microcontrollers With A/D ConverterroquecardanBelum ada peringkat
- Pic16F7X7 Data Sheet: 28/40/44-Pin, 8-Bit Cmos Flash Microcontrollers With 10-Bit A/D and Nanowatt TechnologyDokumen264 halamanPic16F7X7 Data Sheet: 28/40/44-Pin, 8-Bit Cmos Flash Microcontrollers With 10-Bit A/D and Nanowatt TechnologynitsakhBelum ada peringkat
- ECE 513 - PART1-Introduction To PIC16F84ADokumen46 halamanECE 513 - PART1-Introduction To PIC16F84AMitch100% (1)
- SST26VF064B SST26VF064BA 2 5V 3 0V 64 Mbit Serial - 2935898Dokumen91 halamanSST26VF064B SST26VF064BA 2 5V 3 0V 64 Mbit Serial - 2935898ManunoghiBelum ada peringkat
- MKT3811 Week4 03.11.2021 RDokumen62 halamanMKT3811 Week4 03.11.2021 REmirhan AlmaBelum ada peringkat
- PIC16F87XA Data Sheet: 28/40-Pin Enhanced FLASH MicrocontrollersDokumen222 halamanPIC16F87XA Data Sheet: 28/40-Pin Enhanced FLASH MicrocontrollersEziom AlvesBelum ada peringkat
- Pic16f8x PDFDokumen126 halamanPic16f8x PDFGilberto MataBelum ada peringkat
- PIC16F8X: 8-Bit CMOS Flash/EEPROM MicrocontrollersDokumen122 halamanPIC16F8X: 8-Bit CMOS Flash/EEPROM MicrocontrollerssebastienBelum ada peringkat
- PIC16F8X: 8-Bit CMOS Flash/EEPROM MicrocontrollersDokumen122 halamanPIC16F8X: 8-Bit CMOS Flash/EEPROM MicrocontrollersCagatay KaynakBelum ada peringkat
- PIC16C8X DatasheetDokumen117 halamanPIC16C8X DatasheetWarr SteelBelum ada peringkat
- Logic Powered Serial Eeproms: Parameter ConditionsDokumen11 halamanLogic Powered Serial Eeproms: Parameter ConditionsadilBelum ada peringkat
- PIC18XXXDokumen332 halamanPIC18XXXmilenarico100% (1)
- X24C04 4K 512 X 8 Bit: 3839 FHD F01Dokumen19 halamanX24C04 4K 512 X 8 Bit: 3839 FHD F01Legna80Belum ada peringkat
- Slaa 115Dokumen4 halamanSlaa 115api-3744762Belum ada peringkat
- Raana Semicondutors PVT LTD: ARM 7-LPC2148 Development BoardDokumen107 halamanRaana Semicondutors PVT LTD: ARM 7-LPC2148 Development BoardVimal RajBelum ada peringkat
- Pic ReportDokumen46 halamanPic ReportknlkohliBelum ada peringkat
- PIC16F84XDokumen33 halamanPIC16F84XSofi Caballero MestraBelum ada peringkat
- Pic 16f870 Data SheetDokumen172 halamanPic 16f870 Data SheetPedro BugueñoBelum ada peringkat
- Interface Clavier PicDokumen27 halamanInterface Clavier Picblaiso2020Belum ada peringkat
- PIC16F627A/628A/648A: 3.0 Architectural OverviewDokumen4 halamanPIC16F627A/628A/648A: 3.0 Architectural OverviewAndrés Gilberto Catalán HernándezBelum ada peringkat
- Using The MSSP Module To Interface Spi™ Serial Eeproms With Pic18 DevicesDokumen12 halamanUsing The MSSP Module To Interface Spi™ Serial Eeproms With Pic18 Deviceskraneak100% (3)
- PIC16F62X: FLASH-Based 8-Bit CMOS MicrocontrollersDokumen114 halamanPIC16F62X: FLASH-Based 8-Bit CMOS MicrocontrollersJames HamiltonBelum ada peringkat
- DS02 PDFDokumen224 halamanDS02 PDFanshu_ranjan1Belum ada peringkat
- Programmazione - AssemblerDokumen36 halamanProgrammazione - AssemblerArthBelum ada peringkat
- 93LC46ADokumen34 halaman93LC46AmordiscoverdeBelum ada peringkat
- 8051 Microcontroller: An Applications Based IntroductionDari Everand8051 Microcontroller: An Applications Based IntroductionPenilaian: 5 dari 5 bintang5/5 (6)
- C Programming for the PIC Microcontroller: Demystify Coding with Embedded ProgrammingDari EverandC Programming for the PIC Microcontroller: Demystify Coding with Embedded ProgrammingBelum ada peringkat
- Token Ring Technology ReportDari EverandToken Ring Technology ReportBelum ada peringkat
- Microprocessors & their Operating Systems: A Comprehensive Guide to 8, 16 & 32 Bit Hardware, Assembly Language & Computer ArchitectureDari EverandMicroprocessors & their Operating Systems: A Comprehensive Guide to 8, 16 & 32 Bit Hardware, Assembly Language & Computer ArchitecturePenilaian: 1 dari 5 bintang1/5 (1)
- The Engineering of Microprocessor Systems: Guidelines on System DevelopmentDari EverandThe Engineering of Microprocessor Systems: Guidelines on System DevelopmentBelum ada peringkat
- ARM Microcontrollers Programming for Embedded SystemsDari EverandARM Microcontrollers Programming for Embedded SystemsPenilaian: 5 dari 5 bintang5/5 (1)
- PLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.Dari EverandPLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.Belum ada peringkat
- Making PIC Microcontroller Instruments and ControllersDari EverandMaking PIC Microcontroller Instruments and ControllersBelum ada peringkat
- Introduction to 6800/6802 Microprocessor Systems: Hardware, Software and ExperimentationDari EverandIntroduction to 6800/6802 Microprocessor Systems: Hardware, Software and ExperimentationBelum ada peringkat
- 2N6071A/B Series Sensitive Gate Triacs: Silicon Bidirectional ThyristorsDokumen8 halaman2N6071A/B Series Sensitive Gate Triacs: Silicon Bidirectional ThyristorsAnonymous 3GwpCKBelum ada peringkat
- Declaratieunica 05102018 PDFDokumen1 halamanDeclaratieunica 05102018 PDFAnonymous 3GwpCKBelum ada peringkat
- Sim600 HD V1.06Dokumen47 halamanSim600 HD V1.06Anonymous 3GwpCKBelum ada peringkat
- Mixed Signal Microcontroller: FeaturesDokumen66 halamanMixed Signal Microcontroller: FeaturesCrhistian SeguraBelum ada peringkat
- Esp Wroom02 Breakout v10Dokumen2 halamanEsp Wroom02 Breakout v10Anonymous 3GwpCK100% (1)
- Neoway M590 AT Command Sets V3.0 PDFDokumen70 halamanNeoway M590 AT Command Sets V3.0 PDFtzotzBelum ada peringkat
- Ai Thinker ESP 01 enDokumen19 halamanAi Thinker ESP 01 enAnonymous 3GwpCKBelum ada peringkat
- Ai Thinker ESP 01 enDokumen19 halamanAi Thinker ESP 01 enAnonymous 3GwpCKBelum ada peringkat
- Atmel 8271 8 Bit AVR Microcontroller ATmega48A 48PA 88A 88PA 168A 168PA 328 328P - Datasheet - Complete PDFDokumen650 halamanAtmel 8271 8 Bit AVR Microcontroller ATmega48A 48PA 88A 88PA 168A 168PA 328 328P - Datasheet - Complete PDFNext MillBelum ada peringkat
- 20 Amp Current TransformerDokumen1 halaman20 Amp Current TransformerAnonymous 3GwpCKBelum ada peringkat
- Neoway M590 Hardware Design Manual V1.1 PDFDokumen29 halamanNeoway M590 Hardware Design Manual V1.1 PDFAnonymous 3GwpCKBelum ada peringkat
- MSP 430 G 2231Dokumen58 halamanMSP 430 G 2231andrewBelum ada peringkat
- PIC12F1571Dokumen334 halamanPIC12F1571Anonymous 3GwpCKBelum ada peringkat
- PIC16F1703Dokumen338 halamanPIC16F1703Anonymous 3GwpCKBelum ada peringkat
- Application Form - Sectiunea 1FDokumen21 halamanApplication Form - Sectiunea 1FAnonymous 3GwpCKBelum ada peringkat
- Spec T1-65WDokumen1 halamanSpec T1-65WAnonymous 3GwpCKBelum ada peringkat
- Pic12f1572 40001723CDokumen308 halamanPic12f1572 40001723CAnonymous 3GwpCKBelum ada peringkat
- 12F617Dokumen212 halaman12F617Paride E LauraBelum ada peringkat
- Cen TR 13201-1 2004Dokumen29 halamanCen TR 13201-1 2004Milos StojanovicBelum ada peringkat
- RH-70 RH-64 Schematics V1 0Dokumen6 halamanRH-70 RH-64 Schematics V1 0Anonymous 3GwpCKBelum ada peringkat
- ECHBDokumen442 halamanECHBAnonymous 3GwpCKBelum ada peringkat
- ECHBDokumen442 halamanECHBAnonymous 3GwpCKBelum ada peringkat
- Consumer Electronics Troubleshooting HandbookDokumen1.202 halamanConsumer Electronics Troubleshooting HandbookDjurica Daniel94% (35)
- D Safra Z 003342Dokumen20 halamanD Safra Z 003342bookreader1968Belum ada peringkat
- MEMS Fabrication Cycle and Key StepsDokumen179 halamanMEMS Fabrication Cycle and Key Stepsarun kumarBelum ada peringkat
- CircuitsDokumen32 halamanCircuitsHarsh ChauhanBelum ada peringkat
- 74HC245Dokumen11 halaman74HC245jnax101Belum ada peringkat
- Vlsi NotesDokumen5 halamanVlsi NotesDiwakar TiwaryBelum ada peringkat
- Multi-Format Digital HDTV Production Camera: CautionDokumen12 halamanMulti-Format Digital HDTV Production Camera: CautionGerman RojasBelum ada peringkat
- Learn Electronics With Basic Theory and Home ExperimentsDokumen427 halamanLearn Electronics With Basic Theory and Home ExperimentsAnderson Valderrama Perez50% (2)
- PDF Computer Science First BookDokumen203 halamanPDF Computer Science First BookEdinson LozanoBelum ada peringkat
- Bachelor of Technology in Electrical Engineering: Programme Level Year of Commencement Minimum Duration Maximum DurationDokumen6 halamanBachelor of Technology in Electrical Engineering: Programme Level Year of Commencement Minimum Duration Maximum Durationmayank kakkarBelum ada peringkat
- Chapter 1 Global VillageDokumen6 halamanChapter 1 Global VillageRbayusetiajiBelum ada peringkat
- Case MonotechDokumen7 halamanCase MonotechAnkita Sethi0% (1)
- Integrated CircuitDokumen21 halamanIntegrated CircuitahmedBelum ada peringkat
- Advanced MOSFET Structures and Processes For Sub-7 NM CMOS TechnologiesDokumen74 halamanAdvanced MOSFET Structures and Processes For Sub-7 NM CMOS TechnologiesxellosdexBelum ada peringkat
- VSX-82 84 RRV3477Dokumen72 halamanVSX-82 84 RRV3477gtmenBelum ada peringkat
- Electronics Projects Circuits Book PDFDokumen136 halamanElectronics Projects Circuits Book PDFMilos Mijatovic100% (1)
- On-Chip Communication ArchitecturesDokumen44 halamanOn-Chip Communication ArchitecturesnvnrevBelum ada peringkat
- IRM-8601 Receptor Infrarrojo Datasheet PDFDokumen8 halamanIRM-8601 Receptor Infrarrojo Datasheet PDFجون أندروBelum ada peringkat
- Generation of ComputersDokumen10 halamanGeneration of ComputersWINORLOSEBelum ada peringkat
- Analog VLSI Design: Nguyen Cao QuiDokumen72 halamanAnalog VLSI Design: Nguyen Cao QuiKhuong LamborghiniBelum ada peringkat
- Gate Level Design FundamentalsDokumen34 halamanGate Level Design FundamentalsYOGESWARI TOLIABelum ada peringkat
- Cooling of Electronic Equipments: HapterDokumen33 halamanCooling of Electronic Equipments: HapterVikas VermaBelum ada peringkat
- CHIPS NOFO-1 Fact Sheet 0Dokumen4 halamanCHIPS NOFO-1 Fact Sheet 0HoubailleBelum ada peringkat
- CircuitsDokumen474 halamanCircuitsSriramBelum ada peringkat
- Performance Comparison of 3D-Mesh and 3D-Torus Network-on-ChipDokumen5 halamanPerformance Comparison of 3D-Mesh and 3D-Torus Network-on-ChipJournal of ComputingBelum ada peringkat
- Deutsche BankDokumen10 halamanDeutsche BankSurabhi MattaBelum ada peringkat
- Unit I COA PPT New EditedDokumen161 halamanUnit I COA PPT New EditedKudzaishe ChitsengaBelum ada peringkat
- Design and Implementation of VLSI SystemsDokumen45 halamanDesign and Implementation of VLSI SystemsLê Bá Phước LongBelum ada peringkat
- Technological University of The Philippines: Lopez Extension CampusDokumen2 halamanTechnological University of The Philippines: Lopez Extension CampusbennieBelum ada peringkat
- Motherboard Voltage Regulator CircuitDokumen22 halamanMotherboard Voltage Regulator Circuitleon_sfBelum ada peringkat