Bio Metrics
Diunggah oleh
Mrrajesh RajeshDeskripsi Asli:
Hak Cipta
Format Tersedia
Bagikan dokumen Ini
Apakah menurut Anda dokumen ini bermanfaat?
Apakah konten ini tidak pantas?
Laporkan Dokumen IniHak Cipta:
Format Tersedia
Bio Metrics
Diunggah oleh
Mrrajesh RajeshHak Cipta:
Format Tersedia
Biometrics:
Biometrics is the science and technology of measuring and analyzing biological data. In information technology, biometrics refers to technologies that measure and analyze human body characteristics, such as DNA, fingerprints, eye retinas and irises, voice patterns, facial patterns and hand measurements, for authentication purposes.
Biometric verification:
Biometric verification is any means by which a person can be uniquely identified by evaluating one or more distinguishing biological traits. Unique identifiers include fingerprints, hand geometry, earlobe geometry, retina and iris patterns, voice waves, DNA, and signatures. The oldest form of biometric verification is fingerprinting. Historians have found examples of thumbprints being used as a means of unique identification on clay seals in ancient China. Biometric verification has advanced considerably with the advent of computerized databases and the digitization of analog data, allowing for almost instantaneous personal identification. Iris-pattern and retina-pattern authentication methods are already employed in some bank automatic teller machines. Voice waveform recognition, a method of verification that has been used for many years with tape recordings in telephone wiretaps, is now being used for access to proprietary databanks in research facilities. Facial-recognition technology has been used by law enforcement to pick out individuals in large crowds with considerable reliability. Hand geometry is being used in industry to provide physical access to buildings. Earlobe geometry has been used to disprove the identity of individuals who claim to be someone they are not (identity theft). Signature comparison is not as reliable, all by itself, as the other biometric verification methods but offers an extra layer of verification when used in conjunction with one or more other methods. No matter what biometric methodology is used, the identification verification process remains the same. A record of a person's unique characteristic is captured and kept in a database. Later on, when identification verification is required, a new record is captured and compared with the previous record in the database. If the data in the new record matches that in the database record, the person's identity is confirmed.
How Biometrics Works:
Imagine you're James Bond, and you have to get into a secret laboratory to disarm a deadly biological weapon and save the world. But first, you have to get past the security system. It requires more than just a key or a password -- you need to have the villain's irises, his voice and the shape of his hand to get inside. You might also encounter this scenario, minus the deadly biological weapon, during an average day on the job. Airports, hospitals, hotels, grocery stores and even Disney theme parks increasingly usebiometrics -- technology that identifies you based on your physical or behavioral traits -- for added security.
In this article, you'll learn about biometric systems that use handwriting, hand geometry, voiceprints, iris structure and vein structure. You'll also learn why more businesses and governments use the technology and whether Q's fake contact lenses, recorded voice and silicone hand could really get James Bond into the lab (and let him save the world). You take basic security precautions every day -- you use a key to get into your house and log on to your computer with a username and password. You've probably also experienced the panic that comes with misplaced keys and forgotten passwords. It isn't just that you can't get what you need -- if you lose your keys or jot your password on a piece of paper, someone else can find them and use them as though they were you. Instead of using something you have (like a key) or something you know (like a password), biometrics uses who you are to identify you. Biometrics can use physical characteristics, like your face, fingerprints, irises or veins, or behavioral characteristics like your voice, handwriting or typing rhythm. Unlike keys and passwords, your personal traits are extremely difficult to lose or forget. They can also be very difficult to copy. For this reason, many people consider them to be safer and more secure than keys or passwords. Biometric systems can seem complicated, but they all use the same three steps:
Enrollment: The first time you use a biometric system, it records basic information about you, like your name or an identification number. It then captures an image or recording of your specific trait. Storage: Contrary to what you may see in movies, most systems don't store the complete image or recording. They instead analyze your trait and translate it into a code or graph. Some systems also record this data onto a smart card that you carry with you. Comparison: The next time you use the system, it compares the trait you present to the information on file. Then, it either accepts or rejects that you are who you claim to be. Systems also use the same three components:
A sensor that detects the characteristic being used for identification A computer that reads and stores the information Software that analyzes the characteristic, translates it into a graph or code and performs the actual comparisons Biometric security systems, like the fingerprint scanner available on the IBM ThinkPad T43 (right), is becoming more common for home use. You can read other How Stuff Works articles to learn about face recognition and fingerprint scanning. Next, we'll examine how biometrics provides security using other traits, starting with handwriting.
How Facial Recognition Systems Work:
Anyone who has seen the TV show "Las Vegas" has seen facial recognition software in action. In any given episode, the security department at the fictional Montecito Hotel and Casino uses its video surveillance system to pull an image of a card counter, thief or blacklisted individual. It then runs that image through the database to find a match and identify the person. By the end of the hour, all bad guys are escorted from the casino or thrown in jail. But what looks so easy on TV doesn't always translate as well in the real world. In 2001, the Tampa Police Department installed police cameras equipped with facial recognition technology in their Ybor City nightlife district in an attempt to cut down on crime in the area. The system failed to do the job, and it was scrapped in 2003 due to ineffectiveness. People in the area were seen wearing masks and making obscene gestures, prohibiting the cameras from getting a clear enough shot to identify anyone. Boston's Logan Airport also ran two separate tests of facial recognition systems at its security checkpoints using volunteers. Over a three month period, the results were disappointing. According to the Electronic Privacy Information Center, the system only had a 61.4 percent accuracy rate, leading airport officials to pursue other security options. Humans have always had the innate ability to recognize and distinguish between faces, yet computers only recently have shown the same ability. In the mid 1960s, scientists began work on using the computer to recognize human faces. Since then, facial recognition software has come a long way. In this article, we will look at the history of facial recognition systems, the changes that are being made to enhance their capabilities and how governments and private companies use (or plan to use) them.
How Fingerprint Scanners Work :
Computerized fingerprint scanners have been a mainstay of spy thrillers for decades, but up until recently, they were pretty exotic technology in the real world. In the past few years, however, scanners have started popping up all over the place -- in police stations, high-security buildings and even on PC keyboards. You can pick up a personal USB fingerprint scanner for less than $100, and just like that, your computer's guarded by high-tech biometrics. Instead of, or in addition to, a password, you need your distinctive print to gain access. In this article, we'll examine the secrets behind this exciting development in law enforcement and identity security. We'll also see how fingerprint scanner security systems stack up to conventional password and identity card systems, and find out how they can fail.
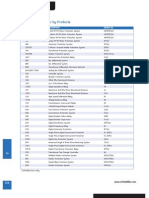
Anda mungkin juga menyukai
- Alstom SCS VAA Aux RelayDokumen4 halamanAlstom SCS VAA Aux RelaypsatyasrinivasBelum ada peringkat
- JRV 022Dokumen3 halamanJRV 022Mrrajesh RajeshBelum ada peringkat
- P14x Relay Case DimensionsDokumen1 halamanP14x Relay Case DimensionsMrrajesh RajeshBelum ada peringkat
- Digital Panel Meters.133110152Dokumen24 halamanDigital Panel Meters.133110152Prince Al Rossi0% (1)
- B.arch Anna University SyllabusDokumen23 halamanB.arch Anna University SyllabusSuresh PothyBelum ada peringkat
- BackupDokumen6 halamanBackupMrrajesh RajeshBelum ada peringkat
- SUBSTATION AND TRANSMISSION LINE PROTECTIONDokumen90 halamanSUBSTATION AND TRANSMISSION LINE PROTECTIONkedsoi2100% (1)
- Control and Relay PanelsDokumen59 halamanControl and Relay PanelsMrrajesh Rajesh100% (1)
- Why Power Systems Require ProtectionDokumen7 halamanWhy Power Systems Require ProtectionMrrajesh RajeshBelum ada peringkat
- Electrical SafetyDokumen9 halamanElectrical SafetyMrrajesh RajeshBelum ada peringkat
- Powergen Invitation From WOODWARD IndiaDokumen2 halamanPowergen Invitation From WOODWARD IndiaMrrajesh RajeshBelum ada peringkat
- ABBs IEC 61850 SS AutomationDokumen10 halamanABBs IEC 61850 SS Automationprasannakumar_rajaBelum ada peringkat
- Basics of ProtetionDokumen1 halamanBasics of ProtetionMrrajesh RajeshBelum ada peringkat
- EMFs Explained: Electric and Magnetic Fields at Work and HomeDokumen4 halamanEMFs Explained: Electric and Magnetic Fields at Work and HomeGilbert MilesBelum ada peringkat
- Development of Power System Protection Laboratory Through Senior Design ProjectsDokumen6 halamanDevelopment of Power System Protection Laboratory Through Senior Design ProjectsMrrajesh RajeshBelum ada peringkat
- 01308326Dokumen8 halaman01308326Mrrajesh RajeshBelum ada peringkat
- ANSI Product PDFDokumen3 halamanANSI Product PDFkgunaBelum ada peringkat
- C C CCCCCDokumen2 halamanC C CCCCCMrrajesh RajeshBelum ada peringkat
- Shoe Dog: A Memoir by the Creator of NikeDari EverandShoe Dog: A Memoir by the Creator of NikePenilaian: 4.5 dari 5 bintang4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDari EverandGrit: The Power of Passion and PerseverancePenilaian: 4 dari 5 bintang4/5 (587)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDari EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RacePenilaian: 4 dari 5 bintang4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)Dari EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Penilaian: 4 dari 5 bintang4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDari EverandThe Little Book of Hygge: Danish Secrets to Happy LivingPenilaian: 3.5 dari 5 bintang3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealDari EverandOn Fire: The (Burning) Case for a Green New DealPenilaian: 4 dari 5 bintang4/5 (73)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDari EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifePenilaian: 4 dari 5 bintang4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDari EverandNever Split the Difference: Negotiating As If Your Life Depended On ItPenilaian: 4.5 dari 5 bintang4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDari EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FuturePenilaian: 4.5 dari 5 bintang4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDari EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryPenilaian: 3.5 dari 5 bintang3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDari EverandThe Emperor of All Maladies: A Biography of CancerPenilaian: 4.5 dari 5 bintang4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDari EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You ArePenilaian: 4 dari 5 bintang4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDari EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyPenilaian: 3.5 dari 5 bintang3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnDari EverandTeam of Rivals: The Political Genius of Abraham LincolnPenilaian: 4.5 dari 5 bintang4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDari EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersPenilaian: 4.5 dari 5 bintang4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDari EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaPenilaian: 4.5 dari 5 bintang4.5/5 (265)
- Rise of ISIS: A Threat We Can't IgnoreDari EverandRise of ISIS: A Threat We Can't IgnorePenilaian: 3.5 dari 5 bintang3.5/5 (137)
- The Unwinding: An Inner History of the New AmericaDari EverandThe Unwinding: An Inner History of the New AmericaPenilaian: 4 dari 5 bintang4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Dari EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Penilaian: 4.5 dari 5 bintang4.5/5 (119)
- Her Body and Other Parties: StoriesDari EverandHer Body and Other Parties: StoriesPenilaian: 4 dari 5 bintang4/5 (821)
- Multiple Choice Question (MCQ) of Alternator and Synchronous Motors PageDokumen29 halamanMultiple Choice Question (MCQ) of Alternator and Synchronous Motors Pagekibrom atsbha0% (1)
- NEW CREW Fast Start PlannerDokumen9 halamanNEW CREW Fast Start PlannerAnonymous oTtlhP100% (3)
- Group 4-Hospital Information System - His - QuizDokumen2 halamanGroup 4-Hospital Information System - His - QuizGeeyan Marlchest B NavarroBelum ada peringkat
- 13-07-01 Declaration in Support of Skyhook Motion To CompelDokumen217 halaman13-07-01 Declaration in Support of Skyhook Motion To CompelFlorian MuellerBelum ada peringkat
- QSK45 60 oil change intervalDokumen35 halamanQSK45 60 oil change intervalHingga Setiawan Bin SuhadiBelum ada peringkat
- Deed of Sale - Motor VehicleDokumen4 halamanDeed of Sale - Motor Vehiclekyle domingoBelum ada peringkat
- Inflatable Packers enDokumen51 halamanInflatable Packers enDavid LuhetoBelum ada peringkat
- Ten Golden Rules of LobbyingDokumen1 halamanTen Golden Rules of LobbyingChaibde DeBelum ada peringkat
- AHP for Car SelectionDokumen41 halamanAHP for Car SelectionNguyên BùiBelum ada peringkat
- The Human Resource Department of GIK InstituteDokumen1 halamanThe Human Resource Department of GIK InstitutexandercageBelum ada peringkat
- Gerhard Budin PublicationsDokumen11 halamanGerhard Budin Publicationshnbc010Belum ada peringkat
- Indian Institute of Management KozhikodeDokumen5 halamanIndian Institute of Management KozhikodepranaliBelum ada peringkat
- Continuation in Auditing OverviewDokumen21 halamanContinuation in Auditing OverviewJayBelum ada peringkat
- (Free Scores - Com) - Stumpf Werner Drive Blues en Mi Pour La Guitare 40562 PDFDokumen2 halaman(Free Scores - Com) - Stumpf Werner Drive Blues en Mi Pour La Guitare 40562 PDFAntonio FresiBelum ada peringkat
- Well Control Kill Sheet (Low Angle Wells)Dokumen8 halamanWell Control Kill Sheet (Low Angle Wells)Tatita ValenciaBelum ada peringkat
- Palmetto Bay's Ordinance On Bird RefugeDokumen4 halamanPalmetto Bay's Ordinance On Bird RefugeAndreaTorresBelum ada peringkat
- Top 35 Brokerage Firms in PakistanDokumen11 halamanTop 35 Brokerage Firms in PakistannasiralisauBelum ada peringkat
- Collaboration Live User Manual - 453562037721a - en - US PDFDokumen32 halamanCollaboration Live User Manual - 453562037721a - en - US PDFIvan CvasniucBelum ada peringkat
- Lec - Ray Theory TransmissionDokumen27 halamanLec - Ray Theory TransmissionmathewBelum ada peringkat
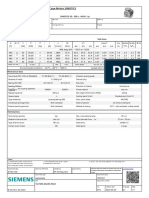
- 1LE1503-2AA43-4AA4 Datasheet enDokumen1 halaman1LE1503-2AA43-4AA4 Datasheet enAndrei LupuBelum ada peringkat
- Introduction To Elective DesignDokumen30 halamanIntroduction To Elective Designabdullah 3mar abou reashaBelum ada peringkat
- Abra Valley College Vs AquinoDokumen1 halamanAbra Valley College Vs AquinoJoshua Cu SoonBelum ada peringkat
- Micromaster 430: 7.5 KW - 250 KWDokumen118 halamanMicromaster 430: 7.5 KW - 250 KWAyman ElotaifyBelum ada peringkat
- Photoshop Tools and Toolbar OverviewDokumen11 halamanPhotoshop Tools and Toolbar OverviewMcheaven NojramBelum ada peringkat
- SAP PS Step by Step OverviewDokumen11 halamanSAP PS Step by Step Overviewanand.kumarBelum ada peringkat
- 1.1 Introduction To Networks - Networks Affect Our LivesDokumen2 halaman1.1 Introduction To Networks - Networks Affect Our LivesCristian MoralesBelum ada peringkat
- WELDING EQUIPMENT CALIBRATION STATUSDokumen4 halamanWELDING EQUIPMENT CALIBRATION STATUSAMIT SHAHBelum ada peringkat
- BRD TemplateDokumen4 halamanBRD TemplateTrang Nguyen0% (1)
- Advance Bio-Photon Analyzer ABPA A2 Home PageDokumen5 halamanAdvance Bio-Photon Analyzer ABPA A2 Home PageStellaEstel100% (1)
- Dell 1000W UPS Spec SheetDokumen1 halamanDell 1000W UPS Spec SheetbobBelum ada peringkat