DBS3900 WiMAX Feature Configuration Guide (V300R002C02 - 01)
Diunggah oleh
Varkis RathinamJudul Asli
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
DBS3900 WiMAX Feature Configuration Guide (V300R002C02 - 01)
Diunggah oleh
Varkis RathinamHak Cipta:
Format Tersedia
DBS3900 WiMAX
V300R002C02
Feature Configuration Guide
Issue 01
Date 2009-03-20
Huawei Proprietary and Confidential
Copyright © Huawei Technologies Co., Ltd.
Huawei Technologies Co., Ltd. provides customers with comprehensive technical support and service. For any
assistance, please contact our local office or company headquarters.
Huawei Technologies Co., Ltd.
Address: Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website: http://www.huawei.com
Email: support@huawei.com
Copyright © Huawei Technologies Co., Ltd. 2009. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior written
consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are the property of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective holders.
Notice
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but the statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Proprietary and Confidential
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
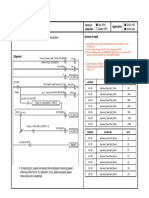
Feature Configuration Guide Contents
Contents
About This Document.....................................................................................................................1
1 HARQ Feature.............................................................................................................................1-1
1.1 Overview of the HARQ Feature......................................................................................................................1-2
1.2 Availability of the HARQ Feature..................................................................................................................1-4
1.3 Description of the HARQ Feature...................................................................................................................1-4
1.3.1 Fundamental Principles of the HARQ...................................................................................................1-5
1.3.2 HARQ Types..........................................................................................................................................1-6
1.3.3 HARQ Processing in the Signaling Plane..............................................................................................1-6
1.3.4 HARQ Processing in the User Plane......................................................................................................1-8
1.3.5 HARQ Allocation Algorithm and Buffer Management.........................................................................1-9
1.3.6 Power Control and AMC Processing for HARQ Connections..............................................................1-9
1.4 Implementation of the HARQ Feature............................................................................................................1-9
1.4.1 Activating the HARQ Feature..............................................................................................................1-10
1.4.2 Deactivating the HARQ Feature..........................................................................................................1-11
1.5 Maintenance Information About the HARQ Feature....................................................................................1-11
1.6 Reference Information About the HARQ Feature........................................................................................1-13
2 Multi-Antenna Feature..............................................................................................................2-1
2.1 Overview of the Multi-Antenna Feature.........................................................................................................2-2
2.2 Availability of the Multi-Antenna Feature......................................................................................................2-4
2.3 Functions of the Multi-Antenna Feature.........................................................................................................2-5
2.3.1 Key Multi-Antenna Technologies..........................................................................................................2-5
2.3.2 Strategy of Multi-Antenna Applications................................................................................................2-9
2.4 Implementation of the Multi-Antenna Feature................................................................................................2-9
2.4.1 Activating the Multi-Antenna Feature...................................................................................................2-9
2.4.2 Deactivating the Multi-Antenna Feature..............................................................................................2-14
2.5 Maintenance of the Multi-Antenna Feature..................................................................................................2-15
2.6 Reference Information of the Multi-Antenna Feature...................................................................................2-16
3 Power Control and AMC Feature............................................................................................3-1
3.1 Overview of the Power Control and AMC Feature.........................................................................................3-2
3.2 Availability of the Power Control and AMC Feature.....................................................................................3-4
3.3 Description of the Power Control and AMC Feature......................................................................................3-4
3.4 Implementation of the Power Control and AMC Feature...............................................................................3-7
Issue 01 (2009-03-20) Huawei Proprietary and Confidential i
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Contents Feature Configuration Guide
3.4.1 Activating the Power Control and AMC Feature...................................................................................3-7
3.4.2 Deactivating the Power Control and AMC Feature...............................................................................3-8
3.5 Maintenance Information of the Power Control and AMC Feature................................................................3-8
3.6 Reference Information of the Power Control and AMC Feature....................................................................3-9
4 Idle Mode Feature......................................................................................................................4-1
4.1 Overview of the Idle Mode Feature................................................................................................................4-2
4.2 Availability of the Idle Mode Feature.............................................................................................................4-4
4.3 Description of the Idle Mode Feature.............................................................................................................4-5
4.3.1 Entering Idle Mode.................................................................................................................................4-5
4.3.2 Paging.....................................................................................................................................................4-7
4.3.3 Location Update.....................................................................................................................................4-8
4.3.4 Exiting Idle Mode.................................................................................................................................4-10
4.4 Implementation of the Idle Mode Feature.....................................................................................................4-13
4.4.1 Activating the Idle Mode Feature.........................................................................................................4-13
4.4.2 Deactivating the Idle Mode Feature.....................................................................................................4-13
4.5 Maintenance Information of the Idle Mode Feature.....................................................................................4-14
4.6 Reference Information of the Idle Mode Feature..........................................................................................4-15
5 QoS Feature.................................................................................................................................5-1
5.1 Overview of the QoS Feature..........................................................................................................................5-2
5.2 Availability of the QoS Feature......................................................................................................................5-3
5.3 Description of the QoS Feature.......................................................................................................................5-4
5.3.1 QoS Network Model..............................................................................................................................5-5
5.3.2 QoS Mechanism and Parameters............................................................................................................5-5
5.3.3 QoS Transmission Control...................................................................................................................5-10
5.4 Implementation of the QoS Feature..............................................................................................................5-11
5.4.1 Activation of the QoS Feature..............................................................................................................5-11
5.4.2 Deactivation of the QoS Feature..........................................................................................................5-14
5.5 Maintenance Information of the QoS Feature...............................................................................................5-14
5.6 Reference Information of the QoS Feature...................................................................................................5-15
6 Handover Feature.......................................................................................................................6-1
6.1 Overview of the Handover Feature.................................................................................................................6-2
6.2 Availability of the Handover Feature..............................................................................................................6-3
6.3 Description of the Handover Feature..............................................................................................................6-3
6.4 Implementation of the Handover Feature........................................................................................................6-5
6.4.1 Activating the Handover Feature...........................................................................................................6-5
6.4.2 Deactivating the Handover Feature........................................................................................................6-8
6.5 Maintenance Information of the Handover Feature........................................................................................6-8
6.6 Reference Information of the Handover Feature.............................................................................................6-9
7 Automatic Discovery Feature...................................................................................................7-1
7.1 Overview of the Automatic Discovery Feature...............................................................................................7-2
7.2 Availability of the Automatic Discovery Feature...........................................................................................7-3
ii Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide Contents
7.3 Description of the Automatic Discovery Feature............................................................................................7-4
7.4 Implementation of the Automatic Discovery Feature.....................................................................................7-5
7.4.1 Activating the Automatic Discovery Feature.........................................................................................7-5
7.4.2 Deactivating the Automatic Discovery Feature.....................................................................................7-9
7.5 Maintenance Information of the Automatic Discovery Feature....................................................................7-10
7.6 Reference Information of the Automatic Discovery Feature........................................................................7-10
8 FFR Feature..................................................................................................................................8-1
8.1 Overview of the FFR Feature..........................................................................................................................8-2
8.2 Availability of the FFR Feature......................................................................................................................8-3
8.3 Description of the FFR Feature.......................................................................................................................8-3
8.4 Implementation of the FFR Feature................................................................................................................8-6
8.4.1 Activating the FFR Feature....................................................................................................................8-6
8.4.2 Deactivating the FFR Feature................................................................................................................8-7
8.5 Maintenance Information of the FFR Feature.................................................................................................8-7
8.6 Reference Information of the FFR Feature.....................................................................................................8-7
Issue 01 (2009-03-20) Huawei Proprietary and Confidential iii
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide Figures
Figures
Figure 1-1 SAW hybrid ARQ solution.................................................................................................................1-5
Figure 1-2 Fundamental principles of the HARQ................................................................................................1-6
Figure 1-3 HARQ processing flow chart in the user plane..................................................................................1-8
Figure 2-1 Transmit matrix of Matrix A..............................................................................................................2-5
Figure 2-2 Transmit matrix of Matrix B..............................................................................................................2-6
Figure 2-3 Principle of four-antenna CDD...........................................................................................................2-6
Figure 2-4 CDD transmission mode.....................................................................................................................2-7
Figure 2-5 Transmit matrix of Matrix A..............................................................................................................2-7
Figure 2-6 Transmit matrix of Matrix B..............................................................................................................2-8
Figure 2-7 Principle of uplink CSM.....................................................................................................................2-8
Figure 4-1 Network model of the idle mode feature............................................................................................4-2
Figure 4-2 Idle mode entry initiated by the SS/MS..............................................................................................4-6
Figure 4-3 Idle mode entry initiated by the BS....................................................................................................4-6
Figure 4-4 Paging process....................................................................................................................................4-7
Figure 4-5 Secure location update process...........................................................................................................4-8
Figure 4-6 Insecure location update process........................................................................................................4-9
Figure 4-7 Idle mode exiting after the timer expires..........................................................................................4-11
Figure 4-8 Idle mode exiting before the timer expires.......................................................................................4-12
Figure 5-1 External interfaces of the WiMAX DBS3900....................................................................................5-5
Figure 7-1 DHCP Configuration Tool interface................................................................................................7-9
Figure 8-1 PUSC with all SC(1,3,3) networking mode.......................................................................................8-4
Figure 8-2 PUSC(1,1,3) networking mode..........................................................................................................8-5
Figure 8-3 FFR(1,1,3) networking mode.............................................................................................................8-5
Issue 01 (2009-03-20) Huawei Proprietary and Confidential v
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide Tables
Tables
Table 1-1 Network elements involved in the HARQ feature...............................................................................1-4
Table 1-2 Versions that support the HARQ feature.............................................................................................1-4
Table 1-3 Parameters in the MOD CARRIERBLOCKFLAG command...........................................................1-11
Table 1-4 Parameters in the MOD ULCHANPARA command.........................................................................1-11
Table 1-5 Parameters in the MOD DLCHANPARA command.........................................................................1-12
Table 1-6 Parameters in the MOD OFDMACAPABILITAY command...........................................................1-12
Table 1-7 Parameters in the MOD MACCAPABILITY command...................................................................1-12
Table 1-8 Parameters in the MOD MACCAPABILITY command...................................................................1-13
Table 1-9 Parameters in the MOD RRMSOFT command.................................................................................1-13
Table 2-1 Requirements of the multi-antenna feature for the network elements.................................................2-4
Table 2-2 Versions that support the multi-antenna feature..................................................................................2-5
Table 2-3 Downlink PUSC 1/3 + PUSC 1/3 STC Zone, uplink PUSC 1/3.......................................................2-11
Table 2-4 Downlink PUSC with All + PUSC with All STC zone, uplink PUSC with All................................2-12
Table 2-5 Down link PUSC 1/3 + PUSC 1/3 STC Zone + PUSC with All + PUSC with All STC Zone, uplink
PUSC 1/3 + PUSC with All................................................................................................................................2-12
Table 2-6 Downlink PUSC 1/3 + PUSC 1/3 STC Zone + PUSC with All + PUSC with All STC Zone, uplink PUSC
with All................................................................................................................................................................2-13
Table 2-7 Parameters of the MOD RRMSWITCH command...........................................................................2-14
Table 2-8 Parameters of the MOD RRMSWITCH command...........................................................................2-14
Table 2-9 Parameters of the MOD SECTOR command....................................................................................2-15
Table 2-10 Parameters of the MOD OFDMACAPABILITY command...........................................................2-15
Table 2-11 Parameters of the MOD RRMSWITCH command.........................................................................2-15
Table 2-12 Parameters of the MOD RRMSOFT command...............................................................................2-16
Table 3-1 Network elements involved in the power control and AMC feature...................................................3-4
Table 3-2 Versions that support the power control and AMC feature.................................................................3-4
Table 3-3 Parameters of the MOD RRMSWITCH command.............................................................................3-9
Table 3-4 Parameters of the MOD ULAMCTHRESH command........................................................................3-9
Table 3-5 Parameters of the MMOD ULPERTHRESH command......................................................................3-9
Table 4-1 Network elements involved in the idle mode feature...........................................................................4-4
Table 4-2 Versions that support the idle mode feature.........................................................................................4-5
Table 4-3 Parameters of the MOD MACCAPABILITY command.................................................................4-14
Table 4-4 Parameters of the ADD PAGINGINF command.............................................................................4-14
Table 4-5 Performance measurement items related to the idle mode feature.....................................................4-15
Table 5-1 NEs involved in the QoS feature..........................................................................................................5-4
Issue 01 (2009-03-20) Huawei Proprietary and Confidential vii
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Tables Feature Configuration Guide
Table 5-2 Versions that support the QoS feature.................................................................................................5-4
Table 5-3 QoS scheduling types and corresponding typical services...................................................................5-6
Table 6-1 Network elements involved in the handover feature............................................................................6-3
Table 6-2 Versions that support the handover feature..........................................................................................6-3
Table 6-3 Parameters of the ADD NBR command..............................................................................................6-8
Table 6-4 Parameters of the MOD CARRIERBLOCKFLAG command............................................................6-8
Table 6-5 Parameters of the MOD HOPARA command.....................................................................................6-9
Table 7-1 Network elements involved in the automatic discovery feature..........................................................7-3
Table 7-2 Versions that support the automatic discovery feature........................................................................7-3
Table 7-3 DHCP parameters.................................................................................................................................7-6
Table 7-4 Parameters of the SET DHCPFUNC command.................................................................................7-10
Table 8-1 Requirements of the FFR feature for network elements......................................................................8-3
Table 8-2 Versions that support the FFR feature.................................................................................................8-3
Table 8-3 Parameters of the MOD FFRPARA command....................................................................................8-7
viii Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide About This Document
About This Document
Overview
This document describes the features of the DBS3900 WiMAX in terms of their definitions,
principles, service flows, and implementation.
Product Versions
The following table lists the product versions related to this document.
Product Name Product Version
DBS3900 WiMAX V300R002C02
Intended Audience
This document is intended for:
l Network planning engineers
l System engineers
l Commissioning engineers
l Network operators
Change History
Version Description
01 (2009-03-20) Initial release.
Organization
1 HARQ Feature
This describes the Hybrid Automatic Repeat Request (HARQ), which is a technology that uses
both Forward Error Correction (FEC) and Automatic Repeat Request (ARQ) to improve the
communications reliability.
2 Multi-Antenna Feature
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
About This Document Feature Configuration Guide
This describes the functions, application strategies, and engineering of the multi-antenna
technologies that the Huawei WiMAX products adopt.
3 Power Control and AMC Feature
Power control and AMC algorithms are core algorithms of WiMAX. The MS and BS cooperate
over the R1 interface to achieve power control and AMC.
4 Idle Mode Feature
This describes the basic concepts, functions, and implementation method of the idle mode
feature.
5 QoS Feature
The WiMAX BS can provide users with five different Quality of Service (QoS) levels. Users
need to choose the desired QoS level when subscribing to services.
6 Handover Feature
This describes the handover feature of the WiMAX BS. The WiMAX BS supports hard
handovers, including intra-BS handovers and inter-BS handovers.
7 Automatic Discovery Feature
This describes the automatic discovery feature, which is the application of DHCP in the WiMAX
system.
8 FFR Feature
FFR is an enhanced function of the WiMAX system.
Conventions
Symbol Conventions
The symbols that may be found in this document are defined as follows.
Symbol Description
Indicates a hazard with a high level of risk, which if not
avoided,will result in death or serious injury.
Indicates a hazard with a medium or low level of risk, which
if not avoided, could result in minor or moderate injury.
Indicates a potentially hazardous situation, which if not
avoided,could result in equipment damage, data loss,
performance degradation, or unexpected results.
Indicates a tip that may help you solve a problem or save
time.
Provides additional information to emphasize or supplement
important points of the main text.
General Conventions
2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide About This Document
The general conventions that may be found in this document are defined as follows.
Convention Description
Times New Roman Normal paragraphs are in Times New Roman.
Boldface Names of files, directories, folders, and users are in
boldface. For example, log in as user root.
Italic Book titles are in italics.
Courier New Examples of information displayed on the screen are in
Courier New.
Command Conventions
The command conventions that may be found in this document are defined as follows.
Convention Description
Boldface The keywords of a command line are in boldface.
Italic Command arguments are in italics.
[] Items (keywords or arguments) in brackets [ ] are optional.
{ x | y | ... } Optional items are grouped in braces and separated by
vertical bars. One item is selected.
[ x | y | ... ] Optional items are grouped in brackets and separated by
vertical bars. One item is selected or no item is selected.
{ x | y | ... }* Optional items are grouped in braces and separated by
vertical bars. A minimum of one item or a maximum of all
items can be selected.
[ x | y | ... ]* Optional items are grouped in brackets and separated by
vertical bars. Several items or no item can be selected.
GUI Conventions
The GUI conventions that may be found in this document are defined as follows.
Convention Description
Boldface Buttons, menus, parameters, tabs, window, and dialog titles
are in boldface. For example, click OK.
> Multi-level menus are in boldface and separated by the ">"
signs. For example, choose File > Create > Folder .
Keyboard Operations
The keyboard operations that may be found in this document are defined as follows.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
About This Document Feature Configuration Guide
Format Description
Key Press the key. For example, press Enter and press Tab.
Key 1+Key 2 Press the keys concurrently. For example, pressing Ctrl+Alt
+A means the three keys should be pressed concurrently.
Key 1, Key 2 Press the keys in turn. For example, pressing Alt, A means
the two keys should be pressed in turn.
Mouse Operations
The mouse operations that may be found in this document are defined as follows.
Action Description
Click Select and release the primary mouse button without moving
the pointer.
Double-click Press the primary mouse button twice continuously and
quickly without moving the pointer.
Drag Press and hold the primary mouse button and move the
pointer to a certain position.
4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
1 HARQ Feature
About This Chapter
This describes the Hybrid Automatic Repeat Request (HARQ), which is a technology that uses
both Forward Error Correction (FEC) and Automatic Repeat Request (ARQ) to improve the
communications reliability.
1.1 Overview of the HARQ Feature
This provides an overview of the HARQ feature. In an adverse radio channel environment, the
HARQ technology enables the system to adapt to channel fading and rapid interference
environment change, hence, effectively decreasing the error rate in data transmission.
1.2 Availability of the HARQ Feature
This describes the network elements involved in and version information about the HARQ
feature.
1.3 Description of the HARQ Feature
This describes the fundamental principles of HARQ. To understand the HARQ feature, you need
to know how HARQ works. The HARQ feature is a hybrid ARQ solution that enables
retransmission of error data to decrease the impact of error bits on ongoing services.
1.4 Implementation of the HARQ Feature
This describes how to activate and deactivate the HARQ feature.
1.5 Maintenance Information About the HARQ Feature
This describes the parameters and performance measurement items related to the HARQ feature.
1.6 Reference Information About the HARQ Feature
The HARQ feature complies with the IEEE 802.16e standard.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
1.1 Overview of the HARQ Feature
This provides an overview of the HARQ feature. In an adverse radio channel environment, the
HARQ technology enables the system to adapt to channel fading and rapid interference
environment change, hence, effectively decreasing the error rate in data transmission.
Definition
HARQ is a PHY/MAC-layer technology that uses both hybrid ARQ and forward error correction
(FEC).
After HARQ is enabled, the transmitter decides whether to retransmit a data packet according
to the received ACK or NACK message from the receiver. If data retransmission is required,
the receiver combines the data packet with the previously received packet and then retransmits
the data packet for error correction decoding.
Through data retransmission, the receiver can obtain the time diversity gain, coding gain, and
power gain to enhance the decoding performance and spectrum efficiency and intensify coverage
effect.
Purpose
Featuring the advantages of both FEC and ARQ, HARQ is aimed at improving quality and
reliability in signal transmission. In an adverse radio environment, HARQ can reduce the
impaction of channel fading and interference fluctuation, thereby achieving high system gains,
lowering the BER, and improving data transmission performance.
Specification
The Huawei specifications of the HARQ feature are described as follows:
l The UL HARQ delay and DL HARQ delay can be four frames.
l A maximum of 16 HARQ channels can be allocated to each DL subscriber and each UL
subscriber. The supported highest HARQ capability set is HARQ set 3.
l A DL single-subscriber frame supports a maximum of four subbursts, and an UL single-
subscriber frame supports a maximum of three subbursts.
Influence
l HARQ improves spectrum efficiency and enhances coverage.
l The data retransmission and combination during HARQ increase transmission delay to a
small extent.
l Relation between the HARQ feature and other features:
– The HARQ feature is related to power control and AMC feature. HARQ and AMC are
used together to combat the fading of radio channels and time-variable interference.
AMC provides rough and slow adaptive control within a large dynamic range. HARQ
provides precise and fast adaptive control within a small dynamic range.
– The HARQ feature is related to the QoS feature. During service establishment, the BS
decides whether HARQ is enabled for a connection according to the service flow
parameter for QoS feature.
1-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
Term
Term Definition
Stop-and-wait The transmitter processes another data block only after the previously
mechanism transmitted data block is correctly received.
Retransmission For an incorrect data block, the transmitter retransmits the check bits
first. If error occurs again, the transmitter retransmits the entire data
block.
Chase combing The transmitter transmits system information and redundancy
information, and the receiver corrects errors in the data packet. If any
error bit fails to be corrected, the receiver sends a packet requesting
retransmission from the transmitter. Then, the transmitter uses the same
error correction code and includes the same redundancy information in
the retransmitted packet as that the previously packet uses and includes.
After receiving an error packet, the receiver does not discard the error
packet, but directly decodes the retransmitted code words or combines
the retransmitted code words with buffered code words, and then
decodes them.
Incremental The data transmitted by the sending send for the first time contains
Redundancy system information and some redundancy information. The
retransmitted data, however, does not contain system information bit
except new redundancy information. After the receiver receives an error
packet, it does not discard the error packet but combines the error packet
with the retransmitted redundancy information and then decodes the
combined information.
Abbreviations and Acronyms
Abbreviations
and Acronyms Full Spelling
ARQ Automatic Retransmission Request
AMC Automatic Modulation Control
BS Base Station
CC Chase Combining
CTC Convolutional Turbo Code
DSA/DSC Dynamic Service Addition/Chang
FEC Forward Error Correction
HARQ Hybrid Automatic Retransmission Request
IR Incremental Redundancy
MAC Medium Access Control
MS Mobile Station
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
Abbreviations
and Acronyms Full Spelling
PDU Protocol Data Unit
SAW Stop And Wait
SS Subscriber Station
1.2 Availability of the HARQ Feature
This describes the network elements involved in and version information about the HARQ
feature.
Network Element Involved
The HARQ feature requires the coordination of the SS/MS, BS, and M2000. Table 1-1 lists the
network elements involved in the HARQ feature.
Table 1-1 Network elements involved in the HARQ feature
AAA DHCP
SS/MS BS ASN-GW Server Server M2000
√ √ - - - √
NOTE
In Table 1-1, √ is used to mark network elements that are involved in the HARQ feature, and - is used to
mark network elements that are not involved in the HARQ feature.
Supporting Versions
Table 1-2 lists the versions that support the HARQ feature.
Table 1-2 Versions that support the HARQ feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Support
This feature does not require the license support.
1.3 Description of the HARQ Feature
This describes the fundamental principles of HARQ. To understand the HARQ feature, you need
to know how HARQ works. The HARQ feature is a hybrid ARQ solution that enables
retransmission of error data to decrease the impact of error bits on ongoing services.
In the IEEE 802.16 standard, two types of HARQs are defined: CC-HARQ and IR-HARQ. As
defined in Mobile System Profile Release 1.0, the base station must support the CC-HARQ
1-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
feature that uses Convolutional Turbo Code (CTC) coding and need not support the IR-HARQ
feature. Hence, this document describes mainly the functions and working principles of the CC-
HARQ feature.
The CC-HARQ feature involves the processing for network access and service establishment in
the signaling plane, processing for the UL and DL HARQ in the user plane, HARQ allocation
management, and buffer management.
1.3.1 Fundamental Principles of the HARQ
The HARQ feature defined by IEEE 802.16 standard is applied to air interface links of the base
station and mobile station (MS). In fact, it is a Stop-and-Wait (SAW) hybrid ARQ solution.
1.3.2 HARQ Types
In the IEEE 802.16 standard, two types of HARQs are defined: CC-HARQ and IR-HARQ.
1.3.3 HARQ Processing in the Signaling Plane
HARQ processing in the signaling plane involves the initial network entry of the MS, handover,
idle-mode network reentry, location update, and service flow establishment.
1.3.4 HARQ Processing in the User Plane
The BS performs HARQ processing in the user plane on the PHY layer and MAC layer.
1.3.5 HARQ Allocation Algorithm and Buffer Management
1.3.6 Power Control and AMC Processing for HARQ Connections
1.3.1 Fundamental Principles of the HARQ
The HARQ feature defined by IEEE 802.16 standard is applied to air interface links of the base
station and mobile station (MS). In fact, it is a Stop-and-Wait (SAW) hybrid ARQ solution.
After a transmitter sends a packet to the receiver, it sends the next packet only when it receives
the ACK message from the receiver. If the transmitter fails to receive the ACK message, it
retransmits the packet that fails to be received, as shown in Figure 1-1.
Figure 1-1 SAW hybrid ARQ solution
Both the UL and DL over the R1 interface of the WiMAX network support the HARQ. DL
HARQ: After a base station (BS) sends a HARQ data packet, the MS responds with the ACK
or NACK message based on whether the correct data packet is received. UL HARQ: After an
MS sends an HARQ data packet, the BS decides whether to retransmit according whether the
UL decoding is correct.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
HARQ enables selective retransmission of error data to decrease the impact of error codes over
the channel on services. Figure 1-1 shows how HARQ is implemented at the base station side
(the HARQ implementation at the MS side is similar).
Figure 1-2 Fundamental principles of the HARQ
1.3.2 HARQ Types
In the IEEE 802.16 standard, two types of HARQs are defined: CC-HARQ and IR-HARQ.
When the CC-HARQ is adopted and data retransmission is required, the transmitter uses the
same modulation and coding (MC) mode to retransmit the burst. After the receiver receives the
data, it combines the data with its previously received one to raise the Signal Noise Ratio (SNR)
before decoding, hence, increasing the probability of correct decoding.
When the IR-HARQ is adopt and data retransmission is required, the transmitter can use different
MC mode and can add redundancy information different from previous one to the error
correction (EC) block for data retransmission. After the receiver receives the data, it combines
the data with its previously received one to raise the SNR or adds redundancy information to
the decoding code, hence, increasing the probability of correct decoding. The IR-HARQ feature
performance is slightly better than the CC-HARQ feature performance but requires higher
hardware capability.
According to the WiMAX Forum Mobile System Profile Release 1.0, the base station must
support the CC-HARQ feature that uses Convolutional Turbo Code (CTC) coding and need not
support the IR-HARQ feature.
1.3.3 HARQ Processing in the Signaling Plane
HARQ processing in the signaling plane involves the initial network entry of the MS, handover,
idle-mode network reentry, location update, and service flow establishment.
The HARQ parameter renegotiation procedures during MS handover, idle-mode network
reentry, and location update are similar to that during the initial network entry of the MS. The
following describes the HARQ parameter negotiation procedure during the initial network entry
of the MS.
1. HARQ parameter configuration during sector carrier establishment
The HARQ related parameter configuration at the BS side is performed on the M2000 or
Web LMT. The HARQ parameter configuration procedure is described as follows:
1-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
(1) On the M2000 or Web LMT, configure the OFDMA support capability parameter of
the BS. This parameter indicates the HARQ support capability of the BS. The HARQ
related OFDMA support capability parameters are:
l Demodulation Mode: The BIT#4 (the fifth bit from the least significant bit to the
most significant bit) set to 1 is one of the prerequisites for enabling the HARQ.
When the BIT#4 is set to 0, HARQ is disabled.
l Modulation Mode: The BIT#5 (the sixth bit from the least significant bit to the
most significant bit) set to 1 is one of the prerequisites for enabling the HARQ.
When the BIT#5 is set to 0, HARQ is disabled.
l Uplink Control Support: HARQ retransmission requires the UL ACK channel
to transmit the DL ACK or NACK message. The BIT#2 (the third bit from the
least significant bit to the most significant bit) set to 1 indicates supporting the UL
ACK channel and enabling the HARQ. When the BIT#2 is set to 0, HARQ is
disabled.
(2) During sector carrier establishment, the BS decides whether to enable the HARQ
function according to the HARQ capability parameters and records the decision for
the sector. The result is used during the network entry negotiation of the MS.
2. SBC processing procedure during the initial network entry of the MS
During the initial network entry of the MS, whether the BS supports the HARQ function
is negotiated through the SS basic capability (SBC) processing procedure. The SBC
processing procedure is described as follows:
(1) The MS initiates the SBC processing procedure to negotiate whether to support the
HARQ function by sending a message to the BS.
(2) The BS negotiates with the MS on whether to support the HARQ parameters HARQ
Buffer Capability, Number of UL/DL HARQ Channels, and Maximum Number
Of Bursts Per Frame Capability In HARQ according to the HARQ Chase indicator
bit in parameters Modulation Mode and Demodulation Mode. Through negotiation,
the BS decides whether to enable HARQ for a connection, the number of HARQ
channels to be used, and whether to enable the PDU SN subheader in MAC Header
and Extended Subhead Support.
l HARQ Buffer Capability: The value of this parameter indicates the maximum
size of buffer that a sub-burst can occupy. The value of this parameter impacts the
transmission rate of the MS that enables the HARQ function.
l Number of UL/DL HARQ Channels: The value of this parameter needs to be
negotiated between the BS and the MS and set to the smallest value supported by
the BS and the MS. The value of this parameter and the value of HARQ Buffer
Capability together determine the peak rate of the MS that enables the HARQ.
l Maximum Number Of Bursts Per Frame Capability In HARQ: The value of
this parameter indicates the maximum number of bursts in each frame supported
by the HARQ. The value of this parameter impacts the number of MSs that a frame
can process synchronously.
(3) The BS saves the negotiation result. The DSA processing procedure during service
establishment is started.
3. DSA processing procedure during service establishment
During the service establishment, whether the BS supports the HARQ function is negotiated
through the Dynamic Service Addition (DSA) procedure. The DSA processing procedure
is described as follows:
(1) The BS decides whether to enable HARQ according to MS service flow QoS
parameters, negotiated Number of UL/DL HARQ Channels and HARQ Buffer
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
Capability supported by the MS during SBC processing procedure, and service flow
delay threshold of the BS.
(2) The BS saves related negotiation parameters and sets up the HARQ connection
according to the negotiation parameters.
1.3.4 HARQ Processing in the User Plane
The BS performs HARQ processing in the user plane on the PHY layer and MAC layer.
Figure 1-3 shows the HARQ processing flow chart in the user plane.
Figure 1-3 HARQ processing flow chart in the user plane
The HARQ processing in the user plane is classified into DL processing in the user plane and
UL processing in the user plane.
1. HARQ DL processing in the user plane
As shown in Figure 1-3, the BS packs, fragments, and then assembles the data packets
from the classifier into a subburst, adds the CRC16 code, performs coding and modulation,
and then sends the subburst to the MS.
After an HARQ ACK Delay for DL Burst, the MS responds with an ACK or NACK
message through the ACK channel. The BS demodulates the message on the ACK channel,
and then performs HARQ allocation according to the demodulation result.
HARQ ACK Delay for DL Burst: It indicates the time an MS takes to responds with an
ACK or NACK message after receiving a sub-burst. The value of this parameter impacts
data transmission performance and system overhead over the air interface.
1-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
2. HARQ UL processing in the user plane
During UL processing in the user plane, the MS sends HARQ data according to the MAP
message sent by the BS. Then, the BS demodulates UL data. If the BS receives HARQ data
for the first time, its demodulation module decodes the data. If the BS receives the
retransmitted HARQ data, it combines the retransmitted data with the previously received
one and overwrites the original data in the buffer. Then, the decoding module performs
data decoding. The BS decides whether to allocate related resources for the retransmission
of the next frame of HARQ data according to the decoding result.
1.3.5 HARQ Allocation Algorithm and Buffer Management
The HARQ allocation algorithm and buffer management are performed on the PHY layer and
MAC layer of the BS.
l The PHY layer supports fast ACK channel demodulation and UL buffer management.
l The MAC layer supports HARQ burst allocation and DL buffer management.
The BS uses the HARQ ACK Delay for DL Burst parameter in the UCD message to define
how soon an MS responds with an ACK or NACK message after receiving a DL sub-burst.
The BS performs fast ACK channel demodulation for the ACK or NACK message received
from the MS, performs HARQ allocation according to the demodulation result and
retransmission times, and decides whether to empty the buffer corresponding to the DL HARQ
subchannel.
1.3.6 Power Control and AMC Processing for HARQ Connections
AMC Processing for the DL HARQ
The BS supports AMC processing for the DL HARQ, including the DL AMC processing for an
MS that uses both HARQ connections and non-HARQ connections. The demodulation
thresholds of HARQ and non-HARQ connections are different. Therefore, different AMC outer-
loop thresholds are used.
The MAC layer selects the DL MC mode for the HARQ connection according to the DL outer-
loop threshold and the CINR measured by the MS.
Power Control and AMC Processing for the UL HARQ
The BS supports power control and AMC processing for the UL HARQ, including UL power
control and AMC processing for an MS that uses both DL HARQ links and non-HARQ links.
The MAC layer periodically adjusts the UL outer-loop threshold for enabling an HARQ
connection according to the CRC16 result on the PHY layer.
The MAC layer selects the UL MC mode and calculates the UL power control result for the
HARQ connection according to the UL outer-loop threshold and the CINR and RSSI
measurement result on the PHY layer.
1.4 Implementation of the HARQ Feature
This describes how to activate and deactivate the HARQ feature.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
1.4.1 Activating the HARQ Feature
This describes how to activate the HARQ feature. On the M2000 or Web LMT, you can perform
related configurations for the BS to activate the HARQ feature.
1.4.2 Deactivating the HARQ Feature
This describes how to deactivate the HARQ feature. You can deactivate the HARQ feature by
setting demodulation mode parameter BIT#5 and modulation mode parameter BIT#4 to 0.
1.4.1 Activating the HARQ Feature
This describes how to activate the HARQ feature. On the M2000 or Web LMT, you can perform
related configurations for the BS to activate the HARQ feature.
Context
The HARQ parameter configuration at the BS side is as follows:
NOTE
Before performing the HARQ parameter configuration at the BS side, ensure that the sector carrier is in
deactivate state. Step 2 to step 6 of the following configuration steps are not in a particular sequence.
Procedure
Step 1 Run MOD CARRIERBLOCKFLAG to deactivate the sector carrier.
For example,
MOD CARRIERBLOCKFLAG: SECTORID=0, CARRIERID=0, BLOCKFLAG=Blocked;
Step 2 Run MOD OFDMACAPABILITY to enable the HARQ UL/DL modulation mode,
demodulation mode, MAP capability, and UL ACK channel support. Modulation mode enabled
(BIT#4 set to 1) and demodulation mode enabled (BIT#5 set to 1) are the prerequisites for
enabling the HARQ.
For example,
MOD OFDMACAPABILITY: SECTORID=0, CARRIERID=0, DEMODULATION=37, MODULATION=20,
ULCTRLSUPP=4, OFDMAMAPCAP=6;
Step 3 Run MOD MACCAPABILITY to enable the BS to support the PDU SN extended subheader,
to set the BS-supported HARQ buffer size (5140 bits are recommended), and to set the HARQ-
supported maximum number of subbursts (65 is recommended) in a frame.
For example,
MOD MACCAPABILITY: SECTORID=0, CARRIERID=0, HEADERTYPESUPP=327647, EXTCAP=1,
HARQCHASEBUFCAP=5140, MAXBURINHARQ=65;
Step 4 Run MOD ULCHANPARA and MOD DLCHANPARA to configure the UL/DL HARQ
maximum retransmission times and HARQ DL ACK delay.。
For example,
MOD ULCHANPARA: SECTORID=0, CARRIERID=0, HARQDELAYFORDLBURST=1, ULHARQMAXRETRAN=4;
MOD DLCHANPARA: SECTORID=0, CARRIERID=0, DLMAXHARQRETRAN=4;
Step 5 Run MOD RRMSOFT to enable the service flow priority threshold and service flow delay
threshold at the BS side. HARQ can be enabled for the service flow only when the previous two
thresholds are smaller than those thresholds in the QoS parameters set for the MS.
For example,
MOD RRMSOFT: PARANO=21, VALUE=0;
MOD RRMSOFT: PARANO=22, VALUE=8;
1-10 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
Step 6 Run MOD RRMSOFT to configure the UL public-area mode of the BS. The UL public-area
supports five modes (mode 0 to mode 4). Where, mode 3 does not support UL HARQ ACK
channels. Therefore, to enable the HARQ, do not configure mode 3.
For example,
MOD RRMSOFT: PARANO=5, VALUE=4;
Step 7 Run MOD CARRIERBLOCKFLAG to activate the sector carrier.
For example,
MOD CARRIERBLOCKFLAG: SECTORID=0, CARRIERID=0, BLOCKFLAG=Unblocked;
----End
1.4.2 Deactivating the HARQ Feature
This describes how to deactivate the HARQ feature. You can deactivate the HARQ feature by
setting demodulation mode parameter BIT#5 and modulation mode parameter BIT#4 to 0.
Procedure
Run MOD OFDMACAPABILITY to set demodulation mode parameter BIT#5 and
modulation mode BIT#4 to 0 to deactivate the HARQ feature.
For example,
MOD OFDMACAPABILITY: SECTORID=0, CARRIERID=0,
DEMODULATION=5,MODULATION=4,ULCTRLSUPP=2,OFDMAMAPCAP=6;
----End
1.5 Maintenance Information About the HARQ Feature
This describes the parameters and performance measurement items related to the HARQ feature.
Related Parameters
Table 1-3, Table 1-4, Table 1-5, Table 1-6, Table 1-7, Table 1-8 and Table 1-9 list the
parameters related to the HARQ feature.
Table 1-3 Parameters in the MOD CARRIERBLOCKFLAG command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
BLOCKFLAG Block flag
Table 1-4 Parameters in the MOD ULCHANPARA command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-11
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
1 HARQ Feature Feature Configuration Guide
Parameter Meaning
HARQDELAYFORDLBURST HARQ delay frames for the downlink burst
ULHARQMAXRETRAN Maximum retransmission times of the uplink
HARQ
Table 1-5 Parameters in the MOD DLCHANPARA command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
HARQACKDELAYFORULBURST HARQ ACK delay frames for uplink BURST
DLMAXHARQRETRAN Maximum retransmission times of downlink
HARQ
Table 1-6 Parameters in the MOD OFDMACAPABILITAY command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
DEMODULATION Demodulation mode
MODULATION Modulation mode
ULCTRLSUPP Uplink control support
OFDMAMAPCAP OFDMA MAP capability
Table 1-7 Parameters in the MOD MACCAPABILITY command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
HEADERTYPESUPP MAC header and extended subheader support
HARQCHASEBUFCAP HARQ chase combining and buffer
capability
EXTCAP Extended subheader capability
MAXBURINHARQ Maximum number of burst per frame
capability in HARQ
1-12 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 1 HARQ Feature
Table 1-8 Parameters in the MOD MACCAPABILITY command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
HEADERTYPESUPP MAC header and extended subheader support
HARQCHASEBUFCAP HARQ chase combining and buffer
capability
EXTCAP Extended subheader capability
MAXBURINHARQ Maximum number of burst per frame
capability in HARQ
Table 1-9 Parameters in the MOD RRMSOFT command
Parameter Meaning
PARANO Software parameter number
Related Performance Measurement Items
The related performance measurement items related to the HARQ feature are as follows:
l HARQ RETRANSMISSION TIMES
l HARQ TOTAL TRANSMISSION TIMES
1.6 Reference Information About the HARQ Feature
The HARQ feature complies with the IEEE 802.16e standard.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 1-13
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
2 Multi-Antenna Feature
About This Chapter
This describes the functions, application strategies, and engineering of the multi-antenna
technologies that the Huawei WiMAX products adopt.
2.1 Overview of the Multi-Antenna Feature
Multi-antenna is a technology that uses multiple antennas at the transmitter and receiver. Multi-
antenna systems can be categorized into single input multiple output (SIMO) diversity, multiple
input single output (MISO) diversity, and multiple input multiple output (MIMO) diversity. All
these systems are called the MIMO systems.
2.2 Availability of the Multi-Antenna Feature
This describes the license and version information about the multi-antenna feature and the
involved network elements.
2.3 Functions of the Multi-Antenna Feature
This describes the principles and application strategy of the key multi-antenna technologies.
2.4 Implementation of the Multi-Antenna Feature
This describes how to activate and deactivate the multi-antenna feature.
2.5 Maintenance of the Multi-Antenna Feature
This describes the parameters and performance counters related to the multi-antenna feature.
2.6 Reference Information of the Multi-Antenna Feature
The multi-antenna feature complies with the IEEE 802.16e standard.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
2.1 Overview of the Multi-Antenna Feature
Multi-antenna is a technology that uses multiple antennas at the transmitter and receiver. Multi-
antenna systems can be categorized into single input multiple output (SIMO) diversity, multiple
input single output (MISO) diversity, and multiple input multiple output (MIMO) diversity. All
these systems are called the MIMO systems.
Definition
The IEEE 802.16e system supports multiple multi-antenna technologies, including downlink
transmitter diversity (such as Matrix A and CDD), space division multiplexing (such as Matrix
B), and uplink multi-antenna receiver (MRC), and uplink collaborative MIMO (collaborate
spatial multiplex: CSM).
l If the BS uses two transmit antennas, two-antenna Matrix A or Matrix B transmission can
be adopted. For common channels like the Preamble, two-antenna CDD transmission can
be adopted.
l If the BS uses four transmit antennas, Matrix A+CDD or Matrix B+CDD transmission can
be adopted. For common channels like the Preamble, four-antenna CDD transmission can
be adopted.
l If the terminal supports demodulation under Matrix A or Matrix B, the BS transmits signals
to the terminal in these two MIMO modes.
The multi-antenna technologies are defined as follows:
l Downlink transmitter diversity: The BS uses multiple antennas for transmission. Signals
are processed (such as STC) by the transmitter and then sent through multiple antennas.
Using transmitter diversity can achieve diversity gain and power gain from multi-antenna
transmission.
l Downlink space division multiplexing: Different streams are transmitted through the same
time and frequency resources. These streams are identified with their antennas. Using space
division multiplexing can achieve multiplexing gain.
l Uplink multi-antenna receiver: Also called diversity receive, the most frequently used
signal receive mode in mobile communication systems. The BS receives data from different
antennas and combines them to cancel the fading effect. Through diversity receiving, array
gain and diversity gain can be obtained.
l Uplink CSM: A transmit mode in which multiple SSs, which are identified with their
transmitter antennas, use the same time and frequency resources. Using this technology
can achieve multiplexing gain.
Purpose
The multi-antenna technology can help significantly increase the system capacity or expand the
coverage so that the spectrum resources can be fully used or the number of sites can be reduced.
With this technology, the customers can reduce the CAPEX for the WiMAX market and protect
their investment, thus bringing better service experience to their subscribers.
Specifications
System peak throughput:
2-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
l Under the configuration of 4T4R, the peak downlink throughput in each sector carrier is
45 Mbit/s. Conditions: 10 MHz bandwidth, PUSC/all sc, and 35:12 subframe ratio.
l Under the configuration of 4T4R, the peak uplink throughput in each sector carrier is 10
Mbit/s. Conditions: 10 MHz bandwidth, PUSC/all sc, and 26:21 subframe ratio.
Impact
Multi-antenna technologies do not affect each other. When used together with other features,
the multi-antenna feature has the following impact on the system.
Two-antenna Matrix A and two-antenna Matrix B:
l On the signaling system: The system must support the MAP format of MIMO.
l On Zone management: The system must support the allocation and management of the STC
Zone.
Four-antenna Matrix A + CDD and four-antenna Matrix B + CDD:
l On the signaling system: The system must support the MAP format of MIMO.
l On Zone management: The system must support the allocation and management of the STC
Zone.
Term
Term Definition
Throughput Throughput is the maximum transmission rate that a measured object
can reach. The measured object may be a system, a piece of equipment,
a connection, or a service type. Throughput can be measured by
bandwidth.
Space-time Space-time coding (STC) is a signal coding technology that can be used
coding to obtain enhanced data transmission rates. It combines the space
transmitted signals and time transmitted signals. In essence, it is a two-
dimension (space dimension and time dimension) processing method. In
a new-generation communication system, space diversity achieved
through multiple transmit and receive antennas raises the system
capacity and information rate. Meanwhile, different signals are
transmitted in different timeslots by the same antenna, and therefore
receive diversity can be implemented at the receiver. In this way,
diversity and coding gains are obtained to achieve high-speed
transmission. This technology is used in 3G communication systems to
increase spectrum utilization.
mTnR The BS or SS have m transmit antennas and n receive antennas.
m*n The uplink or downlink links have m transmit antennas and n receive
antennas.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
Abbreviations and Acronyms
Abbreviations
and Acronyms Expansion
MS Mobile Station
CSM Collaborative Spatial Multiplexing
CDD Cyclic Delay Diversity
MIMO Multi-In Multi-Out
OFDM Orthogonal Frequency Division Multiplex
OFDMA Orthogonal Frequency Division Multiple Access
SS Subscriber Station
MAC Medium Access Control
BS Base Station
STC Space Time Coding
MRC Maximum Ratio Combining
2.2 Availability of the Multi-Antenna Feature
This describes the license and version information about the multi-antenna feature and the
involved network elements.
Network Element Involved
The multi-antenna feature requires the interoperation between the SS/MS and the BS. Table
2-1 lists the network elements involved.
Table 2-1 Requirements of the multi-antenna feature for the network elements
ASN AAA DHCP
SS/MS BS -GW Server Server M2000
√ √ - - - √
NOTE
In Table 2-1, √ is used to mark network elements that must meet specific requirements, and - is used to
mark network elements that do not have to meet specific requirements.
Supporting Versions
Table 2-2 lists the versions that support the multi-antenna feature.
2-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
Table 2-2 Versions that support the multi-antenna feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Support
To use this feature, you need to apply for a license that supports it.
2.3 Functions of the Multi-Antenna Feature
This describes the principles and application strategy of the key multi-antenna technologies.
2.3.1 Key Multi-Antenna Technologies
The major multi-antenna application is based on the MIMO + CDD transmit mode and MRC/
CSM receive mode.
2.3.2 Strategy of Multi-Antenna Applications
This describes the strategy of multi-antenna applications supported by the current Huawei
WiMAX BSs.
2.3.1 Key Multi-Antenna Technologies
The major multi-antenna application is based on the MIMO + CDD transmit mode and MRC/
CSM receive mode.
Downlink MIMO
Downlink MIMO is a multi-antenna open-loop technology in which multiple antennas are used
to transmit signals without knowing downlink channel condition. The WiMAX system profile
defines that the major downlink MIMO technologies are Matrix A and Matrix B, which features
vertical coding.
In Matrix A, the two links of transmitted signals are content-related. Under the impact (reflection
and refraction) of physical space environment, a transmitted signal is dispersed into multiple
signals with different phases. In optimum conditions, two receiving signals may be combined
into one signal with the power doubled. In this way, the receiving diversity can increase by 3
dB to enhance the system coverage. Figure 2-1 shows the transmit matrix of Matrix A.
Figure 2-1 Transmit matrix of Matrix A
In the scenario of Matrix A transmission, the recommended number of receive antennas at the
receiver side is two or more. Although only one antenna can also demodulate data, such
configuration is not recommended because the performance is poor.
Matrix B: Different streams are transmitted through two antennas over the same time and
frequency resources. Figure 2-2 shows the transmit matrix of Matrix B.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
Figure 2-2 Transmit matrix of Matrix B
In the scenario of Matrix B transmission, the receiver must be equipped with two or more receive
antennas to demodulate data because it must separate the two streams using the same resources.
Matrix B cannot provide diversity gain. Instead, it brings space multiplexing diversity because
two streams use the same time and frequency resources. The performance of Matrix B can be
ensured when the signal-to-noise ratio is high and the channels of the two channels of the two
streams must be uncorrelated.
The system can perform self-adaptive switching between Matrix A and Matrix B through the
adaptive MIMO switching (AMS) algorithm, which helps maximize the spectrum gain.
Downlink CDD
CDD is implemented through the transmission of data duplicate with different delays through
different antennas. This technology can provide diversity gain and improve performance. The
IEEE 802.16e standard specifies that the downlink preambles and the first downlink zone cannot
use STC coding. However, the CDD can be used to improve the demodulation performance of
the common channel, thus improving the coverage of common channels. With the CDD
technology, the power gain can be obtained from multi-antenna transmission. In the scenario of
channel fading, this technology can even bring a small amount of diversity gain. In the scenario
of LOS, no diversity gain can be obtained.
Figure 2-3 shows principle of CDD.
Figure 2-3 Principle of four-antenna CDD
Downlink MIMO + CDD
For downlink non-STC Zone, CDD can be used to obtain diversity gain. The CDD technology
can logically combine multiple physical antennas into a virtual antenna, thus realizing four-
antenna downlink MIMO, that is, Matrix A + CDD and Matrix B + CDD.
There are two modes of four-antenna downlink transmission.
2-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
1. The Preamble and data on common channels are transmitted in CDD mode. Figure 2-4
shows the transmission mode.
Figure 2-4 CDD transmission mode
2. Transmission mode of traffic channel. On the traffic channel, the four-antenna MIMO +
CDD transmission mode is Matrix A+CDD/Matrix B+CDD self-adaptive switching.
l Figure 2-5 shows the mapping between the Matrix A + CDD baseband data and antenna.
l Figure 2-6 shows the mapping between the Matrix B + CDD baseband data and antenna.
Figure 2-5 Transmit matrix of Matrix A
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
Figure 2-6 Transmit matrix of Matrix B
Uplink Multi-Antenna Technologies
There are two uplink multi-antenna technologies.
1. Uplink diversity receiving. Uplink receive diversity is the most commonly used multi-
antenna technology. The BTS performs coherent combination for the signals received by
multiple antennas. In this way, array gains and four-way receiver diversity are obtained.
The receive algorithm is maximum ratio combining (MRC). In MRC, coherent combination
is performed for the signals received by multiple antennas. Through MRC, array gains and
diversity gains can be obtained.
2. Uplink CSM. In uplink CSM, the terminals of two transmit-only antennas are fixed to the
same time or frequency resources. The BS uses multiple antennas to receive signals, thus
distinguishing between subscribers and improving uplink capacity. Figure 2-7 shows
principle of uplink CSM.
Figure 2-7 Principle of uplink CSM
2-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
2.3.2 Strategy of Multi-Antenna Applications
This describes the strategy of multi-antenna applications supported by the current Huawei
WiMAX BSs.
With the MIMO License, the BS uses MIMO transmission by default regardless of the multi-
antenna transmission configuration.
l If the SS does not support MIMO or the downlink transmission is on a non-STC Zone,
CDD is used. The system reserve a Zone dedicated for this transmission mode. The SSs in
this Zone automatically use CDD mode to transmit data.
l If the MS supports Matrix A and Matrix B, the system determines to MIMO mode to be
used according to the channel environment. The switching between Matrix A and Matrix
B is performed automatically.
The performance of a four-antenna system varies with the scenario.
l If the scenario is sensitivity-limited, the four-antenna configuration can significantly
improve the performance.
l If the scenario is interference-limited, the four-antenna configuration contributes little in
performance improvement.
2.4 Implementation of the Multi-Antenna Feature
This describes how to activate and deactivate the multi-antenna feature.
2.4.1 Activating the Multi-Antenna Feature
This describes how to activate the MIMO feature and the CSM function.
2.4.2 Deactivating the Multi-Antenna Feature
This describes how to deactivate the multi-carrier feature and the CSM function.
2.4.1 Activating the Multi-Antenna Feature
This describes how to activate the MIMO feature and the CSM function.
Prerequisite
l The M2000 has issued the License to the NE.
l The basic configurations related to sector carriers have been implemented.
Context
l You can set the parameters through the background maintenance tool Web LMT or the
M2000.
l The parameters used in steps 2–6 and step 8 can be changed only during the deactivation
of sector carriers. The changes take effect after the sector carriers are activated again.
Procedure
Step 1 Query and set the License information.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
1. Run the LST CARRIERLICENSEINFO command to query the information about the
License of a carrier.
Example:
LST CARRIERLICENSEINFO: SECTORID=0, CARRIERID=0;
2. Run the MOD CARRIERLICENSEINFO command to set the four-antenna MIMO
control parameters for a carrier.
Example:
MOD CARRIERLICENSEINFO: SECTORID=0, CARRIERID=0, FOURANTENNAMIMO=1;
Step 2 Query and set the numbers of transmit antennas and receive antennas of a BS.
1. Run the LST SECTOR command to query the numbers of the transmit antennas and
receive antennas of a sector.
Example:
LST SECTOR: SECTORID=0;
2. Run the MOD SECTOR command to set the numbers of the transmit antennas and receive
antennas of a sector.
Example:
MOD SECTOR: SECTORID=0, TXANTNUM=4, RXANTNUM=4;
NOTE
The values of TXANTNUM and RXANTNUM are both 4.
Step 3 Query and set the antenna mode of a BS.
1. Run the LST CARRIERBASICINFO command to query the antenna mode of a sector
carrier.
Example:
LST CARRIERBASICINFO: SECTORID=0, CARRIERID=0;
2. Run the MOD CARRIERBASICINFO command to set the antenna mode of a sector
carrier.
Example:
MOD CARRIERBASICINFO: SECTORID=0, CARRIERID=0, ANTBITMAP=2;
NOTE
The value range of ANTBITMAP is 0–2. 0 means using the antennas A and B of a 4T4R RRU to set
up a 2T2R configuration. 1 means using the antennas C and D of a 4T4R RRU to set up a 2T2R
configuration. 2 means using the antennas A, B, C, and D of a 4T4R RRU to set up a 4T4R
configuration.
Step 4 Query and set the iCSD switch.
1. Run the LST RRMSOFT command to query the iCSD switch.
Example:
LST RRMSOFT: PARANO=47;
2. Run the MOD RRMSOFT command to set software parameter 47 to 1.
Example:
MOD RRMSOFT: PARANO=47, VALUE=1;
NOTE
Software parameter 47 is the iCSD switch. 0 means disable, and 1 means enable.
Step 5 Query and set the SBC negotiation capability.
1. Run the LST OFDMACAPABILITY command to query the BS's capability in MIMO
negotiation.
Example:
2-10 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
LST OFDMACAPABILITY: SECTORID=0, CARRIERID=0;
2. Run the MOD OFDMACAPABILITY command to set the BS's capability in MIMO
negotiation.
Example:
MOD OFDMACAPABILITY: SECTORID=0, CARRIERID=0, DEMODULATIONMIMOSUPP=3,
MODULATIONMIMOSUPP=64;
Step 6 Query and set the STC Zone capability of a BS.
1. Run the LST CARRIERZONEINFO command to query the BS's STC Zone capability.
Example:
LST CARRIERZONEINFO: SECTORID=0, CARRIERID=0;
2. Run the MOD CARRIERBASICINFO and MOD CARRIERZONEINFO commands
to set the BS's STC Zone capability.
The 10 MHz bandwidth supports the subframe ratios of 35:12, 32:15, 29:18, and 26:21.
Take 29:18 as an example. Table 2-3, Table 2-4, Table 2-5, and Table 2-6 list the mapping
between the parameters and the STC Zones.
Table 2-3 Downlink PUSC 1/3 + PUSC 1/3 STC Zone, uplink PUSC 1/3
Sector Parameter Setting
0 MOD CARRIERBASICINFO: SECTORID=0,
CARRIERID=0, DLSEGMENTNO =0,
DLBITMAP="00000003",
ULBITMAP="000000000000000FFF";
MOD CARRIERZONEINFO: SECTORID=0,
CARRIERID=0, DLZONENUM=1,
DLZONEIND=3, DL2NDSTARTSYMBOL=17,
DL2NDZONESCHNUM=0, ULZONENUM=1,
ULZONEIND=1, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
1 MOD CARRIERBASICINFO: SECTORID=1,
CARRIERID=0, DLSEGMENTNO =1,
DLBITMAP="0000000C ",
ULBITMAP="000000000000FFF000";
MOD CARRIERZONEINFO: SECTORID=1,
CARRIERID=0, DLZONENUM=1,
DLZONEIND=3, DL2NDSTARTSYMBOL=17,
DL2NDZONESCHNUM=0, ULZONENUM=1,
ULZONEIND=1, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
2 MOD CARRIERBASICINFO: SECTORID=2,
CARRIERID=0, DLSEGMENTNO =2,
DLBITMAP="00000030 ",
ULBITMAP="0000000007FF000000";
MOD CARRIERZONEINFO: SECTORID=2,
CARRIERID=0, DLZONENUM=1,
DLZONEIND=3, DL2NDSTARTSYMBOL=17,
DL2NDZONESCHNUM=0, ULZONENUM=1,
ULZONEIND=1, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-11
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
Table 2-4 Downlink PUSC with All + PUSC with All STC zone, uplink PUSC with All
Sector Parameter Setting
0 Three sectors use the same parameter
setting. The values of SECTORID and
1 DLSEGMENTNO must be set according
2 to the actual conditions.
MOD CARRIERBASICINFO: SECTORID=0,
CARRIERID=0, DLSEGMENTNO =0,
DLBITMAP="0000003F",
ULBITMAP="0000000007FFFFFFFF";
MOD CARRIERZONEINFO: SECTORID=0,
CARRIERID=0, DLZONENUM=1,
DLZONEIND=24, DL2NDSTARTSYMBOL=17,
DL2NDZONESCHNUM=0, ULZONENUM=1,
ULZONEIND=4, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
Table 2-5 Down link PUSC 1/3 + PUSC 1/3 STC Zone + PUSC with All + PUSC with All
STC Zone, uplink PUSC 1/3 + PUSC with All
Sector Parameter Setting
0 MOD CARRIERBASICINFO: SECTORID=0,
CARRIERID=0, DLSEGMENTNO =0,
DLBITMAP="00000003",
ULBITMAP="000000000000000FFF";
MOD CARRIERZONEINFO: SECTORID=0,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=2,
ULZONEIND=5, UL2NDSTARTSYMBOL=15,
UL2NDZONESCHNUM=35;
1 MOD CARRIERBASICINFO: SECTORID=1,
CARRIERID=0, DLSEGMENTNO =1,
DLBITMAP="0000000C ",
ULBITMAP="000000000000FFF000";
MOD CARRIERZONEINFO: SECTORID=1,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=2,
ULZONEIND=5, UL2NDSTARTSYMBOL=15,
UL2NDZONESCHNUM=35;
2 MOD CARRIERBASICINFO: SECTORID=2,
CARRIERID=0, DLSEGMENTNO =2,
DLBITMAP="00000030 ",
ULBITMAP="0000000007FF000000";
MOD CARRIERZONEINFO: SECTORID=2,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=2,
ULZONEIND=5, UL2NDSTARTSYMBOL=15,
UL2NDZONESCHNUM=35;
2-12 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
Table 2-6 Downlink PUSC 1/3 + PUSC 1/3 STC Zone + PUSC with All + PUSC with All
STC Zone, uplink PUSC with All
Sector Parameter Setting
0 MOD CARRIERBASICINFO: SECTORID=0,
CARRIERID=0, DLSEGMENTNO =0,
DLBITMAP="00000003",
ULBITMAP="0000000007FFFFFFFF ";
MOD CARRIERZONEINFO: SECTORID=0,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=1,
ULZONEIND=4, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
1 MOD CARRIERBASICINFO: SECTORID=1,
CARRIERID=0, DLSEGMENTNO =1,
DLBITMAP="0000000C ",
ULBITMAP="0000000007FFFFFFFF ";
MOD CARRIERZONEINFO: SECTORID=1,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=1,
ULZONEIND=4, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
2 MOD CARRIERBASICINFO: SECTORID=2,
CARRIERID=0, DLSEGMENTNO =2,
DLBITMAP="00000030 ",
ULBITMAP="0000000007FFFFFFFF ";
MOD CARRIERZONEINFO: SECTORID=2,
CARRIERID=0, DLZONENUM=2,
DLZONEIND=27, DL2NDSTARTSYMBOL=21,
DL2NDZONESCHNUM=30, ULZONENUM=1,
ULZONEIND=4, UL2NDSTARTSYMBOL=0,
UL2NDZONESCHNUM=0;
NOTE
l The 5 MHz bandwidth supports the subframe ratios of 35:12, 32:15, 29:18, and 26:21 and
supports only the configuration of all subcarriers (downlink PUSC with ALL + PUSC with All
STC zone, uplink PUSC with All). Configuration method: Three sectors use the same parameter
setting, and the values of SECTORID and DLSEGMENTNO must be set according to the actual
conditions.
l The 7 MHz bandwidth supports the subframe ratio of 21:12. Table 2-3 and Table 2-4 list the
configuration method of subcarriers.
Step 7 Query and set the MIMO and the AMS switches.
1. Run the LST RRMSWITCH command to query the MIMO switch of a sector carrier.
Example:
LST RRMSWITCH: SECTORID=0, CARRIERID=0;
2. Run the MOD RRMSWITCH command to set the MIMO switch of a sector carrier.
Example:
MOD RRMSWITCH: SECTORID=0, CARRIERID=0, DLAMCSWITCH=ON, DLMIMOSWITCH=ON,
DLAMSSWITCH=ON, MIMOBAMCSWITCH=ON;
Step 8 Activate the uplink CSM function. To activate the uplink CSM function, run MOD
RRMSWITCH to set Switch of uplink CSM to ON.
Example:
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-13
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
MOD RRMSWITCH: SECTORID=0, CARRIERID=0, ULCSMSWITCH=ON;
----End
2.4.2 Deactivating the Multi-Antenna Feature
This describes how to deactivate the multi-carrier feature and the CSM function.
Procedure
Step 1 To deactivate the downlink MIMO feature, run MOD RRMSWITCH to set Switch of
downlink MIMO to OFF. To deactivate the Matrix A and Matrix B adaptive function, set
Switch of the AMS algorithm on the downlink to OFF.
Example:
MOD RRMSWITCH: SECTORID=0, CARRIERID=0, DLMIMOSWITCH=OFF, DLAMSSWITCH=OFF;
Table 2-7 lists the parameters of the command.
Table 2-7 Parameters of the MOD RRMSWITCH command
Parameter Meaning Value Range
SECTORID Sector ID 0、1、2
CARRIERID Carrier ID 0、1
DLMIMOSWITCH Switch of downlink MIMO On: 1 (enabled); OFF: 0
(disabled)
DLAMSSWITCH Switch of the AMS algorithm On: 1 (enabled); OFF: 0
on the downlink (disabled)
Step 2 To deactivate the uplink CSM function, run MOD RRMSWITCH to set Switch of uplink
CSM to OFF.
NOTE
If the command does not take effect, deactivate the sector carrier, and then activate it again.
Example:
MOD RRMSWITCH: SECTORID=0, CARRIERID=0, ULCSMSWITCH=OFF;
Table 2-8 lists the parameters of the command.
Table 2-8 Parameters of the MOD RRMSWITCH command
Parameter Meaning Value Range
SECTORID Sector ID 0、1、2
CARRIERID Carrier ID 0、1
ULCSMSWITCH Switch of uplink CSM On: 1 (enabled); OFF: 0
(disabled)
----End
2-14 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 2 Multi-Antenna Feature
2.5 Maintenance of the Multi-Antenna Feature
This describes the parameters and performance counters related to the multi-antenna feature.
Related Parameters
Table 2-9, Table 2-10, Table 2-11, and Table 2-12 list the parameters related to the multi-
carrier feature.
Table 2-9 Parameters of the MOD SECTOR command
Parameter Meaning
SECTORID Sector ID
TXANTNUM Number of transmit antennas
RXANTNUM Number of receive antennas
Table 2-10 Parameters of the MOD OFDMACAPABILITY command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
DEMODULATION Demodulation scheme
MODULATION Modulation scheme
DEMODULATIONMIMO- Supported MIMO demodulation mode
SUPP
MODULATIONMIMOSUPP Supported MIMO modulation mode
Table 2-11 Parameters of the MOD RRMSWITCH command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
DLMIMOSWITCH Switch of downlink MIMO
DLAMSSWITCH Switch of the AMS algorithm on the downlink
ULCSMSWITCH Switch of uplink CSM
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 2-15
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
2 Multi-Antenna Feature Feature Configuration Guide
Table 2-12 Parameters of the MOD RRMSOFT command
Parameter Meaning
PARANO Software parameter No.
VALUE Software parameter value
Related Performance Measurement Items
None.
2.6 Reference Information of the Multi-Antenna Feature
The multi-antenna feature complies with the IEEE 802.16e standard.
2-16 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 3 Power Control and AMC Feature
3 Power Control and AMC Feature
About This Chapter
Power control and AMC algorithms are core algorithms of WiMAX. The MS and BS cooperate
over the R1 interface to achieve power control and AMC.
3.1 Overview of the Power Control and AMC Feature
This describes the definition, purpose, specifications, and impact of the power control and AMC
feature.
3.2 Availability of the Power Control and AMC Feature
This describes the network elements involved in the power control and AMC feature and the
earliest versions that support this feature.
3.3 Description of the Power Control and AMC Feature
According to the IEEE 802.16 REV2 standard, the WiMAX system supports only uplink power
control, which applies to the transmit power of the MS. Downlink AMC works as a substitute
for downlink power control, and uplink AMC works as a supplement to uplink power control.
3.4 Implementation of the Power Control and AMC Feature
This describes how to activate and deactivate the power control and AMC feature.
3.5 Maintenance Information of the Power Control and AMC Feature
This describes the parameters and performance measurement items related to the power control
and AMC feature.
3.6 Reference Information of the Power Control and AMC Feature
This describes the reference information about the power control and AMC feature. The power
control and AMC feature complies with the R1 interface standard, namely IEEE 802.16 REV2.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
3 Power Control and AMC Feature Feature Configuration Guide
3.1 Overview of the Power Control and AMC Feature
This describes the definition, purpose, specifications, and impact of the power control and AMC
feature.
Definition
Power control is a process in which the MS or BS uses certain rules to adjust and control the
transmit power according to the change in the channel condition and the power of the received
signal. In the WiMAX system, power control is implemented mainly to control the transmit
power of the MS.
In AMC, an appropriate MCS is chosen according to the channel quality and system capacity.
Purpose
The purpose of power control is to control the transmit power of the MS, thereby ensuring the
data transmission quality in various radio environments.
In AMC, an appropriate MCS is chosen according to the channel quality and system capacity.
In this way, data transmission efficiency is maximized, and a high rate is achieved.
Power control and AMC can be used together to raise the system average throughput and
transmission quality. When the system capability is limited, the primary goal is to lower the PER
to the target value and minimize reverse interference.
Specifications
This feature supports uplink closed-loop power control, uplink open-loop power control, uplink
AMC, and downlink AMC.
This feature supports the following uplink MCSs:
l QPSKCC1/2
l QPSKCC3/4
l 16QAMCC1/2
l 16QAMCC3/4
l QPSKCTC1/2
l QPSKCTC3/4
l 16QAMCTC1/2
l 16QAMCTC3/4
This feature supports the following downlink MCSs:
l QPSKCC1/2
l QPSKCC3/4
l 16QAMCC1/2
l 16QAMCC3/4
l 64QAMCC1/2
3-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 3 Power Control and AMC Feature
l 64QAMCC2/3
l 64QAMCC3/4
l QPSKCTC1/2
l QPSKCTC3/4
l 16QAMCTC1/2
l 16QAMCTC3/4
l 64QAMCTC1/2
l 64QAMCTC2/3
l 64QAMCTC3/4
l 64QAMCTC5/6
NOTE
Not all MCSs must be used.
Impact
None.
Terms
Term Definition
Uplink An uplink is a channel on which data is transmitted from the terminal to
the BS.
Downlink A downlink is a channel on which data is transmitted from the BS to the
terminal.
Abbreviations and Acronyms
Abbreviation or
Acronym Full Spelling
AMC Adaptive Modulation and Coding
BS Base Station
BWA Broadband Wireless Access
CINR Carrier to Interference and Noise Ratio
FEC Forward Error Correction
MC Modulation and Coding
MCS Modulation Coding Scheme
MS Mobile Station
PER Packet Error Rate
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
3 Power Control and AMC Feature Feature Configuration Guide
3.2 Availability of the Power Control and AMC Feature
This describes the network elements involved in the power control and AMC feature and the
earliest versions that support this feature.
Network Elements Involved
The power control and AMC feature requires the joint work of the SS/MS and the BS. Table
3-1 lists the network elements involved in the power control and AMC feature.
Table 3-1 Network elements involved in the power control and AMC feature
AAA DHCP
SS/MS BS ASN-GW Server Server M2000
√ √ - - - √
NOTE
In Table 3-1, √ is used to mark the network elements involved in this feature, and - is used to mark the
network elements not involved in this feature.
Supporting Versions
Table 3-2 lists the versions that support the power control and AMC feature.
Table 3-2 Versions that support the power control and AMC feature
Product Version
BS DBS3900 V300R002C02
License Support
This feature is not subject to license restrictions.
3.3 Description of the Power Control and AMC Feature
According to the IEEE 802.16 REV2 standard, the WiMAX system supports only uplink power
control, which applies to the transmit power of the MS. Downlink AMC works as a substitute
for downlink power control, and uplink AMC works as a supplement to uplink power control.
Power Control
By control mode, power control is classified into closed-loop power control and open-loop power
control. Closed-loop power control is further classified into inner-loop power control and outer-
loop power control.
l Closed-loop power control
The BS measures the signal quality on the uplink and sends power control instructions to
the MS.
3-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 3 Power Control and AMC Feature
– Inner-loop power control
The BS measures the signal quality on the uplink and adjusts the transmit power of the
MS according to Cinr Target Value.
– Outer-loop power control
The BS properly adjusts Cinr Target Value, Cinr Low Threshold, and Cinr Up
Threshold to ensure the signal quality.
l Open-loop power control
The uplink and downlink channels are basically symmetrical to each other. In open-loop
power control, when detecting that the CINR on the downlink is poor, the MS regards the
uplink transmission quality to be poor. In this case, the MS raises its transmit power. When
detecting that the CINR on the downlink is good, the MS regards the uplink transmission
quality to be good. In this case, the MS lowers its transmit power.
Uplink Inner-Loop Power Control
In inner-loop power control, the BS compares the measured CINR on the uplink with Cinr
Target Value to determine whether the quality of the uplink signal is good.
l When the measured CINR on the uplink is greater than Cinr Target Value, the quality of
the uplink signal is good, the BS instructs the MS to lower its transmit power.
l When the measured CINR on the uplink is smaller than Cinr Target Value, the quality of
the uplink signal is poor, the BS instructs the MS to raise its transmit power.
The BS sends the adjusted value to the MS over the air interface.
NOTE
You can run the MOD ULAMCTHRESH command to configure the values of Cinr Target Value for all
the MSs under a carrier. For details, see Step 2.
Uplink Outer-Loop Power Control
In outer-loop power control, the BS measures the actual value of the PER and adjusts the values
of Cinr Target Value, Cinr Up Threshold, and Cinr Low Threshold for the MS according
to the values of Per Target Value for different services. The Cinr Up Threshold and Cinr
Low Threshold after adjustment are used for decision on inner-loop power control and AMC
so that the measured values of the PER for different services are close to the values of Per Target
Value for different services.
NOTE
l Different service scheduling types (UGS, eRTPS, RTPS, NRTPS, and BE services) have different
values of Per Target Value.
l You can run the MOD ULPERTHRESH command to configure the values of PER Target Value for
all the MSs under a carrier. For details, see Step 2.
The thresholds are adjusts by steps. The adjustments are accumulated. CINR threshold currently
used for inner-loop power control and AMC = Initial values of Cinr Target Value for all the
MSs under a carrier/Cinr Low Threshold/Cinr Up Threshold + accumulated adjusted value
l If the measured value of the PER is greater than Per Target Value, the Cinr Target
Value, Cinr Low Threshold, or Cinr Up Threshold is too low, and the BS automatically
raises Cinr Target Value, Cinr Low Threshold, or Cinr Up Threshold for the MS.
l If the measured value of the PER is smaller than Per Target Value, the Cinr Target
Value, Cinr Low Threshold, or Cinr Up Threshold is too high, and the BS automatically
lowers Cinr Target Value, Cinr Low Threshold, or Cinr Up Threshold for the MS.
This process is outer-loop power control.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
3 Power Control and AMC Feature Feature Configuration Guide
Uplink Open-Loop Power Control
The MS adjusts its transmit power according to the quality of the downlink signal. Open-loop
power control is fast and causes low overheads over the air interface. The drawback of open-
loop power control is low precision.
Shift Between Uplink Power Control Modes
The uplink power control mode can shift between closed-loop power control and open-loop
power control. Closed-loop power control is precise. This type of power control, however, is
slow and causes high overheads over the air interface. Open-loop power control is fast and causes
low overheads over the air interface. This type of power control, however, is not precise.
A shift between the uplink power control modes is originated by the BS or MS. When the shift
is originated by the BS, the BS sends the PMC-RSP message to the MS, and the MS responds
with the PMC-REQ message acknowledging the receipt of the shift instruction. When the power
control mode shifts from closed-loop power control to open-loop power control, the MS can
start transmitting data on the uplink only if it has received both the PMC-RSP and UL noise and
interference level IE messages from the BS.
AMC
Uplink AMC
The basic principle of uplink AMC is that the BS instructs the MS to use a low-level MCS when
the measured CINR is below the Cinr Low Threshold for the FEC. The BS instructs the MS
to use a high-level MCS when the measured CINR is above Cinr Up Threshold for the FEC.
NOTE
You can run the MOD ULAMCTHRESH command to configure the values of Cinr Lower Threshold
and Cinr Upper Threshold for all the MSs under a carrier. For details, see Step 2.
Generally, uplink inner-loop power control is used together with AMC. In this way, power
control is implemented to adjust the actual CINR, and MCS is adjusted so that the uplink CINR
of the MS stays in the required range. Uplink inner-loop power control and uplink AMC are
implemented at the same time. When the uplink signal is poor, the MCS is lowered or the transmit
power of the MS is raised to ensure correct signal demodulation on the uplink. When the uplink
signal becomes good, the MCS is raised or the transmit power of the MS is lowered to ensure
correct signal demodulation on the uplink.
Downlink AMC
Closed-loop power control is used together with the mode of the MS requesting the MCS. The
MS reports the downlink CINR, and the BS decides the downlink MCS. If the value of the
parameter DownLink MS AMC Switch is set to ON, the system prefers and uses the downlink
MCS reported by the MS if possible. If the MS does not report the MCS, the BS determines the
downlink MCS. If the value of the parameter DownLink MS AMC Switch is set to OFF, the
BS decides the downlink MCS.
NOTE
You can run the MOD RRMSWITCH command to configure the value of the parameter DownLink MS
AMC Switch. For details, see .
You can run the MOD DLAMCTHRESH command to configure the values of Cinr Lower Threshold
and Cinr Upper Threshold for all the MSs under a carrier. For details, see Step 2.
3-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 3 Power Control and AMC Feature
3.4 Implementation of the Power Control and AMC Feature
This describes how to activate and deactivate the power control and AMC feature.
3.4.1 Activating the Power Control and AMC Feature
This describes how to activate the power control and AMC feature. On the M2000 or web LMT,
you can run associated MML commands to set specific parameters to activate the power control
and AMC feature.
3.4.2 Deactivating the Power Control and AMC Feature
This describes how to deactivate the power control and AMC feature. On the M2000 or web
LMT, you can run an associated MML command to deactivate the power control and AMC
feature.
3.4.1 Activating the Power Control and AMC Feature
This describes how to activate the power control and AMC feature. On the M2000 or web LMT,
you can run associated MML commands to set specific parameters to activate the power control
and AMC feature.
Procedure
l Activate uplink inner-loop power control
1. To activate uplink inner-loop power control, run the MOD RRMSWITCH command,
with the value of the parameter UpLink Inner Loop Power Control Switch
(ULINNERLOOPPOWERSWITCH) set to NEWPCALG.
l Activate uplink outer-loop power control.
1. To activate uplink outer-loop power control, run the MOD RRMSWITCH command,
with the value of the parameter UpLink Outer Loop Power Control Switch
(ULOUTERLOOPPOWERSWITCH) set to ON.
2. If necessary, run the MOD ULPERTHRESH command to change the target PER
value and maximum adjustment step of each service. Generally, the default value is
recommended.
For example, the target PER and maximum adjustment step of the BE service are
BePer Target Value (BEPERTARGET) and BePer Maximum Adjust Step
(BEMAXADJSTEP) respectively.
l Activate uplink open-loop power control.
1. Run the MOD RRMSWITCH command to set the value of the parameter UpLink
Power Control Change MS Switch (ULPOWERCTRLMODEMSSWITCH) to
ON. After the value is set in this way, the BS starts open-loop power control if the MS
sends an open-loop power control request and the BS responds with a message
indicating that the power control mode is successfully changed.
By default, the BS starts closed-loop power control.
l Activate uplink AMC.
1. To activate uplink AMC, run the MOD RRMSWITCH command, with the value of
the parameter UpLink AMC Switch (ULAMCSWITCH) set to ON.
2. If necessary, run the MOD ULAMCTHRESH command to modify the initial values
of the parameters Cinr Target Value (CINRTARGET), Cinr Up Threshold
(CINRUPTHRE), Cinr Low Threshold (CINRLOWTHRE), and Maximum
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
3 Power Control and AMC Feature Feature Configuration Guide
Adjust Step(MAXADJUSTSTEP) for all the MSs under a carrier. Generally, the
default value is recommended.
l Activate downlink AMC.
1. To activate downlink AMC, run the MOD RRMSWITCH command, with the value
of the parameter DownLink AMC Switch (DLAMCSWITCH) set to ON.
2. If necessary, run the MOD DLAMCTHRESH command to modify the initial values
of the parameters Cinr Target Value (CINRTARGET), Cinr Up Threshold
(CINRUPTHRE), Cinr Low Threshold (CINRLOWTHRE), and Maximum
Adjust Step(MAXADJUSTSTEP) for all the MSs under a carrier. Generally, the
default value is recommended.
----End
3.4.2 Deactivating the Power Control and AMC Feature
This describes how to deactivate the power control and AMC feature. On the M2000 or web
LMT, you can run an associated MML command to deactivate the power control and AMC
feature.
Procedure
l Deactivate uplink inner-loop power control.
1. To deactivate uplink inner-loop power control, run the MOD RRMSWITCH
command, with the value of the parameter UpLink Inner Loop Power Control
Switch (ULINNERLOOPPOWERSWITCH) set to OFF.
l Deactivate uplink AMC.
1. To deactivate uplink AMC, run the MOD RRMSWITCH command, with the value
of the parameter UpLink AMC Switch (ULAMCSWITCH) set to OFF.
l Deactivate uplink outer-loop power control.
1. To deactivate uplink outer-loop power control, run the MOD RRMSWITCH
command, with the value of the parameter UpLink Outer Loop Power Control
Switch (ULOUTERLOOPPOWERSWITCH) set to OFF.
l Deactivate uplink open-loop power control.
1. Run the MOD RRMSWITCH command to set the value of the parameter UpLink
Power Control Change MS Switch (ULPOWERCTRLMODEMSSWITCH) to
OFF. After the value is set in this way, the BS does not support the power control
mode change, which is initiated by the MS.
l Deactivate downlink AMC.
1. To deactivate downlink AMC, run the MOD RRMSWITCH command, with the
value of the parameter DownLink AMC Switch (DLAMCSWITCH) set to OFF.
----End
3.5 Maintenance Information of the Power Control and
AMC Feature
This describes the parameters and performance measurement items related to the power control
and AMC feature.
3-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 3 Power Control and AMC Feature
Related Parameters
Table 3-3, Table 3-4, and Table 3-5 list the parameters related to the power control and AMC
feature.
Table 3-3 Parameters of the MOD RRMSWITCH command
ID Name
ULINNERLOOPPOWERSWITCH Switch for the uplink inner-loop power control
ULOUTERLOOPPOWERSWITCH Switch for the uplink outer-loop power control
ULAMCSWITCH Switch for uplink AMC
DLAMCSWITCH Switch for downlink AMC
Table 3-4 Parameters of the MOD ULAMCTHRESH command
ID Name
CINRTARGET Target CINR value
CINRUPTHRE Upper threshold of the CINR
CINRLOWTHRE Lower threshold of the CINR
Table 3-5 Parameters of the MMOD ULPERTHRESH command
ID Name
BEPERTARGET Target BEPER value
NRTPSPERTARGET Target NRTPSPER value
RTPSPERTARGET Target RTPSPER value
ERTPSPERTARGET Target ERTPSPER value
UGSPERTARGET Target UGSPER value
Related Performance Measurement Items
None.
3.6 Reference Information of the Power Control and AMC
Feature
This describes the reference information about the power control and AMC feature. The power
control and AMC feature complies with the R1 interface standard, namely IEEE 802.16 REV2.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 3-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
4 Idle Mode Feature
About This Chapter
This describes the basic concepts, functions, and implementation method of the idle mode
feature.
4.1 Overview of the Idle Mode Feature
Idle mode is a mature technology developed for optimum allocation of network resources and
reduced power consumption of an MS.
4.2 Availability of the Idle Mode Feature
This describes the network elements involved in the idle mode feature and the versions that
support the idle mode feature.
4.3 Description of the Idle Mode Feature
The idle mode feature provides functions of idle mode entry, paging, location update, and idle
mode exiting.
4.4 Implementation of the Idle Mode Feature
This describes how to activate and deactivate the idle mode feature.
4.5 Maintenance Information of the Idle Mode Feature
This describes the parameters and performance measurement items related to the idle mode
feature.
4.6 Reference Information of the Idle Mode Feature
The R1 interface protocol and R6 interface protocol that the idle mode feature complies with
are IEEE 802.16 REV2 and WiMAX NWG 1.2 respectively.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
4.1 Overview of the Idle Mode Feature
Idle mode is a mature technology developed for optimum allocation of network resources and
reduced power consumption of an MS.
Definition
Idle mode allows an MS to move within a paging group (PG) composed by multiple BSs without
registration at a specific BS. After an MS enters idle mode, the MS periodically receives DL
broadcast messages. The BS deletes all the link information of the MS, and the ASN-GW retains
only the connection information of the MS on the paging controller (PC).
Purpose
When the SS/MS in idle mode roams to another cell, no handover process is triggered, thus
saving air interface resources and reducing the power of the SS/MS.
The idle mode feature also saves resources that may be wasted during handover of an SS/MS to
another BS when the SS/MS roams across a border of a BS. If the SS/MS is in idle mode, the
BS releases the resources reserved for the SS/MS, thus maximizing the use of the resources.
Network Model
Figure 4-1 shows the network model of the idle mode feature.
Figure 4-1 Network model of the idle mode feature
The BS incorporates a paging agent (PA), and the ASN-GW incorporates a paging controller
(PC)/location registration (LR).
A PG is a logical group composed by multiple BSs. A BS can belong to multiple PGs.
4-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
The PA interfaces with the SS/MS on the R1 interface and with the PC on the R6 interface.
Specifications
A BS supports three PGs.
Impacts
The idle mode feature saves air interface resources and network resources and improves the
capacity of a network.
The idle mode feature reduces the power of an SS/MS.
The idle mode feature prolongs the service activation time.
Terms
Term Definition
Paging A process in which an MS in idle mode is instructed to exit idle mode
or to update the location information through a message broadcast over
the air interface.
Paging Group A logical group composed by multiple BSs. In the coverage of a PG, an
SS/MS can be periodically paged by a BS for location update or network
re-entry without establishment of an air interface link to the BS. A PG
is generally managed and deployed by the network management system
and is identified with a PG ID.
Paging Controller A function entity that implements the idle mode feature. The PC stores
the status and operation parameters of SSs/MSs in idle mode and controls
the paging operations of SSs/MSs in idle mode. PCs can be categorized
into two types: anchor PC and relay PC.
Paging Cycle A period in which a paging process is completed through broadcasting
of paging messages. An SS/MS synchronizes its paging cycle with the
BS to receive broadcast messages that instruct the SS/MS to exit idle
mode or to perform location update.
Paging Offset Paging frame offset. It is used together with a paging cycle to determine
the number of frames of a paging message. An SS/MS synchronizes its
paging cycle with the BS to receive broadcast messages that instruct the
SS/MS to exit idle mode or to perform location update.
Paging Agent A functional entity incorporated on the BS. It is used to implement
functions of the idle mode feature, for example, periodic paging of SSs/
MSs, instructing SSs/MSs to enter or exit idle mode or to perform
location update.
Location A functional entity that stores the status and operation data of SSs/MSs
Registration in idle mode.
Location Update A process initiated when an SS/MS detects changes in the paging group
or the SS/MS is powered off.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
Term Definition
Anchor PC A PC uniquely associated with an SS/MS in idle mode. An anchor PC
retains the information of an SS/MS, controls idle mode entry or exiting
of the SS/MS, and updates the location information of the SS/MS.
Relay PC A PC associated with an SS/MS together with other PCs. A relay PC
forwards control messages between an anchor PC and a PA.
Acronyms and Abbreviations
Acronym Description
SS/MS Subscriber Station/Mobile Station
BS Base Station
PA Paging Agent
PG Paging Group
PC Paging Controller
LR Location Registration
LU Location Update
4.2 Availability of the Idle Mode Feature
This describes the network elements involved in the idle mode feature and the versions that
support the idle mode feature.
Network Element
The idle mode feature requires the joint work of the SS/MS, BS, and ASN-GW. Table 4-1 lists
the network elements involved in the idle mode feature.
Table 4-1 Network elements involved in the idle mode feature
ASN AAA DHCP
SS/MS BS -GW Server Server M2000
√ √ √ √ √ -
NOTE
In Table 4-1, √ indicates network elements that are involved in the idle mode feature, and - indicates
network elements that are not involved.
Version
Table 4-2 lists the versions that support the idle mode feature.
4-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
Table 4-2 Versions that support the idle mode feature
Product Version
BS DBS3900 WiMAX V300R002C02
License
A license is not required for the idle mode feature.
4.3 Description of the Idle Mode Feature
The idle mode feature provides functions of idle mode entry, paging, location update, and idle
mode exiting.
4.3.1 Entering Idle Mode
This describes the idle mode entry process of an SS/MS.
4.3.2 Paging
This describes the paging process initiated by the ASN-GW.
4.3.3 Location Update
This describes the location update process of an SS/MS.
4.3.4 Exiting Idle Mode
This describes the idle mode exiting process of an SS/MS.
4.3.1 Entering Idle Mode
This describes the idle mode entry process of an SS/MS.
After the SS/MS enters idle mode, the BS notifies the paging controller of the SS/MS idle mode
and sends the connection information such as SBC-related context, security-related context, and
traffic stream information to the paging controller for storage. At the same time, the BS initiates
a management resource holding timer. Before the timer expires, the BS saves the connection
information for the SS/MS. After the timer expires, the BS deletes the saved connection
information and releases R6 interface resources.
The SS/MS enters idle mode in the following situations:
l The SS/MS sends a message to the BS to request for idle mode entry.
l The BS puts the SS/MS into idle mode if the UL or DL data related to the SS/MS does not
exist.
Idle Mode Entry Initiated by the SS/MS
Figure 4-2 shows the idle mode entry process initiated by the SS/MS.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
Figure 4-2 Idle mode entry initiated by the SS/MS
1. The SS/MS sends a DREG-REQ message to the BS to request for idle mode entry.
l If the UL or DL data related to the SS/MS exists, the BS performs 2 .
l If the UL or DL data related to the SS/MS does not exist, the BS performs 4.
2. The BS sends a DREG-CMD message to the SS/MS to notify the SS/MS of later request
for idle mode entry after the REQ-duration expires.
3. After the REQ-duration expires, the SS/MS sends a DREG-REQ message to the BS to
request for idle mode entry.
4. The BS sends an IM_Entry_State_Change_Req message to the ASN-GW.
5. The ASN-GW returns an IM_Entry_State_Change_Rsp message to the BS.
6. The BS sends a DREG-CMD message to the SS/MS.
7. The BS sends an IM_Entry_State_Change_Ack message to the ASN-GW to indicate the
SS/MS idle mode entry.
8. The SS/MS exits the network, and the resources are released.
Idle Mode Entry Initiated by the BS
Figure 4-3 shows the idle mode entry process initiated by the BS.
Figure 4-3 Idle mode entry initiated by the BS
4-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
1. When the BS detects that the SS/MS needs to enter idle mode, the BS sends an
IM_Entry_State_Change_Req message to the ASN-GW.
2. The ASN-GW sends an IM_Entry_State_Change_Rsp message to the BS.
3. The BS sends a DREG-CMD message to the SS/MS.
4. The SS/MS sends a DREG-REQ message and enters idle mode.
5. The BS sends an IM_Entry_State_Change_Ack message to the ASN-GW to indicate the
SS/MS idle mode entry.
6. The SS/MS exits the network, and the resources are released.
4.3.2 Paging
This describes the paging process initiated by the ASN-GW.
Paging is a process in which a broadcast message is sent to notify an SS/MS in idle mode of
location update or network re-entry when the location information of the SS/MS needs to be
updated or data related to the SS/MS is present on the ASN-GW.
Paging Process
Figure 4-4 shows the paging process.
Figure 4-4 Paging process
1. The ASN-GW sends a Paging_Announce message to all BSs in the PG where the SS/MS
resides.
l If Paging Cause contained in the Paging_Announce message is 0x01, SS/MS location
update is required.
l If Paging Cause contained in the Paging_Announce message is 0x02, SS/MS network
re-entry from idle mode is required.
2. The paged BS sends an MOB_PAG-ADV message to the SS/MS.
3. Based on Action Code contained in the MOB_PAG-ADV message, the SS/MS determines
whether to perform location update or to re-enter the network from idle mode.
l If Action Code is 0b01, the SS/MS performs location update.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
l If Action Code is 0b10, the SS/MS re-enters the network from idle mode.
4.3.3 Location Update
This describes the location update process of an SS/MS.
Location update is a process in which an SS/MS in idle mode reports its location information to
the network.
Location update can be initiated by the SS/MS or the ASN-GW.
l When the PG changes, the timer expires, or the SS/MS is powered off, the SS/MS in idle
mode initiates location update.
l The ASN-GW can also initiate SS/MS location update through paging.
Location update can be classified into secure location update and insecure location update.
l If a valid secure context exists between the SS/MS and the BS, that is, the BS receives a
valid authentication key, secure location update is initiated. After the secure location update
is complete, the SS/MS remains in idle mode.
l If a valid secure context does not exist between the SS/MS and the BS, that is, the BS does
not receive a valid authentication key, insecure location update is initiated. Insecure
location update is actually a location update failure. After the insecure location update is
complete, the SS/MS re-enters the network from idle mode.
Secure Location Update Process
Figure 4-5 shows the secure location update process.
NOTE
If the location update is initiated by the ASN-GW, the process starts from 1.
If the location update is initiated by the SS/MS, the process starts from 5.
Figure 4-5 Secure location update process
4-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
1. The ASN-GW sends a Paging_Announce message to all BSs in the PG where the SS/MS
resides.
2. The paged BS sends an MOB_PAG-ADV message to the SS/MS.
3. The SS/MS sends ranging codes at an assigned ranging region to the BS.
4. The BS sends an RNG-RSP message to the SS/MS.
l If Raging Status contained in the RNG-RSP message is continue, the process returns
to 3.
l If Raging Status contained in the RNG-RSP message is success, the process goes to
5.
5. The SS/MS sends an RNG-REQ message to the BS for location update.
6. The BS sends an LU-Req message to the ASN-GW to request for the SS/MS location
update.
7. The ASN-GW sends an LU-Rsp message to the BS to acknowledge the SS/MS location
update.
8. The BS sends an RNG_RSP message to the SS/MS to indicate successful location update
after the BS verifies the RNG_REQ message.
9. The BS sends an LU-Cnf message to the ASN-GW to indicate successful location update.
Insecure Location Update Process
Figure 4-6 shows the insecure location update process.
NOTE
If the location update is initiated by the ASN-GW, the process starts from 1.
If the location update is initiated by the SS/MS, the process starts from 5.
Figure 4-6 Insecure location update process
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
1. The ASN-GW sends a Paging_Announce message to all BSs in the PG where the SS/MS
resides.
2. The paged BS sends an MOB_PAG-ADV message to the SS/MS.
3. The SS/MS sends ranging codes at an assigned ranging region to the BS.
4. The BS sends an RNG-RSP message to the SS/MS.
l If Raging Status contained in the RNG-RSP message is continue, the process returns
to 3.
l If Raging Status contained in the RNG-RSP message is success, the process goes to
5.
5. The SS/MS sends an RNG-REQ message to the BS for location update.
6. The BS sends an LU-Req message to the ASN-GW to request for the SS/MS location
update.
7. The ASN-GW sends an LU_Rsp message to the BS.
8. The BS sends an RNG_RSP message to the SS/MS to indicate a location update failure if
any of the following conditions is met:
l The ASN-GW sends the LU-Rsp message to reject the SS/MS location update.
l The LU_Rsp message does not contain the SS/MS-related context.
l The BS fails to verify the RNG_REQ message.
9. The BS sends an LU-Cnf message to the ASN-GW to indicate location update failure.
10. The SS/MS re-enters the network from idle mode.
4.3.4 Exiting Idle Mode
This describes the idle mode exiting process of an SS/MS.
When the SS/MS enters idle mode, the BS starts a management resource holding timer for the
SS/MS. Depending on whether the timer expires, the SS/MS has different processes of network
re-entry from idle mode.
An SS/MS in idle mode re-enters the network in the following situations:
l The UL data is present on the SS/MS side, or the user of the SS/MS wants to re-enter the
network.
l The DL data related to the SS/MS is present on the ASN-GW side, and the paging controller
pages the BS in the PG and instructs the BS to broadcast a paging message for SS/MS
network re-entry from idle mode.
Idle Mode Exiting After the Timer Expires
Figure 4-7 shows the idle mode exiting process after the management resource holding timer
expires.
NOTE
If the SS/MS idle mode exiting is initiated by the ASN-GW, the idle mode exiting process starts from 1.
If the SS/MS idle mode exiting is initiated by the SS/MS, the idle mode exiting process starts from 5.
4-10 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
Figure 4-7 Idle mode exiting after the timer expires
1. The ASN-GW sends a Paging_Announce message to all BSs in the PG where the SS/MS
resides.
2. The paged BS sends an MOB_PAG-ADV message to the SS/MS to instruct the SS/MS to
re-enter the network from idle mode.
3. The SS/MS sends ranging codes at an assigned ranging region to the BS.
4. The BS sends an RNG-RSP message to the SS/MS.
l If Raging Status contained in the RNG-RSP message is continue, the process returns
to 3.
l If Raging Status contained in the RNG-RSP message is success, the process goes to
5.
5. The SS/MS sends an RNG-REQ message to the BS for network re-entry from idle mode.
6. The BS sends an IM_Exit_State_Change_Req message to the ASN-GW after the BS detects
that the management resource holding timer expires.
7. The ASN-GW sends an IM_Exit_State_Change_Rsp message to the BS.
8. The BS sends an RNG-RSP message to the SS/MS after the BS verifies the validity of the
SS/MS.
9. The BS sends a Path_Reg_Req message to the ASN-GW for establishment of data links.
10. The ASN-GW sends a Path_Reg_Rsp message to the BS.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-11
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
11. The SS/MS initiates network re-entry from idle mode.
12. During SS/MS network re-entry from idle mode, the BS sends a
CMAC_Key_Count_Update message to the ASN-GW for update of the CMAC Key Count.
13. The ASN-GW returns a CMAC_Key_Count_Update_Ack message to the BS.
14. After network re-entry is complete, the BS sends a Path_Reg_Ack message to the ASN-
GW to acknowledge the establishment of data links.
Idle Mode Exiting Before the Timer Expires
Figure 4-8 shows the idle mode exiting process before the management resource holding timer
expires.
NOTE
If the SS/MS idle mode exiting is initiated by the ASN-GW, the idle mode exiting procedure starts from 1.
If the SS/MS idle mode exiting is initiated by the SS/MS, the idle mode exiting procedure starts from 5.
Figure 4-8 Idle mode exiting before the timer expires
1. The ASN-GW sends a Paging_Announce message to all BSs in the PG where the SS/MS
resides.
2. After the BS receives the Paging Announce message, the BS sends an MOB_PAG-ADV
message to the SS/MS to instruct the SS/MS to re-enter the network from idle mode.
3. The SS/MS sends ranging codes at an assigned ranging region to the BS.
4. The BS sends an RNG-RSP message to the SS/MS.
l If Raging Status contained in the RNG-RSP message is continue, the process returns
to 3.
l If Raging Status contained in the RNG-RSP message is success, the process goes to
5.
5. The SS/MS sends an RNG-REQ message to the BS for network re-entry from idle mode.
6. The BS sends a RNG_RSP message to the SS/MS after the BS detects that the management
resource holding timer does not expire.
4-12 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
7. The BS sends an IM_Exit_State_Change_Req message to the ASN-GW.
8. The ASN-GW sends an IM_Exit_State_Change_Rsp message to the BS.
4.4 Implementation of the Idle Mode Feature
This describes how to activate and deactivate the idle mode feature.
4.4.1 Activating the Idle Mode Feature
This describes how to activate the idle mode feature. You can activate the idle mode feature on
a web LMT or the M2000.
4.4.2 Deactivating the Idle Mode Feature
This describes how to deactivate the idle mode feature. You can deactivate the idle mode feature
on a web LMT or the M2000.
4.4.1 Activating the Idle Mode Feature
This describes how to activate the idle mode feature. You can activate the idle mode feature on
a web LMT or the M2000.
Procedure
Step 1 Run the DSP CARRIERSTATUS command to query the status of carriers.
l If carriers are unblocked, run the MOD CARRIERBLOCKFLAG command to block the
carriers.
l If carriers are blocked, go to Step 2.
Step 2 Run the MOD MACCAPABILITY command to configure MOBFEATURESUPP.
Example:
MOD MACCAPABILITY: SECTORID=0, CARRIERID=0, MOBFEATURESUPP=7;
NOTE
The value range of MOBFEATURESUPP is 0 to 7.
The BS supports the idle mode feature when MOBFEATURESUPP is set to 4, 5, 6, or 7.
Step 3 Run the MOD CARRIERBLOCKFLAG command to unblock carriers.
Step 4 Run the ADD PAGINGINF command to add a PG for the BS.
Parameters to be configured in this command are SectorID, CarrierID, PagingGroupID,
PagingControllerID, PagingCycle, PagingOffset, PagingIntervallen,
PagingAnnounceTimer, and IdleModeRetainInf. The configuration of PagingGroupID,
PagingCycle, and PagingOffset must be consistent with the configuration of corresponding
parameters of the PG on the ASN-GW.
----End
4.4.2 Deactivating the Idle Mode Feature
This describes how to deactivate the idle mode feature. You can deactivate the idle mode feature
on a web LMT or the M2000.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-13
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
4 Idle Mode Feature Feature Configuration Guide
Procedure
Step 1 Run the DSP CARRIERSTATUS command to query the status of carriers.
l If carriers are unblocked, run the MOD CARRIERBLOCKFLAG command to block the
carriers.
l If carriers are blocked, go to Step 2.
Step 2 Run the MOD MACCAPABILITY to configure MOBFEATURESUPP.
Example:
MOD MACCAPABILITY: SECTORID=0, CARRIERID=0, MOBFEATURESUPP=0;
NOTE
The value range of MOBFEATURESUPP is 0 to 7.
When the MOBFEATURESUPP parameter is set to 0, 1, 2, and 3, you can infer that the BS does support
the idle mode feature.
Step 3 Run the MOD CARRIERBLOCKFLAG command to unblock carriers.
----End
4.5 Maintenance Information of the Idle Mode Feature
This describes the parameters and performance measurement items related to the idle mode
feature.
Related Parameters
Table 4-3 and Table 4-4 list the parameters related to the idle mode feature.
Table 4-3 Parameters of the MOD MACCAPABILITY command
Parameter Description
SECTORID Sector ID
CARRIERID Carrier ID
MOBMODESUPP Support for mobility
Table 4-4 Parameters of the ADD PAGINGINF command
Parameter Description
CarrierID Carrier ID
SectorID Sector ID
PagingGroupID PG ID
PagingControllerID PC ID
PagingCycle Paging cycle
PagingOffset Paging offset
4-14 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 4 Idle Mode Feature
Parameter Description
PagingIntervallen Paging interval
PagingAnnounceTimer Paging announcement timer
IdleModeRetainInf Resource reservation flag
Related Performance Measurement Items
Table 4-5 lists the performance measurement items related to the idle mode feature.
Table 4-5 Performance measurement items related to the idle mode feature
Item Description
Idle entry success times See Successful Idle Entries Triggered by the MS.
triggered by MS
Idle entry success times See Successful Idle Entries Triggered by the BS.
triggered by BS
Idle entry rejected times by See Idle Entry Rejected Times by MS Times.
MS times
Times of the BS sending See Paging Messages Sent by the BS.
paging messages
Location update times due See Location Updates (Normal).
to normal
Location update times due See Location Update Times Due to Power Off.
to power off
Location update success See Location Update Success Times.
times
Re-entry network times See Re-Entry Network Times From Idle.
from idle
Re-entry network success See Re-Entry Network Success Times From Idle.
times from idle
4.6 Reference Information of the Idle Mode Feature
The R1 interface protocol and R6 interface protocol that the idle mode feature complies with
are IEEE 802.16 REV2 and WiMAX NWG 1.2 respectively.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 4-15
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
5 QoS Feature
About This Chapter
The WiMAX BS can provide users with five different Quality of Service (QoS) levels. Users
need to choose the desired QoS level when subscribing to services.
5.1 Overview of the QoS Feature
This describes the purpose, specifications, impact, and terms of the Quality of Service (QoS)
feature.
5.2 Availability of the QoS Feature
This describes the network elements involved in the QoS feature and the versions that support
the QoS feature.
5.3 Description of the QoS Feature
The Huawei DBS3900 WiMAX BS provides an end-to-end QoS solution, including the QoS
mechanism of the R1 and R6 interfaces.
5.4 Implementation of the QoS Feature
This describes how to activate and deactivate the QoS feature.
5.5 Maintenance Information of the QoS Feature
This describes the parameters and performance measurement items related to the QoS feature.
5.6 Reference Information of the QoS Feature
The R1 interface protocol and R6 interface protocol that the QoS feature complies with are IEEE
802.16 REV2 and WiMAX NWG 1.2 respectively.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
5.1 Overview of the QoS Feature
This describes the purpose, specifications, impact, and terms of the Quality of Service (QoS)
feature.
QoS is an end-to-end processing mechanism used to guarantee the quality of communication
services. On a WiMAX network, QoS ensures that users obtain expected service levels in terms
of the packet loss rate, delay, jitter, and bandwidth. The QoS feature supported by the Huawei
WiMAX solution is deployed over the R1 and R6 interfaces.
Purpose
QoS is used to guarantee the end-to-end service quality. When the network is congested, QoS
guarantees reliable data transmission of important services and ensures efficient use of network
resources.
QoS offers operators with effective control over the use of network resources. With QoS, the
network supports existing and emerging multimedia services and applications. At the same time,
the network can distinguish between services and provide corresponding quality guarantee. In
this way, multiple services such as voice, video, and data can be converged on the same network.
With QoS, operators can divide users into detailed groups and provide user-specific
differentiated and value-added services.
Specifications
The IEEE 802.16e standard defines five service flow QoS sheduling types, that is, the UGS,
ertPS rtPS, nrtPS, and BE.
Impact
None.
Term
Term Definition
Throughput Throughput refers to the rated throughput on a specified medium,
protocol, or connection. Throughput can be interpreted as the maximum
transmission rate when no packet is lost.
Latency Latency refers to the time it takes for the original data to go through a
series of processing steps such as coding, to be transmitted through the
channel, to arrive at the receiver, and to be decoded.
Jitter Generally, signals are not simply transmitted on communication
channels from the transmitter to the receiver in a point-to-point manner.
Instead, signals may be amplified or forwarded by repeaters. There is a
process of storing, processing, and forwarding. In addition, the network
conditions affect the transmission of signals. Therefore, the delay in the
same service flow varies. The variation of packet delay is known as
packet jitter.
5-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
Term Definition
Packet loss rate Because of the limited buffer size of network switching equipment and
the interfering signals on the transmission links, packets may get lost on
the transmission links. The packet loss rate is the ratio of the number of
lost packets to the number of transmitted packets. The packet loss rate
is an important yardstick for measuring the quality of communication
links.
Service flow A service flow is a uni-directional transmission service that is provided
by the MAC layer and used to transmit packets. A service flow may be
a downlink or uplink service flow and provides specific QoS functions.
Each service flow can be described with a set of QoS parameters, such
as delay, jitter, and throughput.
IP PATH An IP path is an end-to-end manageable transmission path between the
BS and the gateway. The IP path is only a concept and management entity
on the control plane, and it is invisible to service flows on the user plane.
Abbreviations and Acronyms
Abbreviations
and Acronyms Expansion
QoS Quality of Service
MS Mobile Station
SS Subscriber Station
MAC Medium Access Control
BS Base Station
UGS Unsolicited grant service
rtPS Real-time polling service
ertPS Extended rtPS
nrtPS Non-real-time polling service
BE Best effort
TOS Type of Service
DSCP Differentiated Service Code Point
5.2 Availability of the QoS Feature
This describes the network elements involved in the QoS feature and the versions that support
the QoS feature.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
Network Element Involved
The QoS feature requires the joint work of the SS/MS, BS, and ASN GW. If authentication is
required, the AAA server must be configured. Table 5-1 lists the network elements (NEs)
involved in the QoS feature.
Table 5-1 NEs involved in the QoS feature
ASN AAA DHCP
SS/MS BS -GW Server Server M2000
√ √ √ √ - -
NOTE
√: involved. -: not involved.
Supporting Versions
Table 5-2 lists the versions that support the QoS feature.
Table 5-2 Versions that support the QoS feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Restriction
This feature is not subject to license restrictions.
5.3 Description of the QoS Feature
The Huawei DBS3900 WiMAX BS provides an end-to-end QoS solution, including the QoS
mechanism of the R1 and R6 interfaces.
The IEEE802.16e defines the QoS mechanism of the R1 interface in the WiMAX system. The
QoS mechanism specifies the association between data packets on the MAC layer and a
connection-oriented service flow. Each service flow is granted QoS parameters such as the
service type, delay, jitter, and data rate. Efficient management and scheduling of service flows
guarantees the satisfaction of QoS requirements.
The QoS mechanism of the R6 interface focuses on transmission resources. It involves the
following technologies: mapping between the QoS parameters and the R6 interface transmission
priority, IP Differentiated Service, and IP flow shaping.
5.3.1 QoS Network Model
This describes the QoS network model in the Huawei WiMAX network.
5.3.2 QoS Mechanism and Parameters
This describes the QoS mechanism and parameters.
5.3.3 QoS Transmission Control
This describes the QoS transmission control mechanism.
5-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
5.3.1 QoS Network Model
This describes the QoS network model in the Huawei WiMAX network.
Figure 5-1 shows the subsystems and NE interfaces involved in the QoS feature.
Figure 5-1 External interfaces of the WiMAX DBS3900
Upon subscription, the QoS profile is configured for subscribers through the Web Management
Access System (WMAS) of the AAA or the LMT of the ASN-GW. When a subscriber accesses
the network, the QoS profile is delivered to the WiMAX DBS3900 along with the pre-
provisioned service flow established. The DBS3900 is responsible for service flow management
and QoS scheduling.
See 5.3.3 QoS Transmission Control for the differentiated service, admission control, and load
control functions in Figure 5-1.
5.3.2 QoS Mechanism and Parameters
This describes the QoS mechanism and parameters.
QoS Application Objects
l Service flow QoS scheduling
The IEEE802.16e defines five types of service flows: UGS, rtPS, ertPS, nrtPS, and BE.
Each type of service flows is associated with different QoS parameters. The scheduling
policy depends on the type of service flow and its associated QoS parameters. Each
scheduling type supports different typical services, as listed in Table 5-3.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
Table 5-3 QoS scheduling types and corresponding typical services
QoS Scheduling
Service Type Typical Service
UGS l E1/T1 services with fixed bit rates
l VoIP without silence suppression
rtPS MPEG video service flow
ertPS VoIP with silence suppression
nrtPS High-bandwidth FTP service flow
BE Web browsing service of the Internet
l User-oriented QoS
Different user priorities are defined to provide users with differentiated services. There are
four user priorities: golden, silver, copper, and common.
QoS Parameters
In the WiMAX system, QoS parameters are defined to describe scheduling rules for service
flows over the air interface. Each type of scheduling service is configured with a set of QoS
parameters: delay, tolerant jitter, and bandwidth. Each type of scheduling service matches with
a QoS parameter set.
UGS
The UGS is designed to support real-time uplink service flows that transmit fixed-size packets
on a periodic basis.
The BS assigns fixed bandwidth to the preceding service flows on a real-time and periodic basis.
In this way, the overheads consumed by requests from the SSs are reduced, and the real-time
requirements of the service flows are met. Therefore, in a UGS service flow, data is sent through
the bandwidth granted periodically by the BS, and the SS does not request bandwidth from the
BS.
The QoS parameters of the UGS are as follows:
l Maximum Sustained Traffic Rate (Maximum sustained rate, ADD QOSTEMP)
This parameter indicates the average peak rate of data service flows. On the uplink, the SS
ensures that the average rate of the service flows does not exceed the value of this parameter.
On the downlink, the BS limits the rate at the entry of the network. The value range of this
parameter is subject to restrictions due to the transmission capabilities of the air interface
and R6 interface. In addition, the value range of this parameter is related to the uplink and
downlink transmission capabilities of the SS. If the value of this parameter is too large or
too small, calculation is performed during the actual process of establishing the service
flow according to the resource management algorithm, and the calculation result determines
whether the service flow can be successfully established. Based on the current capabilities
of the SS and actual service requirements, the recommended value of this parameter is
between 256 kbit/s and 8 Mbit/s. Operators can provide services of different rates, for
example, 512 kbit/s, 1 Mbit/s, and 2 Mbit/s.
l Request/Transmission Policy (Transmission policy, ADD QOSTEMP)
This parameter is used to configure the attributes of service flows. In the latest IEEE 802.16e
R2D7, this parameter can indicate the following policies:
5-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
– Whether to support broadcast bandwidth requests (whether requests for uplink
bandwidth use the opportunities broadcasted by the BS)
– Whether to support multicast bandwidth requests (whether requests for uplink
bandwidth use the opportunities granted by the BS in multicast mode)
– Whether to support piggyback bandwidth requests (whether to use a tag in the protocol
data header of the uplink services to request bandwidth for the SS; if piggyback
bandwidth requests are supported, the uplink resource efficiency is improved)
– Whether to support segmentation (whether to divide service data units (SDUs) that
exceeds the available resource length into multiple schedulable SDUs during
scheduling; if segmentation is supported, overlong SDUs can be scheduled quickly)
– Whether to support PHS (whether to support load header compression; if load header
compression is supported, bandwidth is saved because only one load header is
transmitted when the same loads and SDUs are transmitted)
– Whether to support packing (whether to merge multiple small SDUs into a large protocol
data unit; if packing is supported, the transmission of protocol data headers is reduced,
and bandwidth is saved)
– Whether to support CRC (whether to perform CRC during the transmission of data; if
CRC is supported, the check results are appended to the protocol data units)
– Whether to support ROHC (ROHC is a highly effective method of compressing RTP/
UDP/IP headers)
In the current versions of Huawei WiMAX BS and ASN-GW, this parameter can indicate
the following policies:
– Whether to support broadcast bandwidth requests
– Whether to support piggyback bandwidth requests
– Whether to support segmentation
– Whether to support PHS
– Whether to support packing
– Whether to support six types of CRC
l Maximum Latency (Maximum latency, ADD QOSTEMP)
This parameter indicates the maximum interval between the reception of a packet at the BS
or SS and the transmission of the packet through the RF port. If the value of this parameter
is too large, the scheduling priority is lowered, and the transmission rate is reduced.
l Tolerated Jitter (Maximum tolerant variation time, ADD QOSTEMP)
This parameter indicates the maximum change in the latency. Generally, signals are not
simply transmitted on communication channels from the transmitter to the receiver in a
point-to-point manner. Instead, signals may be amplified or forwarded by repeaters. There
is a process of storing, processing, and forwarding. In addition, the network conditions
affect the transmission of signals. Therefore, the delay in the same service flow varies. The
variation of latency is measured with jitter. The largest variation that can be tolerated is the
value of Tolerated Jitter. The value of this parameter should be set according to the actual
situations. If the value is too large, the rate is not stable, thereby affecting the service quality.
l SDUFLG (SDU flag, ADD QOSTEMP)
The value of this parameter may be fixed or variable. If the parameter is set to fixed, the
size of the SDU needs to be set. Generally, IP traffic is carried, and the sizes of IP packets
are variable. Therefore, the parameter is set to variable.
l SDUSZ (SDU size, ADD QOSTEMP)
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
When the value of SDU flag is set to fixed, this parameter must be set. The size of the SDU
cannot exceed 254 bytes.
rtPS
The real-time polling service (rtPS) is designed to support real-time uplink service flows that
transmit variable-size packets on a periodic basis, such as MPEG video.
In the rtPS, the BS offers real-time, periodic, and unicast request opportunities, which enable
the service flow to inform the BS of its variable requirements for bandwidth on a periodic basis
so that the BS can grant variable burst bandwidth on a periodic basis for the service flow to
transmit variable-size packets. The rtPS requires more request overheads than the UGS but
supports variable grant sizes for optimum data transport efficiency.
The QoS parameters of the rtPS are as follows:
l Minimum Reserved Traffic Rate (Minimum guaranteed rate, ADD QOSTEMP)
This parameter indicates the minimum data rate reserved by the service flow. The BS offers
the bandwidth required by the minimum data rate reserved by the service flow. If the
bandwidth required by the service flow is less than the reserved bandwidth, the BS can use
the remaining part of the reserved bandwidth for other purposes.
l Request/Transmission Policy (Transmission policy, ADD QOSTEMP)
l Maximum Latency (Maximum latency, ADD QOSTEMP)
l SDUFLG (SDU flag, ADD QOSTEMP)
l SDUSZ (SDU size, ADD QOSTEMP)
l MAXLEN (Maximum burst length, ADD QOSTEMP)
Burst transmission is a type of intermittent data transmission mode. In burst transmission,
data generated at a low rate is buffered by the transmitter. When the buffered data is enough
to form a data group, the data is transmitted at a rate tens of times the rate at which the data
is generated. The receiver buffers the received data and forwards the data to users at normal
rates. The maximum burst length is determined according to the buffering capabilities and
maximum continuous service rate. Within a proper range, an increase in the buffers raises
the transmission rate.
ertPS
The extended real-time polling service (ertPS) is designed to support real-time service flows
that generate variable-size packets on a periodic basis, such as VoIP with silence suppression.
The ertPS is a scheduling mechanism that is built on the benefits of both the UGS and the rtPS.
The BS offers unicast grants in an unsolicited manner like in UGS, thus reducing the delay of
requests for bandwidth. Whereas UGS allocations are fixed in size, ertPS allocations are
dynamic. The BS can provide periodic uplink bandwidth allocations that can be used for
requesting bandwidth and data transmission. By default, the sizes of allocations correspond to
the current value of Maximum Sustained Traffic Rate of the service flow. The SS may request
a change in the size of the uplink allocation by using the Extended Piggyback Request field
of the grant management subheaders or the BR field of the MAC signaling headers or by sending
a codeword over the channel quality indicator channel (CQICH). The BS does not change the
size of uplink allocations until it receives another request for bandwidth change from the SS.
The QoS parameters of the ertPS are as follows:
l Maximum Sustained Traffic Rate (Maximum sustained rate, ADD QOSTEMP)
l Minimum Reserved Traffic Rate (Minimum guaranteed rate, ADD QOSTEMP)
5-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
This parameter indicates the minimum data rate reserved by the service flow. The BS offers
the bandwidth required by the minimum data rate reserved by the service flow. In the ertPS,
the reserved traffic rate is generally configured to be identical to the maximum sustained
traffic rate. On the downlink, bandwidth is allocated according to the data amount but
cannot exceed the maximum sustained traffic rate. On the uplink, the maximum sustained
traffic rate is always allocated. If the remaining bandwidth of the BS is below the maximum
sustained traffic rate when a service flow is established, the service flow cannot be
successfully established.
l Request/Transmission Policy (Transmission policy, ADD QOSTEMP)
l Maximum Latency (Maximum latency, ADD QOSTEMP)
l Tolerated Jitter (Maximum tolerant variation time, ADD QOSTEMP)
l SDUFLG (SDU flag, ADD QOSTEMP)
l SDUSZ (SDU size, ADD QOSTEMP)
l MAXLEN (Maximum burst length, ADD QOSTEMP)
nrtPS
The non-real-time polling service (nrtPS) is designed to support non-real-time uplink service
flows that transmit variable-size packets on a non-periodic basis, such as high-bandwidth FTP
service flows.
The BS offers unicast polls on a regular but not necessarily periodic basis, which ensures that
the service flow receives request opportunities even during network congestion. The service
flow can also send requests for bandwidth in a manner of competition.
The QoS parameters of the nrtPS are as follows:
l Minimum Reserved Traffic Rate (Minimum guaranteed rate, ADD QOSTEMP)
If the bandwidth required by the service flow is less than the reserved bandwidth, the BS
can use the remaining part of the reserved bandwidth for other purposes.
l Maximum Sustained Traffic Rate (Maximum sustained rate, ADD QOSTEMP)
l Request/Transmission Policy (Transmission policy, ADD QOSTEMP)
l SDUFLG (SDU flag, ADD QOSTEMP)
l SDUSZ (SDU size, ADD QOSTEMP)
l MAXLEN (Maximum burst length, ADD QOSTEMP)
BE
The best-effort (BE) service is designed to offer best-effort transmission and has the lowest
priority.
A BE service flow can use transmission opportunities offered by unicast polls or send bandwidth
requests in a manner of competition. The chance of the BE service flow using opportunities
offered by unicast polls depends on the load on the network. If the load on the network is light,
the BE service flow may probably have transmission opportunities. If the load on the network
is heavy, the chance of transmission opportunities is slim or even none. Therefore, when
transmitting BE service flows, the SS cannot relay on transmission opportunities offered by
unicast polls. The network provides no QoS guarantee for BE service flows.
The QoS parameters of the BE service are as follows:
l Maximum Sustained Traffic Rate (Maximum sustained rate, ADD QOSTEMP)
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
l Request/Transmission Policy (Transmission policy, ADD QOSTEMP)
l SDUFLG (SDU flag, ADD QOSTEMP)
l SDUSZ (SDU size, ADD QOSTEMP)
In addition, the BE service has another parameter that indicates the transmission attribute of the
service flow, that is, Traffic Priority (Flow priority, ADD FLOW).
This parameter defines the priority of the transmission. The bigger the parameter is, the higher
the priority is. For example, two service flows having the same QoS parameters except the
priority, so the service flow with a higher priority has lower latency and higher buffering
preference. If some other QoS parameters of the two service flows have different values, the
priority determined by these parameters is preferably considered.
For the detailed attributes and value ranges of the previous parameters, see
#wimax-9-73_table1.
5.3.3 QoS Transmission Control
This describes the QoS transmission control mechanism.
The QoS transmission control mechanism defines the mapping relation between the transmission
bearer priorities and the WiMAX R6 interface transmission resource configuration and traffic.
It addresses many problems, for example, how to guarantee the service QoS, bandwidth utility
rate, and user fairness in the scenarios such as fixed transmission bandwidth, dynamically
changing bandwidth, branching transmission, and load balance. The QoS transmission control
involves the transmission differentiated service, transmission admission control, and
transmission overload control.
Differentiated Transmission Service
In the differentiated transmission service, different priorties are assigned to the user data,
including five types of scheduling service data, signaling data, and maintenance data. This
enables different transmission priorities. Under the circumstance of network congestion, the
traffic with higher priority will take precedence in transmission.
Differentiated transmission services use two types of rules. One is based on the priority indicator
in TOS field of the IP header; the other is the DSCP value in TOS. Currently, only the latter rule
is supported.
Transmission Admission Control
Transmission admission control: Uplink and downlink admission control is implemented
according to the admission thresholds of different types and levels of services. High-priority
services (such as the UGS) of high-priority users (such as handover users) are admitted on a
preferential basis. The number of admitted users is limited with the aim of guaranteeing the
quality of ongoing services.
Transmission Overload Control
In the case of system overload, the transmission overload control mechanism enables the system
to remove low-priority service connections according to the transmission overload treshold and
clearance threshold. When the system load becomes normal, the system congestion is
automatically and quickly cleared.
5-10 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
5.4 Implementation of the QoS Feature
This describes how to activate and deactivate the QoS feature.
5.4.1 Activation of the QoS Feature
When authentication is required, you need to perform operations on the graphic user interface
(GUI) of the Web Management Access System of the AAA to activate the QoS feature for the
R1 interface. For the detailed procedure, refer to the documentation shipped with the AAA.
When authentication is not required, you need to run MML commands on the ASN-GW to
activate the QoS feature for the R1 interface. You need to run MML commands on the M2000
or the LMT of the WiMAX BS to activate the QoS feature for the R6 interface.
5.4.2 Deactivation of the QoS Feature
The QoS is a mandatory feature, so never deactivate the QoS feature.
5.4.1 Activation of the QoS Feature
When authentication is required, you need to perform operations on the graphic user interface
(GUI) of the Web Management Access System of the AAA to activate the QoS feature for the
R1 interface. For the detailed procedure, refer to the documentation shipped with the AAA.
When authentication is not required, you need to run MML commands on the ASN-GW to
activate the QoS feature for the R1 interface. You need to run MML commands on the M2000
or the LMT of the WiMAX BS to activate the QoS feature for the R6 interface.
Procedure
l Run MML commands on the ASN-GW or the AAA to activate the QoS feature for the R1
interface. The procedure for running MML commands on the ASN-GW to activate the QoS
feature for the R1 interface is as follows:
Data collection
– QoS templates for traffic flows
– Template index: 1
– Direction (upward or downward): UPWARD
– Media flow type: VOD
– Scheduling type: UGS
– Transmission policy:
NOBCREQ-0&NOPIGGYBACK-0&NODEFRAG-0&NOSUPPRESS-0&NOPA
CK-0&NOCRC-0 (No transmission policy is employed.)
– SDU flag: Variable
– Maximum sustaining rate: 1171200 bit/s
– Minimum guaranteed rate: 1171200 bit/s
– Maximum jitter duration: 50 ms
– Maximum delay time: 5 ms
– Template index: 2
– Direction (upward or downward): DOWNWARD
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-11
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
– Downlink paging flag: ENABLE (Paging is allowed.)
– Media flow type: VOD
– Scheduling type: UGS
– Transmission policy:
NOBCREQ-0&NOPIGGYBACK-0&NODEFRAG-0&NOSUPPRESS-0&NOPA
CK-0&NOCRC-0 (No transmission policy is employed.)
– SDU flag: Variable
– Maximum sustaining rate: 1171200 bit/s
– Minimum guaranteed rate: 1171200 bit/s
– Maximum jitter duration: 50 ms
– Maximum delay time: 5 ms
– Classifier parameters
– Classifier index: 1
– Protocol type: TCP
– Destination IP address mask: 255.255.255.0
– Destination IP address: 10.1.1.1
– Source IP address mask: 255.255.255.0
– Source IP address: 10.2.2.2
– IP service type/lower limit for DiffServ code point: 0
– IP service type/upper limit for DiffServ code point: 240
– IP service type/DiffServ code point mask: 255
– Classifier index: 2
– Protocol type: TCP
– Destination IP address mask: 255.255.255.0
– Destination IP address: 10.10.10.1
– Source IP address mask: 255.255.255.0
– Source IP address: 10.20.20.2
– IP service type/lower limit for DiffServ code point: 0
– IP service type/upper limit for DiffServ code point: 240
– IP service type/DiffServ code point mask: 255
– Traffic flow templates
– Flow sequence number: 1 and 2
– Direction (upward or downward): UPWARD and DOWNWARD
– Classifier priority: The priority of the classifier with the index 1 is 1 and that of the
classifier with the index 2 is 2.
– QoS template index: 1
– QoS priority: 6 (The value ranges from 0 to 7. A larger value indicates a higher
priority.)
Example script
ADD QOSTEMP: INDEX=1, DIRECT=UPWARD, FLWTYPE=VOD, SDTYPE=UGS,
TSPLCY=NOBCREQ-0&NOPIGGYBACK-0&NODEFRAG-0&NOSUPPRESS-0&NOPACK-0&NOCRC-0,
5-12 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
SDUFLG=Variable, MAXRATE=1171200, MINRATE=1171200, MAXTRTM=50, MAXDLY=5;
ADD QOSTEMP: INDEX=2, DIRECT=DOWNWARD, PGFLG=ENABLE, FLWTYPE=VOD, SDTYPE=UGS,
TSPLCY=NOBCREQ-0&NOPIGGYBACK-0&NODEFRAG-0&NOSUPPRESS-0&NOPACK-0&NOCRC-0,
SDUFLG=Variable, MAXRATE=1171200, MINRATE=1171200, MAXTRTM=50, MAXDLY=5;
ADD CLASSIFIER: INDEX=1, PROTOTYPE=TCP, DSTIP="10.1.1.1",
DSTIPMASK="255.255.255.0", SRCIP="10.2.2.2", SRCIPMASK="255.255.255.0",
TOSLOW=0, TOSHIGH=240, TOSMASK=255;
ADD CLASSIFIER: INDEX=2, PROTOTYPE=TCP, DSTIP="10.10.10.1",
DSTIPMASK="255.255.255.0", SRCIP="10.20.20.2", SRCIPMASK="255.255.255.0",
TOSLOW=0, TOSHIGH=240, TOSMASK=255;
ADD FLOW: SEQNUM=1, DIRECTION=UPWARD, CLASSIFIERINDEX=1, PRECEDENCE=1,
CLASSIFIERINDEX2=2, PRECEDENCE2=2, QoSINDEX=1, FLOWPRI=6;
ADD FLOW: SEQNUM=2, DIRECTION=DOWNWARD, CLASSIFIERINDEX=1, PRECEDENCE=1,
CLASSIFIERINDEX2=2, PRECEDENCE2=2, QoSINDEX=2, FLOWPRI=6;
l Configure four user priorities, that is, golden, silver, copper, and common, on the AAA.
For the detailed configuration modes, see the document shipped with the AAA. By default,
all subscribers are regarded as common subscribers.
l Run the MOD QOSFACTOR command on the M2000 or the LMT of the WiMAX BS to
configure the weighing factors corresponding to the user priorities (namely golden, silver,
copper, and common) based on the operation strategy of the customer.
By default, the weighing factors of the golden, silver, copper, and common subscribers are
4, 3, 2, and 1 respectively.
l Run MML commands on the M2000 or the LMT of the WiMAX BS to activate the QoS
feature for the R6 interface.
When activating the QoS feature for the R6 interface, you need to configure the logical
interface for transmission, IP path, and priorities of differentiated services. Moreover, the
transmission differentiated service, transmission admission control function, and
transmission overload control function can be configured to meet requirements of the
customer.
1. Run the ADD LGCPORT command to configure the logical interface.
For example,
ADD LGCPORT: CN=0, SRN=0, SN=7, LPN=6, SSN=0, PT=ETH, PN=1, TXBW=150000,
RX
BW=150000, TXCBS=200000, TXEBS=200000, TXSSW=OFF, RTMP=6, TXRTFC=26,
RXRTFC=24;
2. Run the ADD IPPATH command to configure the IP path and QoS parameters of the
R6 interface.
For example,
ADD IPPATH: PATHID=128, CN=0, SRN=0, SN=6, LPN=0, LOCALIP="172.16.12.251",
PEERIP="192.168.1.155", PATHTYPE=ANY, PATHCHK=ENABLED;
NOTE
The IP path is configured at a specific logical port, the IP address of the BS is the IP address of the
port, and the IP address of the gateway is the physical or logical IP address of the gateway.
3. Run the SET DIFPRI command to configure the priorities of differentiated services.
NOTE
l Configuring the priorities of differentiated services refers to specifying the DSCP priorities of
services. If this step is not performed, the system uses the default DSCP priorities for services.
l The BS needs to be restarted for the configuration of differentiated services to take effect.
For example, to configure the priorities of differential services (the priority rule is
DSCP, the signaling priority is 48, the VLAN priority for signaling is 6, the OAM
priority is 32, the OAM VLAN priority is 3, the OAMFTP priority is 1, the OMFTP
VLAN priority is 0), run the following command:
SET DIFPRI: PRIRULE=DSCP, SIGPRI=48, SIGVLANPRI=6, OAMPRI=32,
OAMVLANPRI=4, OAMFTPPRI=1, OAMFTPVLANPRI=0, DT1PRI=46, DT1VLANPRI =6
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-13
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
5 QoS Feature Feature Configuration Guide
, DT2PRI=34, DT2VLANPRI=4, DT3PRI=46, DT3VLANPRI=6, DT4PRI=10,
DT4VLANPRI=1, DT5PRI=18, DT5VLANPRI=2, DT6PRI=26, DT6VLANPRI=3, DT7PR
I=0, DT7VLANPRI=0;
4. Run the SET TACALG command to configure transmission admission control.
For example, you need to configure transmission admission control. The uplink and
downlink admission thresholds of high-priority subscribers (handover subscribers)
are 85%, and the uplink and downlink admission thresholds of new subscribers are
75%. That is, when the system load is lower than 75%, all subscribers are admitted.
When the system load is higher than 75% and lower than 85%, only the high-priority
subscribers are admitted. When the system load is higher than 85%, all subscribers
are not admitted. The value of USERDATATYPE5GBR is the fixed bandwidth that
is reserved for non-real-time services such as BE services. To make the preceding
configurations, run the following command:
SET TACALG: TRMULCACSWITCH=ON, TRMDLCACSWITCH=ON, TRMULVIPUSERCACTH=85,
TRMULUSERCACTH=85, TRMDLVIPUSERCACTH=75, TRMDLUSERCACTH=75,
USERDATATYPE5GBR=100, USERDATATYPE1ACTFACTOR=100,
USERDATATYPE2ACTFACTOR=100, USERDATATYPE3ACTFACTOR=100,
USERDATATYPE4ACTFACTOR=100, USERDATATYPE5ACTFACTOR=100;
5. Run the SET TOLCALG command to configure transmission overload control.
For example, to configure the OLC algorithm (the UL OLC algorithm switch is OFF,
the DL OLC algorithm switch is ON, the UL OLC trigger threshold is 100, the UL
OLC release threshold is 0, the DL OLC trigger threshold is 100, the DL OLC release
threshold is 0, OLC time trigger is 0, the OLC action period is 100, the OLC release
bearer No. is 0), run the following command:
SET TOLCALG: TRMULOLCSWITCH=OFF, TRMDLOLCSWITCH=ON, TRMULOLCTRIGTH=100,
TRMULO
LCRELTH=0, TRMDLOLCTRIGTH=100, TRMDLOLCRELTH=0, TRMOLCTIMETRG=0,
TRMOLCACTIONPRD
=100, TRMOLCRELBEARERNUM=0;
----End
Verifying the QoS Feature
You need to access the network with a WiMAX SS and check whether service flows can be
established. If service flows can be established, the QoS feature is successfully activated. If
service flows cannot be established, the QoS feature is not successfully activated.
5.4.2 Deactivation of the QoS Feature
The QoS is a mandatory feature, so never deactivate the QoS feature.
5.5 Maintenance Information of the QoS Feature
This describes the parameters and performance measurement items related to the QoS feature.
Related Parameters
For the detailed information of the QoS parameters, see the documents delivered with the
WASN9770 packet service gateway.
5-14 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 5 QoS Feature
Related Performance Measurement Items
Handover Performance Measurement lists the performance measurement items related to the
QoS feature.
5.6 Reference Information of the QoS Feature
The R1 interface protocol and R6 interface protocol that the QoS feature complies with are IEEE
802.16 REV2 and WiMAX NWG 1.2 respectively.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 5-15
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 6 Handover Feature
6 Handover Feature
About This Chapter
This describes the handover feature of the WiMAX BS. The WiMAX BS supports hard
handovers, including intra-BS handovers and inter-BS handovers.
6.1 Overview of the Handover Feature
This describes the basic information of the handover feature.
6.2 Availability of the Handover Feature
This describes the license and version information of the handover feature and the network
elements involved in it.
6.3 Description of the Handover Feature
This describes handover scenarios and handover processes.
6.4 Implementation of the Handover Feature
This describes how to activate and deactivate the handover feature.
6.5 Maintenance Information of the Handover Feature
This describes the parameters and performance measurement items related to the handover
feature.
6.6 Reference Information of the Handover Feature
This describes the reference information of the handover feature. The handover feature complies
with the protocol Air Interface for Broadband Wireless Access Systems 802.16Rev2/D2.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 6-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
6 Handover Feature Feature Configuration Guide
6.1 Overview of the Handover Feature
This describes the basic information of the handover feature.
Definition
When the MS moves from one cell to another, the signal strength of the source cell becomes
weak whereas that of the target cell becomes strong, because of reasons such as distance. To
obtain better signal quality and ensure service continuity, the MS switches to the target cell. This
process is known as a handover, which is a major function enabling mobility management in
wireless communications.
The Huawei WiMAX BS supports handovers between the same frequency points of different
sectors. Intra-frequency handovers can be initiated by the MS or BS.
The Huawei WiMAX BS supports handovers between different frequency points of the same
sector or different sectors. Inter-frequency handovers can be initiated by the MS or BS.
Purpose
The purpose of handovers is to provide better service quality and ensure service continuity.
When the radio channels change or the BS is overloaded, the BS requires the terminal to initiate
a handover so that the terminal obtains better signal quality or service continuity. The MS itself
can also initiate handovers.
Specifications
None.
Impact
Improper network planning may cause frequent handovers, which affect subscriber services.
Terms
Term Definition
R6 interface This is the interface between the BS and the GW.It supports signaling
exchange between the BS and the GW and the setup of R6 tunnel to carry
the traffic of the MS.
Hard handover A hard handover is a handover in which the terminal is disconnected from
the source cell before a connection is established between the terminal and
the target cell.
Abbreviations and Acronyms
Abbreviation or Acronym Full Spelling
MS Mobile Station
6-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 6 Handover Feature
Abbreviation or Acronym Full Spelling
BS Base Station
BWA Broadband Wireless Access
6.2 Availability of the Handover Feature
This describes the license and version information of the handover feature and the network
elements involved in it.
Network Elements Involved
The handover feature requires the joint work of the SS/MS and the BS. Table 6-1 lists the
network elements involved in the handover feature.
Table 6-1 Network elements involved in the handover feature
ASN AAA DHCP
SS/MS BS -GW Server Server M2000
√ √ √ - - √
NOTE
In Table 6-1, √ is used to mark the network elements involved in this feature, and - is used to mark the
network elements not involved in this feature.
Supporting Versions
Table 6-2 lists the versions that support the handover feature.
Table 6-2 Versions that support the handover feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Support
This feature is subject to license restrictions.
6.3 Description of the Handover Feature
This describes handover scenarios and handover processes.
Handover Processes
An entire handover consists of the following processes:
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 6-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
6 Handover Feature Feature Configuration Guide
1. Handover preparation
2. Handover triggering
3. Network reentry
MS-Initiated Handover
Handover Preparation
1. The MS obtains the information of the neighboring BSs.
2. The serving BS sends the broadcast message MOB_NBR_ADV, which carries the
information of the neighboring BSs, to the MS.
3. The MS obtains the information of neighboring BSs through scanning.
4. The MS receives the broadcast message MOB_NBR-ADV from the BS, scans the signals
of the neighboring cells, obtains the downlink information, and issues a neighboring cell
scanning report. According to quality comparison, the MS selects a proper target cell for
the handover.
Handover Triggering
The MS can initiate a handover request according to the trigger configured by the BS. The
message carries the list of target BSs, and the MS can identify the measured values of the target
BSs according to the indicator bits.
Network Reentry
Network reentry refers to the process in which the MS enters the network again through the
target BS after sending the MOB_HO-IND message to the source BS. Different from the initial
network entry process, the network reentry process involves optimization. The target BS
implements optimization according to the MS information obtained from the source BS. The
target BS sends the optimization instruction to the MS through the RNG RSP message, and then
the MS performs network reentry optimization according to the optimization instruction. The
optimization of the process expedites network reentry and reduces the handover delay.
BS-Initiated Handover
Handover Preparation
In a scanning handover initiated by the BS, the BS detects that specific conditions are met and
then sends a scanning response to the MS. The response message carries a recommended list of
target BSs. After receiving the scanning response, the MS starts a scanning process and sends
the scanning report to the BS. After receiving the scanning report, the BS checks whether the
conditions for an outgoing handover are met. If the conditions are met, the BS sends a handover
request to the MS, which triggers a handover. Currently, the BS supports scanning triggered by
the following three conditions:
l When the BS detects that the uplink CINR of the MS is below the value of
SCANCINRBADTHRESH, a scanning process is triggered.
l When the BS detects that the PER of the MS is below the value of
SCANPERRBADTHRESH, a scanning process is triggered.
l When the BS detects that the load on a BS is above the value of LOADOUTTHRESH, a
scanning process is triggered by an MS that is heavily loaded. The scanning process is
stopped when any of the following conditions is met:
– The load on the BS is below the value of LOADOUTSTOPTHRESH.
6-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 6 Handover Feature
– The value of LOADOUTMAXUSERNUM is exceeded.
The preceding three conditions can be used as the same time. In this case, the BS triggers a
handover process using the method whose condition is met first. A new handover process is not
triggered before the current handover process is complete.
Handover Triggering
A scanning handover process is triggered if the thresholds are properly set, scanning handovers
are enabled, and conditions are met. See detailed steps on how to perform proper configurations.
Network Reentry
Network reentry refers to the process in which the MS enters the network again through the
target BS after sending the MOB_MSHO-IND message to the source BS. Different from the
initial network entry process, the network reentry process involves optimization. The target BS
implements optimization according to the MS information obtained from the source BS. The
target BS sends the optimization instruction to the MS through the RNG RSP message, and then
the MS performs network reentry optimization according to the optimization instruction. The
optimization of the process expedites network reentry and reduces the handover delay.
6.4 Implementation of the Handover Feature
This describes how to activate and deactivate the handover feature.
6.4.1 Activating the Handover Feature
This describes how to activate the handover feature. Handover requires neighboring cells. At
present, a maximum of 30 neighboring cells is supported. The configured active neighboring
cells must be available so that the coverage environments required by handovers are available.
At the same time, the following configurations must be complete, and the MS must be able to
enter the network through the configured neighboring cells.
6.4.2 Deactivating the Handover Feature
This describes how to deactivate the handover feature.
6.4.1 Activating the Handover Feature
This describes how to activate the handover feature. Handover requires neighboring cells. At
present, a maximum of 30 neighboring cells is supported. The configured active neighboring
cells must be available so that the coverage environments required by handovers are available.
At the same time, the following configurations must be complete, and the MS must be able to
enter the network through the configured neighboring cells.
Prerequisite
The licenses are activated.
NOTE
For details on how to upload, distribute, and query licenses for the DBS3900 WiMAX, see the M2000
Online Help.
Procedure
l Activate MS-initiated handovers.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 6-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
6 Handover Feature Feature Configuration Guide
1. On the M2000 client or Web LMT, run the MOD MACCAPABILITY command,
with the value of the parameter Support for mobility (MOBFEATURESUPP) set
to 1, which indicates that the BS supports handovers.
Check the value of bit 0 of the parameter Support for mobility
(MOBFEATURESUPP). If the value of the bit is 1, the handover feature is supported.
If the value of the bit is 0, the handover feature is not supported.
NOTE
The value range of the parameter Support for mobility (MOBFEATURESUPP) is 0–7.
l Bit 0: Mobility (HO) support
l Bit 1: Sleep mode support
l Bit 2: Idle mode support
If the value of the parameter Support for mobility (MOBFEATURESUPP) is 7, the BS
supports the handover, sleep mode, and idle mode.
2. Configure sector carriers on the M2000 client or Web LMT.
Run the DSP CARRIERSTATUS command to query the status of source sector
carriers and target sector carriers.
NOTE
The coverage environment required by handovers can be guaranteed only when the source
sector carrier and target sector carrier are active and available. In addition, the MS must be able
to enter the network through the configured sector carriers successfully.
3. Run the LST NBR command to query the configured neighboring cells.
For example, you need to query the neighboring relations, the BSID of the central BS
is 0000-2E00-6400, and the BSID of the neighboring BS is 0000-2F00-7000. Run the
following command: LST NBR: CBSID="0000-2E00-6400",
NBRBSID="0000-2f00-7000";
4. Run the ADD NBR command to add the neighboring cell relations.
For example, to add the neighboring cell relation between the central BS with BSID
0000-2E00-6400 and the neighboring BS with BSID 0000-2F00-7000, run the
following command: ADD NBR: CBSID="0000-2E00-6400",
NBRBSID="0000-2F00-7000";
5. Run the LST TRIGGER command to query the trigger information.
For example, to query the information of trigger 0 of carrier 0 under sector 0, run the
following command: LST TRIGGER:SECTORID = 0,CARRIERID =
0,TRIGGERID = 0;
6. Run the ADD TRIGGER command to configure the trigger information.
For example, to add the trigger information in a case where the sector number is 0,
the carrier number is 0, the trigger type is 1, the trigger function is 1, the trigger action
is 1, the trigger value is 1, and the trigger interval is 1, run the following command:
ADD TRIGGER: SECTORID=0, CARRIERID=0, TRIGGERID=1,
TRIGGERTYPE=1, TRIGGERFU NCTION=1, TRIGGERACTION=1,
TRIGGERVALUE=1, TRIGGERAVERDURATION=1;
l Activate BS-initiated handovers.
To activate BS-initiated handovers, you need to perform the preceding six steps and then
perform the step that follow.
1. Run the LST HOPARA command to query the handover parameters of the BS.
6-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 6 Handover Feature
For example, you need to query the handover parameters of a BS, the sector ID is 0,
and the carrier ID is 0. Run the following command:
LST HOPARA:
The following information is displayed:
MML% LST HOPARA:SECTORID = 0,CARRIERID = 0;
+++ HUAWEI 2008-03-30 07:34:52
O&M #42
%%LST HOPARA:SECTORID = 0,CARRIERID = 0;%%
RETCODE = 0 Operation succeeded
HO
PARA
-------
SECTORID =
0
CARRIERID =
0
LOADOUTTHRESH(Unit:1/100) =
90
LOADINTHRESH(Unit:1/100) =
60
LOADOUTSTOPTHRESH(Unit:1/100) =
80
LOADOUTMAXUSERNUM = 5
SCANCINRBADTHRESH(Unit:dB) = 15
SCANPERRBADTHRESH(Unit:1/100) = 5
HOCINRTHRESH(Unit:dB) = 3
HOPERRTHRESH(Unit:dB) = 3
HODIFFREQTHRESH(Unit:dB) =
3
ULCINRHOSWITCH =
OFF
ULPERHOSWITCH =
OFF
LOADHOSWITCH = OFF
DIFFREQPRIORHOSWITCH = OFF
PERWEIGHT =
5
MEAREPTIMELEN(Unit:ms) = 1000
LOADHOTIMELEN(Unit:ms) = 120000
HOPINGPANGDELAYLEN(Unit:ms) = 60000
SCANDURATION(Unit:Frame) = 20
SCANINTERVAL(Unit:Frame) = 10
SCANITERATION =
3
(Number of results = 1)
--- END
NOTE
l When the value of the parameter DIFFREQHOSWITCH is set to ON and the frequency
point of the target BS detected by the MS belongs to an inter-frequency neighboring cell,
handover decision is performed according to the value of the parameter
HODIFFREQTHRESH, and an intra-frequency handover is initiated.
l When the value of the parameter DIFFREQHOSWITCH is set to OFF, an inter-frequency
handover is not initiated even if the MS detects an inter-frequency neighboring cell.
l If the MS detects an intra-frequency neighboring cell, an inter-frequency handover is not
performed, regardless of the value of the parameter DIFFREQHOSWITCH.
2. Run the MOD HOPARA command, with the value of the parameters
ULCINRHOSWITCH, ULPERHOSWITCH, LOADHOSWITCH, and
DIFFREQHOSWITCH set to ON.
For example, you need to modify the handover parameters of a BS, the sector ID is 0,
and the carrier ID is 0. Run the following command:
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 6-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
6 Handover Feature Feature Configuration Guide
MOD HOPARA: ULCINRHOSWITCH=ON, ULPERHOSWITCH=ON, LOADHOSWITCH=ON,
DIFFREQHOSWITCH=ON;
----End
6.4.2 Deactivating the Handover Feature
This describes how to deactivate the handover feature.
Procedure
Step 1 On the M2000 client or Web LMT, run the MOD MACCAPABILITY command, with the
value of the parameter Support for mobility (MOBFEATURESUPP) set to 0, which indicates
that the BS does not support handovers.
Step 2 Run the RMV NBR command to remove the neighboring cell relations so that the MS cannot
find target neighboring cells for handovers.
For example, you need to remove the neighboring cell relations, the central BSID is
0000-2E00-6400, and the BSID of the neighboring cell is 0000-2F00-7000. Run the following
command:CBSID="0000-2E00-6400", NBRBSID="0000-2F00-7000";
Step 3 Run the MOD HOPARA command, with the value of the parameters
ULCINRHOSWITCH, ULPERHOSWITCH, LOADHOSWITCH, and
DIFFREQHOSWITCH set to OFF.
----End
6.5 Maintenance Information of the Handover Feature
This describes the parameters and performance measurement items related to the handover
feature.
Related Parameters
Table 6-3, Table 6-4, and Table 6-5 list the parameters related to the handover feature.
Table 6-3 Parameters of the ADD NBR command
Parameter Meaning
CBSID BSID of the central BS
NBRBSID BSID of the neighboring cell
Table 6-4 Parameters of the MOD CARRIERBLOCKFLAG command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
BLOCKFLAG Block flag of the carrier
6-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 6 Handover Feature
Table 6-5 Parameters of the MOD HOPARA command
Parameter Meaning
LOADOUTTHRESH Threshold for load balance outgoing handovers
LOADINTHRESH Threshold for load balance incoming handovers
LOADOUTSTOPTHRESH Threshold for stopping load balance outgoing
handovers
LOADOUTMAXUSERNUM Maximum number of subscribers for load balance
outgoing handovers
SCANCINRBADTHRESH Threshold for BS initiating scanning triggered by the
uplink CINR
SCANPERBADTHRESH Threshold for BS initiating scanning triggered by the
uplink PER
HOCINRTHRESH Threshold for outgoing handovers triggered by the
uplink CINR
HOPERTHRESH Threshold for outgoing handovers triggered by the
uplink PER
HODIFFREQTHRESH Switch for outgoing inter-frequency handovers
ULCINRHOSWITCH Switch for decision on uplink CINR handovers
ULPERHOSWITCH Switch for decision on uplink PER handovers
LOADHOSWITCH Switch for load balance hard handovers
DIFFREQHOSWITCH Switch for inter-frequency handovers
Related Performance Measurement Items
Handover Performance Measurement lists the performance measurement items related to the
handover feature.
6.6 Reference Information of the Handover Feature
This describes the reference information of the handover feature. The handover feature complies
with the protocol Air Interface for Broadband Wireless Access Systems 802.16Rev2/D2.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 6-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 7 Automatic Discovery Feature
7 Automatic Discovery Feature
About This Chapter
This describes the automatic discovery feature, which is the application of DHCP in the WiMAX
system.
7.1 Overview of the Automatic Discovery Feature
This describes the basic information of the automatic discovery feature.
7.2 Availability of the Automatic Discovery Feature
This describes the network elements involved in the automatic discovery feature and the earliest
versions that support this feature.
7.3 Description of the Automatic Discovery Feature
This describes the principle, application scenarios, and process of the automatic discovery
feature.
7.4 Implementation of the Automatic Discovery Feature
This describes how to activate and deactivate the automatic discovery feature.
7.5 Maintenance Information of the Automatic Discovery Feature
This describes the parameters and performance measurement items related to the automatic
discovery feature.
7.6 Reference Information of the Automatic Discovery Feature
This describes the protocols and specifications that the automatic discovery feature complies
with.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 7-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
7 Automatic Discovery Feature Feature Configuration Guide
7.1 Overview of the Automatic Discovery Feature
This describes the basic information of the automatic discovery feature.
Definition
Automatic discovery is a function that automatically assigns OM IP addresses to the BSs through
the DHCP function and establishes OMLs between the M2000 and the BSs so that the BSs are
automatically managed by the M2000 in a centralized manner.
Purpose
The automatic discovery feature effectively simplifies local maintenance of the BSs. With this
feature, local software commissioning is not necessary during site deployment.
After the BS is powered on, the DHCP server automatically assigns the BS the parameters
required for the establishment of the OML. Then, the OML between the M2000 and the BS is
automatically established. All the software commissioning work on the BS can be performed
on the management center in a centralized manner. In this way, the maintenance cost is lowered.
Specifications
None.
Impact
l The automatic discovery feature is mainly used during site deployment. If automatic
discovery fails during site deployment, local software commissioning must be performed.
In this case, remote centralized configuration is not possible.
l The automatic discovery feature does not interfere with the daily operation of the system.
l The information about the OML established through the automatic discovery feature is not
saved to the data configuration file. Therefore, engineers need to use MML commands on
the M2000 to manually configure the OML information of the network element for future
use and maintenance.
l If the OML parameters need to be configured manually, the DHCP function must be
disabled first, and the parameter configuration must be consistent with that on the DHCP
server. Otherwise, the DHCP function modifies the manually configured parameter values
in the case of intermittent interruptions of the OML, and the OML may malfunction.
Terms
Term Definition
OML Link between the BS and the M2000 for operation and maintenance
7-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 7 Automatic Discovery Feature
Abbreviations and Acronyms
Abbreviation or
Acronym Full Spelling
BS Base Station
DHCP Dynamic host configuration protocol
EMS Element management system
MS Mobile Station
OM Operation and maintenance
SS Subscriber Station
ESN Electronic Serial Number
7.2 Availability of the Automatic Discovery Feature
This describes the network elements involved in the automatic discovery feature and the earliest
versions that support this feature.
Network Element Involved
The automatic discovery feature requires the joint work of the SS/MS and the BS. Table 7-1
lists the network elements involved in the automatic discovery feature.
Table 7-1 Network elements involved in the automatic discovery feature
ASN
SS/MS BS -GW AAA Server M2000
- √ - - √
NOTE
In Table 7-1, √ is used to mark network elements that are involved in this feature, and - is used to mark
network elements that are not involved in this feature.
Supporting Versions
Table 7-2 lists the versions that support the automatic discovery feature.
Table 7-2 Versions that support the automatic discovery feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Support
This feature is not subject to license restrictions.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 7-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
7 Automatic Discovery Feature Feature Configuration Guide
7.3 Description of the Automatic Discovery Feature
This describes the principle, application scenarios, and process of the automatic discovery
feature.
Principle Description
The automatic discovery feature is achieved through the DHCP server configured on the M2000.
The DHCP server configured on the M2000 server is responsible for allocating IP addresses for
the BSs. This server is different from the DHCP server that is responsible for allocating IP
addresses for the terminals. The DHCP server is responsible for assigning BSs configuration
parameters related to the operation and maintenance links (OMLs), for example, OM IP
addresses. After a BS configures its own OM transmission parameters, it can establish an OML
to communicate with the M2000. Meanwhile, with the cooperation of the DHCP server, the BS
and M2000 can interact to achieve mutual discovery. In this way, the M2000 manages the BSs
in a centralized manner.
This feature enables the following functions:
l After a BS is powered on, it automatically obtains the OML parameters through the DHCP
protocol to establish the OML.
l The M2000 automatically discovers and manages network elements.
Application Scenarios
Generally, the BSs are converged on the bearer network and connected to the ASN-GW and
M2000.
When the M2000 and the BS are configured in the same network segment, the DHCP broadcast
messages from the BS can be sent to the DHCP server on the M2000 directly through the IP
bearer network.
When the M2000 and the BS are not configured in the same network segment, the DHCP relay
service needs to be configured on the layer 3 switching device that is configured on the IP bearer
network and closest to the BS. The broadcast messages are sent to the DHCP server on the
M2000 through the layer 3 switching network.
After a BS is powered on, it requests its own OM transmission parameters from the DHCP server
on the M2000 through the DHCP protocol. These parameters are used to establish the OML
between the BS and the M2000. In order for the DHCP broadcast packets from the BS to be sent
over the IP bearer network and received by the M2000, the DHCP relay service needs to be
configured on the layer 3 switching equipment closest to the BS on the bearer network so that
the broadcast packets from the BS are converted to unicast packets and sent to the DHCP server
on the M2000 through the layer 3 switching network. The detailed configuration is related to
the network segment information of the subnetwork served by the relay server and the IP address
of the destination DHCP server. For details on the configuration commands and procedure, see
the manuals of the specific equipment.
Principle
The automatic discovery feature is used mainly during site deployment. The user needs to plan
the OM transmission parameters of the BSs. After each BS is powered on at the site, it
automatically establishes an OML between itself and the M2000. In this way, the maintenance
7-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 7 Automatic Discovery Feature
personnel can perform centralized maintenance for the BSs on the M2000. The principle of this
feature is as follows:
1. The user plans OM transmission parameters for each BS on the network according to the
actual situations of the bearer network and the details of network planning. Table 7-3 lists
the OM transmission parameters.
2. The user types the information in the parameter table on the DHCP server on the M2000.
The parameter table can take the form of an Excel worksheet, which can be imported to
the DHCP server. At this time, the DHCP already can provide services. This Excel template
can be obtained from the DHCP server configuration tool. The user only needs to export
the worksheet from the tool.
3. The user installs the hardware and powers on the BS.
NOTE
If the ESN of the BS cannot be determined, the user needs to report the ESN and physical location
to the personnel at the network management center and ask them to record the ESN on the DHCP
server.
4. By interacting with the DHCP server, the BS obtains its own OM transmission parameters.
5. The BS validates the OM transmission parameters that it obtains.
6. The M2000 automatically creates the BS in the topology view and establishes an OM
management link between itself and the BS.
7. The user manages the BS in remote mode and performs software commissioning through
the M2000.
The parameters listed in Table 1 are crucial to the establishment of the OML. If parameter
planning is incorrect, the network management center may fail to manage the BS. In this case,
the configurations of the DHCP server on the M2000 and of the topology on the M2000 need
to be modified so that the BS can be managed through the network management center in remote
mode. Some parameters, mainly the OM IP address of the BWA, listed in Table 1 need to be
modified.
If the DHCP switch is set to ON, the BS originates a DHCP request to reconnect to the M2000
after detecting that it is disconnected from the M2000 for a period of time. The OML parameters
obtained through the DHCP protocol are not written into the configuration data of the BS and
therefore not permanently saved after the BS is powered off. If the OML parameters need to be
written into the configuration data after automatic discovery is performed, you need to run
associated MML commands to configure OML parameters the same as those planned on the
DHCP server. Otherwise, the BS automatically uses the parameters saved in the configuration
data and may break away from the management of the M2000.
7.4 Implementation of the Automatic Discovery Feature
This describes how to activate and deactivate the automatic discovery feature.
7.4.1 Activating the Automatic Discovery Feature
This describes how to activate the automatic discovery feature.
7.4.2 Deactivating the Automatic Discovery Feature
This describes how to deactivate the automatic discovery feature.
7.4.1 Activating the Automatic Discovery Feature
This describes how to activate the automatic discovery feature.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 7-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
7 Automatic Discovery Feature Feature Configuration Guide
Prerequisite
l The M2000 works properly, and the M2000 client is functional.
l The DHCP server assigning IP addresses for the BSs is already deployed, and the DHCP
software is already installed. The DHCP server can be deployed on the same computer as
the M2000.
l The DHCP relay service is available on the layer 3 switch that is closest to the BS among
all the layer 3 switches between the BS and the M2000, and the relay parameters are
configured. After the configuration, DHCP broadcast messages from the BSs can reach the
M2000, and response messages from the M2000 can be received by the BSs.
Data Preparation
When configuring the BS data through the WCS, you need to create NEs on the M2000 topology.
Fill the planned NE information in the DHCP Parameter Template, and then create NEs in
batches through the DHCP tool.
NOTE
l You do not need to fill BWA_IP_ALLOC_STATUS in the DHCP Parameter Template.
l All the parameters except BWA_IP_ALLOC_STATUS and DBS3900 WiMAX Esn are mandatory
for creating NEs.
l If you fail to obtain the ESN of an NE, create the NE on the topology by using the default ESN. After
obtaining the ESN of the NE, fill the ESN.
l If you fill the correct ESN when creating an NE, the OM links between the BS and the M2000 are
automatically set up after the BS is powered on.
Table 7-3 DHCP parameters
Parameter Description Example
DBS3900 WiMAX Name It is an NE name. wimax
DBS3900 WiMAX ESN It is the ESN of an NE and is 2102120275P08A000109
used uniquely for identifying
an NE. The ESN is attached
on the BBU before delivery.
During engineering
installation, the installation
engineer reports the mapping
between the position of each
site and the ESN.
ASN-GW IP It is the IP address of the 172.16.45.10
gateway server.
7-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 7 Automatic Discovery Feature
Parameter Description Example
DBS3900 WiMAX OM It is the VLAN ID used for Default value: 0
Channel VLAN ID the OM channel. If the
maintenance network is
VLAN networking, and the
broadcast messages without
the VLAN ID cannot be
transmitted on the OM
channel, you need to
configure the VLAN ID.
DBS3900 WiMAX Interface It is the ITFIP of the OM 172.16.12.123
IP channel.
DBS3900 WiMAX Interface It is the mask of the ITFIP of 255.255.255.0
IP Mask the OM channel.
DBS3900 WiMAX OM IP It is the logical IP address of 172.16.12.11
the OM channel and can be
the same as the ITFIP. It is
used for the connection
between the BTS and the
M2000.
DBS3900 WiMAX OM IP It is the mask of the OM IP 255.255.255.0
Mask address.
M2000 IP It is the IP address of the 192.168.10.105
M2000.
BWA_M2000_NETMASK It is the mask of the IP 255.255.255.255
address of the M2000.
DBS3900 WiMAX OM Next It is the IP address of the next 172.16.12.1
IP equipment of the OM
channel and is provided by
the network planner or
operator.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 7-7
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
7 Automatic Discovery Feature Feature Configuration Guide
Parameter Description Example
DBS3900 WiMAX OM It is the detection IP address 192.168.10.105
Channel Detection IP of the OM channel and is
used to check whether the
route from an NE to the
M2000 is operational.
Generally, the detection IP
address of the OM channel is
the same as the IP address of
the M2000. If the M2000 is
configured with the firewall,
you cannot successfully ping
the M2000 through the
computer connected to the
BTS. In this case, the
detection IP address of the
OM channel is the IP address
of the switching equipment
on the lower layer, for
example, the IP address of the
switch closest to the M2000.
Procedure
Step 1 Copy the filled DHCP parameter template to a folder under a path of the M2000 client.
Step 2 On the iManager M2000 Mobile Element Management System, choose Configuration >
DHCP Configuration Tool. The DHCP Configuration Tool interface is displayed, as shown
in Figure 7-1.
7-8 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 7 Automatic Discovery Feature
Figure 7-1 DHCP Configuration Tool interface
If the login fails, the system displays the following message Server may be not running. System
will be exit!. In this case, log in to the M2000 server as the superuser in Telnet mode, and then
run the start_dhcpserver command to start the DHCP service.
If the system displays the following message DHCPServer start succeed!, you can
infer that the DHCP service is started successfully.
Step 3 In the DHCP Configuration Tool interface, click , select the DHCP parameter template,
and then import the DHCP parameters to the DHCP server.
Click the DBS3900 Wimax tab to view the imported data.
Step 4 On the iManager M2000 Mobile Element Management System, choose Topology > Main
Topology to view the Main Topology tab page.
Step 5 On the Main Topology tab page, select the ASN-GW to be connected to the NE, right-click the
ASN-GW, and then select Search BTS from the shortcut menu.
All the NEs imported by the DHCP tool are displayed on the Main Topology tab page. Creating
NEs is complete.
----End
7.4.2 Deactivating the Automatic Discovery Feature
This describes how to deactivate the automatic discovery feature.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 7-9
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
7 Automatic Discovery Feature Feature Configuration Guide
Procedure
Run the SET DHCPFUNC command, with the value of the parameter STRFLG set to
DISABLE.
CAUTION
If this command is successfully run, the BS does not automatically originate DHCP requests. In
this case, if the manually configured OM IP address is faulty, the network management center
cannot manage the BS. Therefore, you should be cautious about running this command.
----End
7.5 Maintenance Information of the Automatic Discovery
Feature
This describes the parameters and performance measurement items related to the automatic
discovery feature.
Related Parameters
Table 7-4 lists the parameters related to the automatic discovery feature.
Table 7-4 Parameters of the SET DHCPFUNC command
Parameter Meaning
STRFLG DHCP function switch
TMTHD OML detection cycle
By default, the DHCP function is enabled for the BS. Unless necessary, do not disable the DHCP
function of a BS by using this command.
Related Performance Measurement Items
None
7.6 Reference Information of the Automatic Discovery
Feature
This describes the protocols and specifications that the automatic discovery feature complies
with.
l RFC2131 Dynamic Host Configuration Protocol R. Droms [March 1997]
l RFC2132 DHCP Options and BOOTP Vendor Extensions S. Alexander, R. Droms [March
1997]
7-10 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 8 FFR Feature
8 FFR Feature
About This Chapter
FFR is an enhanced function of the WiMAX system.
8.1 Overview of the FFR Feature
FFR is an enhanced function of the WiMAX system.
8.2 Availability of the FFR Feature
This describes the network elements and version information involved in the FFR feature.
8.3 Description of the FFR Feature
This describes the principle of the FFR feature in terms of networking modes and zone switching.
8.4 Implementation of the FFR Feature
This describes how to activate and deactivate the FFR feature.
8.5 Maintenance Information of the FFR Feature
This describes the parameters and performance measurement items related to the FFR feature.
8.6 Reference Information of the FFR Feature
The FFR complies with the IEEE 802.16e standard.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 8-1
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
8 FFR Feature Feature Configuration Guide
8.1 Overview of the FFR Feature
FFR is an enhanced function of the WiMAX system.
Definition
FFR is an enhanced function of the WiMAX system. With this function, one frequency point
can have PUSC zones and PUSC with all SC zones on the uplink or downlink. The BS instructs
the MS to switch between different zones according to the signal quality.
Purpose
The FFR networking mode is a hybrid networking mode. In this mode, all the BSs uses the same
frequency point. At the borders of cells, only some of the sub-carriers are used to guarantee
coverage. In areas where the signal quality is good, all the sub-carriers are used to guarantee
efficient use of frequency spectrum resources.
Specifications
None.
Impact
None.
Terms
Term Definition
Zone A zone comprises a group of OFDMA symbols that uses the same
substitution formula. The PUSC zone is an example.
Zone switching In FFR networking mode, the BS instructs the MS to switch between
partial use of sub-carriers and use of all sub-carriers according to the
signal quality.
PUSC(1,1,3) In PUSC(1,1,3) networking mode, the entire network uses one
networking mode frequency point, and only PUSC sub-channels are configured on the
uplink or downlink for each sector. In PUSC(1,3,3) networking mode,
the entire network uses three frequency points, and only PUSC with all
SC sub-channels are configured on the uplink or downlink for each
sector.
FFR(1,1,3) In FFR(1,1,3) networking mode, the entire network uses on frequency
networking mode point. PUSC sub-channels and PUSC with all SC sub-channels are
configured on the uplink or downlink for each sector.
8-2 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 8 FFR Feature
Abbreviations and Acronyms
Abbreviatio Full Spelling
n or
Acronym
PUSC Partial Usage Of Subchannels
CINR Carrier-to-Interference-and-Noise Ratio
RSSI Receive Signal Strength Indicator
FFR Fractional Frequency Reuse
BS Base Station
8.2 Availability of the FFR Feature
This describes the network elements and version information involved in the FFR feature.
Network Element Involved
Table 8-1 lists the requirements of the FFR feature for the network elements.
Table 8-1 Requirements of the FFR feature for network elements
SS/MS BS ASN-GW AAA Server M2000
√ √ - - -
NOTE
In Table 8-1, √ is used to mark network elements that are involved in this feature, and - is used to mark
network elements that are not involved in this feature.
Supporting Versions
Table 8-2 lists the versions that support the FFR feature.
Table 8-2 Versions that support the FFR feature
Product Version
BS DBS3900 WiMAX V300R002C02
License Support
This feature is not subject to license restrictions.
8.3 Description of the FFR Feature
This describes the principle of the FFR feature in terms of networking modes and zone switching.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 8-3
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
8 FFR Feature Feature Configuration Guide
The WiMAX BTS supports networking modes such as PUSC(1,1,3), PUSC with all SC(1,3,3),
and FFR(1,1,3). In FFR networking mode, the zone switching function is used to ensure that the
MS can switch between different zones. In this way, co-channel interference is avoided.
Networking Modes
PUSC with all SC(1,3,3) Networking Mode
In PUSC with all SC(1,3,3) networking mode, the three sectors of a BTS use different frequency
points, and each sector uses the PUSC with all SC method on the uplink and downlink. This
networking mode is applicable to operators that have sufficient frequency resources. In this
mode, co-channel interference between BTSs is avoided, and the throughput of each sector and
the entire network is guaranteed.
Figure 8-1 PUSC with all SC(1,3,3) networking mode
PUSC(1,1,3) Networking Mode
In PUSC(1,1,3) networking mode, each of the three sectors of a BTS use one-third of the sub-
channels at the same frequency point. Assume that the bandwidth is 10 MHz, and there are totally
30 downlink sub-channels and 35 uplink sub-channels. In PUSC(1,1,3) networking mode, each
sector uses 10 downlink sub-channels, and the three sectors use 12, 12, and 11 uplink sub-
channels respectively.
This networking mode is applicable to operators that have only one frequency point. In this
mode, co-channel interference does not occur between BTSs. The drawback to this networking
mode is reduced sector throughput because each sector uses only one-third of the sub-channels.
8-4 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 8 FFR Feature
Figure 8-2 PUSC(1,1,3) networking mode
FFR(1,1,3) Networking Mode
In FFR(1,1,3) networking mode, the entire network uses one frequency point. Areas far from
the BTS uses the PUSC substitution mode, and each of the three sectors of a BTS use one-third
of the sub-channels at the same frequency point, as shown by the blue area in Figure 8-3. Zones
close to the BTS uses the PUSC with all SC substitution mode, and the three sectors of the BTS
uses all the sub-channels at a frequency point.
The FFR(1,1,3) networking mode is superior to the PUSC(1,1,3) networking mode in that the
former can both guarantee coverage at borders and improve the throughput of the entire BTS.
The FFR(1,1,3) networking mode requires a precise and fast zone switching algorithm. The BTS
switches the MS to a proper zone according to the uplink and downlink conditions of the MS.
Figure 8-3 FFR(1,1,3) networking mode
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 8-5
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
8 FFR Feature Feature Configuration Guide
Zone Switching
Zone Switching Process
1. In FFR networking mode, the MS enters the PUSC zone by default after entering the
network. If the PUSC zone resources are not sufficient, the MS enters the PUSC with all
SC zone.
2. When the MS is in the PUSC zone, it reports the CINR of the downlink PUSC zone in real
time. After receiving the CINR from the MS, the BS decides whether the CINR exceeds
the zone switching measurement threshold. If the CINR exceeds the zone switching
measurement threshold, the BS requires the MS to measure the CINR of the PUSC with
all SC zone. If the average CINR of all the sub-channels in a period of time exceeds the
threshold for switching from one-third of the sub-carriers to all the sub-carriers, the BS
switches the MS from the 1/3-sub-carrier zone to the all-sub-carrier zone.
3. When the MS is in the PUSC with all SC zone, it reports the CINRs of all the downlink
sub-carriers in real time. After receiving the CINRs reported by the MS, the BS decides
whether they exceed the threshold for switching from all the sub-carriers to one-third of
the sub-carriers. If they exceed the threshold for switching from all the sub-carriers to one-
third of the sub-carriers, the BS switches the MS from the all-sub-carrier zone to the 1/3-
sub-carrier zone.
Settings of Parameters Related to Zone Switching
1. You can run the MOD CARRIERZONEINFO command to set the zone type.
MOD CARRIERZONEINFO: SECTORID=0, CARRIERID=0, DLZONENUM=2, DLZONEIND=9,
DL2NDSTARTSYMBOL=21, DL2NDZONESCHNUM=30, ULZONENUM=2, ULZONEIND=5,
UL2NDSTARTSYMBOL=15, UL2NDZONESCHNUM=35;
2. You can run the MOD CARRIERBASICINFO command to configure the basic
information of the carriers.
MOD CARRIERBASICINFO: SECTORID=0, CARRIERID=0, DLSEGMENTNO =0,
DLBITMAP="00000003", ULBITMAP="000000000000000FFF";
3. You can run the MOD FFRPARA command to configure the measurement threshold.
MOD FFRPARA: SECTORID=0, CARRIERID=0, PUSCTOALLMEATH=18;
4. You can run the MOD FFRPARA command to configure the switching threshold.
MOD FFRPARA: SECTORID=0, CARRIERID=0, PUSCTOALLSWITCHTH=20,
ALLTOPUSCSWITCHTH=16;
8.4 Implementation of the FFR Feature
This describes how to activate and deactivate the FFR feature.
8.4.1 Activating the FFR Feature
This describes how to activate the FFR feature.
8.4.2 Deactivating the FFR Feature
This describes how to deactivate the FFR feature.
8.4.1 Activating the FFR Feature
This describes how to activate the FFR feature.
8-6 Huawei Proprietary and Confidential Issue 01 (2009-03-20)
Copyright © Huawei Technologies Co., Ltd.
DBS3900 WiMAX
Feature Configuration Guide 8 FFR Feature
Procedure
This is an inherent feature of the system, and activation is not required.
----End
8.4.2 Deactivating the FFR Feature
This describes how to deactivate the FFR feature.
Procedure
This is an inherent feature of the system, and deactivation is not possible.
----End
8.5 Maintenance Information of the FFR Feature
This describes the parameters and performance measurement items related to the FFR feature.
Related Parameters
Table 8-3 lists the parameters related to the FFR feature.
Table 8-3 Parameters of the MOD FFRPARA command
Parameter Meaning
SECTORID Sector ID
CARRIERID Carrier ID
PUSCTOALLDELTACINR Pusc to All Zone Handoff Cinr Delta
ALLTOPUSCDELTACINR All Zone to Pusc Handoff Cinr Delta
PUSCTOALLMEATH Pusc To All Measure Threshold
PUSCTOALLSWITCHTH Pusc To All Handoff Threshold
ALLTOPUSCSWITCHTH All To Pusc Switch Threshold
Related Performance Measurement Items
None.
8.6 Reference Information of the FFR Feature
The FFR complies with the IEEE 802.16e standard.
Issue 01 (2009-03-20) Huawei Proprietary and Confidential 8-7
Copyright © Huawei Technologies Co., Ltd.
Anda mungkin juga menyukai
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (121)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (344)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (895)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (73)
- 01 ETR300R Manual Control Ver1.47 201304Dokumen313 halaman01 ETR300R Manual Control Ver1.47 201304chiemenx100% (1)
- Unit - II: Digital CommunicationDokumen76 halamanUnit - II: Digital CommunicationJagan GcBelum ada peringkat
- Rule Breakers FinalDokumen22 halamanRule Breakers Finalnello80Belum ada peringkat
- Introduction To Digital AgeDokumen5 halamanIntroduction To Digital AgeRylleMatthanCorderoBelum ada peringkat
- Data Benchmarking: (RF) Connection Accessibility Task RetainabilityDokumen2 halamanData Benchmarking: (RF) Connection Accessibility Task RetainabilityBonar SianiparBelum ada peringkat
- Exp (3) - Active Filters - Low-Pass & High-PassDokumen13 halamanExp (3) - Active Filters - Low-Pass & High-PassTony SopranoBelum ada peringkat
- Part 3 Electric Control Principle and ParametersDokumen27 halamanPart 3 Electric Control Principle and ParametersrohanBelum ada peringkat
- CatET NEDG6015-09Dokumen2 halamanCatET NEDG6015-09Anderson Oliveira SilvaBelum ada peringkat
- Power Outage ReportDokumen39 halamanPower Outage ReportmateenBelum ada peringkat
- Cuk Trainer ManualDokumen6 halamanCuk Trainer ManualShankar ArunmozhiBelum ada peringkat
- 04 Antenna ArraysDokumen53 halaman04 Antenna Arrayshabtemariam mollaBelum ada peringkat
- Aic 41.3 PDFDokumen39 halamanAic 41.3 PDFAndrew van WykBelum ada peringkat
- Power MOSFET TypesDokumen9 halamanPower MOSFET TypesĐại Nguyễn VănBelum ada peringkat
- Omniswitch 6560 Datasheet enDokumen10 halamanOmniswitch 6560 Datasheet enflrujureuisthvBelum ada peringkat
- RMC41Dokumen4 halamanRMC41Joiver Ismael Rodríguez BruzualBelum ada peringkat
- Feedback Amplifier, Its Operation, Effect Importance and Connecting Types: A ReviewDokumen18 halamanFeedback Amplifier, Its Operation, Effect Importance and Connecting Types: A ReviewJasmineBelum ada peringkat
- P.E.L Iec 60076-3-2000 2021-7-20Dokumen2 halamanP.E.L Iec 60076-3-2000 2021-7-20Luis Alfredo Ramos FernandezBelum ada peringkat
- HTS-32 Panasonic Feature - ManualDokumen80 halamanHTS-32 Panasonic Feature - ManualWaldirBelum ada peringkat
- Manual 1760677 Vestel Vestel Evc02 Ac11rw Emobility Charging Station Type 2 Mode 3 16 A 11 KW Rfid Wi FiDokumen98 halamanManual 1760677 Vestel Vestel Evc02 Ac11rw Emobility Charging Station Type 2 Mode 3 16 A 11 KW Rfid Wi FiMihai MargineanuBelum ada peringkat
- A Comparative Investigation of Orthogonal Pilot Allocation Schemes For Spectral Efficiency Improvement in Massive-MIMO SystemsDokumen6 halamanA Comparative Investigation of Orthogonal Pilot Allocation Schemes For Spectral Efficiency Improvement in Massive-MIMO SystemsfiremailboxBelum ada peringkat
- Summary of The Types of FlipDokumen1 halamanSummary of The Types of FlipPola RismaBelum ada peringkat
- MT4WDokumen11 halamanMT4WFebrianto HermawanBelum ada peringkat
- Omron Electronics Solid State Timers h3cr ADokumen26 halamanOmron Electronics Solid State Timers h3cr ABang GuhBelum ada peringkat
- A Survey of Routing Protocols For Underwater Wireless Sensor NetworksDokumen24 halamanA Survey of Routing Protocols For Underwater Wireless Sensor NetworksGJ GNANA VENKAT NAGBelum ada peringkat
- EV ProSound Speaker and Electronics FullCatalog - LR-spreadDokumen40 halamanEV ProSound Speaker and Electronics FullCatalog - LR-spreadgreggles69Belum ada peringkat
- 50W Monocrystalline Solar Panels: Electrical SpecificationsDokumen1 halaman50W Monocrystalline Solar Panels: Electrical SpecificationsCloue DeriadaBelum ada peringkat
- DLDDokumen8 halamanDLDMuhammad Hamza RafiqBelum ada peringkat
- Iptv STB Manual Zxv10 b720Dokumen2 halamanIptv STB Manual Zxv10 b720disepyBelum ada peringkat
- RS10 ManualDokumen2 halamanRS10 ManualMax PaytonBelum ada peringkat
- Sd3 (U) Over Speed: Application Point of DetectionDokumen1 halamanSd3 (U) Over Speed: Application Point of DetectionAce Noah SomintacBelum ada peringkat